DecYourData ransomware (Virus Removal Guide) - Recovery Instructions Included
DecYourData virus Removal Guide
What is DecYourData ransomware?
DecYourData ransomware – a file locking virus that asks users to contact hackers for a chance of restoring personal data
DecYourData ransomware is a crypto-malware that was first spotted in December 2019, with a new variant appearing a month later.[1] Just as many other similar viruses of such type, it relies on file encryption process (which is performed with the help of AES[2] cipher) to hold all personal files like pictures, documents, databases, videos, PDF, and others, hostage, and demand ransom payment in Bitcoin cryptocurrency for DecYourData ransomware decryption software.
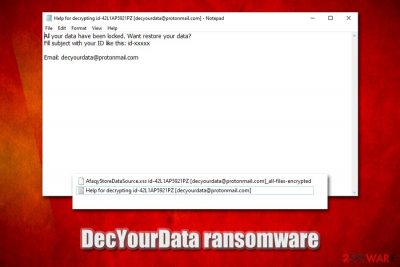
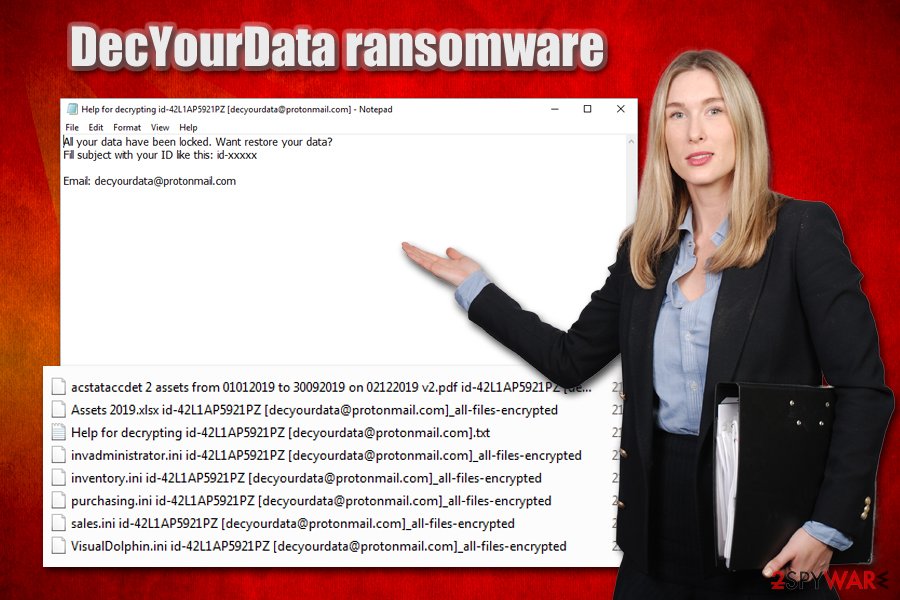
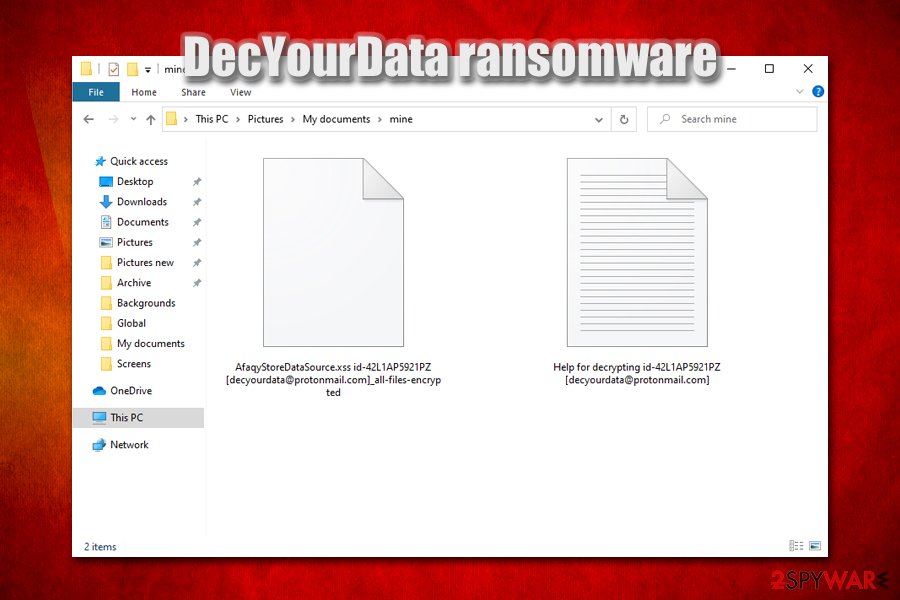
Once the DecYourData virus infection is triggered, it will scan the machine for encryptable files and provide a unique ID for each victim, which will later be used for identification, payment, and decryption process. To make sure that users know how to proceed next, malicious actors drop a ransom note “Help for decrypting id-victim ID [contact email].txt, which emails that users have to contact them via decyourdata@protonmail.com, although later version used backtonormal@tutanota.com and backtonormal@vistomail.com emails. The encrypted data is marked per the following template: id-victim ID [contact email]_all-files-encrypted. Currently, the only safe way to recover DecYourData ransomware encrypted files is by using backups, although using a few alternative methods might sometimes prove successful.
| Name | DecYourData ransomware |
| Type | File locking virus, cryptomalware |
| Encryption algorithm | All files are locked with the help of a symmetric AES encryption algorithm |
| Extension | There is no dot after the full name of the file – instead, the malware uses a space. Each of the encrypted files is appended with a particular template that consists of victim's ID and contact email; an example of an encrypted file: AfaqyStoreDataSource.xss id-42L1AP5921PZ [decyourdata@protonmail.com]_all-files-encrypted |
| Ransom note | A template for the ransom note is also used, and includes victim's ID and email address, for example: Help for decrypting id-42L1AP5921PZ [decyourdata@protonmail.com].txt |
| Contact | decyourdata@protonmail.com, backtonormal@tutanota.com and backtonormal@vistomail.com |
| Ransom size | Some victims were asked to pay $5,000 in Bitcoin to recover all encrypted data |
| Associated crypto-wallet | 1RTvJ9ygzWm74g1WuNcLuQMHXiMtL5hP1 |
| Data decryption | The only safe way to retrieve files is by using backups, although using third-party recovery software might be helpful for some victims |
| Malware removal | To get rid of ransomware infection, scan your computer with reputable anti-malware software (for example, SpyHunter 5Combo Cleaner or Malwarebytes) in Safe Mode with Networking |
| System fix | Malware can cause significant damage to Windows system files. To fix virus damage and restore the registry, use FortectIntego repair tool |
Due to relatively low prevalence of DecYourData ransomware, pinpointing its exact distribution techniques can be difficult. Nevertheless, most of file locking malware is delivered via the following methods:
- Malicious spam email attachments or hyperlinks;
- Pirated software installers or software cracks/loaders/keygens;
- Poorly protected Remote Desktop (RDP) connections;
- Exploit kits and software vulnerabilities;[3]
- Fake updates and other executables presented on phishing sites.
As soon as the DecYourData virus breaks into a computer (it can attack all Windows versions, including the latest Windows 10), it populates various files into %TEMP%, %Users%, and other folders, one of which is typically a main executable of the malware. This file is generally used to examine particular ransomware behavior by automated sandbox tests.
Once launched, DecYourData proceeds with various system modifications, such as deletion of Shadow Volume Copies (prevents data recovery from automated backups), modification of Windows registry database (increases persistence), termination of various recovery features, etc. Due to these changes, DecYourData ransomware removal might sometimes not be successful in the normal environment, which is why experts[4] suggest users accessing Safe Mode and only then perform a full system scan with powerful security software.
Once the preparations are complete, DecYourData ransomware proceeds with file encryption process witch appends a lengthy extension to most commonly used file types, such as .doc, .pdf, .mp4, .jpg, .dat, .mdb, .ini, etc. As a result, victims can no longer access their data, and they see a blank icon instead of an original one. Unlike most of the other ransomware, the DecYourData virus does not use the dot, which is followed by a predetermined file extension but instead replaces it with space.
After that, a brief ransom note is presented to the infected users, which states:
All your data have been locked. Want restore your data?
Fill subject with your ID like this: id-xxxxx
Email: decyourdata@protonmail.com
Most experts recommend avoiding contact with DecYourData, as well as other ransomware authors, as there is no guarantee that they will provide a decryption tool. However, because the decryptor is unique to each victim, there is little chance of recovering data without paying criminals or negating ransomware devastating effects by using backups.
If your files are encrypted by DecYourData, and you have no backups available, you should consider what is best for you. We highly recommend avoiding paying the ransom, although it might be the only choice in some cases (you should realize that you might also lose your money, however). Some victims who contacted cybercriminals claimed that they were asked to pay as much as $5,000 in BTC for decryption software.
Instead, you should copy encrypted files to an external or a virtual drive, remove DecYourData ransomware with anti-malware software, fix your Windows with FortectIntego or similar repair software, and then attempt data restoration via methods provided in our recovery section below.
Data-encrypting malware can be spread via various different methods
As already stated before, there are a variety of methods that cybercriminals behind ransomware viruses can use, including exploits, fake updates, spam emails, weakly protected RDP connections, etc. Some of these methods are relatively primitive, while others are far more sophisticated and complicated, and because no anti-malware software can catch 100% of the incoming computer threats, having a security program installed is not enough to protect yourself.
One of the most prominent ransomware and other malware distribution method is spam emails, where crooks clip malicious attachments or insert hyperlinks. As a general rule, malspam campaigns use popular brand names, such as Amazon, UPS, etc., although random short email messages are common too. With the help of email spoofing[5] and good social engineering skills, criminals convince users to open attachments embedded with malicious macros or click on hyperlinks that would connect to a remote server and deliver the malicious ransomware payload. Thus, please do not casually open email attachments or click on links inside, unless you are sure that the email is real.
Additional protection measure tips include:
- Use strong passwords for all your accounts;
- Apply security updates for all your installed applications and the OS immediately;
- Never download pirated software installers or cracks;
- Employ additional tools for protection, such as ad-block and Firewall;
- Do not use the default TCP port for RDP and disconnect as soon as you are done using the feature;
- Backup your files regularly.
Data recovery options and DecYourData ransomware removal method
Getting infected with ransomware is a tough situation to be in, as DecYourData ransomware removal would not restore all the encrypted files, despite the popular belief. It is important to realize that, once files are encrypted, only a specialized decryption tool that is stored in the reach of hackers or, in some cases, third-party software might be able to work.
Note that security researchers are also constantly working on finding bugs within the encryption process of ransomware viruses, which already resulted in successful decryptor release for multiple malware families or its versions, including BigBobRoss, Djvu, Cerber, Paradise, and many others. You can find many of such tools on the No More Ransom Project page. Thus, while there is no guarantee, it is possible that decryption software will be created for the DecYourData virus as well.
If you had no backups, you should safely copy the encrypted files over (otherwise, the files might get permanently damaged, and even a working decryptor will not be successful in its recovery), remove DecYourData ransomware by following the instructions below, and then use third-party software tools to attempt file recovery.
Getting rid of DecYourData virus. Follow these steps
Manual removal using Safe Mode
To get rid of DecYourData ransomware without interruptions, access Safe Mode with Networking:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove DecYourData using System Restore
You can also employ Safe Mode for malware removal:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of DecYourData. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove DecYourData from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by DecYourData, you can use several methods to restore them:
Data Recovery Pro might be successful in recovering encrypted files
Data recovery software does not decrypt files, but rather looks for working copies burred within your hard drive. The success rate of this process highly depends on how much you used the machine after the infection.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by DecYourData ransomware;
- Restore them.
Make use of Windows Previous Versions Feature
This method could help you recover some files one-by-one if you had System Restore enabled before ransomware struck.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer might sometimes recover 100% of your data
In case the DecYourData ransomware virus failed to delete Shadow Volume Copies, you should be successful in all of your data recovery with tools like ShadowExplorer.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No decryptor is currently available
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from DecYourData and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Amigo-A. New variant #DecYourData #Ransomware. Twitter. Social Network.
- ^ Advanced Encryption Standard. Wikipedia. The free encyclopedia.
- ^ Exploit Kits. NJCCIC. New Jersey Cybersecurity & Communications Integration Cell.
- ^ Virusai. Virusai. Malware analysis and cybersecurity insights.
- ^ Alan Henry. How Spammers Spoof Your Email Address (and How to Protect Yourself). LifeHacker. The ultimate authority on optimizing every aspect of your life.





















