Karo ransomware / virus (Removal Guide) - Recovery Instructions Included
Karo virus Removal Guide
What is Karo ransomware virus?
Karo ransomware infects the system to take your files hostage
Karo ransomware is a data-encrypting computer virus[1] that emerged in the end of June 2017. It targets vulnerable computer systems that have no security software installed on them. The ransomware encrypts data and marks corrupted files with .ipygh file extensions. Then it drops a ransom note with a banal title ReadMe.html.
The virus will encrypt files with an AES-256 encryption algorithm [2], rendering them unreadable and appends .ipygh extensions to indicate which particular files have been affected. The destructive encryption may be applied to a variety of documents on mounted hard drives, external storage drives as well as open network shares.
Extortionists communicate with the victims via Tor network.
Ransomware infection is a serious computer security infringement. Naturally, it has a significant impact on the system’s performance. This means that if you recognize your computer quite well, you may be able to grasp the ransomware at the initial states of its infiltration.
Monitor your system’s performance speed, CPU and RAM utilization. If these indicators show unusual activity while no visible programs are running in the system, you should not ignore it. Take some time to scan your PC for potential ransomware infection and remove Karo if it is found hiding on your system.
Experts do not recommend[3] tackling the virus manually. The virus is way too complicated to be eliminated without the assistance of specialized software. That’s why experts recommend employing FortectIntego, Malwarebytes or similar utilities to perform Karo removal for you.
Alleged connections to Petya
Since this virus has emerged in the middle of Petya/NotPetya ransomware campaign upheaval, some tend to ascribe it to this particular virus family. Nevertheless, the relationship between the two was denied – it turned out that unexpectedly emerged Karo was simply confused with the new Petya virus.
It appears that Karo's downloader hashes were found in a GitHub repository for Petya-related IOCs. It was yet another detail that led to the confusion of these two viruses. However, now it is clear that viruses are not related and created by different cyber crime gangs. 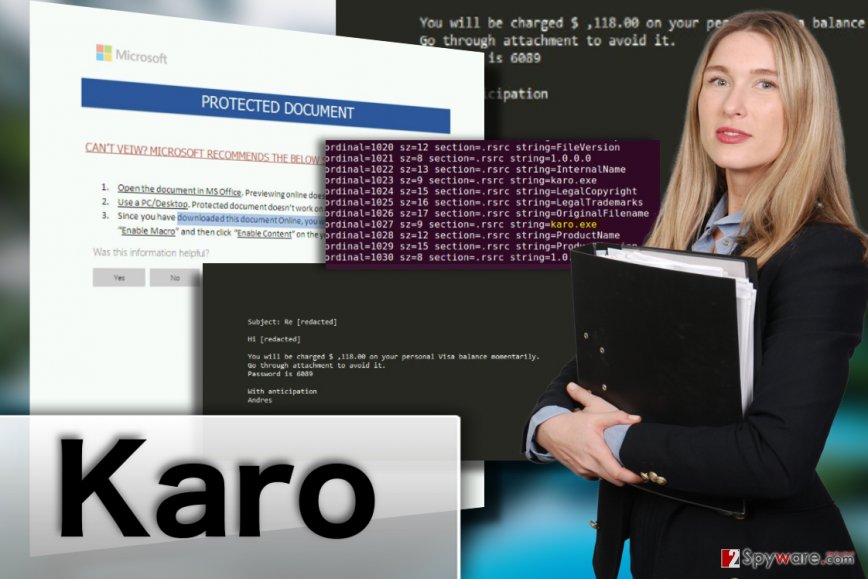
The main Karo ransomware attack vector
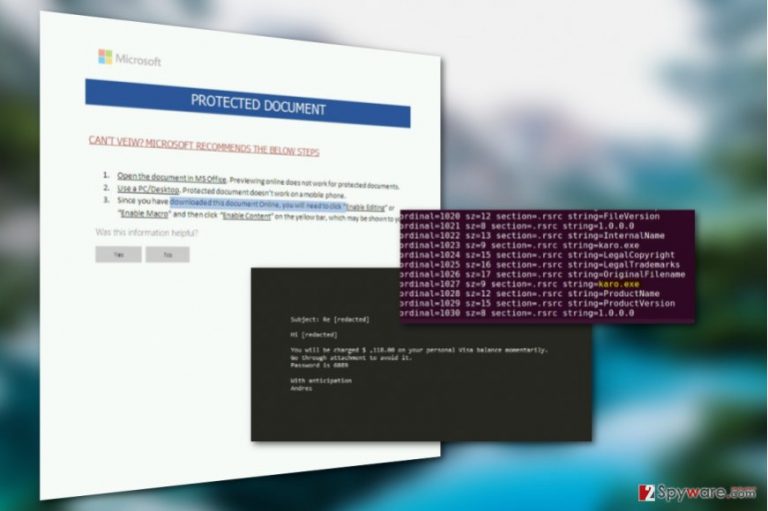
Karo ransomware is mainly promoted via malicious spam. The attackers use victim's name in the email subject. They pretend to be someone from a well-known business company and falsely inform the victim about a sum that they're about to charge from victim's bank account. The crooks state a sum that is not unrealistic, but also quite large as well.
The deceptive message then informs the victim to check an attached password-protected document associated with the payment. The document contains a macro function that, once activated, launched cmd.exe and downloads the ransomware to the system.
This social engineering scheme is extremely effective and it helps to convince users install ransomware on their computers without realizing it. For this reason, you should never interact with files or programs sent to you by unknown people.
Prevent ransomware attack with these easy tips
Karo distribution is currently rather low. If you have not been infected with the malware yet, you should use this for your own benefit – strengthen your system’s security! You can make your system a lot more safe in just four steps:
- Upgrade your system to the latest version. Don’t use outdated OS versions as they don’t receive security patches and are often more vulnerable to different malware infections.
- Keep your antivirus software and other installed programs updated. Programs that don’t receive security patches may have zero-day vulnerabilities that could be easily exploited to drop malware on your computer.
- Be careful while browsing through your email. Malware may arrive at your PC in spam emails as an attached invoice, speeding ticket or some other document. These files may hide Karo ransomware dropper file which will be activated once opened.
- Refrain from browsing on poor reputation websites and stay away from unsafe peer-to-peer networks. Ransomware tend to circle around in such places and can be well disguised as legitimate programs.
Get rid of Karo ransomware virus
Trying to remove Karo virus from the infected device can be risky and may result in total data corruption as well as the entire operating system. All it takes is a single mistake while eliminating one of its malicious files from the PC. Luckily, mistakes can be prevented by putting professional anti-malware software to work.
Just launch some reliable malware removal tool on your PC and let it take care of all the dirty work. After the security software is done with the system scan, there should be no malicious components left on your computer and Karo removal should be complete.
Getting rid of Karo virus. Follow these steps
Manual removal using Safe Mode
Karo ransomware may block your security utility from running system scans in order to prevent its elimination from the system. Nevertheless, the virus can be decontaminated. You only need to boot your PC in Safe Mode and then run the system scan again.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Karo using System Restore
One more technique which may unblock you antivirus is presented below:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Karo. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Karo from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Karo, you can use several methods to restore them:
Make use of Data Recovery Pro
Here are a few simple steps which will explain how to use Data Recovery Pro for the restoration of the encrypted data.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Karo ransomware;
- Restore them.
How to use Windows Previous Versions feature?
This is a question that users often ask us. Thus, we've prepared a brief tutorial below to guide you through the process.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Shadow Explorer as data recovery option
According to the preliminary findings, Karo virus does not seem to be destroying Volume Shadow Copies of the encrypted files. If these findings are true, you should be able to recover your files using Shadow Explorer like explained below
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Currently, Karo decryptor is unavailable
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Karo and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Jason Witty. Crypto-ransomware: Why your business needs to plan for it. Bizjournals. How To: Tech Tips.
- ^ Advanced Encryption Standard. Wikipedia. The Free Encyclopedia.
- ^ NoVirus. NoVirus UK. Virus Removal Tutorials, Tech News.







