Dragon ransomware (Removal Instructions) - Recovery Instructions Included
Dragon virus Removal Guide
What is Dragon ransomware?
Dragon ransomware – a decryptable cryptovirus that avoids infecting users from China, Taiwan, and Hong Kong
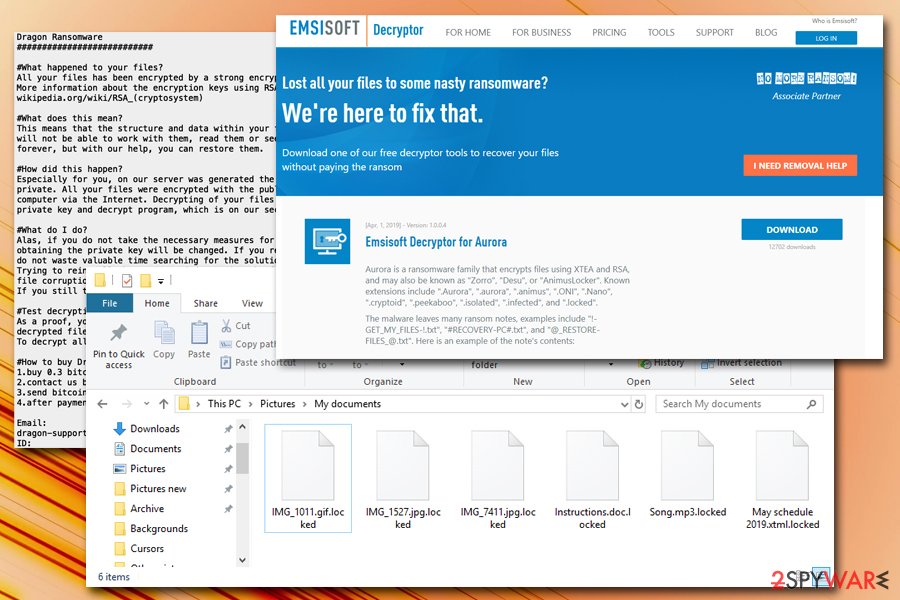
Dragon ransomware is a new variant of Aurora virus and first showed up in mid-August 2019. It is yet unknown what type of distribution methods hackers use, but victims are most likely to get infected with the malware strain when they open a malicious email attachment, visit a malicious site while using an outdated version of Windows, download software cracks, use unprotected Remote Desktop, etc.
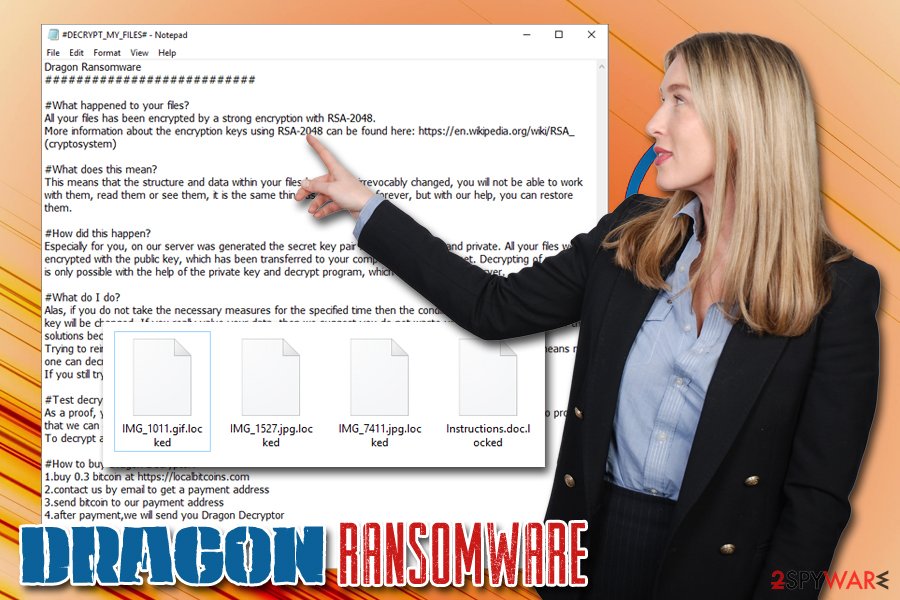
Once inside, Dragon ransomware modifies various system settings and starts the encryption process with the help of RSA-2048 cipher. Once complete, the content of the data is changed in a way that prevents users from accessing it. Besides, a .locked extension is added (note that this appendix has been used by many different ransomware developers), so there is a high chance that the affected users will notice the infection straight away.
Dragon ransomware then drops a ransom note #DECRYPT_MY_FILES#.txt which explains that culprits are selling the “Dragon Decryptor” for 0.3 BTC and suggest to contact them via dragon-support@pm.me email. Do not associate with hackers – there is no need to buy the tool they offering, as security researchers from Emsisoft released a decryptor that can recover all the Dragon virus locked files for free.
| Name | Dragon ransomware |
| Type | Cyprovirus |
| Encryption algorithm | RSA-2048 |
| File extension | .locked |
| Ransomware family | Aurora |
| Ransom note | #DECRYPT_MY_FILES#.txt |
| Contact | dragon-support@pm.me |
| Ransom size | 0.3 BTC |
| Additional information | Malware exists if it detects that the victim's IP is from China, Taiwan or Hong Kong |
| Background process | factura.exe |
| Decryption | Use a free decryption tool from Emsisoft |
| Removal | Employ professional anti-malware software like FortectIntego to get rid of Dragon ransomware |
As soon as Dragon ransomware enters the machine in one way or another, it changes Windows registry, deletes Shadow Volume Copies, opens/writes/copies system files, spawns a factura.exe process that runs in the background, loads various modules, etc.
After encrypting data, Dragon ransomware also contacts a Command & Control[1] server to send out a private RSA key for each of the victims (it is needed in order to decipher files). Finally, the malware encrypts pictures, documents, databases, videos, and other files, sparing only system data, among a few other exceptions.
A quite interesting fact is that Dragon ransomware will not start any system modification if the host computer IP is from China, Taiwan, or Hong Kong.[2] This is most likely because culprits themselves are from those countries and do not want to attract the attention of local authorities.
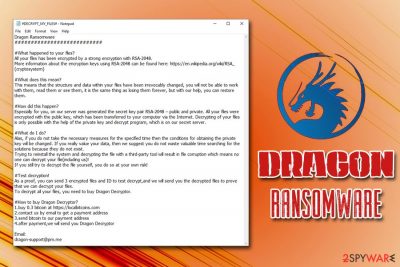
Crooks behind Dragon ransomware try to convince users that all the decryption tools are useless and they are the only ones that can provide an effective solution for file recovery. Here's what they say in the ransom note that is dropped in every folder of the PC:
Dragon Ransomware
############################What happened to your files?
All your files has been encrypted by a strong encryption with RSA-2048.
More information about the encryption keys using RSA-2048 can be found here: https://en.wikipedia.org/wiki/RSA_(cryptosystem)#What does this mean?
This means that the structure and data within your files have been irrevocably changed, you will not be able to work with them, read them or see them, it is the same thing as losing them forever, but with our help, you can restore them.#How did this happen?
Especially for you, on our server was generated the secret key pair RSA-2048 – public and private. All your files were encrypted with the public key, which has been transferred to your computer via the Internet. Decrypting of your files is only possible with the help of the private key and decrypt program, which is on our secret server.#What do I do?
Alas, if you do not take the necessary measures for the specified time then the conditions for obtaining the private key will be changed. If you really value your data, then we suggest you do not waste valuable time searching for the solutions because they do not exist.
Trying to reinstall the system and decrypting the file with a third-party tool will result in file corruption which means no one can decrypt your file(including us)!
If you still try to decrypt the file yourself, you do so at your own risk!#Test decryption!
As a proof, you can send 3 encrypted files and ID to test decrypt,and we will send you the decrypted files to prove that we can decrypt your files.
To decrypt all your files, you need to buy Dragon Decryptor.#How to buy Dragon Decryptor?
1.buy 0.3 bitcoin at https://localbitcoins.com
2.contact us by email to get a payment address
3.send bitcoin to our payment address
4.after payment,we will send you Dragon DecryptorEmail:
dragon-support@pm.me
Test decryption is also that many ransomware developers offer nowadays, as it might give victims a false sense of security and shows that the malicious actors can actually decrypt all the data. However, the unfortunate part is that they might not necessarily send the required key and the tool, even after the payment of 0.3 Bitcoin is processed. Thus, do not hesitate and proceed with Dragon ransomware removal.
Speaking of malware analysis, 49 vendors currently recognize Dragon ransomware and detect it under the following names:[3]
- HEUR/AGEN.1034529
- A Variant Of Win32/Filecoder.NVB
- W32/Chapak.A!tr.ransom
- Troj/Auroran-A
- Ransom.FileCryptor
- Trojan:Win32/Skeeyah.A!MTB
- Win32:Malware-gen, etc.
Therefore, you can use any of these tools or FortectIntego (based on Avira engine) to remove Dragon ransomware safely. Remember, if you start the file recovery process before that, all the data will be encrypted repeatedly. Besides, any files that you download from the internet will get immediately locked if the infection is still present.
Spam emails, outdated operating system and careless behavior online can put you into serious trouble
Ransomware is one of the most devastating malware families, and seems like it one of the most lucrative ones as well, as millions of users resort to paying the ransom when they can't find any other ways to recover their files. Unfortunately, that just fuels cybercrime, and more ransomware viruses are developed every day. To increase the profits, malicious actors also employ various methods to distribute malware, such as spam emails, exploits, web infects, fake updates software cracks, vulnerabilities, phishing sites, etc.
Security experts from Novirus.uk[4] advise users to stay vigilant and promote the following computer security tips:
- Install reputable anti-malware software and update its database in order to stop most malware from entering the machine;
- Make sure your operating system and the installed applications are patched with security updates;
- Never download cracks, keygens, or pirated software installers;
- Do not use the default port when using Remote Desktop and protect it with a strong password;
- Enable two-factor authentication for all your accounts;
- Install adblock or use a browser that blocks ads automatically;
- Backup your files!
Remove Dragon ransomware from your computer and recover your data for free
Before you proceed with file recovery, you need to make sure that Dragon ransomware removal was executed successfully. For that, you need to employ reputable anti-malware software like FortectIntego or SpyHunter 5Combo Cleaner and perform a full system scan. In some cases, malware might tamper with security applications, however, preventing them from working correctly or stopping their startup in the first place. In such a case, enter Safe Mode with Networking as explained below and do the scan from there.
Once you remove Dragon ransomware, you can then use the Decryption tool from Emsisoft to recover your locked data. If for some reason, the tool does not work for you, we provide an additional option for file recovery below.
Getting rid of Dragon virus. Follow these steps
Manual removal using Safe Mode
If you struggle to remove Dragon ransomware from your computer, you should enter Safe Mode with Networking and perform a full system scan:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Dragon using System Restore
If the previous method did not work for you, you could also try System Restore:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Dragon. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Dragon from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.Do not pay ransom to cybercriminals, as you might lose all your money in addition to personal files.
If your files are encrypted by Dragon, you can use several methods to restore them:
Data Recovery Pro is a tool for file recovery
This application is capable of recovering corrupted, damaged or accidentally deleted files. Nevertheless, some users reported that it helped them with ransomware-encrypted files.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Dragon ransomware;
- Restore them.
Make use of Windows Previous Versions Feature
This method is only possible if you had System Restore enabled before the Dragon ransomware infection occurred.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer will retrieve all your data in some cases
In case ransomware failed to remove Shadow Volume Copies, use ShadowExplorer to recover your files.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Make use of the Aurora decryption tool from Emsisoft
Download a free decryptor from Emsisoft to recover your data for free.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Dragon and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Kashinath T. Command And Control Servers : Things You Should Know. SecPod. Endpoint Security and Management Platform.
- ^ Jack. "Dragon Ransomware" appears to be a variant of Aurora. Twitter. Social network.
- ^ R.exe. Virus Total. URL and file analysis.
- ^ Novirus. Novirus. Cyber threat analysis and security news.





















