Followtube.biz pop-up (fake) - Free Instructions
Followtube.biz pop-up Removal Guide
What is Followtube.biz pop-up?
Followtube.biz spams users with commercial content

Followtube.biz is classified as adware because it displays unwanted adverts on users' computer screens even when the browser is closed, potentially tracks browsing behavior, and provides it to third parties. Ads shown by this website are unfiltered, so they can lead users to other shady websites where they can be tricked into sharing their personal information and download harmful software.
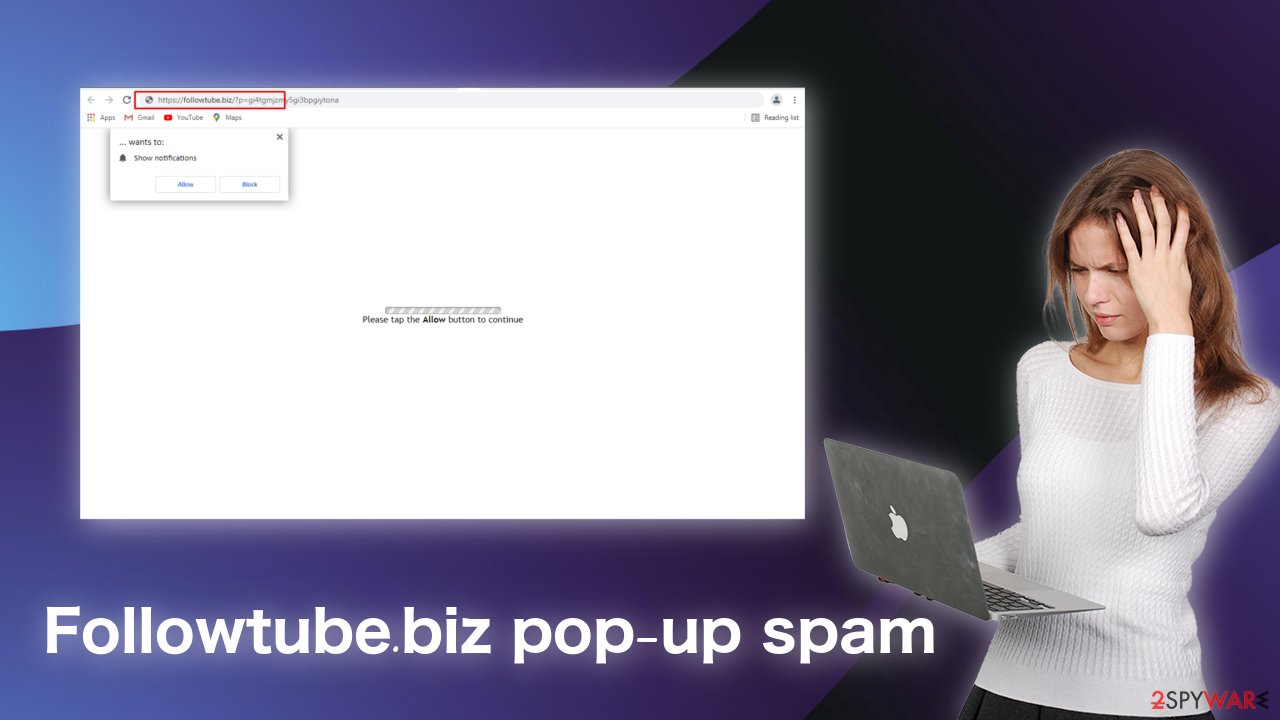
Upon stumbling on this page, people are met with a request to grant permission to send push notifications. Often, this is done using deceptive tactics. Some of the shown messages can urge you to do this by asking you to press the “Allow” button to watch a video, continue further, confirm your age, and so on. Without looking, people can miss that the button actually grants permission to send pop-ups directly to their screen even when the browser is closed.
In this emerging digital world, it is important to distinguish all types of different threats you can run in while surfing the web.[1] Although adware is not malware and should not cause any damage to your system, you should still eliminate it to make your browser work as smoothly as possible. Taking care of knowing how your personal data is used can help protect it.
| NAME | Followtube.biz |
| TYPE | Adware, potentially unwanted program |
| DISTRIBUTION | Suspicious websites, freeware |
| SYMPTOMS | Push notification spam, advertisements annoyingly popping up on the screen |
| DANGERS | Promoted links can lead to unsafe websites where users can get tricked into giving away their personal information, downloading PUPs |
| ELIMINATION | Delete website permissions by going to your browser settings |
| FURTHER STEPS | After removal, it is advised to use FortectIntego to try and fix any damage caused by adware |
It might not be possible to prevent every personal data breach, but you can minimize the risk significantly by making sure you handle personal data with care. Learning to identify suspicious websites and scam ads[2] will give you a better chance of avoiding unwanted guests entering your digital bubble.
Social engineering methods have significantly increased in popularity among cybercriminals since the pandemic started as people spend more time on their computers. Messages containing shock value, clickbait to get you to act quickly on your emotions work much better than regular ways of spreading their influence. This is why Followtube.biz is not clear about the fact that it wants to send you push notifications, instead trying to trick you by promising you will get something in exchange when this is a lie.
Announcements of prizes like a vacation on a cruise ship or a brand new iPhone are commonly used by scammers, so you should always keep your guard up and not believe everything you see while browsing. Google, Mozilla, Chromium do not just pick random visitors using their search engines and give away freebies.
When you suddenly get redirected to a website you did not intentionally go to, it might be because of adware action. Inspect the content of the page and if you see anything suspicious, do not interact with it and just close the window. If an advertisement pops up on your screen, look for any mistakes in the wording, decide if the imaging looks professional, modern, and high quality.
Adware is spread on third-party websites
Potentially unwanted programs or otherwise called PUPs/PUAs, commonly come as a package with a method known as software bundling. Usually, this occurs when users download free or “cracked[3]” versions of software from unofficial sources. If they skip through the installation process, they miss additional files that are hiding and then start experiencing some erratic behavior.
It is crucial not to rush things and chose “Custom” or “Advanced” installation methods. This way, you will go through all the stages, will be able to read through the License Agreement and Privacy Policy, and check the contents. If you see any unrelated files next to the application you need, make sure to untick the boxes not far from their names.
Sometimes PUAs come disguised looking as handy tools that will provide you a lot of value. This could be antivirus software, video, and image editing programs, VPNs, etc. So if you see these types of apps when trying to download something else, do not accept, even though it may be tempting.
You can add an extra layer of security by frequently scanning your machine with trusted professional security software SpyHunter 5Combo Cleaner and Malwarebytes, which will help prevent malicious and unwanted programs from getting far in their operations.
Removing intrusive web pages like Followtube.biz manually is significantly easy. By following our guide step-by-step, you should successfully accomplish this.
Remove unwanted notifications from Google Chrome (desktop):
- Open Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate Privacy and security section and pick Site Settings > Notifications.

- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.

Remove unwanted notifications from Mozilla Firefox:
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click Settings button next to it.

- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.

Get rid of notifications on Safari:
- Click on Safari > Preferences…
- Go to Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.

Remove unwanted notifications from MS Edge:
- Open Microsoft Edge, and click the Settings and more button (three horizontal dots) at the top-right of the window.
- Select Settings and then go to Advanced.
- Under Website permissions, pick Manage permissions and select the URL in question.

- Toggle the switch to the left to turn notifications off on Microsoft Edge.

MS Edge (Chromium):
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.

Clean your cookies and cache
If you want to limit the information websites collect about you and send to third parties which use it how they like, you should clean your browsers' cookies and cache from time to time and decline cookies when it is an option.
To clean your browser manually, follow the instructions below, or FortectIntego can do this for you automatically, saving you time and the struggle to remember.
Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies, and other site data, as well as Cached images and files.
- Click Clear data.

If that did not help, or you could not identify the website causing these intrusive pop-ups, you can try resetting your browser altogether.
Reset Google Chrome:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Getting rid of Followtube.biz pop-up. Follow these steps
Uninstall from Android
Uninstall unwanted programs from Android device:
- Go to Settings -> Apps/Applications.
- Expand the full list of the installed apps.
- Scroll through the list and tap on a suspicious application once.
- Tap on it and select Uninstall.
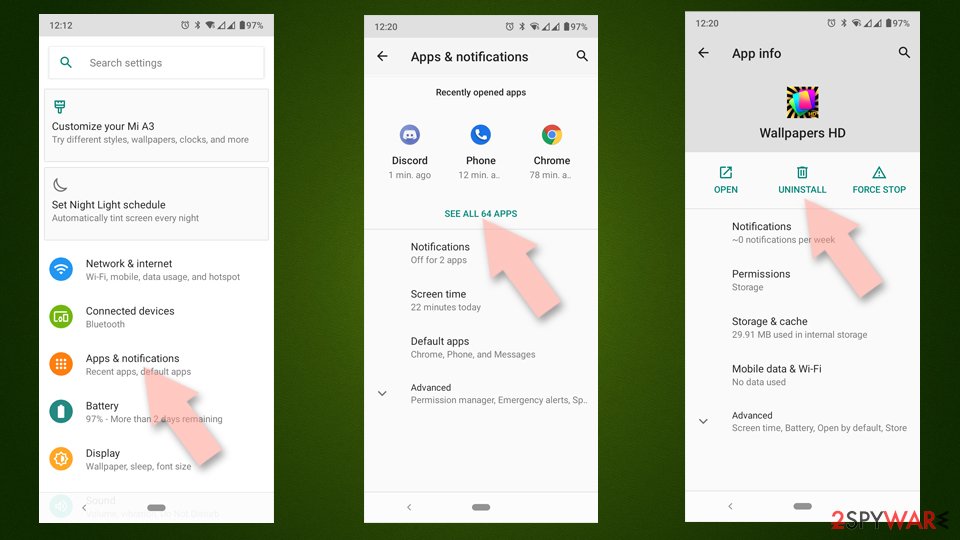
- Reboot the device.
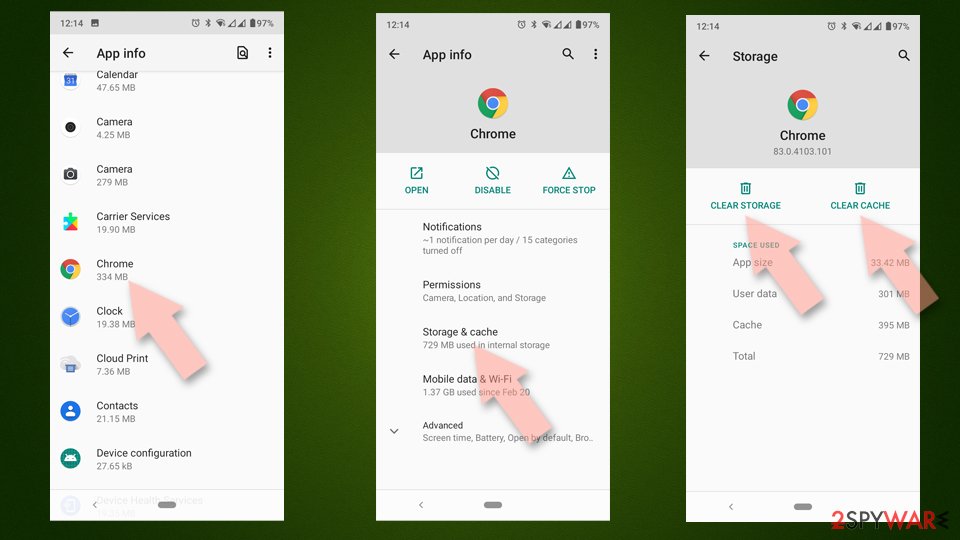
Clear Storage and data files on Android from Google Chrome or other apps:
- Go to Settings > Apps/Applications.
- Expand the full list of the installed apps.
- Tap on Chrome and select Storage & cache.
- Clear storage and clear cache of the app.
If you are seeing ads on top of other apps but are not sure what is causing it, perform the following steps:
- Go to Apps/Applications.
- Tap Advanced.
- Select Special App access.
- Tap on Display over other apps.
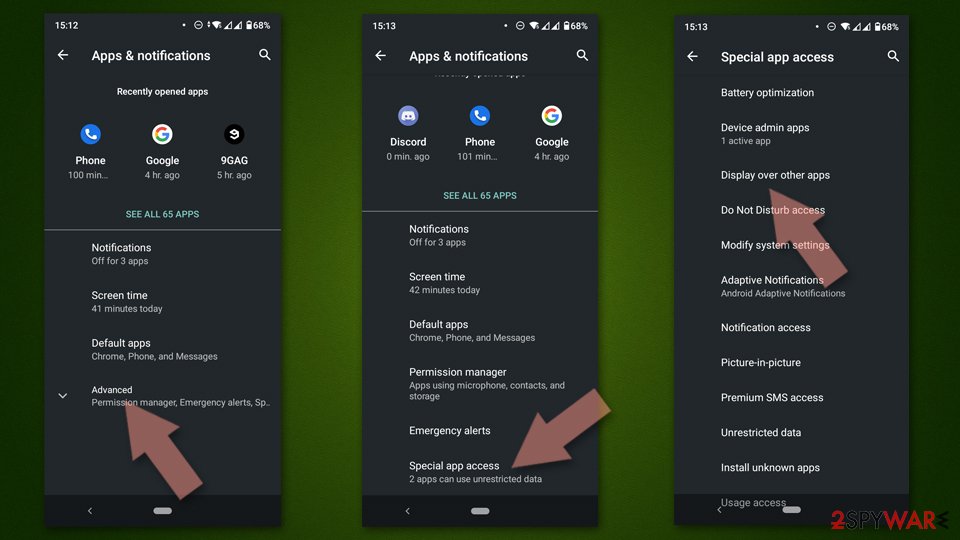
- Eliminate apps with these access rights enabled.
How to prevent from getting adware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Esteban Borges. Top 10 Common Network Security Threats Explained. SecurityTrails. Security Blog. Hacking.
- ^ Chris Fox. Facebook and Google 'failed to remove scam adverts'. BBC. Technology News.
- ^ Wikipedia. Software cracking. Wikipedia. Free Encyclopedia.
