GuLoader (Virus Removal Instructions) - Free Guide
GuLoader Removal Guide
What is GuLoader?
GuLoader is a malware downloader associated with infiltration of Remote Access Trojans like Remcos

GuLoader is a type of malware that is used by the attackers to download and install other malicious software on the targeted machines, predominately Remote Access Trojans. Initially spotted in December 2019 by security researchers, the downloader was used by multiple different cybercriminal gangs to infect regular consumers and corporations with malware like NanoCore, Remcos, FormBook, NetWire,[1] and many other RATs. While GuLoader itself is not used for malicious purposes such as information stealing, the tools that are proliferated via the downloader can perform a variety of tasks. Users infected with this malware can suffer considerable financial losses, loss of data, and even identity theft.
| Name | GuLoader |
| Type | Malware downloader |
| Targeted OS | Windows |
| Associated payloads | The downloader was used in multiple campaigns and installed malware like NanoCore, Remcos, FormBook, NetWire, Parallax, Agent Tesla, Warzone RAT, and many others |
| Distribution | Malware was spotted in various malicious email campaigns but it can also be proliferated using other methods, such as fake updates, drive-by downloads, software cracks, exploit kits, etc. |
| Symptoms | All the activities performed by GuLoader happen in the background, and no visible signs can be seen; once the malware is installed, users might spot some signs of infection, such as suspicious processes running in the background, system slowdowns/errors/crashes/lag, high CPU usage, etc. |
| Implications | The downloaded malware can allow the attackers to control the machine remotely, meaning that they can steal sensitive information, install other malicious programs, steal users' or companies' funds, and perform other malicious activities |
| Removal | To eliminate the downloader and the payload safely, perform a full system scan with anti-malware tools like Malwarebytes |
| System fix | Malware can cause significant damage to system files. If you spotted you computer lagging, crashing, returning errors, you should repair the virus damage with FortectIntego |
GuLoader is a portable executable that is typically stored inside a compressed file, such as an .ISO or a .RAR. Once clicked, it follows a particular behavioral pattern that downloads the malicious payload from a remote server – typically, OneDrive or Google Drive is used. Since the payload is encrypted with XOR algorithm, these platforms are unable to detect malware in the first place, allowing cybercriminals to operate the scheme easily.
In other words, while various companies and businesses often employ the Cloud system for large file storage space (backups are often held on the cloud, for example), threat actors behind the GuLoader virus also use it for malicious purposes.
GuLoader can be downloaded from a variety of sources, although multiple malspam campaigns were spotted employing it. Nonetheless, users might also get infected with malware via the following ways:
- Fake updates
- Drive-by downloads
- Software cracks
- Repacked installers
- Software vulnerabilities[2]
- Exploits, etc.
Once inside the system, GuLoader will contact a particular location on the cloud and download predetermined malware. As mentioned above, this downloader is typically used to install Remote Access Trojans, which are extremely dangerous. They allow the attackers to perform a variety of functions, such as stealing sensitive information (credit card details, passwords, email contents, etc.), downloading and installing files, taking screenshots, monitoring computer resources, etc.
Without a doubt, GuLoader can be the cause of the infection of multiple different malicious programs, that can all operate silently, performing malicious operations in the background. In case such malware like ransomware is installed, users can also lose access to all their files, such as work documents or personal pictures. Malicious actors then demand to pay a ransom in Bitcoin or another cryptocurrency, and the amount can be relatively high. Even then, there is no guarantee that the promised decryptor is provided by the attackers.
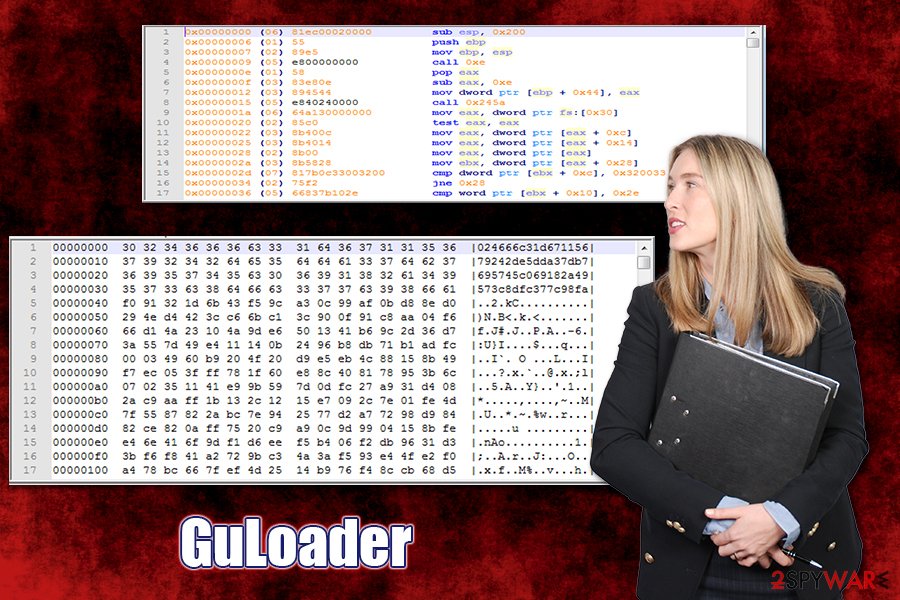
What makes GuLoader removal and detection complicated is its obfuscation capabilities. It uses a variety of process injection techniques, such as spawning a child process of itself, overwriting the DLL image of the system, etc.[3] Due to these sophisticated methods, analyzing of GuLoader is difficult. Unfortunately, but users are likely not to notice the malware in operation, as everything it does is performed silently in the background.
The best way to remove GuLoader, you will have to employ powerful anti-malware software and perform a full system scan. In case malware is tampering with security software, you can access Safe Mode with Networking (malware's operations are temporarily disabled in this mode, as the system is launched with only the most necessary drivers) as explained below. Additionally, after GuLoader malware elimination, you should also use FortectIntego to fix virus damage.
Prevent the infiltration of malicious software by being attentive online
As evident, there is a multitude of methods that malicious actors use to deliver malware to as many users as possible. Despite the popular belief, however, malware does not simply access the machine out of nowhere – its infiltration point can often be traced back to actions that users made, either intentionally or not. There are several attack vectors that we would like to discuss – we will also explain how to reduce the probability of the infection to a minimum.
- Spam email attachments are possibly one of the most common malware delivery methods used by cybercriminals. While some phishing emails can be targeted (attack a particular individual or a company of interest), crooks typically employ botnets and other spam tools to ensure that thousands of users receive the fake message in their inboxes. Luckily, many such emails end up in spam boxes, although some still manage to break in. Thus, never all a macro to be run via MS Office documents, as it begins the infection chain immediately. Also, do not click on embedded links, even if they look as legitimate banners or buttons.
- To prevent the automatic installation of malware, you need to ensure that your system is running on the latest patch. For that, enable automatic updates on Windows. Do not forget to do the same with all the applications you have installed on the PC, as they can also be laced with vulnerabilities that the attackers can exploit.
- Practice good browsing habits – do not click on suspicious ads or visit high-risk websites. In most cases, users are aware that sites like torrents that host pirated programs/software cracks are riddled with malware, but they are still willing to risk it. What makes it worse, that some of the installers might install the anticipated program along with malware that will be running in the background, out of sight of the user.
- Equip your computer with powerful security software that can prevent the infiltration of malware in the first place. While there is no anti-malware tool that could protect from all malicious programs (malware is constantly evolving and using various obfuscation techniques), you can be sure that it will increase the security of your machine exponentially.
Eliminate GuLoader along with other malware installed on the device
As evident, the main goal of the GuLoader virus is to download and install other malware, such as RATs or info-stealers. These malicious programs can be extremely dangerous, as they can steal sensitive data without users' knowledge, turn the machine into a spam bot, or even completely corrupt the operating system. In other words, Remote Access Tools enable the attackers to perform any actions they want on a hijacked machine. That is why a timely GuLoader removal is so important.
However, if you remove GuLoader manually, malicious programs that were installed by it will remain on the system. Therefore, you should employ powerful anti-malware solutions and perform a full system scan. Since malware injected by the virus can be deceptive and advanced, it might also attempt to disable your security software. In such a case, you should access Safe Mode with Networking and perform a full system from there. This will temporarily render malware useless, allowing it to get eliminated without problems.
After you are completely sure that you got rid of GuLoader and all the other malware on your system, you should also change all your passwords and monitor your online banking activities. If you are aware that your banking credentials were accessed, you should contact your bank and disable the account immediately.
Getting rid of GuLoader. Follow these steps
Manual removal using Safe Mode
In case GuLoader malware is preventing its termination, access Safe Mode with Networking:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from GuLoader and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting malware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Brad Duncan. GuLoader: Malspam Campaign Installing NetWire RAT. PaloAlto. Security blog.
- ^ Vulnerability (computing). Wikipedia. The free encyclopedia.
- ^ GuLoader: A Popular New VB6 Downloader that Abuses Cloud Services. Proofpoint. Threat research blog.














