Afrodita ransomware (Virus Removal Guide) - Decryption Steps Included
Afrodita virus Removal Guide
What is Afrodita ransomware?
Afrodita ransomware – a new malware string that targets businesses in Croatia
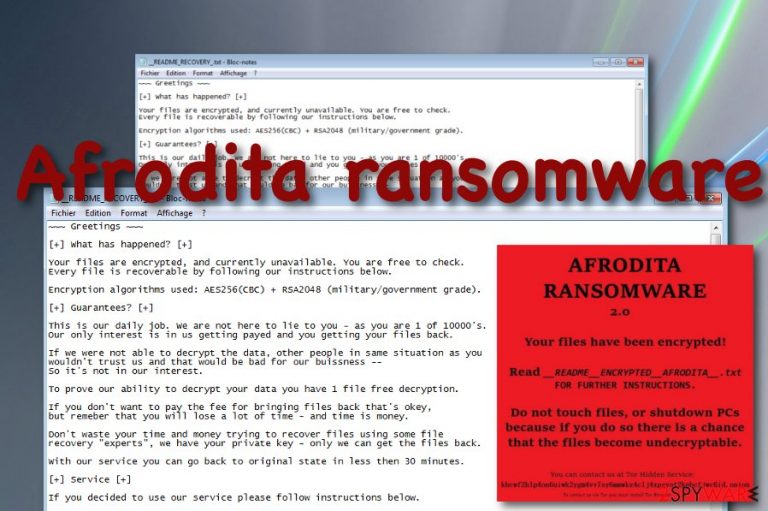
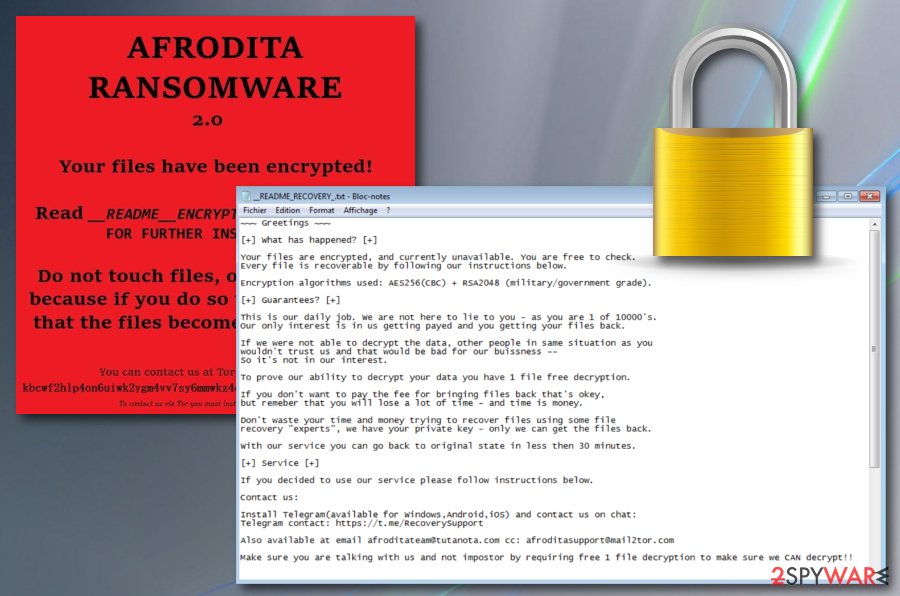
Afrodita ransomware is a notorious parasite that is spread via phishing emails and attached excel sheets.[1] The malware uses AES-256 and RSA-2048 keys to lock up files but adds no extension to the filenames. Continuously, the _README_RECOVERY.txt and __README__ENCRYPTED__AFRODITA__.txt. ransom notes are delivered to the computer screen. One of them provides the afroditeam@tutanota.com and afroditasupport@mail2tor.com email addresses for making contact with the Afrodita ransomware developers and discussing all the terms about the decryption price when the other one provides a contact link to the Tor web browser.[2] These people offer to send them one file for free decryption to receive evidence that the software truly exists.
Afrodita ransomware plays tricks on random users by getting delivered as the Invoice.xlsm file attached to a phishing email message. It might not seem strange at first but once opened, the attachment places the verynice.jpg file on the computer which is saved as Afrodita.dll. This particular component is the one that executes the malicious infection. Continuously, another file named info.jpg is dropped to the machine and is supposed to change the desktop's background after the encryption process succeeds.
| Name | Afrodita ransomware |
|---|---|
| Type | Ransomware virus/malware |
| Encryption | The ransomware virus uses the AES-256 and RSA-2048 algorithms to lock up files that are placed on the infected Windows computer system. However, this malware adds no extension after the encryption process |
| Ransom note | The malware displays the _README_RECOVERY.txt and _README_ENCRYPTED_AFRODITA_.txt ransom messages when the encryption on files succeeds |
| Contacts | The criminals provide afroditeam@tutanota.com and afroditasupport@mail2tor.com email addresses as a way to contact them and discuss the payment terms and conditions |
| Related files | Afrodita virus is capable of delivering these random files to the computer system: verynice.jpg that is saved as Afrodita.dll and info.jpg |
| Other activities | The ransomware might have other capabilities such as booting up within every startup process, evading antimalware detection, deleting the Shadow Volume Copies of encrypted data, damaging the Windows hosts file, including other malware into the system |
| Spreading | It is known that this malicious string is most commonly delivered through email spam campaigns and malicious attachments such as Invoice.xlsm. However, the malware can also be spread through cracked products that come from p2p networks, malvertising, infectious hyperlinks, fake software updates, and unsecured RDP configuration |
| Removal process | You should get rid of the ransomware virus as soon as you spot it on your Windows computer system. For this process, employ reliable security software only as manual steps might not be enough to terminate the malware fully and safely |
| Fixing tool | If you have discovered any signs that your system might have got compromised during the ransomware attack, try repairing your machine with a piece of software such as FortectIntego |
Afrodita virus is a notorious infection that can hit any type of user nevermind if the person has high computing skills or weak ones. In order not to get caught by the cybercriminals, you have to manage your received email wisely. If you do not do that, all of your files and documents that are on your infected Windows computer will get encrypted.
It might be hard to spot Afrodita ransomware at first as it does not append any extension to the locked files. However, you can recognize the malware if it changes your background image or displays you this ransom note:
~~~Greetings~~~
[+] What has happened? [+]
Your files are encrypted, and currently unavailable. You are free to check. Every file is recoverable by following our instructions below.
Encryption algorithms used: AES256(CBC) + RSA2048 (military/government grade).
[+] Guarantees? [+]
This is our daily job. We are not here to lie to you – as you are 1 of 10000's. Our only interest is in us getting payed and you getting your files back.
If we were not able to decrypt the data, other people in same situation as you wouldn't trust us and that would be bad for our buissness — So it's not in our interest.
To prove our ability to decrypt your data you have 1 file free decryption.
If you don't want to pay the fee for bringing files back that's okey, but remeber that you will lose a lot of time – and time is money.
Don't waste your time and money trying to recover files using some file recovery “experts”, we have your private key – only we can get the files back.
With our service you can go back to original state in less then 30 minutes.
[+] Service [+]
If you decided to use our service please follow instructions below.
Contact us:
Install Telegram(available for Windows,Android,ios) and contact us on chat: Telegram contact: https://t.me/RecoverySupport
Also available at email afroditateam@tutanota.com cc: afroditasupport@mail2tor.com
Make sure you are talking with us and not impostor by requiring by requiring free 1 file decryption to make sure we CAN decrypt!!
Afrodita ransomware offers to deliver the crooks one file for free encryption to receive proof of the decryption software's existence. These people state that they are the only ones that can recover the blocked data within 30 minutes after the ransom payment. Even though the cybercriminals claim that they are not lying, you can never now.
Victims who fall for believing in the promises of cyber crooks often get scammed and are left without their promised product. The same can happen with Afrodita ransomware developers as these people are orientated only in collecting income. thus, you should avoid making contact with the developers and paying the demanded amount.
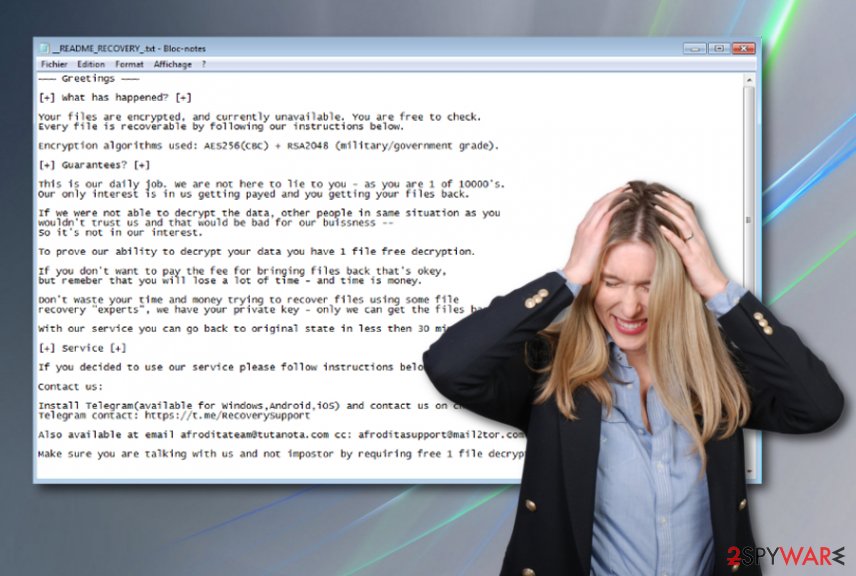
Afrodita ransomware does not provide any particular payment demands but the malware creators can ask for any type of price from tens of dollars to thousands of them. However, the criminals will likely urge some type of cryptocurrency payment, e.g. Bitcoin, to ensure that the transfer process is kept safe and untrackable by federal agencies.
Afrodita ransomware might have a much complex module than it can be thought from the first view. The malware might be able to deactivate antimalware software, boot itself within every startup process, and search for encryptable files and documents in particular time periods, e.g. ten, thirty minutes, one hour, and so on.
Continuously, the malware can be capable of deleting the Shadow Volume Copies[3] of encrypted data in order to hard the decryption process for the users. Another thing that Afrodita ransomware can do is permanently damage the Windows hosts file to prevent access to cybersecurity-related websites, forums, and networks.
Besides all that the ransomware might install other types of malware into the infected computer system, e.g. trojans. For this not to happen, you should remove Afrodita ransomware as soon as you recognize the infection. You should use only reliable automatical software that is capable of eliminating such complex cyber threats.
Even though the ransomware is likely to be eliminated automatically after the files are encrypted, there is no guarantee that this will happen, so you still might have to deal with the Afrodita ransomware removal process. Also, if you find any corrupted areas on your Windows computer system, you can try repairing the damage with software such as FortectIntego.
Email spam is the most common ransomware distribution source
Phishing email messages are often dropped to random users by ransomware developers. This is the most popular technique that is employed for pushing the malicious payload. The hackers pretend to be from reliable organizations, companies, and agencies. They attach executables, pdfs, or word documents to the email message where the ransomware infection is hidden. Also, they can include the malware into a hyperlink and insert it into the content of the email.
If you want to protect yourself from ransomware attacks, you should be careful while opening unknown emails. If you were not expecting to receive anything important lately, you should consider deleting the message right away. Also, you should never open questionable-looking attachments without scanning them with antimalware software, try to identify the deliverer of the message and search the email's content for possible grammar mistakes.
Continuously, ransomware viruses are delivered through unsecured RDP. According to cybersecurity specialists from NoVirus.uk,[4] if the port does not include a strong and reliable password, remote hackers can easily connect to it and brutally enter your computer system. Regarding this fact, never forget to secure your RDP with a strong password. However, there are also more techniques used for ransomware delivery.
These cyberthreats can camouflage as fake software updates, get distributed through malvertising or infectious hyperlinks that are found on third-party networks. Also, peer-to-peer sources are widely distributing various malware strings, including ransomware. The Pirate Bay and other secondary downloading websites are known for their weak protection and ability to carry malware instead of the regular product. Avoid these types of sources, get your programs and products from reliable sources only and use antimalware protection that will alert if something wrong is going on.
The Afrodita ransomware virus elimination guide
Even though Afrodita ransomware should eliminate itself after the encryption process, this might also not happen or the malware might leave additional malicious components on the computer system that also require cleaning.
To remove Afrodita ransomware from your Windows machine, employ reliable and strong antimalware software only, otherwise, the tool might not be capable of proceeding with the elimination. Note that the malware might have filled the Task Manager, Windows Registry and other sections with malicious products that also need to be deleted.
If you are having struggles with Afrodita ransomware removal, you should reboot your machine in Safe Mode with Networking or activate the System Restore feature in order to disable the malicious processes that the ransomware might be running. Afterward, scan your computer system for possible damage with the help of software such as SpyHunter 5Combo Cleaner or Malwarebytes. If these tools find any corrupted areas, you can try repairing them with another program such as FortectIntego.
When Afrodita ransomware is completely gone and you have returned your computer back to its previous state, you can continue with data recovery. Below we have provided some data restoring methods that might help you.
Getting rid of Afrodita virus. Follow these steps
Manual removal using Safe Mode
To deactivate the ransomware virus and diminish malicious changes on your Windows computer system, apply the following steps that will help you to boot in Safe Mode with Networking.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Afrodita using System Restore
To disable the dangerous infection and prevent its malicious processes from continuing, you should activate the System Restore feature on your computer system. Here are instructions on how to do it.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Afrodita. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Afrodita from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.Afrodita ransomware encrypts files but does not add any extension to the filenames that might make the encryption process hard to spot. However, once you see it, you will not be pleased that you cannot load your files properly anymore. Thus, we decided to try and help people by providing some data recovery software below that might be helpful an allow restoring at least some individual files.
If your files are encrypted by Afrodita, you can use several methods to restore them:
The Data Recovery Pro software can help with file restoring tasks.
If Afrodita ransomware virus has locked your files and documents, you have a chance of restoring them with the help of this software.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Afrodita ransomware;
- Restore them.
Windows Previous Versions feature might be capable of recovering some files.
Try using this tool for recovering at least some of your documents that were affected by the ransomware virus. However, this method requires booting the computer in System Restore before completing the recovery with this tool
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Using Shadow Explorer might help you with data recovery.
This tool might allow you to restore at least some of your individual files. However, note that this method might not work if the ransomware virus has deleted the Shadow Copies of encrypted data.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Currently, the cybersecurity specialists are working on the decryption key's development.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Afrodita and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Check Point Research. #Afrodita Ransomware. Twitter. Social Platform.
- ^ J. M. Porup. What is the Tor Browser? And how it can help protect your identity. CSO online. Articles.
- ^ Shadow Copy. Wikipedia. The free encyclopedia.
- ^ NoVirus.uk. NoVirus. Security and spyware news.







