Digisom ransomware (Tutorial) - Virus Removal Instructions
Digisom virus Removal Guide
What is Digisom ransomware?
Digisom malware enters the ransomware market
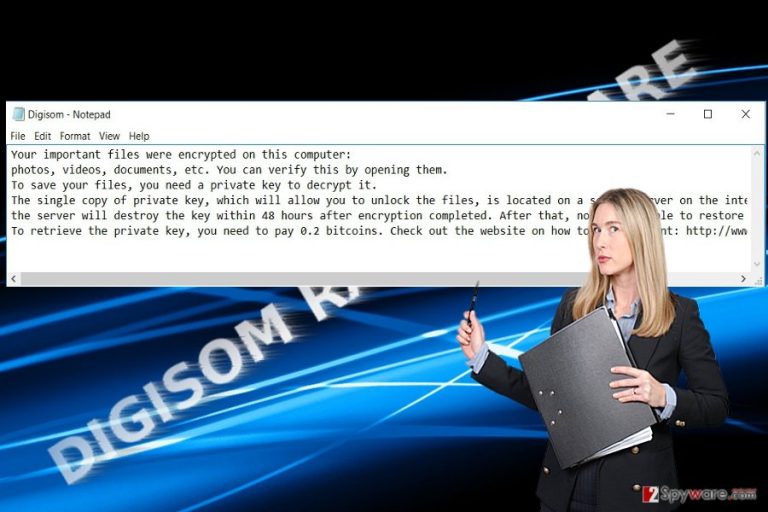
Digisom virus operates as a new file-encrypting virus. It does not differ much from other threats, as it does not only encrypt data, but also deletes them after a couple of hours. Even if this behavior might seem terrifying, there is still a solution. The virus is designed according to the manner as other crypto-malware. It utilizes asymmetric algorithm RSA to encode files[1]. It seems that the malware prefers exerting psychological terror as well as it scares users to transmit the money within 48 hours[2]. It also puts a timer which forbids users not to exit it as it may delete the encrypted files sooner. Nonetheless, there is no need to fall into depression even if you have got entangled by this cyber infection. Below the article, we provide an extensive guide how to remove Digisom permanently.
The key features of this virus do not differ much from other threats. Most likely, the malware sneaked into your computer via an infected spam email message or system vulnerability. Some variations of ransomware even occupy devices with the devices by performing DDoS attacks[3]. In this regard, Digisom malware works in a standard way. It enters the device, modifies registry files which enable it to execute on the computer without any disturbances. Before the encryption, it targets a series of potentially important files and then encodes them with the method of public cryptography, specifically, RSA algorithm. After the encryption is completed, all the files contain altered names – [original_file_name][3_random_characters].x file extension. The encrypted public key is stored in a remote Command and Control[4] server. In comparison with other threats, Digisom ransomware turns out quite into a greedy virus since it demands 2 bitcoins in exchange for the files[5]. Let us warn you not to transfer the money since it is unlikely that the crooks will transfer the files. Ransomware has become a gold mine for racketeers. It is futile to think that they will return the files even if you remit the payment. However, you might lose the money and fail to retrieve the files. Concentrate on Digisom removal.
When does the ransomware invade the device?
Crooks have invented multiple and most diverse distribution channels. Usually, they happen to be spam emails. Therefore, it is crucial not to rush opening spam attachments. Look for typos and grammar mistakes. Corrupted websites such as file sharing and torrent domains frequently serve as malware havens as well. However, cyber villains turn increasingly to legitimate websites as well. One of the recent utilized and quite undetectable technique has remained EITest. It helps forward the user to a domain with an exploit kit. Later on, it delivers the ransomware, and Digisom hijack occurs. Trojanized malware also helps accelerate the infection. In order to decrease the risk of getting infected with this malware again or a similar infection. Besides your anti-virus program, we recommend you to install FortectIntego or Malwarebytes. They will help you get rid of this malware as well.
Is there a way to delete Digisom virus?
When it comes to crypto-malware, do not waste time and initiate its elimination. Anti-malware utilities will help you complete fast and effective Digisom removal. Do not forget to update it for the program to locate all related elements. It is likely that you might not remove Digisom from the first time as the malware might lock your computer screen. In that case, feel free to use the instructions provided below. There are two methods which assist you to unlock the computer screen and bonus suggestions for recovering the data. Lastly, look for suspicious tasks running in the Task Manager and end them.
Getting rid of Digisom virus. Follow these steps
Manual removal using Safe Mode
Use the below-indicated method to recover the full control of the device.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Digisom using System Restore
Perform System Recovery in case the above-suggested methods fail to help you.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Digisom. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Digisom from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Digisom, you can use several methods to restore them:
Data Recovery Pro – solution to decrypt the files?
This program aids at times when your files got corrupted or damaged due to an unexpected system crash. It might help you also retrieve the files affected by Digisom virus.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Digisom ransomware;
- Restore them.
What is Shadow Explorer?
The program works on the basis of shadow volume copies. If the virus does not delete them beforehand, this method might prove effective.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
What about Digisom Decrypter?
At the moment, there is no free decryption software, but either one of the suggested methods might help. If you have regularly performed backups, try recover the files with them.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Digisom and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Tibi Puiu. Quantum computers might soon render RSA encryption obsolete. ZME Science. Not exactly rocket science.
- ^ Brian Mastroianni. Dangerous escalation in ransomware attacks. CBS News. Breaking and Live Streaming News.
- ^ Dave Neal. Malware uses DDoS attacks to wreak havoc on Mac users. The Inquirer. News, reviews, and opinion for tech buffs .
- ^ Garrett Gross. Command and Control Server Detection: Methods . Alien Vault. United Security Management and Threat Intelligence.
- ^ Lily Hay Newman. Ransomware Turns to Big Targets—with Even Bigger Fallout. Wired. Tech News and Reviews.







