Findinfo.us browser hijacker (virus) - Chrome, Firefox, IE, Edge
Findinfo.us browser hijacker Removal Guide
What is Findinfo.us browser hijacker?
Findinfo.us – a browser hijacker that fails to perform basic search functions

Once a browser hijacker is installed on your computer, your browsing experience is not going to be the same. These potentially unwanted programs change the settings of Google Chrome or another web browser in order to modify the way users perceive website discovery and exploration. To be precise, once the unwanted app is installed, your homepage, new tab address as well as search bar change; in this case, you would see Findinfo.us as your starting page once you open the browser.
One of the main reasons why this app is considered a potentially unwanted program is its distribution methods. In most cases, users find it installed on their systems seemingly out of nowhere, and they claim that they never install it on purpose. This can be attributed to a deceptive scheme known as software bundling – many freeware[1] websites employ it.
Another reason to remove Findinfo.us is its operation, as it changes the way you browse the web – not in a good way. Not only does it change your browser preferences but also hijacks the search function, which you have to use to look for something online. You would quickly notice that your searches do redirect to Google or other preferred provider but rather
| Name | Findinfo.us |
|---|---|
| Type | Browser hijacker, potentially unwanted program |
| IP address | 104.21.17.195 |
| Distribution | Freeware bundles, deceptive ads |
| Symptoms | Search results are filled with sponsored links and ads; homepage and new tab address is set to Findinfo.us; overall increased amount of advertisements |
| Risks | Installation of other potentially unwanted programs, privacy risks due to information gathering practices, financial losses |
| Removal | To get rid of the unwanted browser extension, you should access the settings section of your browser. You should also check for other PUPs or malware with SpyHunter 5Combo Cleaner or another powerful security tool |
| Optional steps | Cleaning your browsers is just as important as removing the extension that caused the unwanted activities. For that, check the instructions below or employ FortectIntego |
Why is Findinfo.us not worth your time
First of all, it is worth mentioning that many people download browser hijackers inadvertently; less experienced PC users might not even realize that their homepages have been hijacked. Nonetheless, there is a reason why this distribution method is so widely used – people don't want to have their browser hijacked.
To compensate, PUP creators often use fancy words and slogans to attract users. They often boast about the “enhanced search results” or “improved web browsing experience.” In some cases, the hijackers even include some type of function or a theme that should be useful in their name, e.g., MovieSearchOnline, ProSportSearch, BestADSBlock, or Rick Tab.
In reality, all these promises are fake, and the allegedly “improved” search function is nothing more butt sponsored content that helps the developers to monetize user clicks. This is why search results are commonly inserted with ads; some users might not even realize that they
If we look at Findinfo.us, the pattern prevails. According to the main page's “About Us” section, this app is capable of the incredible:[2]
The best results from the entire Internet
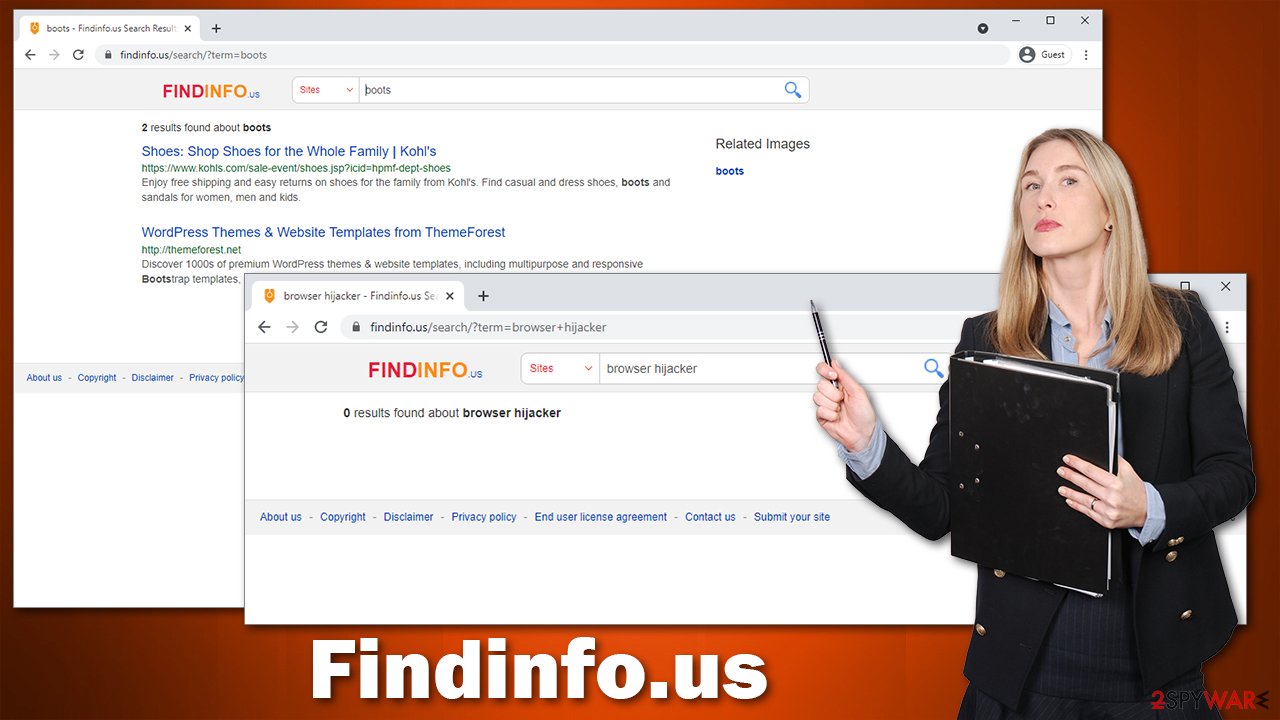
This is a rather bold statement – something that almost every browser hijacker maker tends to state. According to the statement, “Findinfo.us searches multiple types of information from multiple sources to generate optimal results.” This sounds very promising, although the results are very disappointing.
After entering a search query “browser hijacker,” no results were found. Even such a simple keyword as “boots” returned a total of two results. Even Alta Vista (an ancient search provider used in the 90s) was able to provide hundreds of thousands of hits, and we are getting two links for “boots”?
Besides this useless “search” function, it is important to note that the hijacker collects various non-personal information about users. For example, IP addresses or search queries might be recorded. This is done in order to optimize the targeted advertising practice, which retains revenue from user clicks on ads.
All in all, we strongly recommend you remove the app from your device. Not only does it changes the settings of your browser but also fails to provide any relevant information via its search. Below you will find all the details needed to succeed at this process.
Eliminate Findinfo.us correctly
There could be two ways a browser hijacker is installed on your device – either on the system level (as an application) or on the browser (as an extension). In most recent years, most PUP producers tend to use the latter option, as it is much cheaper and convenient.
If you have previously used browser extensions, you should have no problems with deleting this one. It might be hiding under different names, however, so it might be difficult to determine which app is causing the unwanted browser behavior. Well, if you see something you never installed – this is your culprit. If you need help in doing this, proceed with the following steps:
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the window's top-right).
- Select Add-ons.
- In here, select the unwanted plugin and click Remove.
![Remove extensions from Firefox Remove extensions from Firefox]()
MS Edge (Chromium)
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.
![Remove extensions from Chromium Edge Remove extensions from Chromium Edge]()
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
Alternatively, the app could be installed on your system rather than a browser. In this case, you need to access the Control Panel (Windows) or Applications (Mac) sections to eliminate the unwanted app for good. Here's how it's done:
Windows
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.
![Uninstall from Windows 1 Uninstall from Windows 1]()
- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.
![Uninstall from Windows 2 Uninstall from Windows 2]()
Mac
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)
![Uninstall from Mac 1 Uninstall from Mac 1]()
To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
![Uninstall from Mac 2 Uninstall from Mac 2]()
If you want to avoid all these manual steps and rather remove Findinfo.us automatically, we recommend you perform a full system scan with SpyHunter 5Combo Cleaner or Malwarebytes. If you have not installed the app yourself, there is a good chance that more PUPs are present on your device. In worst cases, there could even be malware lurking in the background. Security software can take care of all of it automatically so you won't have to worry about anything.
Why is it important to clean your browser
As an overall precautionary measure, security experts[3] strongly recommend users clean their browsers from time to time. There are many components and elements that are saved on your computer (known as caches); they allow previously visited websites to be loaded faster. At the same time, these caches might also include some malicious content (whatever is present on the page).
Besides, browsers also store cookies and similar tracking mechanisms. These can remain on the system until they are deleted, providing the cookie owner to continue tracking activities on your device. You can clean your browsers via browser settings, although using FortectIntego is a much quicker option. It can also serve as a complementary tool for anti-malware, as it is great for dealing with problems that might arise due to the aftermath of malware or adware infections.
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.
![Clear cookies and site data from Firefox Clear cookies and site data from Firefox]()
MS Edge
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.
![Clear browser data from Chroum Edge Clear browser data from Chroum Edge]()
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
How to prevent from getting browser hijacker
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.












