Avaddon ransomware (Virus Removal Instructions) - Decryption Steps Included
Avaddon virus Removal Guide
What is Avaddon ransomware?
Avaddon ransomware is file-encrypting virus changing file names to .avdn and spreading via Phorphiex/Trik Botnet
Avaddon is a cryptovirus that has been first spotted by cybersecurity researcher GrujaRS[1] in June 2020. According to experts, this ransomware can be predicted to be exceptionally active as the criminals behind it are applying all kinds of dissemination strategies, including Phorphiex/Trik Botnet, wink spam attacks, Ransomware-as-an-Affiliate (RaaS) for Russian hackers, exploit kits and more.
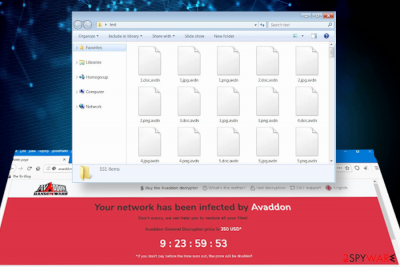
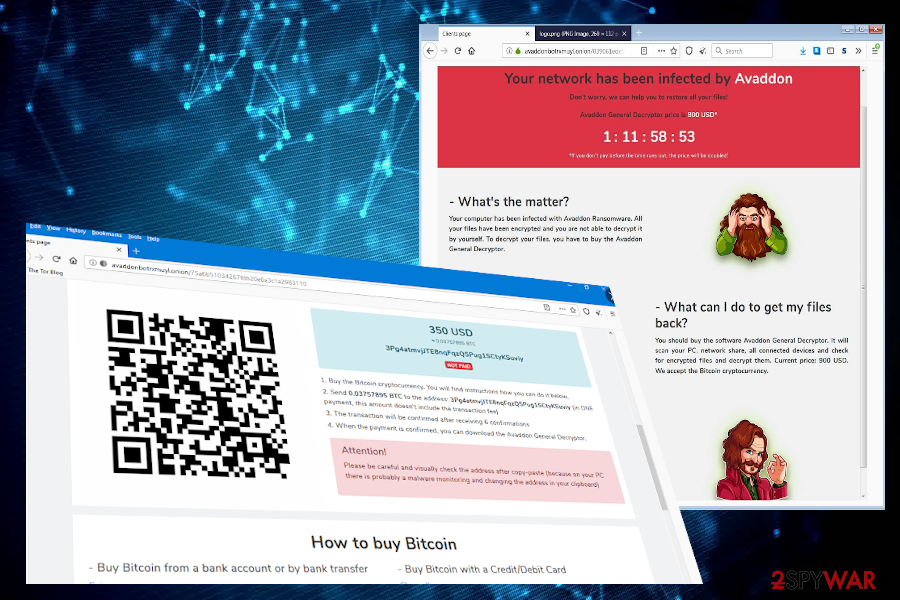
The executable of the Avaddon ransomware (temp27472466.exe or img164186.jpg.js) runs PowerShell and Bitsadmin commands within %Temp% to enable the ransomware. The inbuilt file encryption software scans the machine for compatible file extensions and locks the ones that it successfully recognized by happening the .avdn file extension to each of them. The virus also replaces the desktop background and creates a ransom note [id]-readme.html (instead of the ID, people see the unique identification number), which redirects to the TOR payment site, which demands victims to purchase Bitcoins and pay for the Avaddon General Decryptor 350 USD in Bitcoins.
| Name | Avaddon |
| International classification | Ransomware |
| Distribution | Phorphiex/Trik Botnet, malicious IMG123101.jpg spam attachments, unprotected RDPs, exploit kits, infected software download links, RaaS offered on Russian hacking forums, etc. |
| Related files | temp27472466.exe[2], img164186.jpg.js, sava.exe |
| File extension | The ransomware changes the extension of personal people's files to .avdn |
| Note | As a typical file-encrypting virus, it replaces the desktop background to “All your files has been encrypted” note and generates an HTML file [id]-readme.html |
| Exclusion list | The ransomware is programmed to skip CIS countries by initiating self-destruction |
| The size of the ransomware | It's not static. It can vary from 350 USD to 900 UAS depending on the amount of encrypted data |
| Decryptable? | .avdn files cannot be recovered for free. Experts provided the analysis of the virus and it seems that it's using online IDs that cannot be deciphered without a unique key |
| Elimination | Automatic removal is the only option to get rid of dangerous cyber infection |
| Ransomware may trigger Windows malfunctions by compromising registries, boot files, libraries, and more. To fix suchlike damage, try running FortectIntego utility | |
The Avaddon ransomware virus is a newcomer to the market of crypt-extortionists. Nevertheless, experts see its potential to become a prevalent cyber threat competing with families like GandCrab, Djvu, or Jigsaw. Such presumptions are based on the activity logs and infections rate.
According to the researchers, the campaigns that criminals behind this ransomware show positive dynamics. According to the cybersecurity firm Appriver, the spams distributed via Phorphiex botnet[3] standalone reached over 300 potential victims within a few days. Even more, the ransomware can be spread by affiliate parties, Russian hackers basically, as the Avaddon ransomware virus is being offered as a Ransomware-as-an-Affiliate, paying the affiliate distributors 65% of the ransom.
However, the countries of the former Commonwealth of Independent States (CIS) are not very likely to meet this malware. According to its founders, the virus has an automatic command, which initiates Avaddon virus removal by default if the system detects the AZ, AM, BY, KZ, KG, MD, RU, TJ, UZ, UA, GE, and TM keyboard layout.
The other countries all across the world are at a high risk of getting acquainted with the .avdn file virus. Upon running the malicious sava.exe file, the virus changes the background image and creates a new directory, for example, Z folder. Besides, all personal files are locked using a sophisticated encryption algorithm (AES, RSA, ChaCha or combination) and then launches the [id]-readme.html note, which once clicked launches the TOR website and displays the following instructions:
Your network has been infected by Avaddon
All your documents, photos, databases and other important files have been encrypted and you are not able to decrypt it by yourself. But don't worry, we can help you to restore all your files!The only way to restore your files is to buy our special software – Avaddon General Decryptor. Only we can give you this software and only we can restore your files!
You can get more information on our page, which is located in a Tor hidden network.
How to get to our page
Download Tor browser – hxxps://www.torproject.org/
Install Tor browser
Open link in Tor browser – avaddonbotrxmuyl.onion
Follow the instructions on this page
Your ID:
–DO NOT TRY TO RECOVER FILES YOURSELF!
DO NOT MODIFY ENCRYPTED FILES!
OTHERWISE, YOU MAY LOSE ALL YOUR FILES FOREVER!
The TOR website informs users about the size of the redemption (varies from $350-900) and provides a detailed guide on how to purchase Bitcoins and make the payment. In addition, people can find a support chat, a free Avaddon decryption test page, help page, and similar.
Possible versions of the Avaddon file virus extensions that appear on encoded files
Avaddon ransomware uses the mix of AES and RSA encryption methods, so there are many similarities between this and other threats. But there are particular features that help determine this virus and its versions from other ransom-demanding threats. It is believed that particular creators rely on the random character extensions creation, but we have determined a few particular versions of the malware already.
.e5W7fivNP and .JGHh4eBP8Fd1I
The .e5W7fivNP version was noticed at the start of July 2020. It is known that the threat is spread around using malicious macros and file attachments on email notifications. The second one mentioned – .JGHh4eBP8Fd1I got distributed a few days after. The amount of ransom asked on the sY_readme.html window – $1495. Paying is never a solution. Contents of the note:
Your network has been infected!
Your files are locked due to a vulnerability in your system!
You will not be able to decrypt the files yourself, in the worst case you can destroy the data irreversibly.
The only way to unlock your data is to buy the decryption program.
Go to the link written below to more details.
If you do not pay for recovery, then all the confidential data from your computer WILL BE TRANSFERRED TO PUBLIC ACCESS!
Follow the instructions below to restore your files and keep them confidential.
If you cannot do this yourself, find a data recovery company in internet.
They cannot help you unlock your data, because only we have decryption key, but will help you make a payment and provide you guarantees.
ATTENTION! DATA RECOVERY AGENCIES WORK AND DURING THE CORONOVIRUS QUARANTINE, THEY WILL HELP YOU REMOTE.
Also, I ask you to note, you have no long time, if you do not make payment soon, the price for the decryptor will double. So I recommend you dont waste time and move!
How to get to our page
• Download Tor browser from the official site
• Install Tor browser
• Open link in Tor browser – OZdvQ5.z64nuzgptrb4ujf5.onion/?m9
• Follow the instructions on this page
Your ID:
MjY1LS82ZUZHV1dGZGFMMCswZy9SMW1kZaFaZXR1 [total of 22 characters]
Do not try to recover files yourself!
Do not modify encrypted files!
Otherwise, you may lose all your files forever!
hiscrm3hT5Yg1xZTDDh0bDzCqN50S
.CaWdDadCcE
With the .CaEdDadCcE version the amount demanded was raised up to $2000 in Bitcoins. The version that came out on September 8th in 2020 also came with a ransom note as a text file delivery. The tM1Au_readme.txt message listed the same Avaddon link on Tor browser and payment instructions.
.bdCDdCBaAd
The version that appeared at the start of October carried out the ransom note with a text file named SxgPNwKy_readme_.txt that stated about the further options – paying the Bitcoin transfer via onion link that supposed to go via Tor web browser.
.bbCceaBDEc
A version that appended all the encoded files with .bbCceaBDEc marker asked for payments in a message similar to other versions. The text file named cx3lk_readme_.txt appeared in various folders with encoded files and on the desktop as soon as the encryption process ended.
The particular Avaddon ransomware threat can use various randomized extensions, as you can see. So pay attention to details like avaddonbotrxmuyl.onion link listed as the Tor-URL for the payment transfer and similar images, messages on those text files, and HTML windows.

Naturally, users get a shock finding their files locked by .avdn virus files and that is understandable. Not only the fact that your access to personal files is restricted worries. However, people should also consider the fact that having a ransomware virus on the system leaves it extremely vulnerable to other cyber attacks, for example, the infiltration of Trojan or spyware.
Therefore, it's important to remove Avaddon ransomware as soon as possible. If you found your files locked, do not hesitate and restart the system into Safe Mode to quarantine malicious processes, such as sava.exe. This way, the ransomware won't interfere with your security tool and you will be able to launch a full system scan.
At this point, we recommend people to rely on the most robust security tool, such as SpyHunter 5Combo Cleaner, Malwarebytes, and similar. Beware that not all malicious entries run by this ransomware can be detected. Take for instance a malicious img164186.jpg.js file, which is recognized by 35 AV tools out of 65 possible. Thus, using a weak security program can end up with a failed Avaddon removal.
A multiplicity of methods are applied for spreading the ransomware all across the world
According to the researchers, this particular ransomware stands out from the crowd as its developers are spreading the ransomware in an extremely active way. The criminals themselves are using one basic dissemination strategy, known as spam.
The email messages that carry malicious attachments are being distributed by Phorphiex/Trik Botnet, which is a huge campaign capable of spreading hundreds of thousands of emails at a time (over 300,000 ar once). The details of the malicious email are the following:
- the sender – billy73@3189.com (though it can differ)
- Subject line – “Your new photo?”
- Body text – a winking emoji
- Attachment – IMG123101.jpg
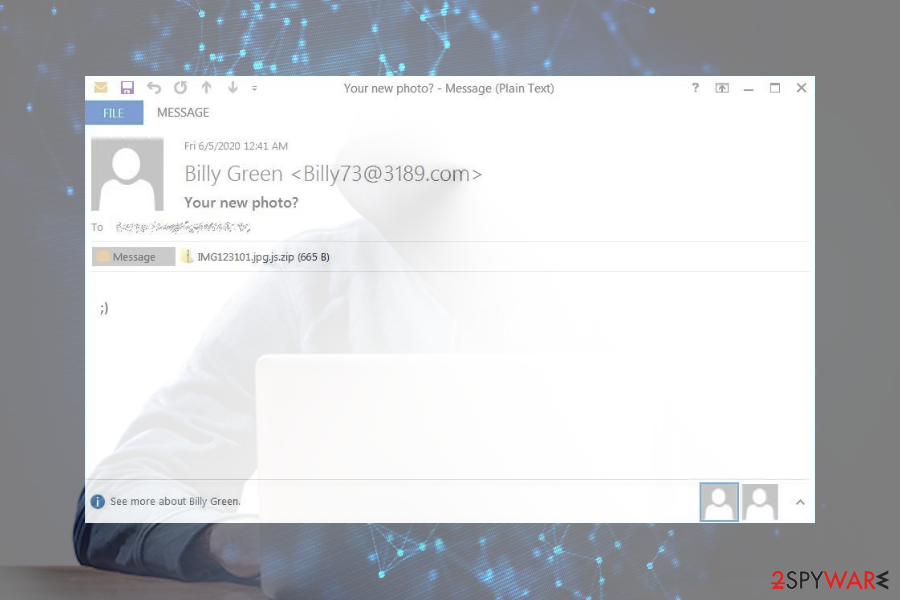
The jpg attachment is, in fact, a malicious JavaScript file, which once opened downloads a malicious ransomware payload. Nevertheless, this particular virus can be distributed via other means. That's because it is offered as a RaaS, Ransomware-as-a-service, meaning that the developers of this virus are not the only ones distributing the malware. According to NoVirus.uk[4] researchers, the affiliates can render their own means of distribution to infect PCs and then collect commissions for every paid ransom fee. The other means that can be used for spreading this tool:
- Links embedded into spam emails
- Software vulnerabilities and exploit kits
- Pirated software installers
- Keygens, software cracks
- Fake Flash Player (or similar) updates
- Freeware bundles shared on shady websites
- Poorly protected Remote Desktop connections, etc.
Avaddon virus ransomware removal and .avdn file recovery
As we have already mentioned in the first part of this article, the Avaddon ransomware removal can be initiated in one way only – using a professional security program that has the latest virus database, powerful scanner, and virus removal possibilities. Our recommended programs are Malwarebytes and SpyHunter 5Combo Cleaner, but you can use any application of your preferences.
If, however, you cannot remove Avaddon virus from the system because it infringes the AV engine and keeps it disabled all the time, restart Windows OS and boot it into Safe Mode with Networking. This way, all malicious processes will be disabled and you will be able to start the security scan.
Once the ransomware is removed, you can start thinking about the recovery of the .avdn files. As pointed out by cybersecurity experts, there's no free decryptor for this virus. Therefore, you should select if you are going to pay the ransom (not recommended), use backups, or apply alternative data recovery methods listed below.
Getting rid of Avaddon virus. Follow these steps
Manual removal using Safe Mode
Safe Mode environment is required for a successful ransomware elimination.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Avaddon using System Restore
If you cannot enable Safe Mode for some reason, you can try to get rid of malicious ransomware files by enabling the System Restore point that has been created before the Avaddon ransomware attack.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Avaddon. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Avaddon from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.The methods that can be used to unlock .avdn virus files
If your files are encrypted by Avaddon, you can use several methods to restore them:
Data Recovery Pro
This third-party software can ransomware victims retrieve at least some of the encoded files for no charge.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Avaddon ransomware;
- Restore them.
ShadowExplorer may be of use for those who cannot rename .avdn files without paying the ransom
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Unfortunately, there's no free Avaddon decryptor launched
Even though there's no decryptor for this malicious virus, do not rush to pay the ransom. Make cold copies of the encrypted files and upload the sample of the virus to the websites owned by ransomware researchers.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Avaddon and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ GrujaRS @GrujaRS. Twitter. Social network.
- ^ emp27472466.exe. VirusTotal. Free URL and file scanner.
- ^ David Pickett. Phorphiex/Trik Botnet Campaign Leads to Multiple Infections - Ransomware, Banking Trojan, & CryptoJacking. Appriver. Cybersecurity, Productivity and Compliance Solutions.
- ^ Security and spyware news. NoVirus. Virus and spyware news.





















