HackTool:win32/autoKMS (Removal Guide) - Oct 2020 update
HackTool:win32/autoKMS Removal Guide
What is HackTool:win32/autoKMS?
HackTool:win32/autoKMS is a potentially malicious file designed to crack Microsoft products such as MS Office Suite
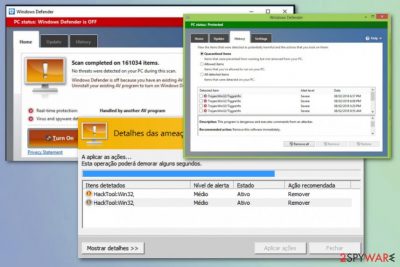
HackTool:win32/autoKMS is software that can be used to crack or patch unregistered copies of various Microsoft applications. This heuristic name is reported by researchers[1] and indicated on various forums by users themselves.[2] There are many possible outcomes when such an alert appears on the system because it either shows the malicious behavior of actors and malware on the device or is reporting false infection. Unfortunately, in most cases, such detection can be actually related to malware or unwanted programs, so you should never ignore these warnings.
Hacking tools like HackTool:win32/autoKMS virus can be set to spread malware and help hack systems. This particular detection is closely related to KMSpico tools, which are used for precisely the same purpose. If you installed any of such tools yourself, your device may be safe and secure, but when these alerts are not associated with a program that you added and know about, make sure to take action and avoid serious infections since this may lead to malware issues.
| Name | HackTool:win32/autoKMS |
|---|---|
| Type | Hacking tools, possibly trojan or other malware |
| Symptoms | Malicious behavior detection-based engines alerts users about the suspicious program or file and offer to delete the threat. The virus itself is not causing any issues besides occasional pop-up messages about software issues |
| Danger | The detection can indicate serious malware infection and lead to the damaged system if you remove the program that is essential, or decide to leave the intruder running |
| Distribution | Malicious websites and other services that offer free downloads of programs and tools lead to infiltrations of malicious applications. It is possible to install a particular malicious program on your device during installation of other freeware or get the executable file with malicious code from legitimate-looking but the insecure email notification |
| Elimination | HackTool:win32/autoKMS removal can happen with your program that indicated this intruder in the first place. You need to rely on professional anti-malware tools or security programs to avoid possible file corruption |
| Repair | When the program can run in the background and affect processes crucial for the infected device, you should run a system tool like FortectIntego and look out for the damaged files or entries that can trigger malicious activities |
HackTool:win32/autoKMS pop-ups and detection alerts mean that there is a potential risk on the machine, and you should take malware infection into consideration. Using hack tools is not recommended by any experts[2], on the opposite, these programs can be considered dangerous and malware, hence these generic detections.
When malware is associated with the detection and manages to run on the machine, HackTool:win32/autoKMS virus may be set to:
- connect to the remote server;
- receive additional configurations or files;
- install and download programs;
- execute arbitrary files;
- steam or upload data on the system;
- take actions from a remote attacker.
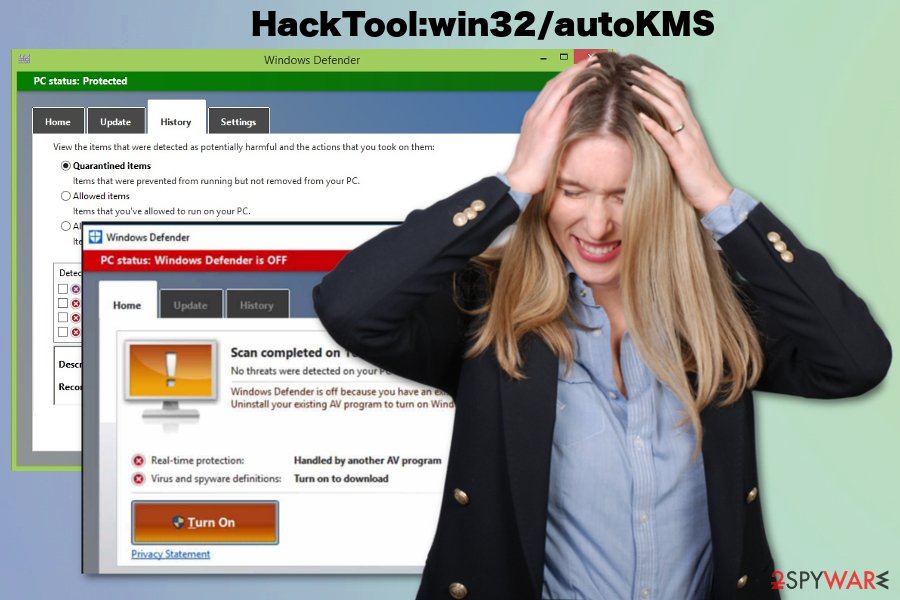
HackTool:win32/autoKMS, or Auto KMS in particular, can be associated with automatic windows operating system activation services, so when you use the fake version of the software, you can get these alerts. However, removing the threat can lead to corruption of your device, unless you use a genuine Windows version.
The best way to react to this detection would probably be a secondary check with alternate anti-malware tools or software. When you get additional suggestions to remove HackTool:win32/autoKMS from more than two programs, you should do as suggested and clean the machine. Anti-malware programs can do that for you without damaging additional processes or files.
Malware might also sometimes cause damage to Windows system files, which might prompt users to reinstall the system due to continuous crashes or errors. Instead of doing that, you can attempt to repair the damage done by the threat with FortectIntego – a unique application capable of replacing damaged files with brand new ones.
HackTool:win32/autoKMS can be associated with particular hacking tools or illegal software. If that is the case, the following pop-up can possibly appear on the screen occasionally:
AutoKMS 2.4.3.0 Ran At.
Attempting To Activate Microsoft Office
Attempting to Activate OfficeProPlus-KMS_Client
Product activation successful
HackTool:win32/autoKMS can make changes in the registry and other system folders, affect processes, damage functions, and features since there are many possible functions such intruder can rely on. Once it gets on the computer, it drops various files to activate specific processes and places data, malicious code to ensure that it gets launched with every system reboot.
Since there are no particular symptoms HackTool:win32/autoKMS removal can get difficult. You need to find and remove all associated files and programs that may interfere with the particular hack tool functions or the trojan that is associated with this detection name.
There are no physical programs of such threats like HackTool:win32, in most cases, so you need a professional anti-malware tool that can find various applications and files. However, remember that no visible symptoms and discrete operations can mean attackers and silent executions, so double-check before adding any files or programs on the machine.
HackTool:Win64/AutoKMS – a new version of the virus that spreads among Windows 64-bit users
In May 2020, Microsoft announced that it would no longer be offering 32-bit operating systems to the hardware manufacturers.[3] This version of Windows only supports systems that do not exceed 4GB of RAM, so adding more of it becomes impossible. In other words, all these changes, along with new technology arrival, prompted users to switch to 64-bit Windows systems.
HackTool:Win64/AutoKMS is a popup that users using 64-bit Windows can encounter after Windows Defender detects such a tool. Most commonly, the detection is flagged after users attempt to download a crack tool designed to break the licensing process of Microsoft programs.
While some of these tools are (even though illegal) safe and will do the job that they are designed to, there is plenty of malware that can be disguised as HackTool:Win64/AutoKMS. The malware within the malicious file can represent various malware, including ransomware Djvu ransomware, which is known to be spread via illegal program installers and cracks/keygens/loaders. Once inside, it would block access to all personal files and then demand ransom for a unique that is required to unlock data.
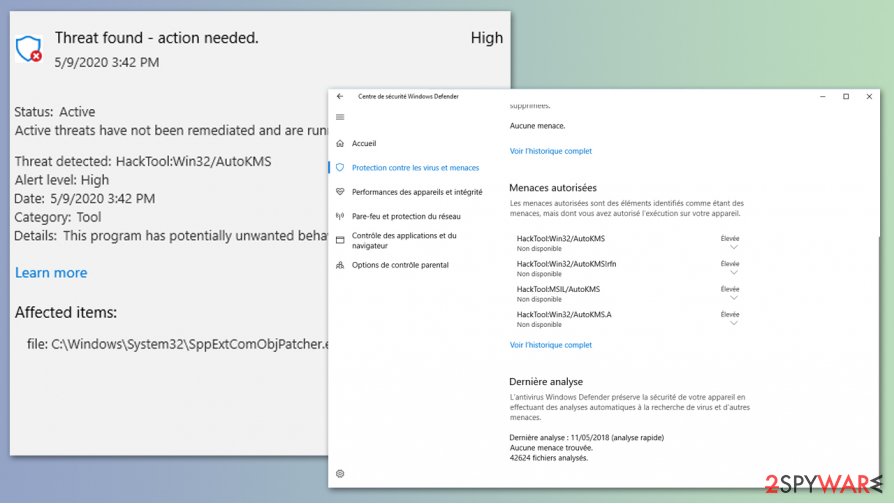
However, there is no way to determine for sure whether HackTool:Win64/AutoKMS is actually a virus or not. By design, any anti-malware software is likely to flag such a file as malicious due to its functionality of breaking the original code of the application. Thus, even if the crack is “safe,” there is no way to be sure.
Do not ignore the warnings of your anti-malware software and remove HackTool:Win64/AutoKMS from your system before it manages to cause any damage. If Windows Defender fails to delete the infection, we suggest trying other security solutions, such as SpyHunter 5Combo Cleaner or Malwarebytes.
Malicious tools and programs get delivered via deceptive sites and other applications
The payload of threats that run in the background, in most cases, gets on the machine without users' permission or even knowledge because this malware drop is a silent process. Sometimes malicious websites offer these programs as deals or extra applications during the initiated download of freeware.
In most cases, these hacking tools or crack software is installed by the person that wants to use the illegal application. Torrent services and pirated sites often distribute these programs, so you should pay attention if you go for these methods of installations or choose to crack apps and cheat.
The best advice is to use legal applications, official providers, and developers as your main source of freeware. Also, choosing correct installation options could help you, so always go for Advanced or Custom options and control programs that you install. Avoid surfing on suspicious or potentially malicious pages, so you can keep the machine virus-free and safe.
Terminate HackTool:win32/AutoKMS or HackTool:Win64/AutoKMS to prevent possible damage to the system
Once HackTool:win32/autoKMS virus gets in the system it can download other threats and launch malicious processes. The malware[4] runs on the machine without causing particular issues or noticeable symptoms, so it is not the program that could raise questions until alerts start coming to the screen.
You should note that threats like this can become exceptionally persistent and hide core files all over the system, or disable AV tools to avoid detection. You can go for Safe Mode reboot and then focus on HackTool:win32/autoKMS removal. Such an option allows running the anti-malware program on the machine without interruption.
To remove HackTool:win32/autoKMS once and for all, rely on programs like SpyHunter 5Combo Cleaner or Malwarebytes. Anti-malware programs can find and indicate various types of malicious programs and files, remove such content from the system, clean your device from PUPs and viruses. Also, remember to check system files and affected parts using FortectIntego that can find and repair various virus damage,
Getting rid of HackTool:win32/autoKMS. Follow these steps
Manual removal using Safe Mode
Reboot the machine in Safe Mode with Networking and remove HackTool:win32/autoKMS fully
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove HackTool:win32/autoKMS using System Restore
Try System Restore for terminating HackTool:win32/autoKMS virus
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of HackTool:win32/autoKMS. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from HackTool:win32/autoKMS and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting malware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ HackTool:Win32/AutoKMS. Microsoft. Security community blog.
- ^ I faced this thread "HackTool: Win32/AutoKMS" in windows defender (win 10 pro) ? What should I do?. Quora. Online question and answer platform.
- ^ Marc DeAngelis. Microsoft stops offering 32-bit Windows 10 to computer manufacturers. Engadget. Technology news and reviews..
- ^ Malware. Wikipedia. The free encyclopedia.





















