Keep It Secure browser hijacker (virus) - Free Instructions
Keep It Secure browser hijacker Removal Guide
What is Keep It Secure browser hijacker?
Keep It Secure does not protect your privacy or provide a secure browsing experience

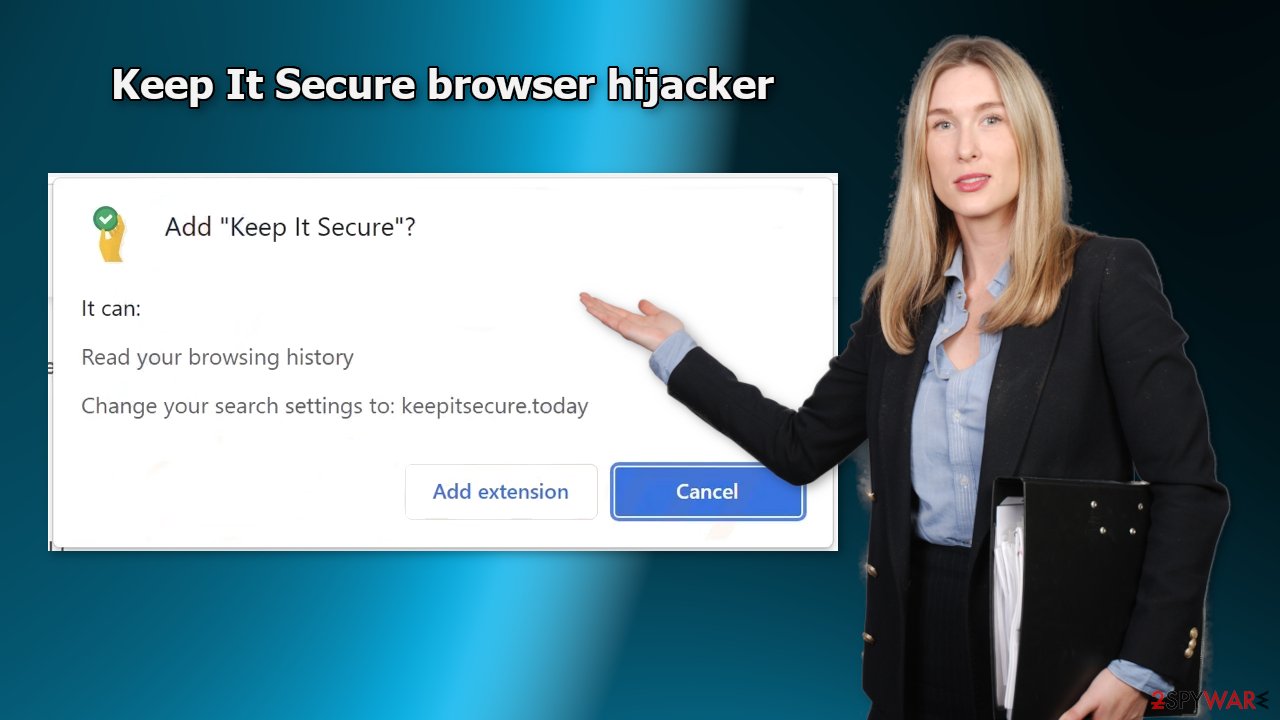
Keep It Secure is a browser hijacker that changes the main browser settings. It redirects users' queries through keepitsecure.today to Yahoo. While this may not look like a big deal, such applications can cause quite a lot of issues. First of all, users are forced to use only selected channels for browsing which raises many user privacy and security concerns.
The next thing is that web-based applications can monitor users' browsing activities. Some hijackers can also cause an increased amount of commercial content, like pop-ups, banners, surveys, and redirects. Crooks can generate revenue from your clicks[1] and your data. What is more, they could be using rogue advertising networks that place ads leading to dangerous websites.
Security experts recommend clearing cookies[2] and cache regularly. Cookies can store information such as your IP address, geolocation, websites you visit, links you click on, and things you purchase online. This data can later be sold to the same advertising networks or other third parties. Having a maintenance tool like FortectIntego helps by automating the process of cookie removal.
The extension also does not provide any benefits. The name of the plugin implies that the add-on should help your browsing remain secure but that could not be further from the truth. We urge you to follow this guide to learn more about browser hijackers and how to get rid of them.
| NAME | Keep It Secure |
| TYPE | Browser hijacker; potentially unwanted program |
| SYMPTOMS | The main settings of the browser get changed, like the homepage, new tab address, and search engine |
| DISTRIBUTION | Shady websites, deceptive ads, software bundling |
| DANGERS | The extension may lead to dangerous websites; display misinformation, inaccurate search results; track browsing, and collect data |
| ELIMINATION | Remove the extension by going to your browser settings |
| FURTHER STEPS | Use FortectIntego to fix any remaining damage and optimize the machine |
Browser hijacker promotional tricks
You may be wondering how this application ended up on your machine. Well, some users could have installed it willingly, thinking that they are getting a useful tool. Often, fraudsters create separate promotional websites for plugins like Keep It Secure. They write about all the non-existing features and try to convince people to install the app.
Sometimes they also use social engineering techniques[3] and claim that if users do not download the extension, their access to the Internet will be blocked or their system is going to crash. You should never believe messages that try to scare you into installing some kind of software.
Such promotional pages are spread through the Internet as well as possible. That is why you should avoid suspicious-looking pages, clicking on random links, and visiting websites that engage in illegal activities. If a new tab opens up after you click some button, close that tab and do not interact with the page.
Some browser hijackers can also slip through the extensive review process that official web stores perform. You should always do your research, no matter where you are downloading the digital tools from. Read the reviews, look at the ratings and the number of users. Pick those add-ons, that have plenty of feedback, and thousands of users.
Remove the bogus extension
You can remove browser add-ons by going to your settings. Find the list of extensions installed in your browser and remove the Keep It Secure plugin. We show how to do that in the guide below:
How to prevent from getting browser hijacker
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ What Is PPC? Learn the Basics of Pay-Per-Click (PPC) Marketing. WordStream. Advertising Solutions.
- ^ Chris Maus. What Are Cookies and Are They Dangerous?. Qkey. Secure Online Payment Providers.
- ^ Social Engineering. Imperva. Learning Center.
- ^ Will Dormann. Bundled Software and Attack Surface. Cmu. Carnegie Mellon University Software Engineering Institute Blog.










