CIA Election AntiCheat Control virus (Virus Removal Instructions)
CIA Election AntiCheat Control virus Removal Guide
What is CIA Election AntiCheat Control virus?
What is it necessary to know about CIA Election AntiCheat Control virus?
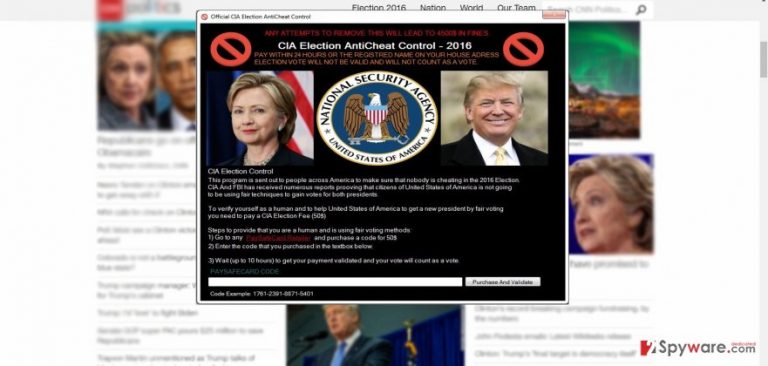
CIA Election AntiCheat Control virus is a newly detected malware which tries to wheedle out money. US presidential elections are certainly one of the hottest topics currently, as Hilary Clinton and Donald Trump is in a tight race for voters’ sympathies. Following the trends, the hackers did not miss the chance to exploit the topic for their benefits. The newly detected malware is presented as the message of an anti-cheat election control. By paying $50, a user proves his identity. All seems fine and dandy except that similar poll tax was abolished already in 1965 with perhaps mere exceptions in several states. However, now US citizens do not have to remit specific payment to vote. Hackers did their best to forge a convincing program that it is a legitimate notification issued by the US government. It might work on credible users who are not aware of malware tendencies. If you spotted this virus on the computer, rest assured as we will tell you how you can remove CIA Election AntiCheat Control. One of the options to do that is to launch FortectIntego and run the system scan.
This malware is not an exception. Throughout the history, hackers have presented multiple stunning masterpieces which sometimes are not only highly credible but amusing as well. In this case, the hackers use a legitimate background. Unfortunately, such felony might work out as citizens, unaware of different cyber deception forms, might fall for the bait. In fact, the crooks did a pretty good job forging such hoax. They place the infection in election.exe file. Afterward, they apply to users’ honesty and ask to confirm their identity by paying a small amount of money. What is more, they urge to transfer the money within 24 hours. Otherwise, the vote will be invalid. The hackers also took some precautions as the malware closes these processes to prevent the victim from ceasing the infection:
cleanmgr,cmd, msconfig,control,firefox, filezilla, iexplore, javaw, mbam, MicrosoftEdge,MSASCui,notepad,opera,chrome,RegEdit,Winrar,Spotify,MMC,msinfo32,Taskmgr,wordpad
Later on, when a victim remits the payment, the technical information about the device is transferred to emilyrosefelt0@gmail.com. The virus also connects to http://textupload.com/d54g3 web page. Likewise, the response is automatically sent to confirm the payment. Ironically, the notification thanks the victims for their honesty. What is more, the threat fortifies its position on the system by injecting its specific registry key: HKLM\SOFTWARE\\Microsoft\\Windows\\CurrentVersion\\Run “Election Cheating Confirmed” = “election.exe”. Do not waste time and proceed to CIA Election AntiCheat Control removal.
When did the malware get into my computer?
This type of infection might have exploited the opportunity to sneak into the device when you were surfing in an infected website or downloaded the corrupted torrent. Such infections also target victims by hiding in the links of various amusing and entertaining videos or legitimately infected applications. If you tend to download new software from secondary distributors, then there is a higher probability of running into a cyber infection. In order to dodge such threat, a proper security tool is vital. Besides it, you can escape CIA Election AntiCheat Control hijack by carefully installing a new application from trusted sources. Visiting file sharing domains and installing cracked games should be avoided as well.
CIA Election AntiCheat Control removal instructions
Since this malware is not an ordinary computer pest, proceed to the termination stage. Remove CIA Election AntiCheat Control virus with the help of a reliable security tool (FortectIntego or Malwarebytes). Check whether it is updated and run the scan. The software will eliminate the threat and its registry keys within a couple of minutes. Manual CIA Election AntiCheat Control removal is not recommended unless you are confident that you can deal with this cyber infection on your own. Lastly, you may suspect similar felony to be a hoax by paying attention to the details. If you give a second look, you might notice that the hoax includes grammar mistakes. Moreover, you might compare the given credentials to the original ones.
How to prevent from getting malware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
