Goba ransomware (virus) - Free Guide
Goba virus Removal Guide
What is Goba ransomware?
Goba is a dangerous computer virus that is after your documents and other files
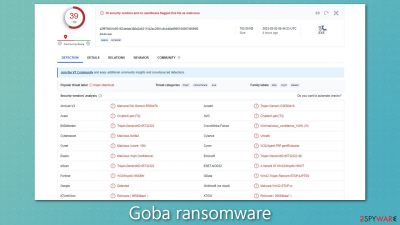
Goba is a ransomware-type virus that is designed to target computers and devices with the aim of extorting money from its victims. This particular version belongs to the Djvu family and was introduced by cybercriminals in early March of 2023.
Goba virus is typically spread through illegally downloaded software installers from untrusted websites. Malicious hackers may also use other means of transmission. Irrespective of the method used to distribute the virus, all victims unwittingly download it and only realize that something is wrong when they observe the initial signs of infection.
Once the ransomware infiltrates a system, it encrypts[1] all the data stored on that network or device. The encryption makes the data inaccessible to legitimate users until they pay a ransom for a decryption key.
After the encryption, Goba ransomware displays a ransom note named _readme.txt on the infected device or system. The note informs victims of the data encryption and demands a payment of $980 (with a $490 discount) in bitcoin in exchange for decryption. Communication with the hackers can be initiated via two emails provided in the note- datarestorehelp@airmail.cc and support@freshmail.top.
Even though there are news about more secured emails and end-to-end encryption in Gmail and other platforms, there are many ways that hackers and criminals are known to use. These methods allow threats to get spread via email attachments and links in emails with malicious code or direct ransomware payload. Threat actors can use cracked software and other malware for distribution of this Goba ransomware too, so be cautious. Stay safe online.
| Name | Goba virus |
|---|---|
| Type | Ransomware, file-locking malware |
| File extension | .goba extension appended to all personal files, rendering them useless |
| Family | Djvu |
| Ransom note | _readme.txt dropped at every location where encrypted files are located |
| Contact | support@freshmail.top and datarestorehelp@airmail.cc |
| File Recovery | There is no guaranteed way to recover locked files without backups. Other options include paying cybercriminals (not recommended, might also lose the paid money), using Emisoft's decryptor (works for a limited number of victims), or using third-party recovery software |
| Malware removal | After disconnecting the computer from the network and the internet, do a complete system scan using the SpyHunter 5Combo Cleaner, Malwarebytes security program |
| System fix | Upon installation, malware can cause severe damage to system files, resulting in instability issues such as crashes and errors. However, FortectIntego PC repair can automatically fix any such damage |
Ransom note – what to expect
Djvu ransomware variants like Qoqa, Iowd, or Vvoo are specifically designed to extort money from their victims by encrypting all kinds of popular file formats, including .jpg, .doc, .pdf, and more. These viruses are programmed to avoid system files like executables to ensure that the device's operating system is not damaged, although unintended consequences may still arise.
After the encryption process, the malware leaves a ransom note on the compromised system to inform the user of the ransom payment and possible file recovery. Here is a sample of what the victims may read in the ransom note:
ATTENTION!
Don't worry, you can return all your files!
All your files like pictures, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://we.tl/t-rayImYlyWe
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that's price for you is $490.
Please note that you'll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don't get answer more than 6 hours.To get this software you need write on our e-mail:
support@freshmail.topReserve e-mail address to contact us:
datarestorehelp@airmail.ccYour personal ID:
Cybercriminals employ various tactics to coerce victims into paying the ransom. One of the most common tactics is to convince them that paying the ransom is the only way to recover their encrypted files. To make their offer seem more appealing, attackers often include a 50% discount if the payment is made within a specific timeframe, usually within three days. They may also offer a free decryption service to prove their capability of decrypting the files.
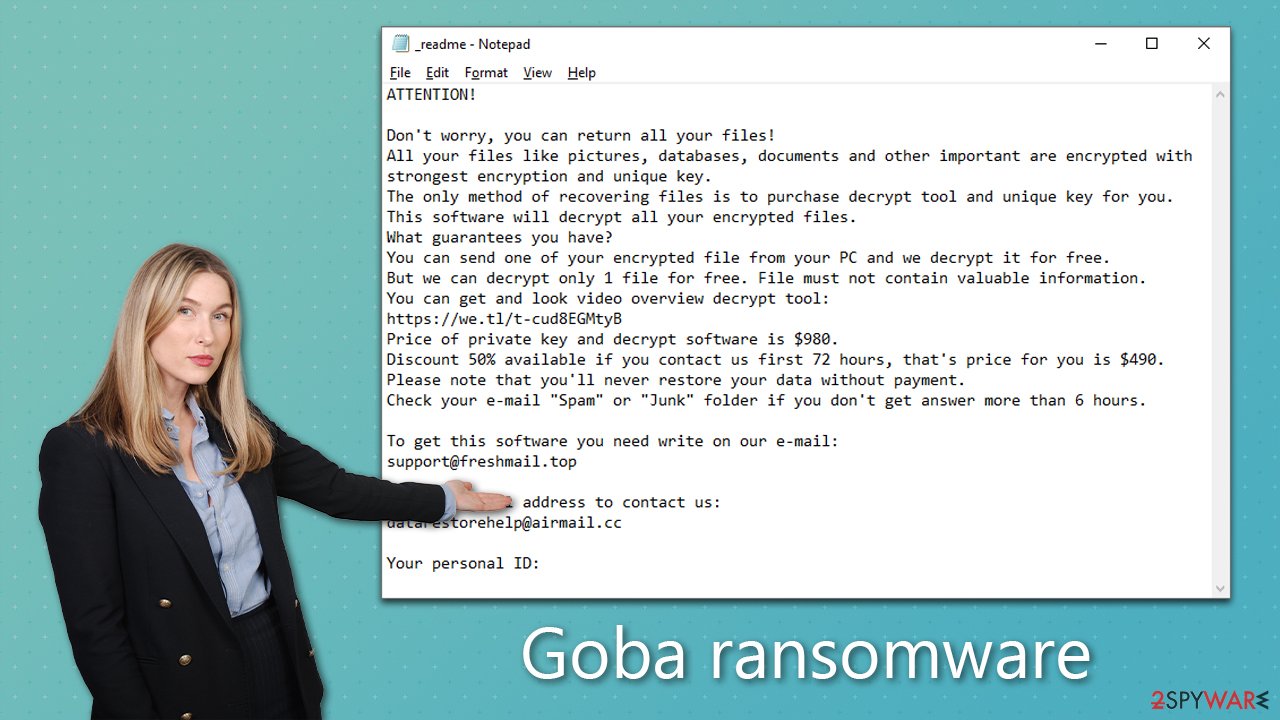
These tactics are designed to create a sense of urgency and desperation among victims, making them believe that paying the ransom quickly is their best option. In reality, however, paying the ransom does not guarantee that the attacker will provide the decryption key or that the key will work as expected. Moreover, it only encourages cybercriminals to continue their illicit activities, fueling the growth of ransomware attacks.
Goba virus removal: how to make your system functional again
As soon as malware gains access to a system, it can establish a connection to a remote Command & Control[2] server. This connection allows attackers to direct the malware to perform various tasks, such as updating itself or distributing new payloads. Consequently, it's essential to disconnect your computer from the internet and network before beginning the process of removing the ransomware.
- Type in Control Panel in Windows search and press Enter
- Go to Network and Internet
![Network and internet Network and internet]()
- Click Network and Sharing Center
![Network and internet 2 Network and internet 2]()
- On the left, pick Change adapter settings
![Network and internet 3 Network and internet 3]()
- Right-click on your connection (for example, Ethernet), and select Disable
![Network and internet 4 Network and internet 4]()
- Confirm with Yes.
After disconnecting your computer from the internet, you can remove Goba ransomware. It is recommended to use advanced security software like SpyHunter 5Combo Cleaner or Malwarebytes to ensure effective removal. In case the malware is trying to prevent the elimination process, access Safe Mode and perform a comprehensive system scan from there. However, before doing this, ensure your security software is up-to-date to detect the latest threats.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing the F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.
![Windows XP/7 Windows XP/7]()
Windows 10 / Windows 8
- Right-click on the Start button and select Settings.
- Scroll down to pick Update & Security.
- On the left side of the window, pick Recovery.
- Now scroll down to find the Advanced Startup section.
- Click Restart now.
- Select Troubleshoot.
- Go to Advanced options.
- Select Startup Settings.
![Startup settings Startup settings]()
- Click Restart.
- Press 5 or click 5) Enable Safe Mode with Networking.
We also advise scanning the system with FortectIntego PC repair utility, as some system files might get corrupted due to malware infection. This way, you can get rid of troubles such as BSODs,[3] crashes, errors, and other stability issues without reinstalling the operating system.
Attempt to recover data
Now that the Mzop ransomware has locked your files, it's time to explore your options for unlocking them without resorting to paying the ransom. Most people are not familiar with the intricacies of data encryption and may feel helpless when it comes to restoring encrypted files. However, there are several methods that you can try to recover your data.
Here are some options to consider:
- Restore your files from a recent backup. This is the most straightforward and reliable method of data recovery, provided that you have a backup of your files that is recent enough.
- Use data recovery software to scan your hard drive and attempt to recover your encrypted files. There are various software tools available that can help you recover deleted or damaged files, which may include some of your encrypted files as well.
- Try using a decryption tool from Emsisoft, specially designed to help victims of Djvu ransomware. While there's no guarantee that this tool will work for everyone, it's worth a try before considering paying the ransom.
We recommend trying the Goba decryption tool as your first option, as it may help you restore your files without paying the ransom.
- Download the app from the official Emsisoft website.
![Goba ransomware Goba ransomware]()
- After pressing Download button, a small pop-up at the bottom, titled decrypt_STOPDjvu.exe should show up – click it.
![Goba ransomware Goba ransomware]()
- If User Account Control (UAC) message shows up, press Yes.
- Agree to License Terms by pressing Yes.
![Goba ransomware Goba ransomware]()
- After Disclaimer shows up, press OK.
- The tool should automatically populate the affected folders, although you can also do it by pressing Add folder at the bottom.
![Goba ransomware Goba ransomware]()
- Press Decrypt.
![Goba ransomware Goba ransomware]()
From here, there are three available outcomes:
- “Decrypted!” will be shown under files that were decrypted successfully – they are now usable again.
- “Error: Unable to decrypt file with ID:” means that the keys for this version of the virus have not yet been retrieved, so you should try later.
- “This ID appears to be an online ID, decryption is impossible” – you are unable to decrypt files with this tool.
If this method is unsuccessful, you could always use specialized data recovery software.
- Download Data Recovery Pro.
- Double-click the installer to launch it.
![Goba ransomware Goba ransomware]()
- Follow on-screen instructions to install the software.
- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders which you want the files to be recovered from.
![Select what to recover Select what to recover]()
- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.
![Select Deep scan Select Deep scan]()
- Press Scan and wait till it is complete.
![Scan Scan]()
- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.
Security researchers are continuously working to develop decryption tools for various ransomware strains, which can help you recover your files without having to pay the ransom. In some instances, law enforcement agencies have seized servers from the perpetrators, leading to the release of decryption keys.
To access these decryption tools, you can visit the following links:
- No More Ransom Project
- Free Ransomware Decryptors by Kaspersky
- Free Ransomware Decryption Tools from Emsisoft
- Avast decryptors

How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ What is encryption? Data encryption defined. IBM. Blog.
- ^ Command and Control [C&C] Server. Trend Micro. Security research blog.
- ^ Blue screen of death. Wikipedia. The free encyclopedia.















