BitRAT malware (Removal Instructions) - Virus Removal Guide
BitRAT malware Removal Guide
What is BitRAT malware?
BitRAT malware is the RAT-type intruder that can be designed to collect keystrokes and audio or video on the targeted computer

BitRAT malware is the cyber infection that is set to provide remote access to various devices. The RAT can have various functionalities and infect the machine to perform different activities. Hackers distribute the threat to access, view, and modify various files, execute commands, and download other programs or data from the internet. The virus can also initiate remote access to the desktop, so malicious attacker directly controls the machine.
This BitRAT virus was spotted promoted and old in various hacker forums and other platforms. It is promoted as a hacking tool, so cybercriminals might take advantage of the silent infiltration techniques and purchase the virus to affect targeted machines. Developers of the trojan copied various open-source[1] projects. They managed to make a low-effort malware that can cause trouble on the machine without particularly causing any symptoms for the user to see. You need to rely on tools created for malware detection and a few tricks that the guide below explains so the AV tool is working properly.
| Name | BitRAT malware |
|---|---|
| Type | Trojan/ Info-stealer malware/ RAT |
| Issues | The program can be set to gather information, record keystrokes, videos, took screenshots. The virus may infect the machine with other viruses |
| Damage | Silent infiltration allows the malware to run for a longer time, so users' passwords, login credentials, other personal details get recorded |
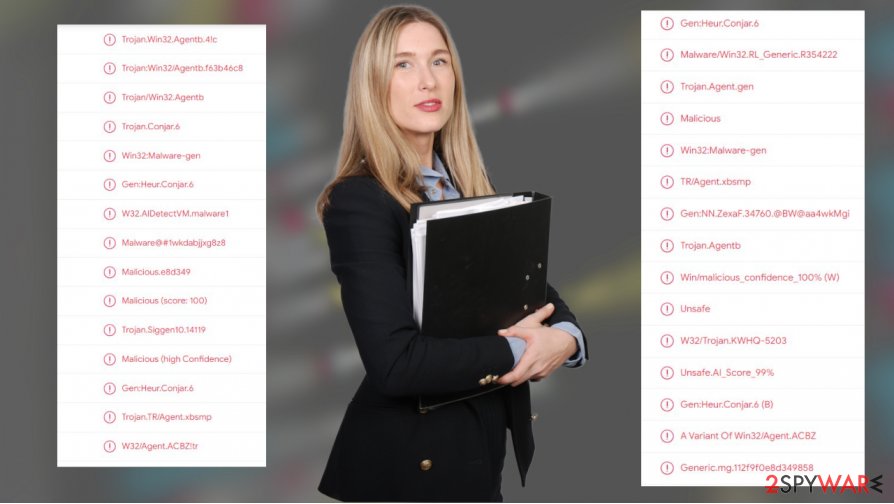
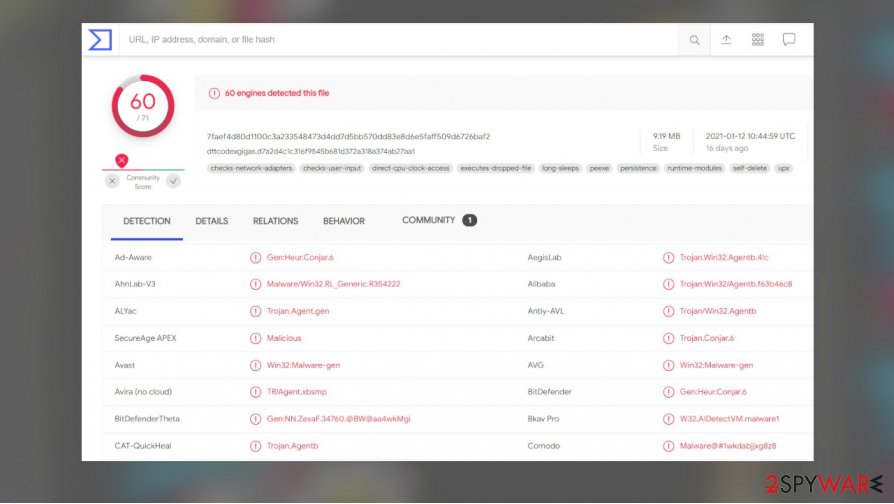
| Possible detection names | Win32:MalwareX-gen, Variant Of Win32/Agent.ACBZ HEUR:Backdoor.Win32.Agent.gen |
| Distribution | Files with malicious code can be spread around using malicious macro filled email attachments, links to malware sites |
| Elimination | You need to remove BitRAT malware using proper anti-malware tools |
| Repair | Make sure to recover the damage that malware made with tools like FortectIntego |
BitRAT malware can be set to access a web camera, microphone and take screenshots, photos, record you and your background. It can also trigger certain system changes, so the malicious process, file, or program is launched every time the device is launched. Issues with the computer can lead to permanent data loss, damage, or errors like BSOD.[2]
Developers of this threat promote the infection online. They claim that BitRAT malware controls the infected machine and collects various inputs or even streams the microphone material, webcam recordings in real-time. RAT can also use various files and processes to run on resources of the machine so cryptocurrency can be generated or other viruses installed.
If the threat is set to steal information, BitRAT malware removal is crucial and needs to happen as soon as possible. The more time this malware has on the PC, the more information can be exfiltrated, so collected information gets used by criminals. Those personal details that can be obtained are extremely valuable on the internet, especially on the dark web.
BitRAT malware can trigger chain infections and execute downloaded files to spread malware, extract login credentials, passwords, usernames. According to promotions, this threat can steal data from 35 different browsers and 500 additional programs. The virus may record keystrokes, so once it is installed, it becomes extremely dangerous to login to any site or social media platform, banking page.
BitRAT malware and other RATs often are sued to obtain login credentials, passwords, and usernames for particular cryptocurrency wallets, banking sites, online platforms, social media. Malware can access:
- name;
- address;
- telephone number;
- email;
- banking account credentials;
- credit card numbers.
If you don't remove BitRAT malware as soon as possible or don't use proper tools like SpyHunter 5Combo Cleaner or Malwarebytes to terminate the infection fully, you might suffer from the attack directly targeted at you or a more in-depth blackmailing campaign. The infection can be detected[3] with many popular AV tools, so it possible to get rid of the trojan.
It is clear that the virus is new and freshly developed. It can function as cryptomining software and damage the machine nonetheless. Some of the functions are not running smoothly or none at all, but BitRAT virus can lead to various issues with the machine. To avoid further issues, make sure to repair any issues with FortectIntego or similar tools, repair any files or functions and terminate pieces of related malware.
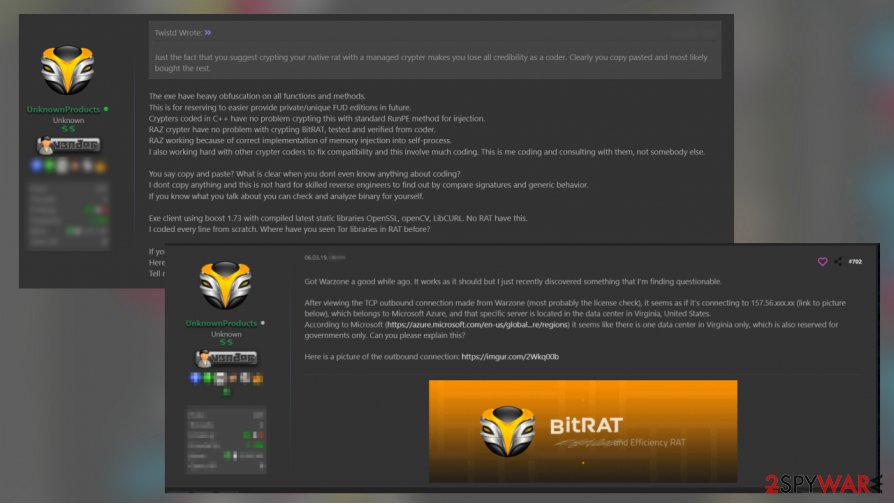
If you suspect that malware is already on your machine, do not hesitate. BitRAT malware should be deleted as soon as possible. It is linked with other RAT named Warzone, so clean the machine thoroughly to avoid repetition of the infection. The code also shows other resemblance, so analysis can confirm that this is a copy-paste threat that is not critical, but it can evolve in the future.
Quick infection spreading methods
Malicious programs like this can be distributed silently, so users do not notice anything until the malware is running its processes. Illegal activation tools, fake updates, promoted applications, and software license versions downloaded from peer-to-peer services can lead to the installation of such malicious code. It also can happen during insecure installation of freeware, when the additional programs have scripts triggering malware downloads.
Another method includes documents, PDFs, excel sheets that contain malicious macros. Such malicious files can be added to emails directly or attached as additional content to notifications that resemble emails from companies and government officials. There are various companies that malware creators use as bait for victims.
Malware files can be in a variety of formats, so any executables, archives, Microsoft Office, and PDF documents should be suspicious. Especially attached to emails that you were not expected to receive. It is enough to open such infectious files, and macros get triggered by a single press of the button. Be careful when suspicious emails come with files or links.
Particular threats like RATs can be distributed online as products for spying on victims. There are many forums and marketplaces for such software, so malicious actors can target you. Run anti-malware tools more often to avoid any silent infections.
Make sure to terminate the BitRAT virus from the system once and for all
BitRAT malware virus is a threat that can be added to various spam email messages presented via malicious links in those notifications or attached as files to the message itself. You cannot be sure when or how the threat appeared on the machine, but time is crucial in this case. The longer this malware has on the PC, the more permanent damage can be done.
Make sure to run a tool like SpyHunter 5Combo Cleaner or Malwarebytes, rely on your anti-malware application, and fully check the system so the BitRAT malware removal can be performed. You can't find the threat manually because it is not a program that waits on the desktop. You might find other programs or suspicious processes, but those are only pieces of the infection, not the main RAT.
When you remove BitRAT malware yourself, you might have a difficult time when AV tools get blocked by the trojan. Enter the Safe Mode before you launch the security tool. This way, your anti-malware program checks all the parts of the system uninterrupted. Then you can run a tool like FortectIntego – system repair app that fixes the damage of the virus and ensures that you can use the machine afterward.
Getting rid of BitRAT malware. Follow these steps
Manual removal using Safe Mode
You might benefit from Safe mode with networking when the AV tool gets blocked by BitRAT malware virus
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove BitRAT malware using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of BitRAT malware. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from BitRAT malware and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting malware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Catalin Cimpanu. Malware gangs love open source offensive hacking tools. ZDNet. IT and security news.
- ^ Blue Screen of Death. Wikipedia. The free encyclopedia.
- ^ Virus detection rate. VirusTotal. Online malware scanner.





















