Ffshrine virus (Microsoft Support Scam) - Virus Removal Guide
Ffshrine virus Removal Guide
What is Ffshrine virus?
Ffshrine virus – a dangerous Trojan related to a popular Final Fantasy Shrine Forum
Ffshrine virus is a malicious Trojan horse[1] infection that might have been injected into Ffshrine (“Final Fantasy Shrine Forum”) domain. Initially, registered forum users started reporting about unusual Norton AV alerts Web Attack: Formjacking Website 2 showing up when browsing the forum. The detection was flagged as High Risk and initially considered as a false positive detection, though later it has been revealed that the URL of the domains FFshrine.net and Ffshrine.org has been hacked and misused for Ffshrine Trojan distribution.
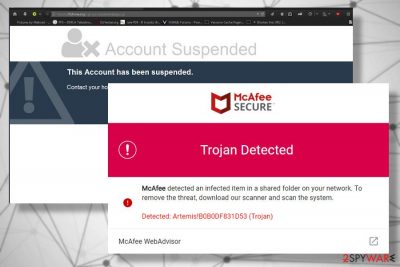
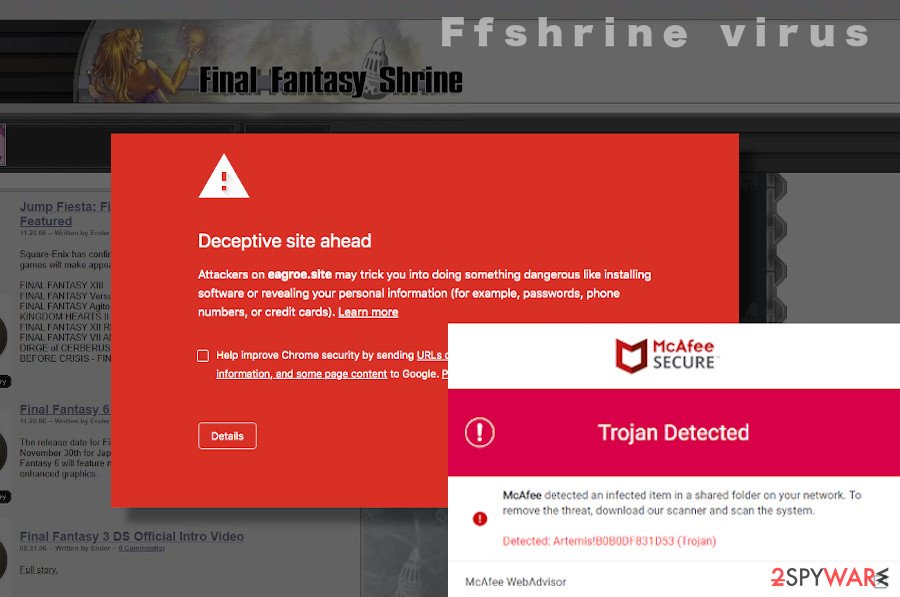
Ffshrine virus on the infected domains typically manifests in the form of fake AV security software alerts that urge people to download software to eliminate the infection. According to cybersecurity researches, criminals misuse many famous names of AV tools, including Norton, McAfee, Windows Defender, and others. One of the malicious pop-up imitating McAfee design warns about Trojan detection Artemis!B0B0DF831D53 found in a shared folder of the network. It’s essential to draw attention to the fact that such notifications show up for people who are not using McAfee. Thus, clicking on a download link may lead to the infiltration of a dangerous Trojan, Spyware, key logger, or activate ransomware payload.
| Name | Ffshrine |
| Type | Trojan horse |
| Distribution means | Hacked websites, fake AV alerts, backdoor access, exploit kits, rootkits, Trojan downloaders, Trojan droppers |
| Precautions | Keep a powerful antivirus installed. Never click on online pop-ups warning about virus infection and urging to download a scanner for free. |
| Symptoms | System crashes, high CPU usage, malicious processes running in the background, questionable programs installed on the system, terminated AV tools. |
| Removal and repair | Viruses like Ffshrine trojan can be terminated with a reputable antivirus program, for example SpyHunter 5Combo Cleaner or Malwarebytes. Nevertheless, we strongly recommend eliminating the system's damage with a FortectIntego repair tool. |
Yet another misleading pop-up Web Attack: Formjacking Website 2 detection by Norton raises more questions about its authenticity. As Norton explains, Formjacking[2] is a type of website hack when criminals inject malicious JavaScript codes, which may result in a disclosure of information, such as credit card details, logins, and similar. Several Norton users reported such alerts of security forums and assured red that the Formjacking Website 2 detection pop-up indicates the IP address from which the attack has been initiated. Therefore, the warning delivered by Norton can hardly be treated as a false negative. However, it can only be genuine if the PC runs the Norton security suite. Otherwise, clicking on possibly fake AV download pop-up may result in a Ffshrine virus infiltration.
Forum.ffshrine, which has had a considerable number of registered users before the closedown, has been represented as a forum where people can discuss the Final Fantasy series of Japanese Role-Playing Games. However, only the minority of the users were aware of such a game at all. The primary service of this questionable, though very popular, forum was to share original soundtrack albums from media like animes, games, and movies in archived .zip, .rar, .tar, and other forms. Such activity has been approved by most of the registered users who seek free services, but at the same time disapproved by opponents of illegal free file-sharing services. Keep in mind that domains that initiate free file-sharing activities are a great target for hackers and other cybercriminals who may seek to cause the website's crash or distribute malicious components via downloadable database.
If the Ffshrine Trojan virus is launched on the system, it may perform a multitude of malicious activities on the network. Trojans are used by hackers to gain access to people’s data, analyze keystrokes, or gain backdoor access to the system. Such and similar cyber infections can:
- Remove pieces of information stored on the system;
- Block access to particular data and files;
- Modify the system’s registry entries and compromise other crucial components;
- Copy data and transmit it to remote servers;
- Diminish PCs performance and disrupt network connections;
- Block AV tools and self-replicate after inappropriate removal;
- Open backdoor access to ransomware and other viruses.
Ffshrine virus and similar may be difficult to detect, and as they tend not to disclose their presence directly. A Trojan may reside silently and keep modifying the system’s registry entries and weakening its core. The presence of the virus may manifest as software crashes, BSODs[3], questionable processes running on the background, high CPU usage, and similar. While the slow system and its malfunctioning may be irritating, the most significant risk Trojans like Ffshrine virus pose is a ransomware or spyware download. These infections may encrypt documents and demand a ransom in exchange for decryption software. At the same time, spyware may capture keystrokes and take screenshots to steal banking information, ID card numbers, and other most sensitive details.

For those who have any suspicions that the Ffshrine virus may have entered the system, we highly recommend rebooting the system into Safe Mode with Networking and initiating a full system scan. Unfortunately, there’s no way to remove FFshrine or other Trojans of its type manually. The longer the dangerous program keeps active on the system, the higher is the risk of damage.
Fake online pop-ups used to spread Trojans actively
A Trojan related to the Ffshrine domain is a dangerous infection, which may cause the system’s crashes and initiate data leakage. According to experts, it is distributed via fake pop-ups imitating trustful AV security tools. Perfectly emulating the design and other features, these pop-ups might have tricked thousands of users and lure them into cybercriminals’ hands.
The forum that has been found spreading the virus is currently down. As soon as a malicious JavaScrip was optioned, the widespread discussion and music streaming domains were closed entirely and are not reachable up-till-now. Nevertheless, this fact does not guarantee that the Ffshrine or its clones are not circulating on the Internet via other popular hacked domains.
In addition to infected domains, such and similar cyber infections can get inside PCs via backdoor access, exploit kits, rootkits, Trojan downloaders, Trojan droppers, and similar highly suspicious means. Therefore, it’s essential to ensure the full system’s protection. First of all, rely on a comprehensive AV security tool, which has a powerful virus detection engine and make sure to download required updates regularly. Moreover, do not access suspicious websites and ignore misleading pop-ups, banners, hyperlinks, and other content that can initiate redirects to unknown domains. Last, but not least recommendation is to pay close attention to freeware and be careful with torrent websites since they tend to have security vulnerabilities making them easily accessible to criminals. The system’s security with a pack of reliable programs and your awareness about dangers online should be sufficient to maintain your safety.
Guide for FFshrine virus removal
If you consider your PC infected with a Trojan, there’s only one way to get rid of it, i.e., a full system scan with a professional AV tool. If you have already tried, but Ffshrine removal failed without even getting started, the virus may be running the command to block the antivirus program. To make it run, please restart the system into Safe Mode with Networking, as explained below. In case you don’t have reliable antivirus software, we recommend using one of these programs: SpyHunter 5Combo Cleaner or Malwarebytes.
However, Ffshrine removal should also be followed by a careful system’s repair. As we have pointed out earlier, Trojan infections contaminate a multitude of entries on the Registries, corrupt running processes, delete libraries, and cause similar damage. Since antivirus programs do not perform optimization tasks, we recommend fixing virus damage with FortectIntego.
Getting rid of Ffshrine virus. Follow these steps
Manual removal using Safe Mode
If your security software is blocked, before starting Ffshrine removal restart the system into Safe Mode with Networking. The guide below will help you to do that.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Ffshrine and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting trojans
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ What is a Trojan Virus?. Kaspersky. Cyber Security Solutions.
- ^ What is Formjacking and How Does it Work?. Norton. Industry-leading antivirus and security software.
- ^ How to fix Windows 10 BSOD Error 0x00000139 (KERNEL_SECURITY_CHECK_ FAILURE)?. Ugetfix. A website helping computer users fix various errors and problems.














