Bestanimegame.com ads (Tutorial) - Chrome, Firefox, IE, Edge
Bestanimegame.com ads Removal Guide
What is Bestanimegame.com ads?
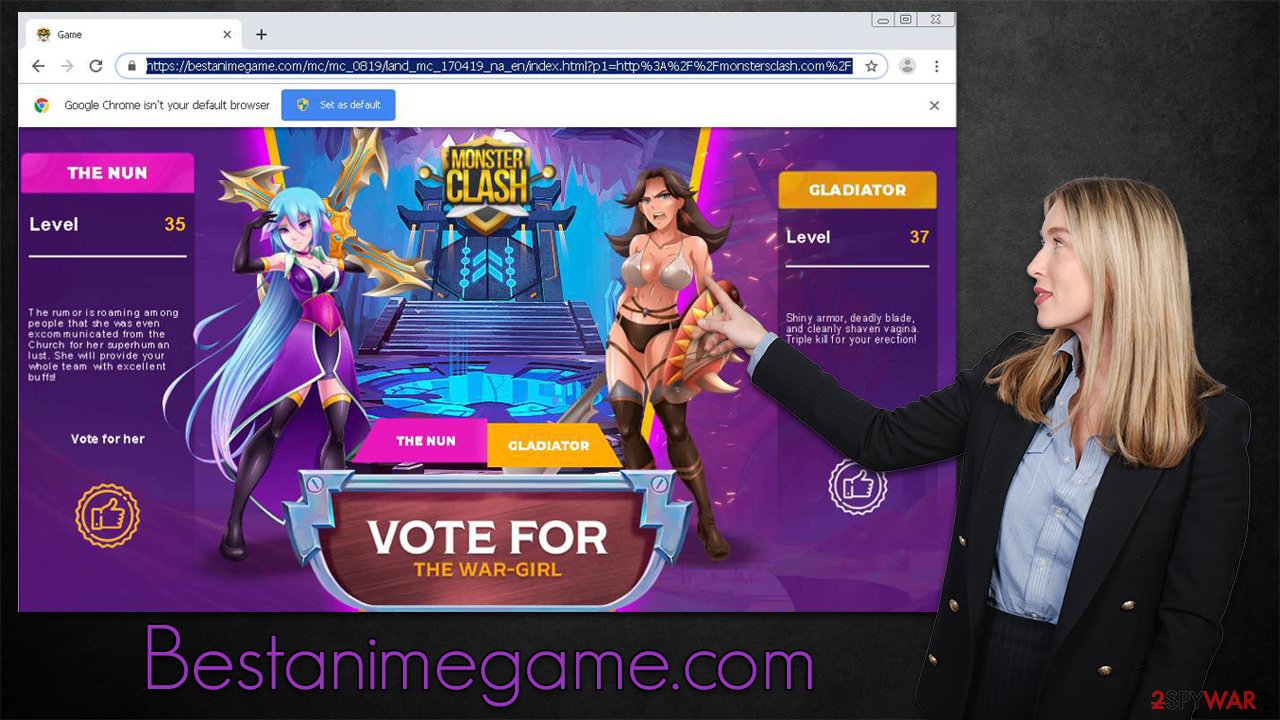
Bestanimegame.com is a potentially dangerous website that shows misleading ads

Bestanimegame.com is a website you might encounter while browsing the web on your Google Chrome, Mozilla Firefox, MS Edge, or another web browser. While some users might visit the page willingly for one reason or another, most people get redirected there from somewhere else. This usually happens after clicking a deceptive link on another website, such as illegal video streaming, torrents, X-rated, etc.
As soon as people enter, they are asked to vote for “the war-girl,” and are shown anime characters in the middle. The problem is that this website is not safe to interact with, as users might be easily redirected to even more dangerous places. When clicking links or even empty spaces on such sites, users can be taken to phishing, spoofing,[1] and other scam material online. Likewise, people might be asked to download potentially unwanted or dangerous software.
Bestanimegame.com redirects might also indicate that the computer has been infected with adware[2] or other potentially unwanted programs. These apps are not usually installed intentionally, so many might not even be aware that they are causing unwanted redirects. Some malware might also initiate suspicious browser behavior and an increased number of ads everywhere, so if you are experiencing these symptoms, it is time to take action sooner than later.
Below, we will provide all the information needed to check the system for unwanted programs and other infections and provide tips on avoiding them. Ultimately, the process should help you to get rid of the redirects to Bestanimegame.com or similar annoying websites.
| Name | Bestanimegame.com |
|---|---|
| Type | Adware, redirect virus |
| Distribution | Software bundles, redirects from other websites, malicious ads |
| Symptoms | Unknown extension of program installed on the browser or system; intrusive ads; redirects to potentially dangerous websites; altered search results and sponsored links, etc. |
| Dangers | Redirects to malicious websites can result in unwanted site notifications, personal information disclosure to unknown parties (cybercriminals), monetary losses, installation of other potentially unwanted programs/malware |
| Elimination | You can remove potentially unwanted programs manually, although you should also perform a full system scan with SpyHunter 5Combo Cleaner to ensure no malicious programs are running in the background |
| Other tips | Cleaning web browsers is one of the secondary things you should do after PUP/malware removal to secure your privacy. You can use FortectIntego to do it quickly |
It is important to note that the internet is very vast – more than a billion websites exist at any given point in time. Most sites are created to be useful or informative, while others aim to harm visitors in one way or another for monetary gains (in most cases, at least). It is true that the number of dangerous websites drastically decreased over the years thanks to regulations that were put in place by tech and security companies such as Google or Microsoft.
Nonetheless, due to the immense size of the internet, it is impossible to segregate all the malicious content online, especially if it is being accessed through less secure search providers, browsers, and other elements used to browse the web. However, redirects that can occur when visiting a random website are by far the most common reason why so many users end up on websites such as Bestanimegame.com.
Once users are redirected, they might easily be caught off guard by the content that is presented to them. Automatic scrips might result in further rerouting, which, in some cases, might result in malware infections without user interactions (this usually happens when users have unpatched software installed on their devices, and vulnerabilities can be exploited).
Thus, it is important to ensure that security software, such as SpyHunter 5Combo Cleaner or Malwarebytes, is running in the background at all times. It is especially important not to ignore warnings from anti-malware tools, as it is one of the main reasons why users get infected in the first place. Ad-blockers can also serve as a great security measure, although there are a few negative aspects associated with these tools – denying websites ad revenue is among the most criticized ones.
Adware removal and system remediation
If you have accessed Bestanimegame.com either intentionally or not, it does not automatically mean that your system is infected. Interactions with ads on the page, downloads, and similar actions could, however, result in various security and privacy issues. Likewise, as we already explained, adware could be the primary reason why you ended up on a malicious website in the first place.
Get rid of the extensions
The developers of adware and browser hijackers have been using extensions to produce ads for years now. This is why, if you encounter suspicious browser behavior, you should first check the section for the extensions and remove everything you don't recognize. If you need help with that, please follow the steps below.
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the window's top-right).
- Select Add-ons.
- In here, select the unwanted plugin and click Remove.
![Remove extensions from Firefox Remove extensions from Firefox]()
MS Edge (Chromium)
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.
![Remove extensions from Chromium Edge Remove extensions from Chromium Edge]()
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
Uninstall programs
In more rare cases, adware might be disguised as a seemingly useful app. For example, media players or file converters might be a reason why you see pop-up ads outside your browser as well. However, it might not always be so clear which precise program is causing the issue, especially if there are a lot of them installed on the compromised device. If you are not sure about this step, follow the steps below to uninstall everything suspicious on your Mac or Windows computer.
Windows
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.
![Uninstall from Windows 1 Uninstall from Windows 1]()
- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.
![Uninstall from Windows 2 Uninstall from Windows 2]()
Mac
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)
![Uninstall from Mac 1 Uninstall from Mac 1]()
To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
![Uninstall from Mac 2 Uninstall from Mac 2]()
Clean your browsers
It is important to clean your browsers after the elimination of potentially unwanted applications to prevent data tracking via cookies[3] and other technologies. These tiny items are stored locally and might remain even after you uninstall adware. The quickest way to do so is by employing FortectIntego PC repair and maintenance tool, although manual instructions are also available:
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.
![Clear cookies and site data from Firefox Clear cookies and site data from Firefox]()
MS Edge
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.
![Clear browser data from Chroum Edge Clear browser data from Chroum Edge]()
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
Other security tips
Adware is deceptive when it comes to not only its operation but also distribution, thus it is important to talk about it. It is clear that most users would not risk their security or privacy by installing programs they deem to be unsafe. Unfortunately, many people are unaware of the full extent of some apps' actions, as these can only be observed once they are installed.
Thus, in order to avoid installing programs that could cause issues in the future, you should be very careful when installing apps from unknown sources. For example, you might encounter a pop-up message saying that your computer is infected and viruses need to be removed or that Flash Player needs to be updated. Always ignore these alerts, as they are fake – you will end up installing PUPs or other malicious software on your system.
Another popular delivery method for the adware that could cause Bestanimegame.com ads and redirects is software bundling. When dealing with freeware installers, keep in mind that they might include optional applications inside, so your job is to find these offers and decline them. We recommend checking pre-ticked checkboxes, misleading button placements, and fine print text. Choosing Advanced over Quick mode would also drastically reduce the possibility of extra program installation.
The most important part when dealing with bundles is not to rush the process, as this is precisely what the distributors are counting on – lack of attention. Security tools can also warn you about dangerous programs, so make sure anti-malware is constantly running in the background.
How to prevent from getting adware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Website spoofing. Wikipedia. The free encyclopedia.
- ^ Will Kenton. Adware. Investopedia. Source of financial content on the web.
- ^ What are cookies? | Cookies definition. Cloudflare. The Web Performance & Security Company.












