Guildma (Removal Instructions) - Free Guide
Guildma Removal Guide
What is Guildma?
Guildma – a dangerous banking Trojan that targets Latin American users

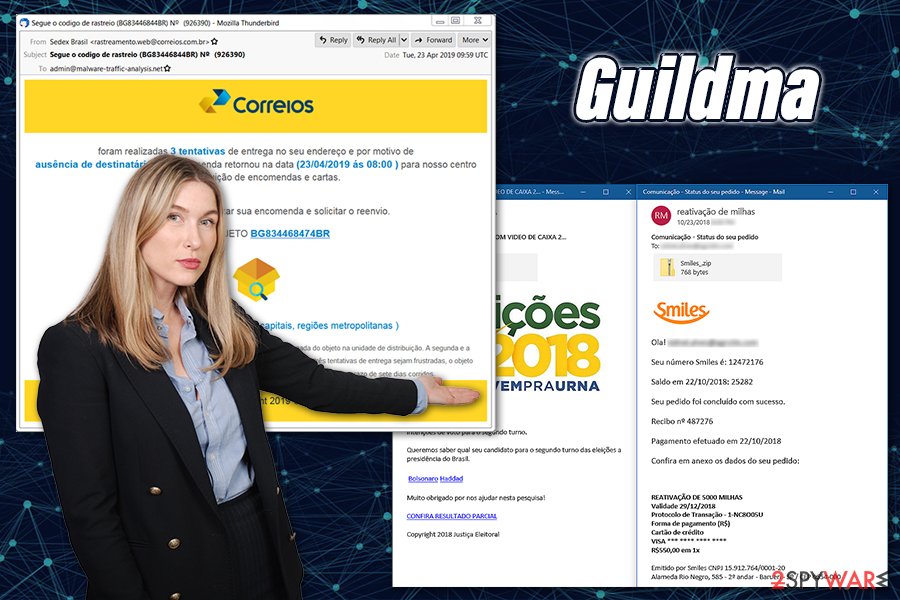
Guildma is a sophisticated data-stealing malware that was recently discovered and analyzed by most prominent security research teams. The virus targets more than 130 Latin American banking systems and 75 local web services, with its primary goal being to steal banking, email, entertainment service, and other credentials. Threat actors behind Guildma launched multiple large campaigns that were infecting as many as 50 thousand people a day via contaminated spam email attachments.[1] Its first emergence traces date back to 2015, although its peak was (so far) in summer/autumn of 2019. Currently, the Guildma virus is still spiking in popularity, and is currently the most prominent banking malware in Latin America, infecting ten times more victims than the second most common banking malware in the area.
| Name | Guildma |
| Also known as | Astaroth |
| Type | Banking Trojan |
| Platform | Windows |
| Programming languages | Threat actors use a combination of different programming languages which the malware is written in: Delphi, JS, VBS, and others |
| Affected area | Malware is almost elusively focusing on Latin America – Brazil in particular |
| Infection means | Guildma malware is spread exclusively using spam email attachments and incorporating Facebook and YouTube profiles. Emails are sent as invoices, tax reports, and similar messages – these include a .zip file which, once opened, initiates the infection process |
| Functions | Records keystrokes, takes screenshots, proliferates other malware, emulates keyboard and mouse inputs, steals credentials of e-commerce, email, and other services |
| Risks | Loss of sensitive information (disclosure to cybercriminals), financial losses, identity theft, infection of other malware |
| Removal | The only secure way to terminate malware is by performing a full system scan with the most up-to-date anti-virus software, accessing Safe Mode as required (instructions can be found below) |
| System fix | To remediate Windows after malware infection and fix virus damage, we recommend using FortectIntego |
Malware infection might not be so apparent, as, just like many other Trojans, it barely emits any symptoms and performs its operations in the background, which might prevent Guildma removal for weeks or even months. In the meantime, users might be running their computers as normal, providing the most sensitive information directly to cybercriminals.
Nevertheless, most of the legitimate anti-malware solutions would be able to stop all variants of Guildma, as its main executable is recognized as follows:[2]
- Trojan.AgentWDCR.XDE (B)
- TR/Spy.Guildma.mzypz
- Trojan.Win32.DelfiDelfi.4!c
- Trojan.TR/Spy.Guildma.mzypz
- Trojan:Win32/Guildma.V!MTB
- Mal/Generic-L
- W32/Guildma.BS!tr.spy, etc.
To remove Guildma, you will have to download and install one of the reputable AV providers, such as Malwarebytes, and perform a full system scan. Since malware is modular and might interfere with anti-malware operation, you might need to access Safe Mode with Networking and perform the scan from there. Once Guildma is terminated, you can also take care of Windows system files and fix the damage done with tools like FortectIntego.
Guildma distribution and infection routine
While Guildma malware is spread via spam email attachments, its method of doing so is innovative and sophisticated. To spread malicious emails, threat actors behind the malware are using mostly hacked or fake websites, where a malicious PHP code is installed. With this, the attackers can use the gathered email addresses to launch mass spam campaigns, infecting thousands of users daily.
The phishing emails come in the native (Portuguese) language and represent tax refunds, invoices, invitations, and similar events. Each of such emails is injected with a .zip file, usually named as follows: cheque.htm.zip, curriculum_.htm.zip, dados unidas rent a car.htm.zip, nota_fiscal.484.582.85.zip, etc. Such emails look professional, and many users could get tricked and open the clipped attachment.
Inside the archive, there is an obfuscated shell link (LNK) file, which calls the wmic.exe via Command Prompt to download the XSL file. The latter contains the malicious payload that begins the infection routine on the targeted machine.
To prevent infiltration of Guildma malware, users should not open attachments carelessly, as some phishing emails can look very believable. Thus, only open attachments you know are safe and are coming from a secure source. Uploading such attachments to Virus Total or similar analysis services can also help you determine whether it is malicious.
Guildma is modular malware capable of stripping victims of the most sensitive information
Throughout its existence, Guildma was released in several different versions and has been tweaked and improved over time. While threat actors employed a variety of different programming languages, data-stealing methods, as well as infection techniques, most of the code patterns such as encryption algorithms, file names, and other components remained unchanged.
Before starting the infection routine, Guildma Trojan first checks whether it accessed a sandbox environment (or a virtual machine which is often used by security researchers to analyze malware samples and their operation principles), and only proceeds if it detects a regular “user” machine. It will also not infect machines that are not located in the country of interest, i.e., mostly Brazil – Guildma checks keyboard language for that.
According to researchers, Guildma also checks for running applications, which is then followed by immediate data-stealing practice:[3]
Throughout the execution, it frequently performs checks for opened windows, mostly looking for banking applications or PuTTY. These detections trigger injections, screenshots, key hooking and “flag” file creation. All these actions are orchestrated by a vast array of interacting timers with a rather complicated hierarchy.
The main module (“Module G”) is very diverse and is responsible for such operations as C&C server communication establishment (which also incorporates YouTube and Facebook profiles to retrieve the C&C servers), loading of other modules, running application tracking, and much more.
Besides the regular banker malware capabilities, Guildma is equipped with an array of modules (at least 10), each capable of performing different tasks. These tasks are not only comprised of data-stealing but also include the following functionality:
- Screenshot capture
- Keystroke capture
- System reboot
- Keyboard and mouse emulation
- Keyboard shortcut blocking (such as Alt + F4 or Ctrl + W)
- File fetching
- Implementation of secondary payloads (backdoor function)
Guildma uses a variety of tricks to make users expose their credentials. Once the malware is active on the system, it forcefully logs users out of accounts on Google Chrome, Mozilla Firefox, Internet Explorer or MS Edge, making them re-enter credential data repeatedly. This information is later sent to the C&C server via an established network connection. Guildma will also record everything typed by the keyboard and take screenshots to steal relevant information.
Guildma also has a from grabber function, which allows the virus to capture email lists from MS Outlook, Thunderbird, and other email desktop clients. This module also includes the capability of stealing data from relevant websites.
As evident, the presence of Guildma Trojan can seriously compromise the infected machine and result in financial losses, or even identity theft. Therefore, users should ensure that they would not get tricked by realistically crafted phishing emails, although protection of anti-malware software is the most critical component that would defend victims from malware intrusions.
Eliminate Guildma from the system immediately
As previously mentioned, Guildma virus can cause significant damage to the computer owner, as it can steal such sensitive data like banking, email, and other login credentials. As a result, users might see their credit card accounts being drained without permission, or goods being purchased under their names. Online banking accounts should always be monitored for unsolicited transactions. In case you noticed that your bank account was was emptied, there is a high chance you should immediately remove Guildma from your computer.
To remove Guildma malware from the system, download and install a powerful anti-malware program, bring it up to date, and perform a full system scan. This will ensure that all the malicious components, along with other possible malware, is eliminated at once. If you are struggling when trying to perform a scan, you should access Safe Mode with Networking and employ anti-malware software from there.
Additionally, if you have been a victim of Guildma attack, you should reset all your passwords after malware termination. Also, contact your bank and explained what happened, as you should close any compromised bank accounts.
Getting rid of Guildma. Follow these steps
Manual removal using Safe Mode
If you are unable to remove Guildma in a regular mode, access Safe Mode with Networking:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Guildma and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting trojans
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Guildma: The Devil drives electric. We Live Security. ESET research blog.
- ^ 81c86ee2976a5a5f9dcc4ffda5e93900a14ae6dae10958fbf545da2460ecdece. Virus Total. File and URL analysis.
- ^ Adolf Středa, Luigino Camastra. Deep Dive into Guildma Malware. Decoded. Avast security blog.
