Browse Safely hijacker (virus) - Removal Guide
Browse Safely hijacker Removal Guide
What is Browse Safely hijacker?
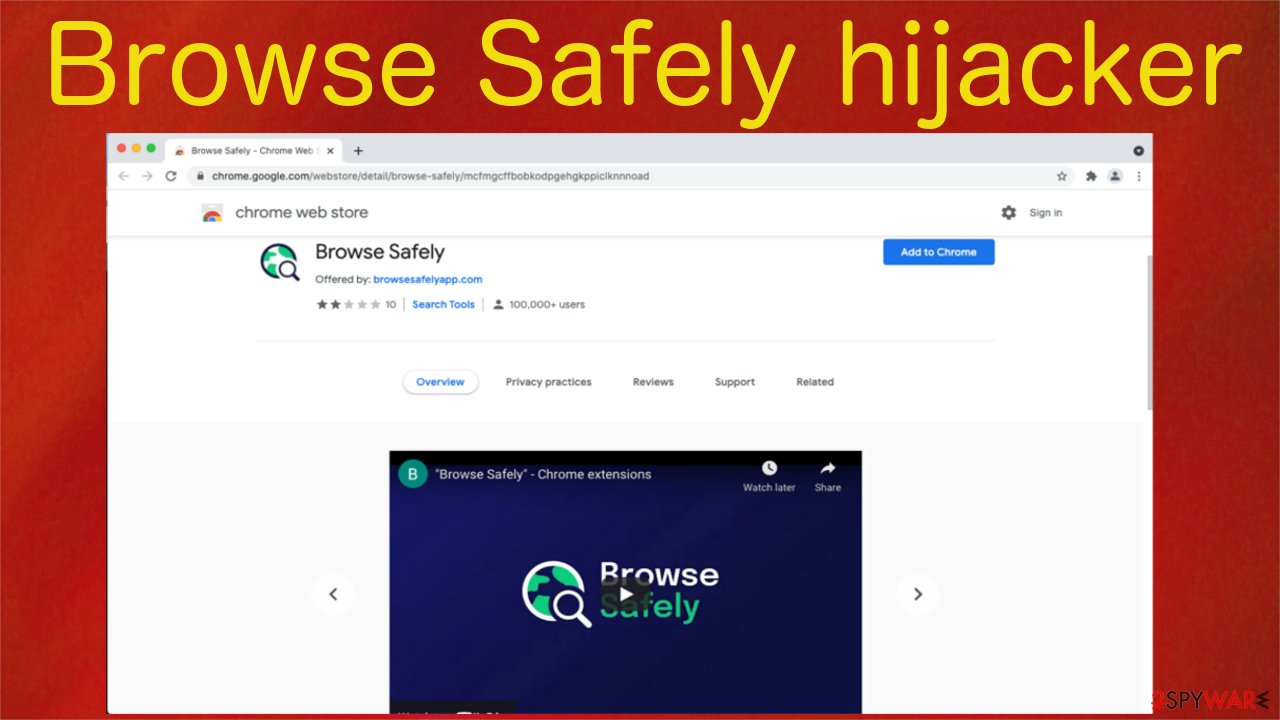
Browse Safely – a browser hijacker that records your online browsing activities

Browse Safely is categorized as a potentially unwanted program[1] due to the many shady functions that it executes when it's installed on a device. We highly recommend not using this browser hijacker as it may endanger your safety and privacy. If it ended up on your device out of the blue – remove it immediately.
First of all, this PUP changes default browser settings by appointing its fake search engine as your default search provider, which continuously changes the homepage and new tab preferences. When you type in a search inquiry, it's redirected through a chain of questionable websites.
That enables Browse Safely hijacker to fill the presented search results with its affiliated websites' deceptive ads and collect browsing-related details (non-personal information).[2] The gathered details are used to make adverts irresistible to you by customizing them by your recent searches, geolocation, visited sites, etc.
The browser extension is advertised to show WoT (Web of Trust) rankings on sites when you type their addresses in the URL bar. In fact, you might be redirected to various treacherous websites that paid the most to advertise through this shady tool. The developers themselves state that:
Despite the convenience and the time saved by the autocomplete suggestions from your Chrome browser’s address bar, not all the website URLs popping up in the autocomplete will necessarily lead you to a safe destination with appropriate content.
Therefore other cybersecurity specialists,[3] and we don't recommend using Browse Safely extension as it may only cause privacy and security issues. Since it can be spread through software bundles, it might end up on your device out of the blue if you're not attentive when installing new software.
Whether you installed this potentially unwanted program willingly or unknowingly, this article will help you to remove it from your computer once and for all. We'll also show you how to restore your default browser settings that were altered by the intruder and repair system-related irregularities.
| name | Browse Safely |
|---|---|
| Type | Browser hijacker, redirect virus, PUP |
| Infection symptoms | Default search engine, new tab, and homepage preferences on your browser are modified; search results contain questionable ads; redirects to shady websites; slower browsing speed |
| Appointed search engine | browsesafelysearch.com |
| Dangers | Privacy issues, malware infections, monetary losses |
| Distribution | Official website, Google Chrome Web Store, software bundling |
| Elimination | To completely remove a browser hijacker from your device, you must use a reliable security tool |
| System health check | The PUP might have altered system files and settings. That may cause abnormal device behavior. Avoid that by performing system diagnostics with the FortectIntego repair software |
Remove Browse Safely whether it's installed as an app or an extension
This chapter will help you to get rid of the pesky cyber threat. Since it can be installed as an application under practically any name, manual removal could be hard to complete. That's why we recommend downloading the Malwarebytes security software and performing a full system scan with it.
If Browse Safely is installed as an app, it will automatically detect the PUP, isolate it, and suggest removing it. Please comply with whatever the reliable anti-malware tool recommends getting rid of, as its trustworthy antivirus engine is capable of determining whether any apps or files could be dangerous both to you and your device.
On the other hand, if you want to remove the browser hijacker manually, use illustrated instructions prepared by our IT experts:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.
![Uninstall from Windows 1 Uninstall from Windows 1]()
- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait until the uninstallation process is complete and click OK.
![Uninstall from Windows 2 Uninstall from Windows 2]()
However, please note that if any files or entries are overlooked, the PUP infection could renew or cause system and browser failures. You can avoid all that by scanning your infected device with the SpyHunter 5Combo Cleaner anti-malware software to remove all intruders automatically.
Now that the device is clear from any malicious software, you have to check for and, if found, remove Browse Safely extension from your browsers. This will be an easy task to complete, as this browser hijacker is targeting exceptionally only the Google Chrome browser.
Our team has once again prepared illustrated guidelines to eliminate the questionable extension so that the whole process would take just a few minutes. Please follow this step-by-step guide:
- Open Google Chrome, click on the menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
Once you remove Browse Safely extension from Google Chrome, it won't block you from changing the default settings back to as they were before the browser hijacker modified them. Let's begin by resetting your default or preferred homepage:
- Click the menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Then you can easily reset the default search engine as using the one from the potentially unwanted program might only bring troubles. Restore it as follows:
- Click the menu and click on the Settings.
- On the left-hand side, press on Search engine.
- Pick your preferred search provider from the dropdown menu.
After completing these steps correctly, the Browse Safely hijacker will be completely eliminated from the system. Please remember that keeping a trustworthy anti-malware tool on your device might prevent you from installing various shady apps and block severe malware from accessing it.

Instructions to repair damaged system sections and remove tracking cookies
Treacherous sites that you might have been forced to visit while the article's culprit was operational on your device could have stored tons of tracking cookies that help to collect various browsing-related details about you and your device. They need to be removed to keep your privacy safe.
You could complete this task manually, but it could take a long time to clean them all if you have multiple browsers. That's why we recommend entrusting taking out the trash to the FortectIntego system diagnostics tool. But that's only one feature of this awesome tool.
It will also remove all traces of Browse Safely from the registry, temporary folders, and other system directories. And last but not least, the powerful software will repair all damages caused by the virus by restoring proper registry values/keys, fixing corrupted system files, and so much more. It's free to try out, so give it a go:
- Download the application by clicking on the link above
- Click on the ReimageRepair.exe
![Reimage download Reimage download]()
- If User Account Control (UAC) shows up, select Yes
- Press Install and wait till the program finishes the installation process
- The analysis of your machine will begin immediately
![Reimage scan Reimage scan]()
- Once complete, check the results – they will be listed in the Summary
- You can now click on each of the issues and fix them manually
- If you see many problems that you find difficult to fix, we recommend you purchase the license and fix them automatically.
![Reimage results Reimage results]()
How to prevent from getting browser hijacker
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Potentially unwanted program. Wikipedia. The free encyclopedia.
- ^ Non-Personal Information definition. Lawinsider. Legal research site for contracts, clauses and defined terms.
- ^ Novirus. Novirus. Spyware news and security.






