Advertizementforyour.com ads (scam) - Free Instructions
Advertizementforyour.com ads Removal Guide
What is Advertizementforyour.com ads?
Advertizementforyour.com ads are intrusive and potentially dangerous
You may start noticing Advertizementforyour.com ads on your device without any warning. The activity can show up on various operating systems, including Windows, macOS, or mobile devices such as Android phones or tablets; its primary way of operating is through web browsers like Google Chrome, Mozilla Firefox, MS Edge, etc., though users would have to change settings within the browser in order to get rid of the intrusive pop-ups.
Many people think that Advertizementforyour.com ads are the result of a computer virus. While it's true that adware can cause browser redirects and an increase in advertising, this is actually due to allowing a malicious website to show push notifications without any restrictions. As such, the removal of push notifications can only be done manually, as our explanation below will detail. It is important to get rid of these pop-ups, as they may bring all sorts of malicious links at any time whenever the browser is active – it doesn't even have to be actively used.
| Name | Advertizementforyour.com |
| Type | Push notifications, ads, scam, pop-ups |
| Distribution | Desktop notifications start showing up at random times after clicking on the “Allow” button upon the site entry |
| Symptoms | Pop-up notifications show up on the desktop at random times – the ads often include inappropriate, scam, phishing, or other similar content |
| Risks | Push notifications sent by the site might result in you visiting dangerous websites; consequently, you might suffer from malware infections, financial losses, or personal data disclosure to malicious parties |
| Removal | To stop the intrusive pop-ups, you need to access the settings section of your browser. You should also check your system with security software to eliminate adware and malware |
| Additional tips | Third parties can use cookies to continue tracking your online activities, so we recommended clearing browser caches and other leftover files with FortectIntego |
You have likely visited Advertizementforyour.com after clicking a malicious link, although adware could also be involved
Few people would be willing to view websites that could endanger their safety and the security of their computers, which is something that scammers are well aware of. In fact, using a search engine like Google or simply browsing websites that are regarded as trustworthy makes it unlikely (but not impossible) to come across a malicious website.
However, whenever users willfully visit websites of questionable origins, the likelihood of encountering suspicious content online dramatically increases. For instance, those who decide to download illegal software run a much higher chance of coming across malware or links that take them to phishing,[1] gambling, or other questionable websites. Evidently, we strongly advise against visiting torrents, software cracks, and similar sites that distribute illegal software.
Another possibility is that adware installed on users' computers would direct them to Advertizementforyour.com or another website of a similar nature. Since adware is often distributed through software bundling[2] and other sneaky means, many people might not even be aware that it is active on their devices.
To avoid the installation of potentially unwanted applications, be very careful when installing new software from third-party websites. For example, choosing Recommend/Quick settings are more likely to result in the installation of PUPs, and the Advanced/Custom option will allow you to remove all optional components before they get into your device.

How scammers reach their goals
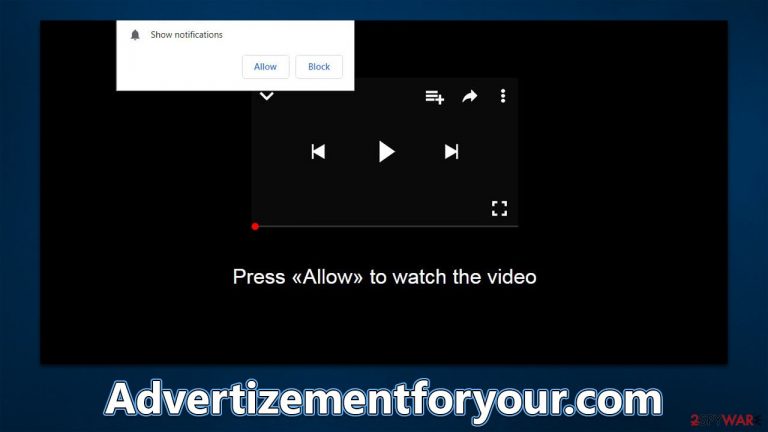
Many people don't understand push notifications because they haven't been around for very long. Even though many users have seen requests to enable them, usually, the prompt's function is presented differently than what it actually is on scam websites such as Advertizementforyour.com.
To be more precise, these types of websites have no content in them whatsoever, and their main goal is to show misleading statements to users in order to make them subscribe to push notifications. It is also relatively common for clicks on random spaces on these pages to reroute users to other similar sites, such as Newspoldays.site or News-vukaje.com.
To be successful, scammers use various social engineering[3] tricks within their messages, applying simple but effective tactics – here are a few examples of fake messages frequently used on push notification scam sites:
- Press “Allow” to watch the video
- Click “Allow” if you are not a robot
- Just one more step! “Allow” to continue
- If you are 18+, click Allow
- Click the Allow button to subscribe to notifications and continue watching
- The download is ready! Click Allow to download the file, etc.
If you're worried about getting too many pop-ups, only allow websites that you trust to send push notifications. If you accidentally allowed a site to send them or were tricked into it, it is vital not to interact with ads that you are seeing, as they could lead you to various malicious places online, resulting in malware infections, personal data disclosure, or financial losses due to the exposure to various scams.
Deal with intrusive push notifications and check your system for infections
Uninstall any software from third-party websites that you have recently installed. If you did not install anything intentionally, there could be more dangerous programs installed on your device without your knowledge. The easiest way to check for adware and malware is by scanning the device with SpyHunter 5Combo Cleaner or Malwarebytes security software – it would make sure that all the found infections are deleted at once.
Once you've completed the removal process, we also suggest clearing your browser cache to stop any unwanted tracking. This can be easily done with FortectIntego, a maintenance and repair tool that can fix system issues caused by malware infections, such as BSODs, errors, registry corruption, and more.
As soon as you are sure that your device is malware-free, you can then proceed with the Advertizementforyour.com ads removal. You can achieve that by accessing browser settings and blocking the correlating URL within the site settings section, as explained below:
Google Chrome
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.

Google Chrome (Android)
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off position).

Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.

Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.

MS Edge
- Open Microsoft Edge, and click the Settings and more button (three horizontal dots) at the top-right of the window.
- Select Settings and then go to Advanced.
- Under Website permissions, pick Manage permissions and select the URL in question.
- Toggle the switch to the left to turn notifications off on Microsoft Edge.

MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.

Internet Explorer
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.

- Locate the web address in question under Allowed sites and pick Remove.
How to prevent from getting adware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Phishing attacks. Imperva. Application and data security.
- ^ Bundled software. Computer Hope. Free computer help.
- ^ What is Social Engineering?. Knowbe4. Security awareness and training solutions.
