FlowAds browser extension (Free Guide)
FlowAds browser extension Removal Guide
What is FlowAds browser extension?
FlowAds promises to improve search results but instead inserts ads into them
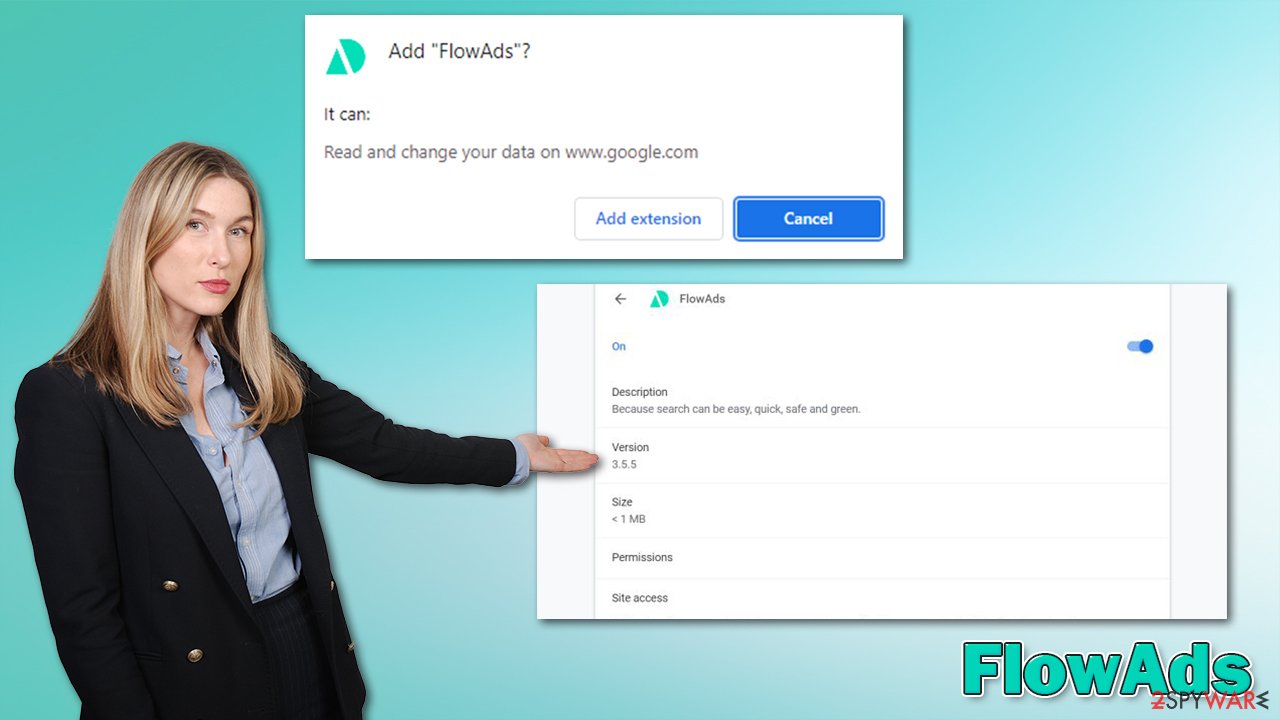
FlowAds is a browser extension that showed up on the internet in fall 2021. While it may look at your regular add-on that is meant to enhance your browsing experience, it is actually a type of potentially unwanted application[1] known as a browser hijacker. It is common for users to find it installed on Google Chrome or another browser without expecting it to be there.
This happens because PUPs often employ deceptive distribution tactics such as software bundling or misleading advertising. In some cases, people might also install these apps after being tricked by fake promises of the allegedly better browsing experience, which in reality, it is anything but that.
Once installed, the extension changes the way the search function operates. While many of such apps alter the homepage and new tab function, FlowAds hijacker does not, although it does not mean that it's not doing what it was set to do.
The major difference with the browser hijacker installed is the search results. They are not the same as they used to, as plenty of ads are inserted at the top. These links might not always be secure, as they may promote deceptive software or services that are useless. Hence, you might end up losing money or get more potentially unwanted programs installed on your device.
Besides, browser hijackers are known for their data tracking practices. It is used to benefit from targeted advertising more, although this might put users' privacy at risk. All in all, we recommend you remove FlowAds from your system. Below you will find all the information required to do just that.
| Name | FlowAds |
|---|---|
| Type | Browser hijacker |
| Distribution | Potentially unwanted applications usually hide in software bundles or are distributed via various deceptive ads over various websites |
| Symptoms |
|
| Risks | Installation of other suspicious apps, privacy risks due to information gathering practices, exposure to inaccurate search results, etc. |
| Removal | Potentially unwanted programs can usually be removed manually, although automatic elimination with SpyHunter 5Combo Cleaner can be much quicker and more effective |
| Additional steps | After you eliminate all browser hijackers and other PUPs from your system, make sure you clean your web browsers and repair system files. You can also do that automatically with FortectIntego |
How browser hijackers are distributed
If you have been wondering how you found a browser extension on your system without permitting it to be there – you should check the recently installed freeware. Most developers who make PUPs use third-party websites to distribute their apps, and software bundling is the primary method.
This deceptive marketing technique has been around for many years now, and, essentially, there's nothing wrong with offering users to try out optional software. However, it all comes down to how this system is implemented, and third-party websites use plenty of tricks to make people install apps they never wanted or needed.
Here are a few tips from security experts[2] that could help you avoid this:
- If possible, download apps from official sources only;
- During the installation, always pick the Advanced/Custom mode instead of Recommended/Quick one;
- Watch out for misplaced buttons – “Skip offer” button is commonly placed on the left side of the window, making people click on “Accept offer” on the right when in a hurry;
- Read the fine print;
- Untick all the checkmarks from the pre-selected boxes that would allow installation of optional apps;
- Install powerful anti-malware software, such as SpyHunter 5Combo Cleaner or Malwarebytes, to warn you about the PUPs and malware.
Browser hijackers can also be found on official sources such as Chrome Web Stire – FlowAds's official website directs users there. Hundreds of apps get removed from the store regularly, although it might take some time before that happens. Likewise, inserting ads into users' searches is not something that is considered malicious (especially when Google is well known for its focus and advertising),[3] although it does not provide any positive experiences for users.
The “enhanced” search results
The Internet changed the lives of many people – we can now find out when's the next bus coming, pay our bills, order stuff online, and watch video streams without any lag or other issues. With the internet's popularity increasing, speeds and usability has been drastically improved; it has also become a much safer place than it used to be 20 years ago.
That being said, internet browsers have also evolved – they became much more customizable, and new features were implemented over the years. Browser extensions are now considered an integral part of most users' web browsing routines, which is understandable considering how much functionality these tiny apps bring in. They are lightweight and easy to develop.
However, not all extensions are useful, and browser hijackers have existed in this form for a while (which means that they are not installed on the system level but rather browser level). Once installed, they usually change the browser's homepage and new tab settings, although FlowAds doesn't seem to do that.
Visually, the app does not change anything. If you are using Google as your primary provider, that option will remain, although you will notice some changes when it comes to the search results. The description of the hijacker sounds as follows:
With this extension, you can get optimized and additional results from other search engine sources.
Some of these results are sponsored.
Google is great but Google + FlowAds is better.
In fact, all of the “additional” search results are sponsored, so all this extension does is increase the number of ads users see every time they are looking up something on the internet. Besides, it also tracks your user data such as IP address, ISP, browser information, websites visited, and much more. These details can be useful when advertising certain products to certain users.
All in all, we recommend proceeding with the hijacker's removal. In the next section, you will find all the information needed to execute that correctly.
Remove FlowAds browser hijacker correctly
Browser hijackers are considered minor computer infections – more like nuisances, although they should not be considered completely safe or useful either. As previously mentioned, PUPs commonly use deceptive distribution methods which make users find them on their systems without allowing them to do so. Usually, there should be no problems with FlowAds removal – proceed with the step-by-step guide below
Delete the extension
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the window's top-right).
- Select Add-ons.
- In here, select the unwanted plugin and click Remove.
![Remove extensions from Firefox Remove extensions from Firefox]()
MS Edge (Chromium)
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.
![Remove extensions from Chromium Edge Remove extensions from Chromium Edge]()
MS Edge (legacy)
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.
![Remove extensions from Edge Remove extensions from Edge]()
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
Clean your browsers
Data tracking is one of the integral parts of browser hijackers, so they commonly use cookies, web beacons, and other tracking technologies for this purpose. Cookies and caches remain on the browser even after the unwanted extension is eliminated, so you should wipe clean those sections. You can either employ FortectIntego to do this quickly or follow these steps to do it manually:
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content, and press Clear.
![Clear cookies and site data from Firefox Clear cookies and site data from Firefox]()
MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.
![Clear browser data from Chroum Edge Clear browser data from Chroum Edge]()
MS Edge (legacy)
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.
![Clear Edge browsing data Clear Edge browsing data]()
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
Check for other unwanted software
Finally, you should not dismiss the possibility that there are additional potentially unwanted programs or even malware installed on your device. This is especially true if you are using older operating system versions and don't employ security software. Thus, we strongly recommend you download SpyHunter 5Combo Cleaner or Malwarebytes and perform a full system scan to automatically delete all the malicious files and programs.
How to prevent from getting browser hijacker
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Potentially unwanted program. Wkipedia. The free encyclopedia.
- ^ Novirus. Novirus. Cybersecurity news and malware insights.
- ^ Personalized advertising. Google. Official site.










