EnkripsiPC ransomware / virus (Removal Guide)
EnkripsiPC virus Removal Guide
What is EnkripsiPC ransomware virus?
Crucial facts about EnkripsiPC ransomware
EnkripsiPC virus is a new file-encrypting malware which mainly targets Indonesian users since the ransom message is published in the respective language. It clearly follows the manner of CryptoLocker since the ransom note has a striking resemblance to the mentioned virus. Though the former ransomware is said to have ended its notorious activity [1], its termination has inspired countless hacker wannabees to maintain the activity of file-encrypting malware. Interestingly, that this time the virus originates from Indonesia. The source contains the information that the virus encodes all files named in the Indonesian language. Nonetheless, it does not mean that users living in other regions are safe from this virtual menace. After the malware gets into a computer, it marks all files with .fucked file extensions. If you notice that all your files are blocked and contain the previous extension, do not panic but instead concentrate on EnkripsiPC removal. For that purpose, it would be better to rely on FortectIntego. This application will effectively remove EnkripsiPC and all its components.
CryptoWall, CryptoLocker, and Locky gave rise for the boom of ransomware which encrypt the files using AES algorithm. The effectiveness of such virtual threats lies in several factors. Firstly, the hackers communicate via the network granting anonymity or single-use email addresses. Secondly, AES encryption is easy to use but provide elaborate and difficult decryption keys which cannot be guessed. What is more, vivid and huge informational resources covering this particular topic enlightened many interested users on how to simply encode the files [2].
Likewise, ransomware business is booming. Though the market is controlled by several cyber gangs which regularly publish a new version of Locky (the latest – Osiris ransomware) and Cerber, the idea of profiting from ransomware appeals to the bright minds of different nationals. While US, UK, Germany, France, Japan and South Koreans and other nationals from wealthy states are a prevalent target, the crook started to take a glance to other countries of [3]. In this regard, this virus, alternatively known as Indonesian ransomware, v3 virus, or IDRANSOMv3 malware, also exclusively prefers targeting Indonesia netizens. For now.
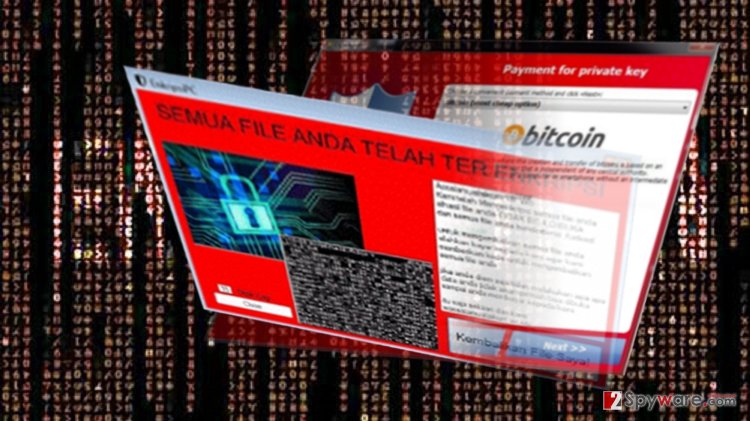
Furthermore, the hacker introduces themselves as humanpuff69. However, it is not known whether the ransomware will evolve into a major threat or it will flash like a temporary manifestation of a protest against something or someone. In comparison with the previous threat, it does not set a time limit. What is more, it demands a ridiculously low ransom – 50 000 or 100 000 Indonesian rupiahs which stand for approximately 4 USD and 7 dollars respectively. Even if the amount seems to be very low, do not expect to get your files back [3]. What is more, EnkripsiPC ransomware developers provide three email addresses in case you decide to contact them: fulldoang@gmail.com, mgfakhri@gmail.com, and muhlubaid69@gmail.com. Believe it or not, but the gearheads even provide their Facebook profile – muhammad.f.nazeeh. All in all, this ransomware does not compete with other notorious ransomware, but certain features suggest that with enough attention and development, EnkripsiPC malware might even evolve into a serious threat.
Distributing the malware
Though spam emails remain to be the main channel for spreading this sort of malware [4], this virtual infection seems to employ less popular methods of infiltration. Specifically, EnkripsiPC hijack might occur if you are not careful and install questionable tools. Virus researchers have detected that it might sneak into the device via corrupted installers, such as Installer Install Program. Afterward, Enkripsi PC malware leaves AutoUBLhack0.97.exe and CheatPBG161218.exe binaries. Then it becomes only a matter of time when the virus entangles your system.
EnkripsiPC eradication procedure
Due to the multiple new file-encrypting threats, the ransomware market has become one of the most profitable ones [5]. Fortunately, not all threats are complex. In this regard, EnkripsiPC removal should not cause any inconveniences if you entrust the procedure to FortectIntego or Malwarebytes. Update the program before the scanning the device. After that, restart the device and repeat the procedure. Keep in mind that the program does not decrypt the files. For that, you might use backups or additional tools. Check out our recommendations below. Remove EnkripsiPC virus fully and proceed to data recovery procedure.
Getting rid of EnkripsiPC virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove EnkripsiPC using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of EnkripsiPC. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove EnkripsiPC from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by EnkripsiPC, you can use several methods to restore them:
Data Recovery Pro solution
If your files are inaccessible, try using this tool to recover them.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by EnkripsiPC ransomware;
- Restore them.
Opting for Windows Previous Versions function
If System Restore is enabled, retrieve the previously saved copies of your documents.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
The usefulness of ShadowExplorer
The main advantage of this utility lies in recreating the files by employing shadow volume copies. They are automatically generated by Windows OS and rarely ransomware threats delete them.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from EnkripsiPC and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Matthew Hughes. CryptoLocker Is Dead: Here’s How You Can Get Your Files Back!. MakeUseOf. Technology, Simplified.
- ^ Are you Protected?. Microsoft. Your potential. Our Passion.
- ^ Graham Cluley. FBI: No, you shouldn’t pay ransomware extortionists. WeLiveSecurity. News, views, and insight from the ESET security community.
- ^ JAMES RODGER. Fraudulent email scam targeting Birmingham university students. Birmingham Mail. Birmingham News, features, and sport .
- ^ Lucian Constantin . Ransomware became one of the top threats to enterprises this year. ComputerWorld. The Voice of Business Technology.







