Gachimuchi ransomware (virus) - Recovery Instructions Included
Gachimuchi virus Removal Guide
What is Gachimuchi ransomware?
Gachimuchi ransomware encrypts your files to later ask for a ransom from you
Gachimuchi ransomware is a data-encrypting virus that targets Windows machines. The malware was first observed making rounds in the middle of June 2022, although it does not seem to belong to either of the bigger ransomware strains.
Once on the system, the virus would encrypt pictures, videos, music, documents, databases, and other valuable files by using a strong encryption algorithm,[1] making the data completely useless. During this time, each of the personal files acquires a “.Gachimuchi” extension, along with additional affixes consisting of personal ID and “BillyHerrington.”
It is worth noting that files affected by ransomware are not corrupted (even if it may seem so) but rather locked behind a special, unique password based on a long string of alphanumeric characters. It is impossible to guess it or acquire it in any other way – it is stored on cybercriminals' servers.
It is not surprising that Gachimuchi ransomware authors are unwilling to give the decryption key for free, and demand a ransom to be paid in exchange. According to the #HOW_TO_DECRYPT#.txt ransom note, victims should contact crooks via @Gachimuchi on ICQ or using the gachimuchi@onionmail.org email. Avoid any contact with ransomware developers and instead, use alternative solutions we provide below.
| Name | Gachimuchi virus |
|---|---|
| Type | Ransomware, file-locking malware |
| File extension | [ID].[BillyHerrington].Gachimuchi |
| Ransom note | #HOW_TO_DECRYPT#.txt |
| Contact | @Gachimuchi on ICQ or gachimuchi@onionmail.org |
| File Recovery | The only secure way to restore files is by using data backups. If such is not available or were encrypted as well, options for recovery are very limited – we provide all possible solutions below |
| Malware removal | Disconnect the computer from the network and internet and then perform a full system scan with SpyHunter 5Combo Cleaner security software |
| System fix | Once installed on the system, malware might seriously damage some system files, resulting in crashes, errors, and other stability issues. You can employ FortectIntego PC repair to fix any of such damage automatically by replacing system corruption |
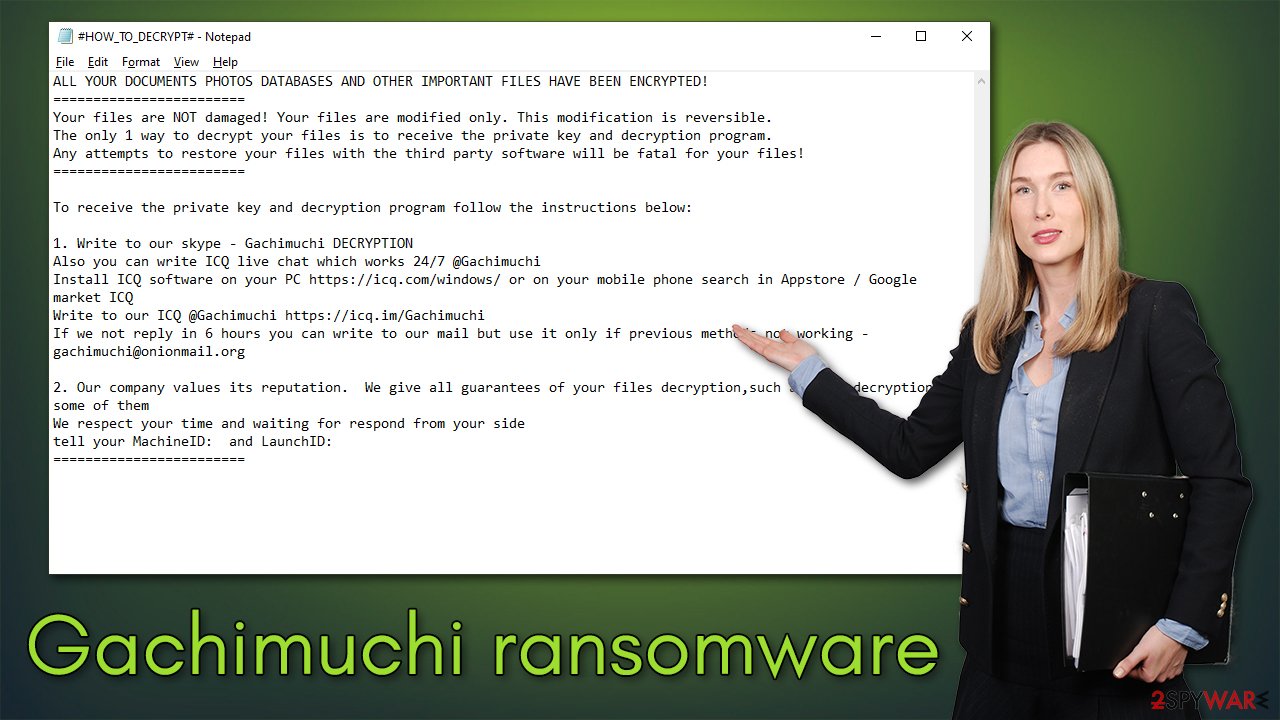
Ransom note explained
The ransom note has become an integral part of ransomware's operation. It provides all the crucial information that victims should know; it includes an explanation of what happened to their files, what they need to do to retrieve them, and how to contact the attackers. Usually, the note is delivered in a simple TXT format for users to easily access the important information – as is the case with the Gachimuchi virus.
The data encryption process usually lasts mere seconds before its complete and after assigning a unique ID to the affected machine, malware delivers the #HOW_TO_DECRYPT#.txt ransom note, which reads:
ALL YOUR DOCUMENTS PHOTOS DATABASES AND OTHER IMPORTANT FILES HAVE BEEN ENCRYPTED!
========================
Your files are NOT damaged! Your files are modified only. This modification is reversible.
The only 1 way to decrypt your files is to receive the private key and decryption program.
Any attempts to restore your files with the third party software will be fatal for your files!
========================To receive the private key and decryption program follow the instructions below:
1. Write to our skype – Gachimuchi DECRYPTION
Also you can write ICQ live chat which works 24/7 @Gachimuchi
Install ICQ software on your PC https://icq.com/windows/ or on your mobile phone search in Appstore / Google market ICQ
Write to our ICQ @Gachimuchi https://icq.im/Gachimuchi
If we not reply in 6 hours you can write to our mail but use it only if previous methods not working – gachimuchi@onionmail.org2. Our company values its reputation. We give all guarantees of your files decryption,such as test decryption some of them
We respect your time and waiting for respond from your side
tell your MachineID: and LaunchID:
========================
It is interesting how the attackers claim they value the “reputation of the company,” completely disregarding the fact that infecting users' machines with malware is despicable and illegal. Communicating with crooks only assures them that their illegal business works as intended and only prompts them to infect more victims in the future. This is one of many reasons why the FBI and other authorities recommend not paying the ransom.[2]
Gachimuchi ransomware removal
Instead of communicating with cybercriminals, we recommend looking for alternative ways of restoring files and remediating your computer. The first task is to make sure that the malware and all its components are removed from the system thoroughly, and for that, you need SpyHunter 5Combo Cleaner, Malwarebytes, or another powerful anti-malware solution.
Manual elimination is possible, although it is not recommended, as it requires extensive IT knowledge. Besides, failing to remove all ransomware components might result in incoming data encryption and system reinfection.
If Gachimuchi virus removal is being tampered with, you should access Safe Mode and eliminate the infection from there. Please follow the following steps to reach the mode where malware's operation is temporarily suspended:
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing the F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.
![Windows XP/7 Windows XP/7]()
Windows 10 / Windows 8
- Right-click on the Start button and select Settings.
- Scroll down to pick Update & Security.
- On the left side of the window, pick Recovery.
- Now scroll down to find the Advanced Startup section.
- Click Restart now.
- Select Troubleshoot.
![Choose an option Choose an option]()
- Go to Advanced options.
![Advanced options Advanced options]()
- Select Startup Settings.
![Startup settings Startup settings]()
- Click Restart.
- Press 5 or click 5) Enable Safe Mode with Networking.
Data recovery
Some users believe that Gachimuchi files can be restored as soon as the computer scan with security software is performed. However, it is not the case, as data encryption is rather permanent – at least until a unique key is applied. It is also not correct to believe that the files are damaged or corrupted, as encryption does not essentially damage files.
As we already mentioned, it is not recommended to contact crooks. Instead, alternative methods could help you restore at least some of the lost data. Before proceeding, make sure you make backups of the encrypted files, as tampering with them might corrupt them for good.
- Download Data Recovery Pro.
- Double-click the installer to launch it.
![Gachimuchi ransomware Gachimuchi ransomware]()
- Follow on-screen instructions to install the software.
![Install program Install program]()
- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders which you want the files to be recovered from.
- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.
![Select Deep scan Select Deep scan]()
- Press Scan and wait till it is complete.
- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.
![Recover files Recover files]()
Security experts are known to work on decryption tools for major ransomware strains. In some cases, flaws within the encryption process can be found or criminals' servers seized by the lay authority agencies. In any case, you could look for decryptors on the following pages, although keep in mind it might take a while until there's a working one made.
- No More Ransom Project
- Free Ransomware Decryptors by Kaspersky
- Free Ransomware Decryption Tools from Emsisoft
- Avast decryptors

Other tips
There are two basic ways of protecting yourself against ransomware attacks effectively – employing powerful anti-malware and having it on at all times and backing your files on a separate medium. While the system must be remediated in order to be usable again, file recovery completely negates the need to contact the attackers and pay them money.
Besides this, we recommend running a scan with FortectIntego PC repair and maintenance utility, as it could find and replace damaged system components. Otherwise, you may experience Blue Screens,[3] program errors, crashes, and similar stability issues after malware removal completion.
Reporting the incident to your local authorities dealing with cybercrime can be a great help with catching criminals behind the attack. Contact your local branch with as many details as possible – here are a few links that could be useful to you:
- USA – Internet Crime Complaint Center IC3
- United Kingdom – ActionFraud
- Canada – Canadian Anti-Fraud Centre
- Australia – ScamWatch
- New Zealand – ConsumerProtection
- Germany – Polizei
- France – Ministère de l'Intérieur

You should contact the local police department or communications center if your country is not listed above.
How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Encryption. Investopedia. Sharper insight, better investing.
- ^ Chris Strohm and Alyza Sebenius. FBI Chief Wray Warns Cyber-Attacked Firms Not to Pay Ransoms. Insurance Journal. Property Casualty Insurance News.
- ^ Tim Fisher. How to Fix a Blue Screen of Death (BSOD). Lifewire. Tech News, Reviews, Help & How-Tos.








