Bostewsom.shop ads (Free Instructions)
Bostewsom.shop ads Removal Guide
What is Bostewsom.shop ads?
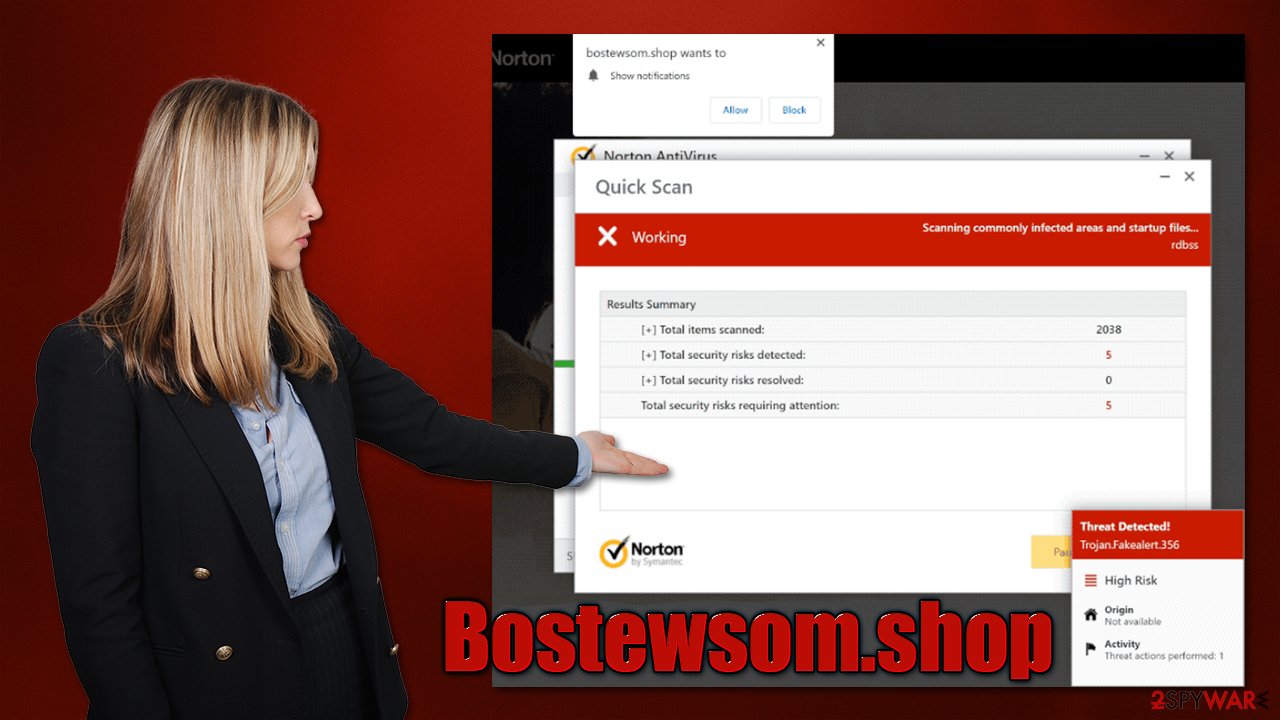
Bostewsom.shop is a fake website that tries to imitate Norton security scans

Bostewsom.shop is a deceptive site you might encounter when browsing the web while using Google Chrome, MS Edge, or another web browser. You are likely to be redirected to this site after clicking a suspicious link somewhere else or after being rerouted by an automatic script. In some cases, redirects could also be caused by adware infections.
How the scam works
Users who enter the Bostewsom.shop website are immediately presented with an alleged system scan that reminds anti-malware program operation. Usually, the site imitates Norton or McAfee security applications to make the phishing attempt more believable.
Just a few seconds later, visitors would be told that their system had been infected with five viruses and that they needed to be removed immediately. The message would also claim that a security software subscription has expired and that it needs to be renewed in order to delete the allegedly found infections.
Bostewsom.shop is just a scam, and you shouldn't interact with it. The main goal of scammers is to profit from pay-per-install schemes, as well as advertisement benefits. Besides, the offered software might not even be legitimate, so you risk installing malware on your system.
| Name | Bostewsom.shop |
|---|---|
| Type | Scam, phishing, adware, redirect virus |
| Goal | Make people provide personal information, subscribe to useless services, download malicious software or subscribe to push notifications |
| Distribution | Redirects from other malicious websites, adware |
| Risks | Financial losses due to fake subscriptions; redirects to other malware-laden, scam websites; installation of potentially unwanted or malicious software |
| Removal | Do not interact with links or other content of a scam site. Instead, check your system with SpyHunter 5Combo Cleaner security software |
| Other tips | Do not forget to clean your browsers properly to avoid the return of ads and further data tracking. You can also repair damaged system files with FortectIntego |
The scam message
Online fraud is extremely profitable, and scams that abuse users' fear and lack of knowledge about how computer viruses work ad unsurprisingly effective. According to various calculations, users lose millions of dollars to tech support and similar scams due to the inability to distinguish real danger from fake notifications and phone calls by scammers.
Social engineering tricks such as the usage of familiar names in cybersecurity are also not new. It gives people the reason to believe these scams, making them feel like they are legitimate – Bostewsom.shop is a prime example of this behavior (there are plenty of identical websites that produce the same message – Performdevelopedgreatlythefile.vip, Bluecodemc1.club, Defender-scan.xyz, and many others). Here's the message you might expect to see:
Norton Security
Your PC is infected with 5 viruses!
ACTION REQUIRED!
Your Norton Subscription Has Expired!
Renew now to keep your pc protected.
If your PC is unprotected, it is at risk for viruses and other malware.
Without a doubt, this message is fake and so are all the claims about virus infections. No website can identify whether or not your system is infected (unless malware is already installed on your system), so all the claims that your computer has viruses are fake, even if it seems like that message is coming from a legitimate source.
What happens after you enter Bostewsom.shop or a similar website
Many users get frightened after they get redirected to a scam website that displays misleading virus detection messages. Those who believe them, end up contacting fake tech support, where they are scammed out of their money. In order cases, people are aware that the message is not real, although they aren't quite sure whether their device is secure now that they entered the site in the first place.
If your system was not infected before you accessed Bostewsom.shop, it would likely remain so as long as you don't interact with the site's contents or download suspicious files. Just to be secure, you should always ensure that all your applications and the operating system are updated to the latest versions to avoid exploitation of software vulnerabilities.[1]
Check your system for infections
While it is unlikely for you to be infected with malware by just entering a phishing website, we strongly recommend you check your system regardless, as there could be adware[2] hiding on it. The easiest way to do this is by performing a full system scan with SpyHunter 5Combo Cleaner, Malwarebytes, or another reputable anti-malware software.
Alternatively, you could check for unwanted programs yourself, although keep in mind that this process might not always be successful, as you may miss some files or other components. This is especially true when it comes to malware. Checking for installed applications could help you remove PUPs installed on the system level:
Windows
- Enter Control Panel into the Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.
![Uninstall from Windows 1 Uninstall from Windows 1]()
- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.
![Uninstall from Windows 2 Uninstall from Windows 2]()
Mac
While moving apps into Trash is how you delete most normal applications, adware tends to create additional files for persistence. Thus, you should look for .plist and other files that could be related to the virus. If you are not sure, skip this step entirely.
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)
![Uninstall from Mac 1 Uninstall from Mac 1]()
To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
You should also check browser extensions and remove them all if you aren't sure which ones are potentially causing unwanted redirects. After that, you should also clean your browsers and system with FortectIntego – it would remove leftover files that could otherwise result in prolonged data tracking[3] and the return of some advertisements.
Disable push notifications
Upon entering the site, you might also be asked to enable push notifications upon entering the site. If you hit the “Allow” button within the prompt either intentionally or not, you would later be spammed with annoying pop-ups – they would come at any point when the browser is operating, regardless if it is being actively used or not.
Bostewsom.shop ads may bring all sorts of misleading and malicious content right to your desktop. Security software won't get rid of them, as the web address needs to be blocked via browser settings manually.
Getting rid of Bostewsom.shop ads. Follow these steps
Stop browser notifications
Remove unwanted notifications from Google Chrome (desktop):
- Open Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate Privacy and security section and pick Site Settings > Notifications.

- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.

Remove unwanted notifications from Google Chrome (Android):
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).

Remove unwanted notifications from Mozilla Firefox:
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.

- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.

Remove unwanted notifications from Safari:
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.

Remove unwanted notifications from MS Edge:
- Open Microsoft Edge, and click the Settings and more button (three horizontal dots) at the top-right of the window.
- Select Settings and then go to Advanced.
- Under Website permissions, pick Manage permissions and select the URL in question.

- Toggle the switch to the left to turn notifications off on Microsoft Edge.

Remove unwanted notifications from MS Edge (Chromium):
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.

Remove unwanted notifications from Internet Explorer:
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.
- Locate web address in question under Allowed sites and pick Remove.

How to prevent from getting adware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Thomas Holt. What Are Software Vulnerabilities, and Why Are There So Many of Them?. Scientific American. Science Magazine.
- ^ Adware. Wikipedia. The free encyclopedia.
- ^ Third-Party Tracking: Cookies, beacons, fingerprints and more. Our Data Our Selves. Tactical Tech.













