Kaenlupuf ransomware / virus (Virus Removal Instructions) - Quick Decryption Solution
Kaenlupuf virus Removal Guide
What is Kaenlupuf ransomware virus?
What do we know about Kaenlupuf ransomware virus so far?
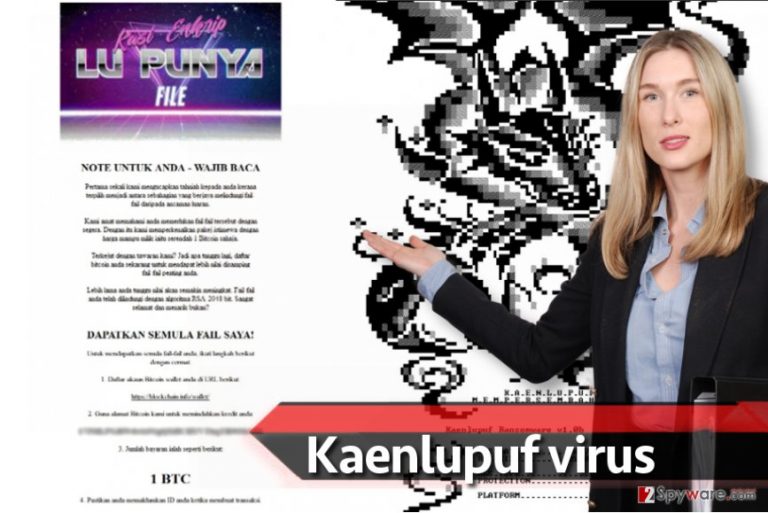
Today we are going to present a Malaysian ransomware[1] called Kaenlupuf virus. This suspicious and malicious program seems to be in the development process at the moment, but there’s no doubt that it is going to be improved and distributed on a much larger scale shortly[2]. The ransomware name stands for KAsi ENkrip LU PUnya File. The ransomware claims to be using a RSA-2048 encryption algorithm to corrupt files on the target computer, and this cryptography method[3] is known to be one of the most secure ones. Once files are encrypted, there are barely any chances to restore them without having a decryption key. The ransomware authors have it, so they ask the victim to pay a ransom of 1 BTC to their Bitcoin wallet. The ransom note that the virus creates after the encryption procedure says that the computer user “was chosen to be among the ones who got their files protected from external threats.” The criminals ramble about a special package available for an affordable price of 1 BTC[4] that the victim needs to purchase, while in reality, these crooks are just asking for a ransom of approximately 1170 USD. Below, you can see the ransom note (written in Malaysian language):
NOTE UNTUK ANDA – WAJIB BACA
Pertama sekali kami mengucapkan tahniah kepada anda kerana terpilih menjadi antara sebahagian yang berjaya melindungi fail-fail daripada ancaman luaran.
Kami amat mamahami anda memerlukan fail fail tersebut dengan segera. Dengan itu kami memperkenalkan pakej istimewa dengan harga mampu milik iaitu serendah 1 bitcoin sahaja.
Terkejut dengan tawaran kami? jadi apa tunggu lagi, daftar bitcoin anda sekarang untuk mendapat lebih nilai disamping fail-fail penting anda.
Lebih lama anda tunggu nilai akan semakin meningkat. fail-fail anda telah dilindungi dengan algoritma rsa-2048 bit. sangat selamat dan menarik bukan?
DAPATKAN SEMULA FAIL SAYA!
Untuk mendapatkan semula fail-fail anda, ikuti langkah berikut dengan cermat:
1. Daftar akaun Bitcoin wallet anda di url berikut:
2. Guna alamat bitcoin kami untuk memindahkan kredit anda:
3. Jumlah bayaran ialah seperti berikut:
4. Pastikan anda memaklumkan ID anda ketika membuat transaksi.
It goes without saying that you shouldn’t pay ransomware crooks the money they don’t deserve. Instead, we suggest removing the virus using anti-malware tools, for instance, FortectIntego, and recovering your files from a backup. Besides, malware analysts might successfully reverse this piece of malware and create a free decryption tool anytime soon, so we suggest you stay patient. You should start Kaenlupuf removal by rebooting your PC into Safe Mode with Networking. You can find full and comprehensive instructions on how to remove Kaenlupuf ransomware right below the article.
How can you get infected with ransomware virus?
Ransomware viruses are mostly distributed via deceptive email messages, but you can also become a victim of a ransomware attack due to RDP attack[5] or in case you have some outdated software on your PC, and you like to browse through shady Internet websites without having a decent anti-malware or antivirus software on your computer system. This way, your security vulnerabilities in the software you have can be easily exploited by attackers. We suggest you to protect your files in advance by creating a data backup, installing a good security software, and staying away from suspicious content online. Of course, you should also make sure that software you have is up-to-date (especially Flash or Java).
Kaenlupuf ransomware removal tutorial
Below the article, you can find a full Kaenlupuf removal tutorial which we prepared with an intention to clarify how ransomware viruses should be removed. Please do not try to remove Kaenlupuf virus without anti-malware software – it is very hard to delete such viruses by yourself, and you can easily do more bad than good when trying to solve the problem by yourself. If you have any questions about this virus, don’t hesitate and send a question to 2-Spyware support team or leave your questions or observations below.
Getting rid of Kaenlupuf virus. Follow these steps
Manual removal using Safe Mode
Delete the virus according to guidelines given below.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Kaenlupuf using System Restore
If the method 1 fails to work, try this technique.
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Kaenlupuf. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Kaenlupuf from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If you have a data backup, it will be extremely easy to recover lost data. Just remove the virus and plug in the drive with backup on it to your PC and export the files you need. If you do not have a backup, follow these easy steps:
If your files are encrypted by Kaenlupuf, you can use several methods to restore them:
Method 1. Use Data Recovery tools
We highly recommend using Data Recovery Pro for users who suddenly become victims of ransomware. In some cases, Data Recovery Pro helps to restore corrupted files.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Kaenlupuf ransomware;
- Restore them.
Method 2. Restore individual files
This trick can work for you if you have created System Restore Point in the past. If you did so, follow these steps:
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Kaenlupuf and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Hanna Sheikh Mokhtar. Alert for Malaysian Internet users of escalating ransomware attacks. New Straits Times. Authoritative Source for Malaysia Latest News on Politics, Business, Sports, World and Entertainment.
- ^ December 2016: The Month in Ransomware. Tripwire. IT Security News & Blog.
- ^ Nicholas G. McDonald. Past, Present, and Future Methods of Cryptography and Data Encryption. University of Utah - Department of Electrical and Computer Engineering. A Research Review.
- ^ Dean Takahashi. Ransomware has Exploded Thanks to Bitcoin’s Anonymity. VentureBeat. Tech News That Matters.
- ^ Ionut Arghire. RDP Tops Email for Ransomware Distribution: Report. SecurityWeek. IT Security News and Information Security News.







