Cauthaushoas.com ads (Free Guide)
Cauthaushoas.com ads Removal Guide
What is Cauthaushoas.com ads?
Cauthaushoas.com ads can bring malicious links directly to your desktop
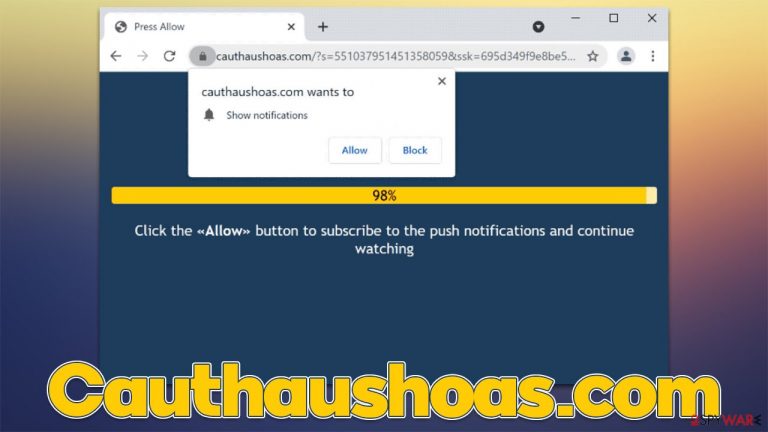
Cauthaushoas.com is a fake website created by crooks. It holds no tangible content, and its main purpose is to convince users to subscribe to push notifications. Several different misleading messages can be used for that, and as long as visitors click the “Allow” button within the prompt upon site entry, the scam can be declared as successful.
Sometime after, users might experience strange Cauthaushoas.com pop-ups showing up at random times without warning. The most strange part about this behavior is that the push notifications are not triggered by user actions, such as visiting a particular website. This happens because the ads are run through the built-in feature and can be shown on the system level as long as the browser is running (it doesn't have to be actively used).
More about the Cauthaushoas.com scam
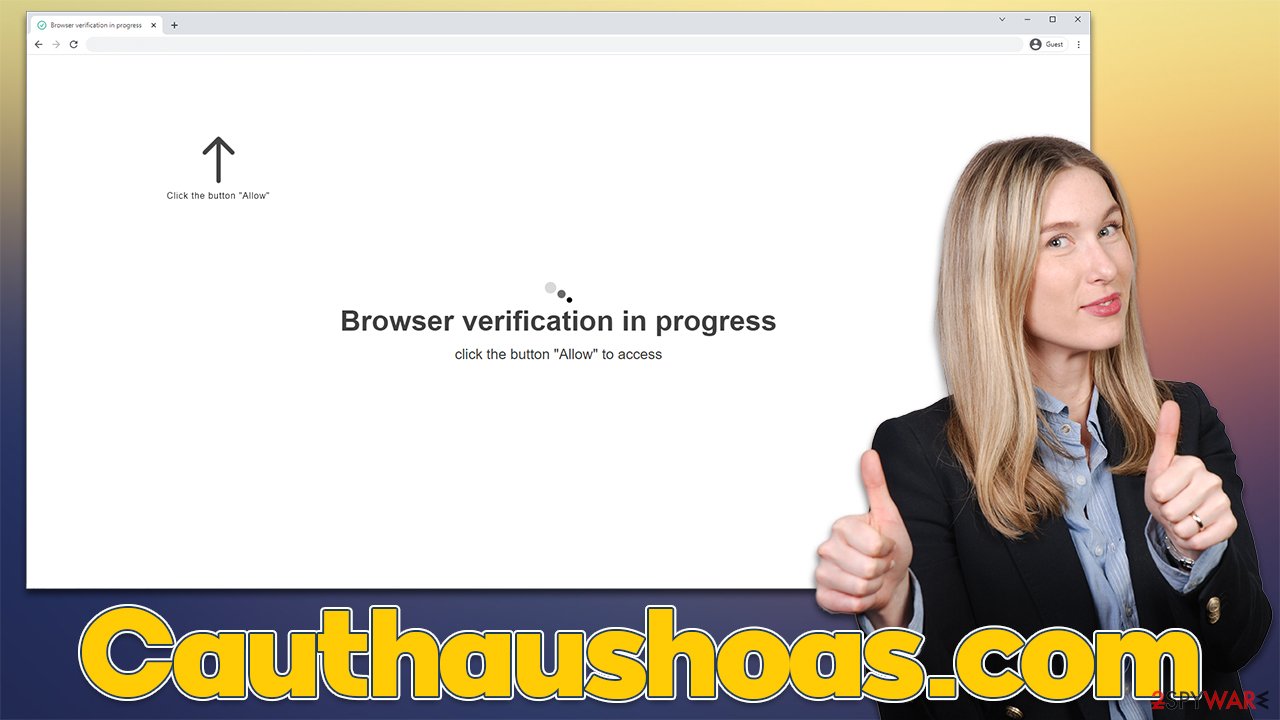
Users are usually redirected to scam sites by a malicious script[1] embedded somewhere else or when they click a booby-trapped link. This means that redirect happens unexpectedly, making it easier for scammers to do their jobs and trick people. For that, they employ several misleading messages that are meant to make people allow notifications, for example:
Click Allow if you are not a robot
This message implies that it's just a simple bot check, which is commonly used by legitimate websites to prevent dangerous DDoS[2] attacks. This familiarity is what often makes people proceed with the instructions they have been given. People might also be told that their browser is blocking video playback, that they need to confirm their age, etc.
| Name | Cauthaushoas.com |
| Type | Push notifications, ads, pop-ups, scam |
| Infiltration | The unwanted activity starts sometime later after the “Allow” button is pressed via the notification prompt |
| Symptoms | Push notifications show on the desktop at random time intervals. They show fraudulent content and links to potentially dangerous websites |
| Risks | If you click on links provided by the website, you might end up infecting your system with malware/PUPs, disclosing your personal information to cybercriminals, or losing money for useless services |
| Removal | Access browser settings to stop intrusive push notifications. After that, make sure that your system is not infected with adware or malware – scan it with SpyHunter 5Combo Cleaner |
| Other tips | Use FortectIntego to remediate the system after adware infection. The tool can also be used to clean web browsers automatically |
Dangers of Cauthaushoas.com ads
Once the permission to show notifications is granted, users can expect to see push notifications shown on their screens at any point in time, as long as the browser is operational. This allows interested parties to expose users to various advertisements, bringing revenue in the process.
Unfortunately, since scammers are known not to use reliable advertising networks, the quality of ads shown are often very poor – they can even be misleading/malicious in some cases. Among your regular ads, those affected can expect to see the following:
- Get-rich-quick schemes that tell users they can invest a (small) sum of money for incredible returns just a few days or weeks later. These are commonly accompanied by fake success stories of local celebrities and fake Facebook user messages;
- Misleading virus infection prompts would claim that the system has been infected with viruses and that they need to be removed as soon as possible with the offered anti-malware. These prompts often impersonate legitimate security vendors by using their logos and norices;
- Gift cards and other giveaway scams might offer an expensive gift by being allegedly chosen by a well-known corporation, such as Amazon, Google, or similar. Usually, crooks want to acquire user information by using these scams, so you should never interact with them.
Take care of adware
While most users venture off to Cauthaushoas.com after clicking links on some dangerous website, there are different circumstances when this can occur. Adware,[3] which is a type of potentially unwanted software, is one of the most common reasons for users encountering suspicious or malicious content online.
The main goal of adware is to expose users to as much commercial content as possible, which can disturb regular browsing sessions with intrusive pop-ups, banners, coupons, offers, and other ads. More aggressive forms of adware might not even emit any symptoms and perform background connections with remote servers, generating revenue for cybercriminals in the process.
To check your device for adware, you should analyze applications installed on it – they can be installed as programs on a system-level or could arrive as extensions on the browser. You could follow the instructions below or pick a more reliable and quicker method – scanning the system with SpyHunter 5Combo Cleaner or Malwarebytes security software, which would automatically remove all the infections. Likewise, FortectIntego can be used to clean browsers from cookies and caches to ensure no remnants remain.
Windows
- Enter Control Panel into the Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till the uninstallation process is complete and click OK.

Mac
While moving apps into Trash is how you delete most normal applications, adware tends to create additional files for persistence. Thus, you should look for .plist and other files that could be related to the virus. If you are not sure, skip this step entirely.
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
Removal of unwanted notifications
The surprise of seeing suspicious ads showing up on the desktop would make any user alert, as there are no prior warnings or other signs. This prompts people to believe that they have been infected with some type of virus, which is not the case this time. In order to stop Cauthaushoas.com ads, you need to access your browser settings and block the website from sending you notifications:
Google Chrome
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.

Google Chrome (Android)
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off position).

Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.

Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.

MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.

Internet Explorer
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.

- Locate the web address in question under Allowed sites and pick Remove.
How to prevent from getting adware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Josep Albors. Malicious scripts in compromised websites and how to protect yourself. WeLiveSecurity. ESET security blog.
- ^ What is a DDoS attack?. Cloudflare. The Web Performance & Security Company.
- ^ Adware. Investopedia. Source of financial content on the web.
