AXLocker ransomware (virus) - Free Instructions
AXLocker virus Removal Guide
What is AXLocker ransomware?
AXLocker is a malicious program that locks peoples' files for the money extortion purposes
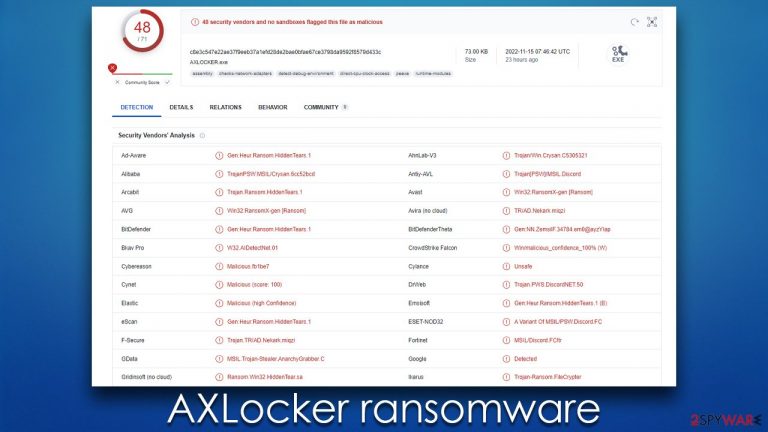
AXLocker is a ransomware-type program that stealthily enters users' computers to perform various malicious tasks, although the most distinctive one of this kind of malware is to lock all personal files. Suchlike files would be locked with a sophisticated encryption algorithm, making the data unrecognizable to a computer. Unlike many ransomware, this one would not append any extensions to the files, and they would also keep their original icons.
Photos, videos, documents, databases, etc., would be unreachable from this point on, and users would only receive a Windows error whenever they try to open any of the files. In order to retrieve access, victims are required to apply a unique key that is held on cybercriminals' servers. In a pop-up window that is delivered right after the encryption,[1] crooks claim that people need to send an email to anoynmous.axo@proton.me to attempt to file restoration.
Of course, this service is not free, and it's the main modus operandi of any ransomware gang – holding files hostage so that users would oblige and transfer money as bitcoin. We recommend avoiding any communication with the attackers and instead following the instructions below on removing AXLocker locker ransomware and attempting to restore data using alternative methods.
| Name | AXLocker virus |
|---|---|
| Type | Ransomware, data locking malware, cryptovirus |
| File extension | The extension is not added (file names remain the same) |
| Ransom note | A pop-up window |
| Contact | anoynmous.axo@proton.me |
| File Recovery | If no backups are available, recovering data is almost impossible. Nonetheless, we suggest you try the alternative methods that could help you in some cases – we list them below |
| removal | Before proceeding with data recovery solutions, make sure you first scan your system with SpyHunter 5Combo Cleaner, Malwarebytes or another reputable anti-malware software |
| System fix | Malware can wreak havoc on Windows systems, causing errors, crashes, lag, and other stability issues even after it is terminated. To fix the operating system, we recommend scanning it with the FortectIntego repair tool. |
The ransom note
A ransom note is one of the crucial elements of any ransomware attack. Cybercriminals often provide the most vital information that would provide them a possibility to receive ransoms – contact details. Usually, ransomware authors use highly anonymous email providers to avoid being detected by authorities, it is no exception here. Likewise, cybercriminals asked to be paid in bitcoin in 99% of the cases, although other cryptocurrencies may also be used occasionally.
While the AXLocker virus authors do not provide details on how much they would want to be paid, it can range anything from a few dozen to a few thousand dollars. Here's the full message that's delivered upon the infection:
WARNING!!
Private key will be deleted in:Your documents, photos, databases and other important files have been encrypted with strongest encryption and unique key, generated for this computer. Private decryption key is stored on a secret Internet server and nobody can decrypt your files until you pay and obtain the private key. The server will eliminate the key after a time period specified in this window.
Warning!!
1. Do not turn off the ransomware, if you do so the private key will be deleted.
2. Do not turn off the computer.How can i decrypt my files?
Send email to: anoynmous.axo@proton.me with your personal id
Once you will send the email you have to wait 48 Hours
After 48 Hours we will send you a decryption program with your decryption keyYour unique personal ID:
Within the pop-up window, victims are also presented with a timer that signifies the time users have before their key is allegedly deleted, removing all the possibilities of data recovery. While this may or may not be true, we do not recommend communicating with the attackers, as they may simply be lying and never provide the requested decryption tool, even after the money is transferred to them.
Following the instructions below can guarantee you won't have to face the risks of losing your money to hackers, although data recovery might be difficult, if not impossible. Proceed with the steps below.
Removal of malware
The first task when dealing with a malware attack is making sure that all its components and malicious files are removed effectively. However, as long as AXLocker can communicate with the attackers via networked connections, it is not safe to do so. Cybercriminals can send various commands via the established connection to their Command & Control[2] server, and this communication must be severed. To do this, please follow these steps:
- Type in Control Panel in Windows search and press Enter
- Go to Network and Internet

- Click Network and Sharing Center

- On the left, pick Change adapter settings

- Right-click on your connection (for example, Ethernet), and select Disable

- Confirm with Yes.
Some ransomware has a self-destructive tendency after encrypting data, but not always. For example, it often spreads with other malware, like data stealers or keyloggers.[3] Therefore, removing all malware components at once is crucial. The simplest approach uses powerful anti-malware software – it can locate all malicious components and then remove them securely. We recommend employing SpyHunter 5Combo Cleaner or Malwarebytes for that; if ransomware is interfering with the removal process, we recommend accessing Safe Mode and performing the removal steps then:
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing the F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on the Start button and select Settings.
- Scroll down to pick Update & Security.
- On the left side of the window, pick Recovery.
- Now scroll down to find the Advanced Startup section.
- Click Restart now.
- Select Troubleshoot.
- Go to Advanced options.
- Select Startup Settings.

- Click Restart.
- Press 5 or click 5) Enable Safe Mode with Networking.
In addition to ensuring the malware is gone from your system, we also recommend verifying that the Windows system hasn't sustained any damage. Ransomware (and other malware) can compromise system files when installed, which often causes more problems even after removal.
If your computer is experiencing any stability issues, such as DLL missing errors or Blue Screen of Death crashes, you may need to use a PC repair tool to fix the damaged files. We recommend using FortectIntego PC repair tool, which is excellent software for dealing with all sorts of malware-related and unrelated computer issues.
Restoring files
Unfortunately, removing AXLocker ransomware from the system would not return your files back to normal. Upon entering a system, the virus encrypts all files on it and then generates a unique ID that is then sent to cybercriminals. At the same time, a unique key is generated, which is also delivered to ransomware authors.
Victims can then pay to the attackers to retrieve the key, which would not work for any other victims. As we already explained, communication with cybercriminals should not be considered a real option, as it may end up really badly – although it is always your choice what to do next.
Below you will find alternative methods for data recovery, although keep in mind that they may not be effective. Still, we recommend trying them. Before proceeding, make sure you copy all the encrypted files onto a separate medium for a backup, as attempting to restore them may end up in data corruption.
- Download Data Recovery Pro.
- Double-click the installer to launch it.

- Follow on-screen instructions to install the software.
- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders which you want the files to be recovered from.

- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.

- Press Scan and wait till it is complete.

- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.
Decryption tools might also be created for certain ransomware strains thanks to the efforts of security researchers. In some cases, law authorities seize the servers of malicious actors, which allows the keys to be released by the public – reputable security vendors usually do this. Here are a few links you might find helpful:
- No More Ransom Project
- Free Ransomware Decryptors by Kaspersky
- Free Ransomware Decryption Tools from Emsisoft
- Avast decryptors

How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Encryption. Investopedia. Sharper insight, better investing.
- ^ Command and Control [C&C] Server. Trend Micro. Security blog.
- ^ Keystroke logging. Wikipedia. The free encyclopedia.
