Arberittertwa.info (Free Guide) - Removal Instructions
Arberittertwa.info Removal Guide
What is Arberittertwa.info?
Arberittertwa.info – a suspicious website that produces the “Confirm notifications” pop-up
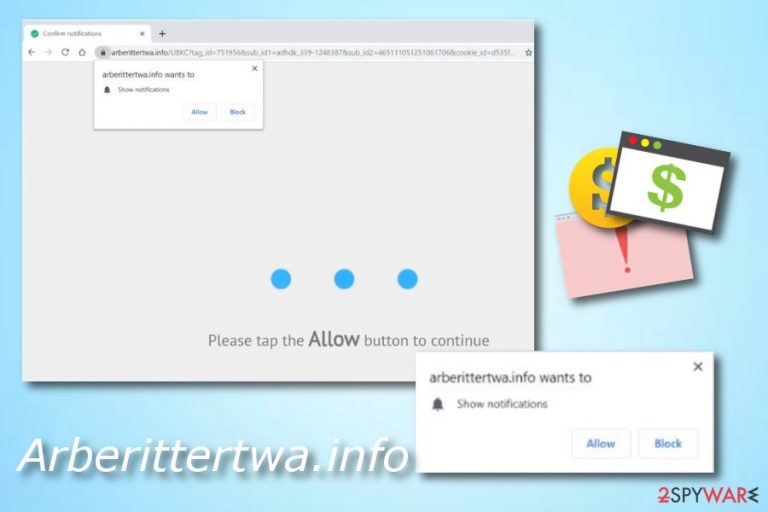
Arberittertwa.info is considered to be an ad-supported program that produces a white dialogue box and urges users to allow its notifications. The “Confirm notifications” or “Show notifications” pop-up has two functions, one is to block the incoming ads, and the other one is to allow. We strongly recommend choosing the first option as giving access to frequent advertising will supposedly cause you only unexpected problems.
Intrusive pop-up ads might interrupt your browsing activity which will slightly decrease the quality and speed of your work.[1] However, if an adware program is causing these pop-up notifications, you might also overcome some unusual things in your web browser, for example, certain changes might be spotted in the homepage or new tab URL locations.
Nevertheless, clicking on adware-provided pop-ups might relate to redirecting to developer-sponsored content. Even though this activity might seem innocent to you from the first view, believe us – it is not. The potentially unwanted program might not be dangerous itself, but it can force you to land on scam or other dangerous websites which have the possibility of affecting your computer system in numerous negative ways.
| Name | Arberittertwa.info |
|---|---|
| Program type | Adware/ad-supported application |
| Infection signs | Advertising has been intruding your browsing lately, suspicious redirects have been taking you to odd pages, changes have been spotted in your web browser such as Chrome, Firefox, Explorer, etc. |
| Purpose | To claim revenue from ads and browsing data |
| Danger level | Low. The program itself does not damage the computer system or its crucial components |
| Appearance sources | Such rogue app can come injected into a software package that you might download from a third-party source. Also, it can be accessed through infectious links |
| Detection tools | Use software such as FortectIntego to scan your entire computer system and search for potential threats |
| Removal | Removing adware is necessary. You can do that with anti-malware or the manual elimination guide that we have provided at the end of the article |
If you have installed a potentially unwanted program on your system, you like have made a mistake somewhere while installing software and the result is adware on the machine. These PUPs can sneak in through other programs and start modifying browsers for their own needs very easily and quickly.[2] The user's lack of carefulness usually is the main reason why adware lands on their computers.
However, we still cannot stand for Arberittertwa.info adware developers as these people use unfair techniques to distribute their applications. They are giving users no choice of their own as the application comes already injected into a certain type of software package, you want it or not. However, adware creators do not worry about their actions as the main goal is to gain as much profit as possible.
The pay-per-click[3] or cost-per-click technique is the easiest and the most effortless way to gather revenue. Each click on a particular pop-up ad brings money to the scam developers. Thus, you may see ads marked by the following:
- “Provided by…”
- “Ads by…”
- “Sponsored by…”, etc.
Keep in mind that such content needs to be avoided as much as possible. While some of the ads might bring you to legitimate websites, some of them might try to steal your personal information or trick you into downloading potentially dangerous software.
However, these ads might have even more negative sides, which we have already mentioned, it is redirecting to affiliate and malware-laden websites, causing browser struggles, crashes, and slowdowns, etc.
You should remove adware as soon as you spot the first signs of infection. This program will not bring any true value to you as a user, so there is no need to keep it. Use reputable software such as SpyHunter 5Combo Cleaner or Malwarebytes to scan your entire system. This is necessary because the adware application might have left its processes running in the background. Note that cleaning web browsers is equally important – either follow the instructions below or employ FortectIntego to do that for you automatically.
Arberittertwa.info removal is a necessary thing if you want to prevent adware developers from achieving their goals. These people can gain income not only from their advertisements but also from information that relates to your browsing sessions. This potentially unwanted application might gather browsing details such as:
- Your IP.
- Geolocation.[4]
- Sites visited.
- Saved bookmarks.
- Pictures and videos viewed.
- Hyperlinks accessed.

Adware applications can be detected in bundled software
According to cybersecurity experts from Virusai.lt,[5] adware applications and their components usually come as a product of bundling. This means that the adware installs together with regular software into the computer system. However, there are other sources from which adware can easily travel to a machine:
- Third-party websites.
- Secondary downloading hyperlinks.
- Promotive adverts.
- Free online gaming networks.
Preventing the secret installation of potentially unwanted programs is not that hard if you have some knowledge in this field. First of all, tracking your downloads is necessary. You can do this in the Custom configuration section. Furthermore, keeping a distance from secondary pages will also increase your computer's safety. Last but not least, antivirus/anti-malware/anti-spyware protection is very useful for all types of machines because it provides threat protection 24/7.
Arberittertwa.info pop-up ads termination
Kill all suspicious processes that relate to the adware program on your Windows computer. If you do this and also clean your web browsers, you will fully remove the virus from the system. Leaving suspicious content in your browsing applications or on your Windows machine will only postpone the renewal of the ad-supported application.
Arberittertwa.info removal needs to be completed with no rush if you take care of the process on your own. Do not forget to refresh your web browser's applications such as Google Chrome, Mozilla Firefox, Internet Explorer, Microsoft Edge, and Safari. To stop notifications, access the settings of your browser and prevent the site from showing them for you – check the full instructions below. For the future, make sure to stay away from possible adware sources.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Arberittertwa.info. Follow these steps
Stop browser notifications
Remove unwanted notifications from Google Chrome (desktop):
- Open Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate Privacy and security section and pick Site Settings > Notifications.

- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.

Remove unwanted notifications from Google Chrome (Android):
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).

Remove unwanted notifications from Mozilla Firefox:
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.

- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.

Remove unwanted notifications from Safari:
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.

Remove unwanted notifications from MS Edge:
- Open Microsoft Edge, and click the Settings and more button (three horizontal dots) at the top-right of the window.
- Select Settings and then go to Advanced.
- Under Website permissions, pick Manage permissions and select the URL in question.

- Toggle the switch to the left to turn notifications off on Microsoft Edge.

Remove unwanted notifications from MS Edge (Chromium):
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.

Remove unwanted notifications from Internet Explorer:
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.
- Locate web address in question under Allowed sites and pick Remove.

Uninstall from Windows
The removal of adware from Windows is shown in these instructing lines and needs to be carried out to ensure the best system optimization possible:
Instructions for Windows 10/8 machines:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

If you are Windows 7/XP user, proceed with the following instructions:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.

- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Remove from Microsoft Edge
Delete unwanted extensions from MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.

Clear cookies and other browser data:
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Restore new tab and homepage settings:
- Click the menu icon and choose Settings.
- Then find On startup section.
- Click Disable if you found any suspicious domain.
Reset MS Edge if the above steps did not work:
- Press on Ctrl + Shift + Esc to open Task Manager.
- Click on More details arrow at the bottom of the window.
- Select Details tab.
- Now scroll down and locate every entry with Microsoft Edge name in it. Right-click on each of them and select End Task to stop MS Edge from running.

If this solution failed to help you, you need to use an advanced Edge reset method. Note that you need to backup your data before proceeding.
- Find the following folder on your computer: C:\\Users\\%username%\\AppData\\Local\\Packages\\Microsoft.MicrosoftEdge_8wekyb3d8bbwe.
- Press Ctrl + A on your keyboard to select all folders.
- Right-click on them and pick Delete

- Now right-click on the Start button and pick Windows PowerShell (Admin).
- When the new window opens, copy and paste the following command, and then press Enter:
Get-AppXPackage -AllUsers -Name Microsoft.MicrosoftEdge | Foreach {Add-AppxPackage -DisableDevelopmentMode -Register “$($_.InstallLocation)\\AppXManifest.xml” -Verbose

Instructions for Chromium-based Edge
Delete extensions from MS Edge (Chromium):
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Clear cache and site data:
- Click on Menu and go to Settings.
- Select Privacy, search and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Reset Chromium-based MS Edge:
- Click on Menu and select Settings.
- On the left side, pick Reset settings.
- Select Restore settings to their default values.
- Confirm with Reset.

Remove from Mozilla Firefox (FF)
Open Mozilla Firefox and search for adware signs. If you find some, follow these guidelines to remove all unwanted components:
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
You can easily and effectively get rid of various adware-related objects from Google Chrome. If you need some help, take a look at the below-given guide:
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Arberittertwa.info registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting adware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Josh George. Adware Effects | How Adware Works & Adware Protection. Street Dictory. Relevant Information.
- ^ Denise Ferreira. How Does Adware Hurt My Computer?. Top Ten Reviews.
- ^ Ronnie Sawant. What is pay per click?. Quora.com. Relevant questions and answers.
- ^ Margaret Rouse. Geolocation. Search Mobile Computing. Tech Target.
- ^ Virusai.lt. Virusai.lt. Cybersecurity information and latest news about computer threats.
