DeriaLock ransomware / virus (Improved Instructions)
DeriaLock virus Removal Guide
What is DeriaLock ransomware virus?
DeriaLock ransomware virus: is it dangerous?
DeriaLock ransomware virus is a screen-locking infection [1] which blocks victims from accessing the data stored on their computers. Though there is normally a clear distinction between crypto-ransomware [2] and lock screen ransomware, the DeriaLock virus balances somewhere between the two: its initial versions are lock screen-based while the later, updated variants involve actual file encryption. Either you are infected with one or the other, you should never succumb to the demands of the extortionists. Their one and only goal is to generate easy money and continue to improve their malicious creations while the state of your computer and your files bothers them the least. Luckily, the hackers behind this virus are quite amateur and have left some flaws which allowed the experts to come up with alternative lock screen removal and data decryption techniques. You will find all the recommendations on how to exterminate this parasite at the end of the article. DeriaLock removal can also be approached by employing antivirus software, say FortectIntego and allowing it to scan the system for infectious files.
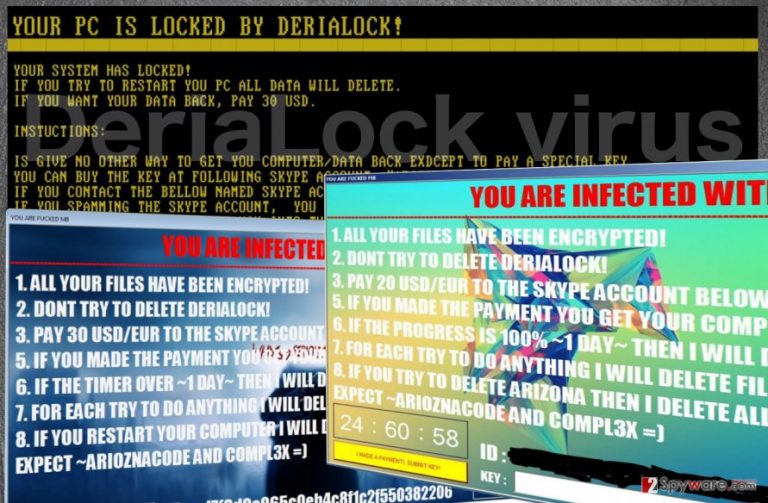
DeriaLock malware is still under development, so its functionality and the scope of targeted operating systems is rather limited. For instance, since it utilizes .NET Framework 4.5 to install, it will not run on Windows XP. Nevertheless, the parasite may cause quite a havoc on the devices it does manage to infect. To initiate the lock screen DeriaLock will generate the MD5 hash [3] and connect to the C&C server [4] in order to take further control of the device. Besides, through this very server, the hackers may also update the lock screen virus version to its newer and more dangerous counterpart. The infected users will see the following ransom note:
Your System has Locked!
If you try to restart you PC, ALL data will delete.
If you want your data back, pay 30 USD.
Instuctions:
Is give no other way to get you computer/data back exdcept to pay a special Key.
You can buy the Key at the following Skype account: “arizonacode”.
If you contact the bellow named Skype account send him you HWID the bottom left is to be seen.
If you Spamming the skype account, you can’t get you data back
After you buy the key, paste him into the textbox.
This yellow-on-black screen will appear every time the computer is launched and prevent the user from properly booting the device. In addition to this, DeriaLock also shuts down access to such Windows functions like Task Manager, Skype or Chrome blocking the victim from easily eliminating the lock screen. If the victim manages to terminate this obstacle, he/she will access the desktop, files, and other computer data once again and remove DeriaLock from the computer. In case the device is infected with the file-encrypting virus, things may get a bit more complicated. Lock screen elimination will not help to regain access to the computer files. The virus jumbles up the contents of the targeted documents and appends them with .deria extensions, making them virtually unreadable without a decryption key [5]. Thus, the encrypted data has to be decrypted some other way. We will talk about the data recovery options just below the DeriaLock elimination guide. As for the users who have not been infected with this ransomware yet, please carefully read through the following paragraph where we talk about ways to prevent its infiltration.
How should you block the ransomware attack?
Unfortunately, if the virus developers choose you as their target victim, there is little that can actually be done to block the attack. Of course, antivirus utilities and other security software may warn you against visiting suspicious websites, downloading shady applications or email attachments that may carry DeriaLock virus, but you should keep in mind that no anti-malware tool can prevent ransomware attack a full 100%. Thus, it is highly recommended to take action and protect your data rather than try to block out the virus. Keep backup copies of your files, store them somewhere safe (preferably, external drives) and you will always be confident that your important documents are secure.
DeriaLock removal strategies:
Since DeriaLock virus is a diverse infection, there are more than one way to approach it. First, if you are about to remove DeriaLock lock screen, you may not bother trying to disable it pressing the ALT + F4. If you do, you will merely get a pop-up saying: “I think that is a bad decision. Nice try mate =)”. To eliminate the lock screen properly, follow the guide below. Just below these instructions, you will find DeriaLock removal guide and data recovery instructions, in case your device is infected with the latest version of the virus.
Getting rid of DeriaLock virus. Follow these steps
Manual removal using Safe Mode
In order to remove DeriaLock lock screen and access your data, you should run your device in Safe Mode and terminate the lock screen process via the Command Prompt. Once you regain the access to your desktop, run the automatic system scan immediately and eliminate the virus from your computer.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove DeriaLock using System Restore
In case the virus is blocking your antivirus from running the system scan check out the instructions below. These should help decontaminate the infection and delete it properly.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of DeriaLock. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove DeriaLock from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by DeriaLock, you can use several methods to restore them:
Free DeriaLock decryptor
That’s right, you do not have to pay the extortionists to decrypt your files. To obtain the decryption tool for free, you should contact the analyst through the Twitter account or his personal profile.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from DeriaLock and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Eric Geier. How to rescue your PC from ransomware. PCworld from IDG news.
- ^ Crypto Ransomware. U.S. Department of Homeland Security Seal. United States Computer Emergency Readiness Team US-CERT website.
- ^ Tim Brookes. TECHNOLOGY EXPLAINED What All This MD5 Hash Stuff Actually Means [Technology Explained]. MakeUseOf. Technology, simplified.
- ^ Command-and-control server (C. Whatis.techtarget.com online dictionary.
- ^ Nate Lord. What Is Data Encryption?. Digital Guardian technology news site.







