Cirlaing.com ads (fake) - Free Guide
Cirlaing.com ads Removal Guide
What is Cirlaing.com ads?
Cirlaing.com asks users to press “Allow” to get them to subscribe to push notifications
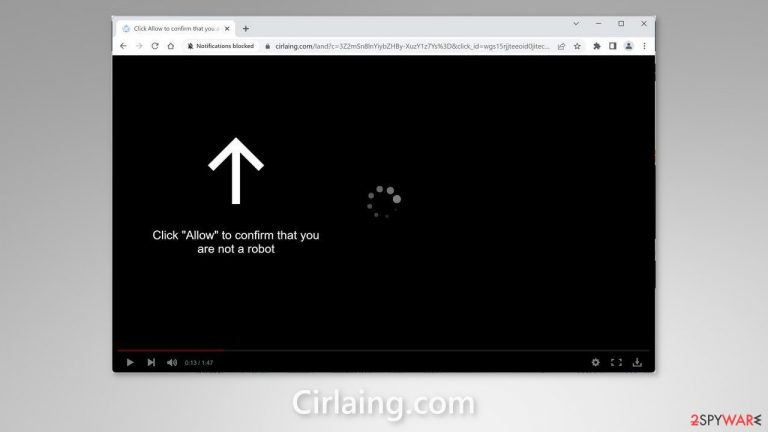
A bogus website called Cirlaing.com was set up by crooks to monetize user activity with pay-per-click advertising. Social engineering methods[1] are used by scammers to deceive individuals into subscribing to push notifications. They urge individuals to hit the “Allow” button to watch a video. However, the only content on this site is the deceptive image and message.
In addition, fraudsters use rogue advertising networks[2] to place ads leading people to dangerous websites. People can accidentally land on scam pages that try to lure out their personal information like credit card numbers or trick them into downloading PUPs (potentially unwanted programs),[3] and even malware.
| NAME | Cirlaing.com |
| TYPE | Push notification spam; adware |
| SYMPTOMS | Pop-up ads start appearing in the corner of the screen after the “Allow” button is pressed |
| DISTRIBUTION | Shady websites, deceptive ads, redirects, freeware installations |
| DANGERS | Links embedded in the push notifications can lead to dangerous websites where users can be tricked into providing their personal information and suffer from monetary losses |
| ELIMINATION | Users can block push notifications via browser settings |
| FURTHER STEPS | It is recommended to use a repair tool like FortectIntego after the removal to fix any remaining damage |
Distribution methods
Notification spam pages, such as Cirlaing.com, rarely show up in the search results. They typically lurk on shady websites that are not regulated. Illegal streaming websites, for example, are filled with fraudulent advertising and deceptive redirects. Users looking to illegally watch a movie or television program may be fooled by phony “Download” or “Play” buttons[4] and sent to pop-up spam pages that employ social engineering tactics to deceive them.
We recommend clicking on links and ads only if they come from websites that you know and trust. If you're not sure whether a product or service is legitimate, do some research before clicking on anything. To be completely safe, use official streaming services like Netflix and Prime Video – you will just need to pay a small monthly subscription fee.

Block notifications from Cirlaing.com
Because push notifications are subscription-based, they can be turned on and off only manually. We have a detailed guide for the most popular browsers below:
Google Chrome (desktop):
- Open Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.

- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.

Google Chrome (Android):
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).

Mozilla Firefox:
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click Settings button next to it.

- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.

Safari:
- Click on Safari > Preferences…
- Go to Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.

MS Edge:
- Open Microsoft Edge, and click the Settings and more button (three horizontal dots) at the top-right of the window.
- Select Settings and then go to Advanced.
- Under Website permissions, pick Manage permissions and select the URL in question.
- Toggle the switch to the left to turn notifications off on Microsoft Edge.

MS Edge (Chromium):
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.

Clear your browsers
It is highly suggested that you clear your web browsers after an encounter with a push notification page. Websites may utilize a variety of tracking methods, like cookies. They can store data such as IP addresses, geolocation, website visits, links clicked on, and online purchases.
While cookies have some positives – like allowing websites to generate personalized content for users – often times they are embedded in order to sell user information to advertising networks and other third parties. You should use a maintenance tool, like FortectIntego. With the click of a button, this software can not only stop cookies from tracking but also delete any existing data that was already collected.
Scan your system for adware
Unwanted browser activity can also be caused by PUPs. Pages like Cirlaing.com occasionally appear without any user interaction. Adware is a computer program that creates commercial content on the machine automatically. Many of them are masqueraded as ” handy” utilities, making them more difficult to detect for average users.
Proper security tools are essential for any PC – think of them as a door to your home. Anti-malware solutions can scan your machine and detect suspicious processes running in the background, which could alert you to dangerous files trying to enter your system. Use professional security tools SpyHunter 5Combo Cleaner or Malwarebytes to scan your system if you still experience unwanted symptoms.
However, if you still want to do this yourself, you can follow our step-by-step instructions for Windows and Mac machines:
Windows 10/8:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

Windows 7/XP:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.

- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Mac:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

How to prevent from getting adware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Cynthia Gonzalez. Top 8 Social Engineering Techniques and How to Prevent Them [2022]. Exabeam. Information Security.
- ^ Zeljka Zorz. How does a rogue ad network function?. Helpnetsecurity. Information Security Blog.
- ^ Chris Hoffman. PUPs Explained: What is a “Potentially Unwanted Program”?. Howtogeek. Technology Magazine.
- ^ Andy Maxwell. Google Targets Fake ‘Download’ and ‘Play’ Buttons. Torrentfreak. Filesharing News.
