.killedXXX file extension virus (Removal Guide) - Free Instructions
.killedXXX virus Removal Guide
What is .killedXXX file extension virus?
Crucial facts about .killedXXX file extension virus
.killedXXX virus has recently joined the excessive family of ransomware threats. In comparison with recently appeared Jhon Woddy and CloudSword, and Jew Crypt, the malware seems to be more elaborate. Since it contains striking resemblance to DNRansomare, it has gained the alternative title. This virus should not be underestimated since it is able to encrypt the files with AES algorithm. Consequently, decoding locked data is a challenge. Nonetheless, there is no need to give into distress even if this menace has seized your private data. Follow our recommendations on .killedXXX removal. You will also find suggestions about data recovery.
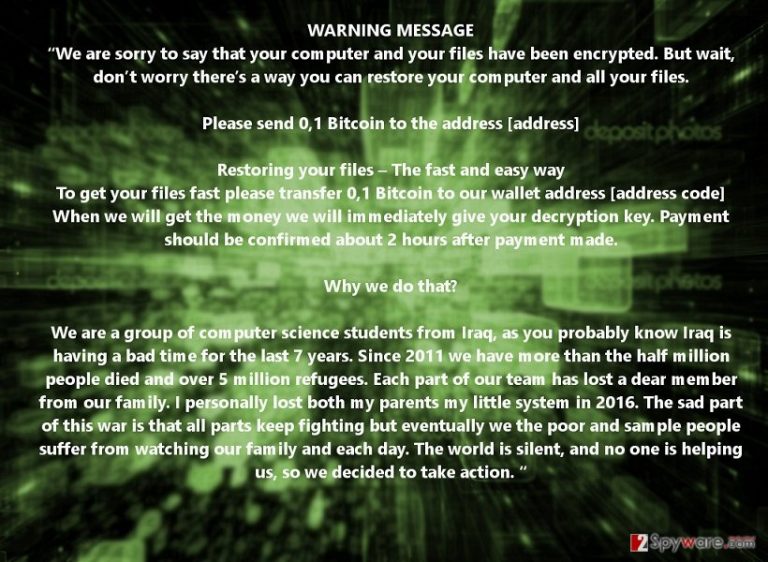
Ransomware has been one of the most discussed topics in the media concerning IT and cyber security. Regarding the activity in 2016 [1], journalists and activists already developed predictions for 2017. As some nervously are waiting for a destructive return of Locky virus, hundreds of online newspapers fish for visitors offering security and prevention means [2]. Crypto-malware is rapidly evolving [3]. Likewise, the virtual community must remain vigilant. Luckily, there has been a dozen of less bothersome threats. However, .killedXXX malware authors put effort into making it. The virus exploits commonly employed Rijndael or AES method to encode the files. After it completes its mission, it presents a touching story about the true motive. Here take a look at the message:
“We are sorry to say that your computer and your files have been encrypted. But wait, don’t worry there’s a way you can restore your computer and all your files.
Please send 0,1 Bitcoin to the address [address]
Restoring your files – The fast and easy way
To get your files fast, please transfer 0,1 Bitcoin to our wallet address [address code] When we will get the money we will immediately give your decryption key. Payment should be confirmed about 2 hours after payment made.
Why we do that?
We are a group of computer science students from Iraq, as you probably know Iraq is having a bad time for the last seven years. Since 2011 we have more than the half million people died and over 5 million refugees. Each part of our team has lost a dear member from our family. I personally lost both my parents my little system in 2016. The sad part of this war is that all parts keep fighting, but eventually we the poor and a sample people suffer from watching our family and each day. The world is silent, and no one is helping us, so we decided to take action. “
Though it tries to divert victims‘ attention, you should not fall for this bait. After all, such motive does not justify hackers‘ real intention to coax out money. As a result of this malware, all your files are encoded. Now they all bear .killedxxx file extension. The malware is able to lock computer‘s screen. Luckily, security experts have devised a workaround for this virus. Use this code to regain access to your system M3VZ>5BwGGVH. Therefore, there is no necessity to pay to the hackers. Ransomware is said to earn over 1 billion dollars revenue from ransomware victims [4]. On the contrary, IT experts encourage users to look for alternative solutions when possibles. Besides, transmitting the money does not boost the chances of file recovery.
The transmission of the ransomware
It is necessary to be aware of the distribution methods in order to prevent similar threat in the future. .killedXXX file extension virus might have penetrated your operating system via a corrupted spam email. Tread emails which ask you to review additional attachments with cautiousness. Messages which pretend to be sent from official institutions and contain grammar mistakes may signal of the destructive content disguised in the attached files. Verify the sender before reviewing the contents. In addition, .killedXXX hijack might have taken place due to the assault of a trojan or exploit kit [5]. It is much harder to deal with them without additional software assistance. Install FortectIntego to help you not only ward off cyber infections but remove .killedXXX virus as well.
.killedXXX termination guide
In case .killedxxx ransomware hasn‘t paralyzed your computer screen, enter Task Manager and end all suspicious tasks. Afterward, install a security program and run the scan. Do not forget to update. Updated virus database must have the latest virus definitions in order to detect the infection and related components. After you remove .killedXXX virus, you can proceed to file recovery steps. At the moment, there is no free decryption software released, but you might look up the alternative options indicated below.
Getting rid of .killedXXX virus. Follow these steps
Manual removal using Safe Mode
In case the virus completely has locked the computer screen and you struggle to proceed to .killedXXX removal, try the following option.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove .killedXXX using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of .killedXXX. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove .killedXXX from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by .killedXXX, you can use several methods to restore them:
Does Data Recovery Pro decrypt the files?
It might not succeed in recovering all the data but at least a portion of it. It is designed for file recovery after an unexpected system crash.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by .killedXXX ransomware;
- Restore them.
ShadowExplorer option
This method might solve your problems if the virus does not delete shadow volume copies in advance. The program recreates the affected files according to the shadow volume copies stored in the operating system.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from .killedXXX and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Nick Ismail. Learning from 2016: ransomware took the cloud computing industry by storm. Information Age. For IT leaders from the UK's fastest growsing enterprises.
- ^ Seung Lee . If You're Not Afraid of Ransomware (or Other Cyberattacks), You Are Crazy. News Week. News, in-depth analysis and reportage.
- ^ Javvad Malik. The Internet Of Ransomware. Huffpost Tech. Tech news, gaming, social networking.
- ^ Darren Pauli. Sundown exploit kit weaves Edge hack hole. The Register. Biting the hand that feeds IT .
- ^ Max Metzger. FBI says Ransomware soon becoming a billion dollar business. PC Tech Athority. Tech reviews, advice, news, and downloads .







