Legend ransomware (Virus Removal Guide) - Recovery Instructions Included
Legend virus Removal Guide
What is Legend ransomware?
Legend ransomware – a new variant of the VoidCrypt ransomware family
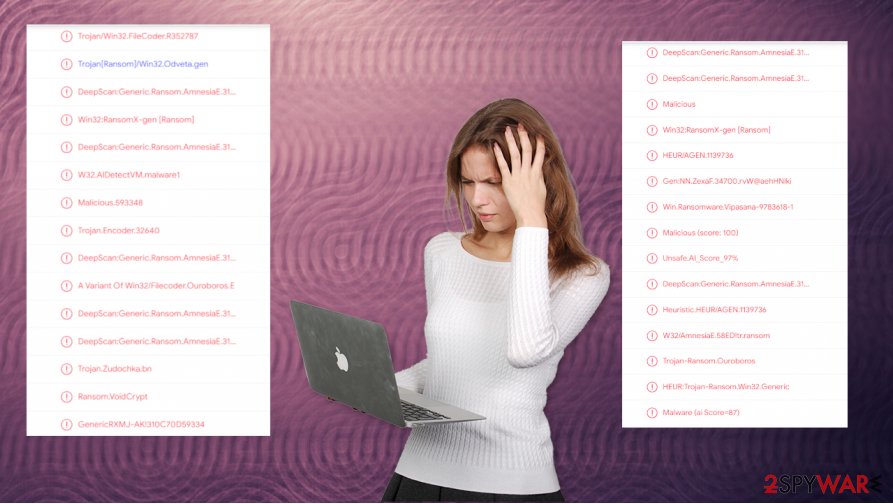
Legend ransomware is a cryptovirus that urges its victims to establish contact within 48 hours of the attack, or the price for decryption of encrypted files will be doubled. This file-locking virus derives from a fairly new VoidCrypt ransomware family that's been detected in April of 2020.
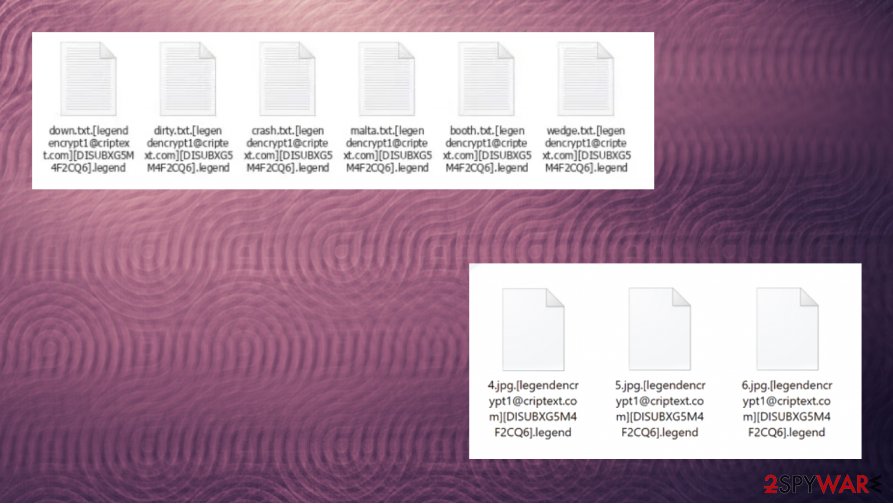
Cryptoviruses from this lineage uses a combination of AES and RSA coding algorithms to encrypt personal data on infected devices. During the encryption, Legend ransomware virus renames files in this manner: original filename.[legendencrypt1@criptext.com].[appointed unique user ID].legend extension. Although the VoidCrypt ransomware family is a new player in the ransomware game, if we can call it that, but it's presenting a new variant every couple of weeks. All versions present almost identical ransom notes, titled !INFO,HTA.
| name | Legend ransomware |
|---|---|
| type | Ransomware, cryptovirus |
| Family | VoidCrypt family |
| Ransom note | !INFO.HTA |
| Appended file extension | Non-executable files are appended with a complex three-part extension that goes like this – [legendencrypt1@criptext.com].[appointed unique user ID].legend |
| Criminal contact details | legendencrypt1@criptext.com, legendencrypt@criptext.com |
| Virus removal | Legend ransomware elimination should be done with professional anti-malware software to make sure it's completely removed |
| System health | Powerful system tune-up tools like the FortectIntego app should be used to revert any changes the infection might have done to the system |
One thing that differs with all the versions in the VoidCrypt virus family for sure, is the email given to contact the cybercriminals. In this case – legendencrypt1@criptext.com and legendencrypt@criptext.com. Previous versions of this cryptovirus include:
Everyday, computer users can get ransomware infections on their devices in numerous ways because cybercriminals are coming up with more sophisticated attacking techniques. But our research indicates that the most frequently used distribution method is spam emails (more on that in the second chapter of this article).
Anti-virus software to protect your passageways on the world wide web is a must these days. Reliable anti-malware applications like SpyHunter 5Combo Cleaner or Malwarebytes could prevent cryptoviruses such as Legend ransomware or others from infecting and encrypting your devices.
Back to the culprit of this article. Its ransom note instructs the victims to contact the assailants via two given emails, which should be done within 48 hours or the ransom price doubles, although the ransom amount isn't specified in the first place. The cybercriminals claim that only they have the ability to decrypt the locked files and offer free decryption of a few files.
As always, we do not recommend contacting the criminals, needless to say, to pay the ransom. Victims that meet the assailants' demands finance their criminal campaigns, and in no way does a payment guarantee that a working Legend ransomware decryption tool will be delivered.
The whole ransom note reads:
!!! Your Files Has Been Encrypted !!!
♦ your files has been locked with highest secure cryptography algorithm ♦
♦ there is no way to decrypt your files without paying and buying Decryption tool♦
♦ but after 48 hour decryption price will be double♦
♦ you can send some little files for decryption test♦
♦ test file should not contain valuable data♦
♦ after payment you will get decryption tool ( payment Should be with Bitcoin)♦
♦ so if you want your files dont be shy feel free to contact us and do an agreement on price♦
♦ !!! or Delete you files if you dont need them !!!
♦Your ID :-
our Email :legendencrypt1@criptext.com
In Case Of No Answer :legendencrypt@criptext.com
So in many cases, paying the ransom leads to a lose-lose situation. Instead, users should focus on Legend ransomware removal. Although, first, we recommend exporting all encrypted files to offline storage. There's no decryption tool available at the moment, but there's always hope that someone will create it in the near future.
When victims remove Legend ransomware, experts[1] suggest performing a system tune-up with powerful system repair tools like the FortectIntego app. This should be done in order to restore any modifications the computer virus might have done to the system registry and other key system settings.
The most common ransomware distribution technique and how to avoid it
Ransomware can infect devices in different ways, such as Remote Desktop Protocol (RDP) attacks,[2] drive-by downloads[3] from compromised websites, and through USB or other removable media. But the most common method used by cybercriminals is still phishing emails.
Phishing or spam emails can be written to trick a specific or a random person into either clicking on a hyperlink or downloading an attachment. Links redirect to sites where a ransomware payload file is downloaded automatically. Email attachments could contain .zip, .docx, .txt, or any other file type with a malicious script built-in.
As soon as either of these options is done, an infection starts right away. When a user receives an email and is unsure whether it's a phishing email or not, don't open anything in an email if it contains any of the following:
- grammatical mistakes
- addresses you not by your real name
- forces to visit a website right away
- urges to open an email attachment ASAP
- request personal, sensitive information
Guide for Legend ransomware virus removal and system tune-up
Dealing with Legend ransomware removal could be a difficult task for a novice computer user. That's why we recommend leaving this dirty business to professional anti-malware software like the SpyHunter 5Combo Cleaner or Malwarebytes to do automatically and with a push of a button.
However, if you didn't keep backups of your essential data, then before you remove Legend ransomware, you should copy all encrypted files to offline storage, like a USB drive or any other kind of external storage. That way, if a decryption tool gets made, you could unlock it.
After you've eliminated the infection, don't forget to clean up your computer system. Ransomware like Legend ransomware virus tends to mess up system settings, leading to devices exhibiting abnormal behavior. Use the FortectIntego or any other powerful system repair tool to restore those settings.
Getting rid of Legend virus. Follow these steps
Manual removal using Safe Mode
Infection elimination in Safe Mode with Networking[
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Legend using System Restore
Removing malware with System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Legend. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Legend from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Legend, you can use several methods to restore them:
Use Data Recovery Pro for file retrieval
This software might recover .legend extension files.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Legend ransomware;
- Restore them.
Restoring files with Windows Previous Version feature
With this Windows function, users could be able to restore .legend extension files to their previous versions.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Shadow Explorer – a powerful data recovery tool
When cryptoviruses don't delete Shadow Volume Copies, then Shadow Explorer might restore files.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No decryption tool is currently available
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Legend and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Virukset. Virukset. Spyware security and news.
- ^ Jaikumar Vijayan. What is an RDP attack? 7 tips for mitigating your exposure. Csoonline. Security news, features and analysis.
- ^ Drive-by download. Wikipedia. The free encyclopedia.





















