Coatimundiresults.shop ads (fake) - Free Guide
Coatimundiresults.shop ads Removal Guide
What is Coatimundiresults.shop ads?
Coatimundiresults.shop is a malicious website designed to make you spend money on software you don't need

Coatimundiresults.shop is a scam website that seeks to benefit from affiliate links in a deceptive way, where users are always victims as a result. People usually end up on this site by accident after clicking a malicious link elsewhere, which contributes to the scheme's overall success.
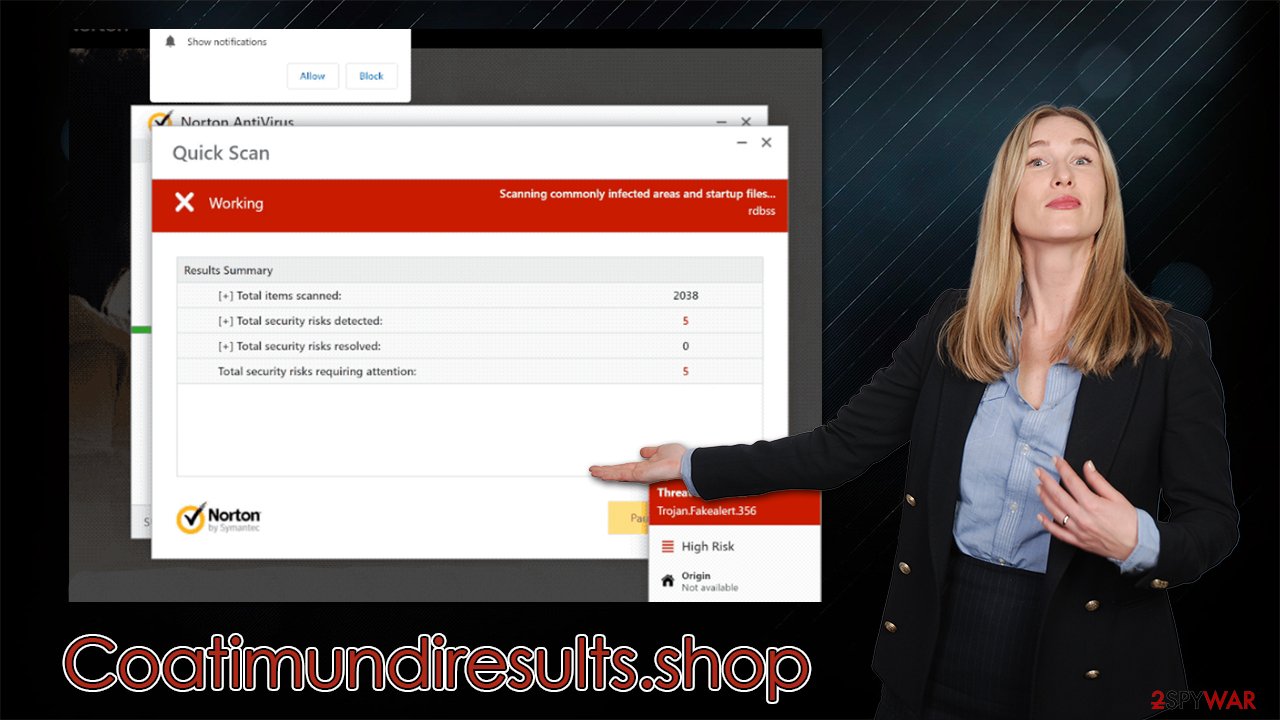
Scammers created Coatimundiresults.shop to impersonate security software provider Norton's system scan results page. The fake results claim that the user's computer is infected with malware and must be fixed immediately.
If users follow instructions on the page, they are redirected to download useless (and possibly harmful) software – the scheme benefits scammers through clicks and affiliate links.[1] To make it clear, everything promoted on this page is fake and shouldn't be trusted – Norton also has nothing to do with phishing pages like these.
If you've come across this scam, read the following information to learn more about it. We also show you how to continue and remove adware from your computer if it is there and explain how to disable the push notifications from Coatimundiresults.shop if they were enabled by accident or otherwise.
| Name | Coatimundiresults.shop |
| Type | Scam, phishing, redirect, adware |
| Operation | Shows fake virus infection messages and claims that security software has expired – asks to renew the alleged subscription. Site also asks to enable push notifications to be able to send ads to users |
| Distribution | Redirects from other malicious websites, adware |
| Risks | Those who have malicious software installed on their systems are more likely to encounter dangerous websites, resulting in financial losses, malware infections |
| Removal | You should not interact with the contents shown by a scam website, check your system for adware or malware infections with SpyHunter 5Combo Cleaner security software |
| Other tips | To prevent third parties from tracking your online activities, we recommend clearing browser caches and other leftover files with FortectIntego |
Oftentimes, people create false messages online to make a quick buck from advertisements, software downloads, or subscriptions to unnecessary services. While it's legal to run an affiliate program, the advertising for the said product in a manner that is considered not only deceptive but straight out malicious – is not, and that's a critical detail.
That being said, fake virus alerts are more likely to cause users distress, which would result in them buying the software just to allegedly get rid of the problem they are presented with. This is a perfect opportunity for scammers to convince people to spend money on software, even though they don't really need it.
The scam message
Upon entering the fake Coatimundiresults.shop site, users are soon shown what seems to be a security scan done by anti-malware software. During this time, people will see several pop-ups and alleged detections, which would ultimately lead to the following message:
Your PC is infected with 5 viruses!
ACTION REQUIRED
Your McAfee Subscription Has Expired!
Renew now to keep your PC protected.
If your PC is unprotected, it is at risk for viruses and other malware.
Even though it may seem so, this is nothing but just an imitation and has nothing to do with a real scan of anti-malware installed on the system. It is also important to note that while some information might be extracted from your device when you visit a particular website (your IP address or your browser type/version), there is no way for a website to tell whether or not your system is infected. Thus, whenever you see a “system scan” triggered upon entering a website, rest assured that it's fake and should not be trusted.
Similar scams
Coatimundiresults.shop is just one of thousands of websites we have recently seen around the web that has been abusing the names of popular security vendors such as Norton. For example, we have recently discussed Securitycheckpanel.com, Rebis.live, and Scanprotectiontoday.com scam sites, which use the exact same tactics as Coatimundiresults.shop. In fact, these websites are identical – they display the same “results” and the same pop-ups during the fake scan.
Whether or not these websites are connected or created by the same cybercriminals is unknown, although the latter is unlikely merely due to the share volume of these sites popping around constantly. It is important you do not interact with any of these websites, as they might redirect you to other malicious places and cause security issues for you.
How phishing messages spread
More often than not, you are likely to encounter a phishing[2] website after visiting an already deceptive one. For example, torrents, peer-to-peer[3] networks, software crack distributors, and similar sites are more likely to include various booby-trapped links that would be hidden inside. Sometimes, an accidental click somewhere on the website's page might also lead to an unexpected redirect. Therefore, you should stay away from such sites as much as possible.
Alternatively, people may already be infected with adware or other potentially unwanted or malicious programs. If that's the case, you are more likely to encounter all sorts of advertisements while browsing the web or notice rerouting tendencies. Thus, if your system is infected, you are more likely to encounter a malicious ad or fake update by accident.
Therefore, we recommend you employ powerful security software, such as SpyHunter 5Combo Cleaner or Malwarebytes, and perform a full system scan with it. The security tool not only locates malicious components on your system but also removes them effectively. Additionally, with FortectIntego, you can clean up leftover files such as cookies used for tracking and improving your system performance.
Remove annoying push notifications
When users arrive at the site, they are not only informed of a phony warning that claims to have viruses but also given the option to enable push notifications. Even if you accidentally clicked “Allow” in the notification prompt by accident, unwanted push notifications would display at random intervals, bringing with them malicious links.
If you are experiencing similar symptoms, we recommend you access your browser settings and block the website's URL within the list of those allowed to show notifications.
Google Chrome
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.
![Stop notifications on Chrome PC 2 Stop notifications on Chrome PC 2]()
Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.
![Stop notifications on Mozilla Firefox 2 Stop notifications on Mozilla Firefox 2]()
Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.
![Stop notifications on Safari Stop notifications on Safari]()
MS Edge
- Open Microsoft Edge, and click the Settings and more button (three horizontal dots) at the top-right of the window.
- Select Settings and then go to Advanced.
- Under Website permissions, pick Manage permissions and select the URL in question.
- Toggle the switch to the left to turn notifications off on Microsoft Edge.
![Stop notifications on Edge 2 Stop notifications on Edge 2]()
MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.
![Stop notifications on Edge Chromium Stop notifications on Edge Chromium]()
Internet Explorer
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.
- Locate web address in question under Allowed sites and pick Remove.
![Stop notifications on Internet Explorer Stop notifications on Internet Explorer]()
How to prevent from getting adware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Affiliate Link. Techopedia. Source for professional IT insight.
- ^ Phishing attacks. Imperva. Application and data security.
- ^ James Cope. What's a Peer-to-Peer (P2P) Network?. Computerworld. IT news, careers, business technology, reviews.






