Like ransomware (Removal Guide) - Decryption Steps Included
Like virus Removal Guide
What is Like ransomware?
Like ransomware is a virus that stealthily infiltrates the system and gives you 72 hours to unlock your encrypted files
Like ransomware is a file-encrypting virus that modifies most of the data stored on the system. As typical ransomware, this virus encrypts files as soon as its executable[1] file is installed on the system. The malicious payload an e triggered by a file from an email or the malicious site. For data locking, it uses a sophisticated encryption method[2] and marks the affected data with .like file extension. After this procedure, the user's images, videos, documents, and similar files become useless.
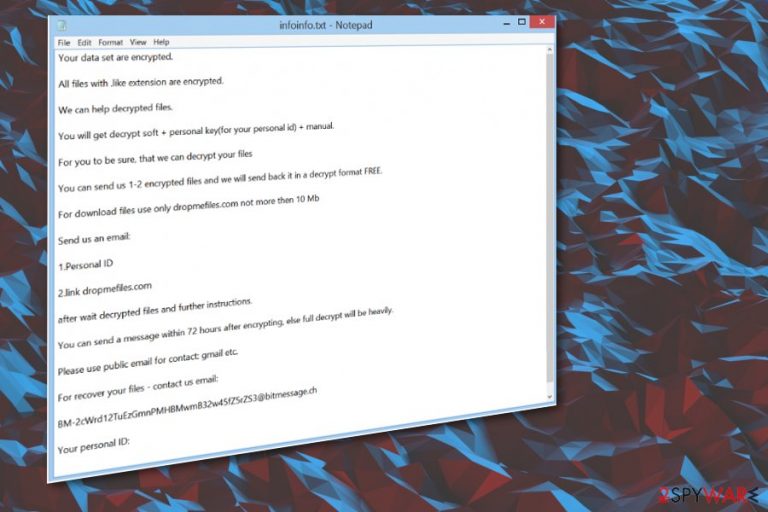
Additionally, the threat generates a ransom note called infoinfo.txt and, in this case, places this file in every existing folder on your PC system. The ransom note is used to convince the victim into paying a required ransom in exchange for files' decryption. However, you can always use alternative methods to recover your encrypted files. Malware mainly deletes itself from the machine once those files get locked, but you need to fully clear the machine to recover performance and the affected data. You can find the helpful guide below to achieve the best goals.
| Name | Like ransomware |
|---|---|
| Type | Cryptovirus |
| File extension | .like is the appendix that marks affected files from other safe pieces on the machine |
| Ransom note | infoinfo.txt |
| Contact email | BM-2cWrd12TuEzGmnPMHBMwmB32w45fZ5rZS3@bitmessage.ch |
| Distribution | Spam email campaigns, malicious sites, other malware |
| Symptoms | Files become locked without the ability to open them; a ransom message appears on every folder |
| Elimination | Use an anti-malware tool to terminate the virus |
| Repair | The machine gets affected on a different level. You can run FortectIntego to fic and solve various problems |
The ransomware encrypts most of your stored data and locks it with the .like appendix. It is still unknown what family this malware is hailing from. However, it is very similar to Support_wc@bitmessage.ch ransomware or Waiting ransomware which is using waiting@bitmessage.ch email for making a contact with potential ransom payers.
To make the victim's files useless, the malware is using either symmetric or asymmetric algorithms. After the encryption procedure is finished, files cannot be used in any way. According to the ransom note, Like virus gives its victim only 72 hours to send the money to the provided bitcoin wallet.
Hackers are also offering to test their decryption services by sending them a few encrypted files which are no bigger than 10Mb. However, even if this test works, there is no guarantee that the decryption tool for this crypto virus really exists.
In the ransom note that Like ransomware virus places on every folder, you may see hackers' contact email which is BM-2cWrd12TuEzGmnPMHBMwmB32w45fZ5rZS3@bitmessage.ch. However, as we have already warned you, you shouldn't write them or pay the ransom. The people behind this software are criminals, and cannot be trusted in any way.
Once the virus encrypts files, it displays such ransom note:
Your data set are encrypted.
All files with .like extension are encrypted.
We can help decrypted files.
You will get decrypt soft + personal key(for your personal id) + manual.
For you to be sure, that we can decrypt your files
You can send us 1-2 encrypted files and we will send back it in a decrypt format FREE.
For download files use only dropmefiles.com not more then 10 Mb
Send us an email:
1.Personal ID
2.link dropmefiles.com
after wait decrypted files and further instructions.
You can send a message within 72 hours after encrypting, else full decrypt will be heavily.
Please use public email for contact: gmail etc.
For recover your files – contact us email:
BM-2cWrd12TuEzGmnPMHBMwmB32w45fZ5rZS3@bitmessage.ch
Your personal ID: –
If your files are locked by this malware, make sure that you get rid of this virus at first and only then try to recover the encrypted data from a backup. To make your system clear again, remove any threats using anti-malware like SpyHunter 5Combo Cleaner, Malwarebytes. Then, try data recovery suggestions that are provided down below.
Note that ransomware can disable your antivirus program. In addition, viruses like this can change the Windows Registry or write new tasks to make sure that they become active each time your PC is rebooted. This means that the virus can silently work in the background without your knowledge. However, if you happen to notice any suspicious activity, reboot your PC to Safe mode to disable the malware on your computer and proceed with Like ransomware removal.
Hackers adopt different approaches to install malware on the target computer
During the last couple of years, virus developers have found many different techniques to infiltrate computers. When dealing with ransomware, the most common spreading technique is spam email campaigns. Beware that email messages can be filled with malicious content, including:
- Malicious attachments (.pdf, .xls, .xlsx, .png, etc.);
- Fraudulent links;
- Other fake information.
Researchers[3] always advise paying more attention to emails you find in your email inbox. Make sure you always double-check every message you find in your inbox. Malicious people often can disguise their content behind the legal names of other services or companies, so you should always check these messages for grammar or typo mistakes. Alternatively, contact the sender to see if it is a real person. Finally, clean your spam email box more often and do not open any suspicious attachments.
Detect and remove any threats found on the machine using anti-malware applications
To remove Like ransomware and get back to safe use on the computer, you should use trustworthy anti-malware programs like SpyHunter 5Combo Cleaner or Malwarebytes. These tools can detect and remove malware you already have on your system. Besides, they will block potential threats in the future. It is crucial not to use manual removal methods when dealing with malware because of the possibility to lead your system into damage.
When proceeding with Like file virus removal, remember to use the latest programs' versions. If you cannot launch the scanner, reboot your computer to Safe mode with Networking. However, make sure you double-check the system with anti-malware software when on normal mode as well. You can try FortectIntego and find any data or system issues. Then, check our suggestions down below for data recovery methods.
Getting rid of Like virus. Follow these steps
Important steps to take before you begin malware removal
File encryption and ransomware infection are two independent processes (although the latter would not be possible without the former). However, it is important to understand that malware performs various changes within a Windows operating system, fundamentally changing the way it works.
IMPORTANT for those without backups! →
If you attempt to use security or recovery software immediately, you might permanently damage your files, and even a working decryptor then would not be able to save them.
Before you proceed with the removal instructions below, you should copy the encrypted files onto a separate medium, such as USB flash drive or SSD, and then disconnect them from your computer. Encrypted data does not hold any malicious code, so it is safe to transfer to other devices.
The instructions below might initially seem overwhelming and complicated, but they are not difficult to understand as long as you follow each step in the appropriate order. This comprehensive free guide will help you to handle the malware removal and data recovery process correctly.
If you have any questions, comments, or are having troubles with following the instructions, please do not hesitate to contact us via the Ask Us section.
IMPORTANT! →
It is vital to eliminate malware infection from the computer fully before starting the data recovery process, otherwise ransomware might re-encrypt retrieved files from backups repeatedly.
Scan your system with anti-malware
If you are a victim of ransomware, you should employ anti-malware software for its removal. Some ransomware can self-destruct after the file encryption process is finished. Even in such cases, malware might leave various data-stealing modules or could operate in conjunction with other malicious programs on your device.
SpyHunter 5Combo Cleaner or Malwarebytes can detect and eliminate all ransomware-related files, additional modules, along with other viruses that could be hiding on your system. The security software is really easy to use and does not require any prior IT knowledge to succeed in the malware removal process.
Repair damaged system components
Once a computer is infected with malware, its system is changed to operate differently. For example, an infection can alter the Windows registry database, damage vital bootup and other sections, delete or corrupt DLL files, etc. Once a system file is damaged by malware, antivirus software is not capable of doing anything about it, leaving it just the way it is. Consequently, users might experience performance, stability, and usability issues, to the point where a full Windows reinstall is required.
Therefore, we highly recommend using a one-of-a-kind, patented technology of FortectIntego repair. Not only can it fix virus damage after the infection, but it is also capable of removing malware that has already broken into the system thanks to several engines used by the program. Besides, the application is also capable of fixing various Windows-related issues that are not caused by malware infections, for example, Blue Screen errors, freezes, registry errors, damaged DLLs, etc.
- Download the application by clicking on the link above
- Click on the ReimageRepair.exe

- If User Account Control (UAC) shows up, select Yes
- Press Install and wait till the program finishes the installation process

- The analysis of your machine will begin immediately

- Once complete, check the results – they will be listed in the Summary
- You can now click on each of the issues and fix them manually
- If you see many problems that you find difficult to fix, we recommend you purchase the license and fix them automatically.

By employing FortectIntego, you would not have to worry about future computer issues, as most of them could be fixed quickly by performing a full system scan at any time. Most importantly, you could avoid the tedious process of Windows reinstallation in case things go very wrong due to one reason or another.
Restore files using data recovery software
Since many users do not prepare proper data backups prior to being attacked by ransomware, they might often lose access to their files permanently. Paying criminals is also very risky, as they might not fulfill the promises and never send back the required decryption tool.
While this might sound terrible, not all is lost – data recovery software might be able to help you in some situations (it highly depends on the encryption algorithm used, whether ransomware managed to complete the programmed tasks, etc.). Since there are thousands of different ransomware strains, it is immediately impossible to tell whether third-party software will work for you.
Therefore, we suggest trying regardless of which ransomware attacked your computer. Before you begin, several pointers are important while dealing with this situation:
- Since the encrypted data on your computer might permanently be damaged by security or data recovery software, you should first make backups of it – use a USB flash drive or another storage.
- Only attempt to recover your files using this method after you perform a scan with anti-malware software.
Install data recovery software
- Download Data Recovery Pro.
- Double-click the installer to launch it.

- Follow on-screen instructions to install the software.

- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders where you want the files to be recovered from.

- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.

- Press Scan and wait till it is complete.

- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.

Create data backups to avoid file loss in the future
One of the many countermeasures for home users against ransomware is data backups. Even if your Windows get corrupted, you can reinstall everything from scratch and retrieve files from backups with minimal losses overall. Most importantly, you would not have to pay cybercriminals and risk your money as well.
Therefore, if you have already dealt with a ransomware attack, we strongly advise you to prepare backups for future use. There are two options available to you:
- Backup on a physical external drive, such as a USB flash drive or external HDD.
- Use cloud storage services.
The first method is not that convenient, however, as backups need to constantly be updated manually – although it is very reliable. Therefore, we highly advise choosing cloud storage instead – it is easy to set up and efficient to sustain. The problem with it is that storage space is limited unless you want to pay for the subscription.
Using Microsoft OneDrive
OneDrive is a built-in tool that comes with every modern Windows version. By default, you get 5 GB of storage that you can use for free. You can increase that storage space, but for a price. Here's how to setup backups for OneDrive:
- Click on the OneDrive icon within your system tray.
- Select Help & Settings > Settings.
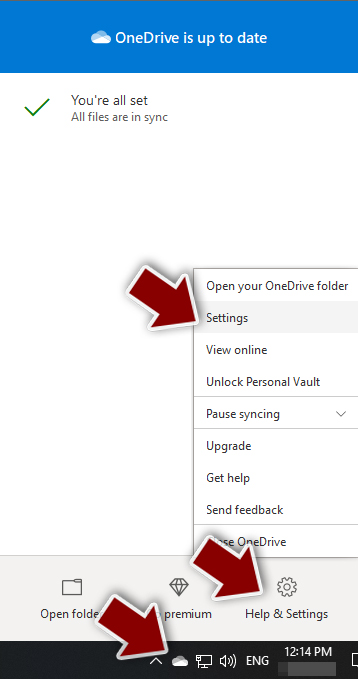
- If you don't see your email under the Account tab, you should click Add an account and proceed with the on-screen instructions to set yourself up.
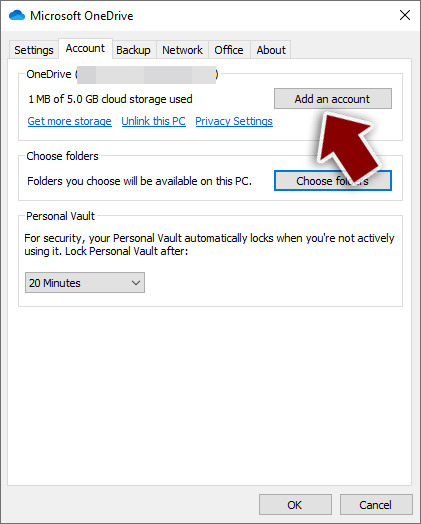
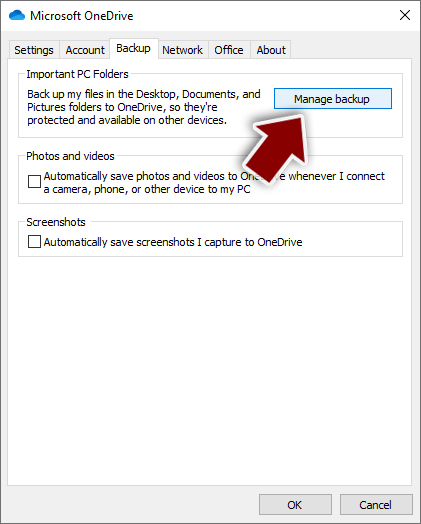
- Once done, move to the Backup tab and click Manage backup.
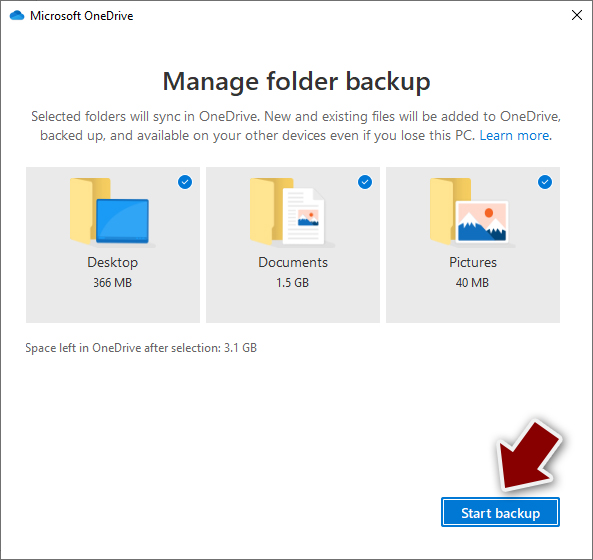
- Select Desktop, Documents, and Pictures, or a combination of whichever folders you want to backup.
- Press Start backup.
After this, all the files that are imported into the above-mentioned folders will be automatically backed for you. If you want to add other folders or files, you have to do that manually. For that, open File Explorer by pressing Win + E on your keyboard, and then click on the OneDrive icon. You should drag and drop folders you want to backup (or you can use Copy/Paste as well).
Using Google Drive
Google Drive is another great solution for free backups. The good news is that you get as much as 15GB for free by choosing this storage. There are also paid versions available, with significantly more storage to choose from.
You can access Google Drive via the web browser or use a desktop app you can download on the official website. If you want your files to be synced automatically, you will have to download the app, however.
- Download the Google Drive app installer and click on it.

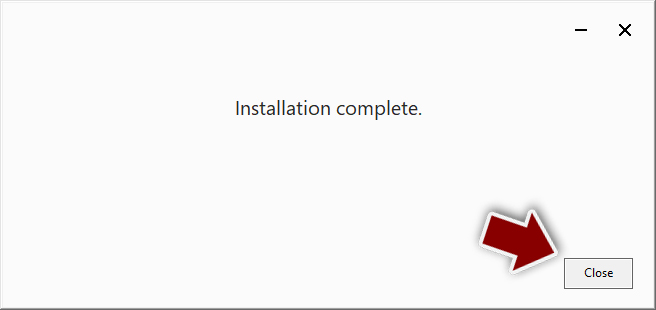
- Wait a few seconds for it to be installed.
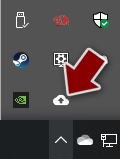
- Now click the arrow within your system tray – you should see Google Drive icon there, click it once.
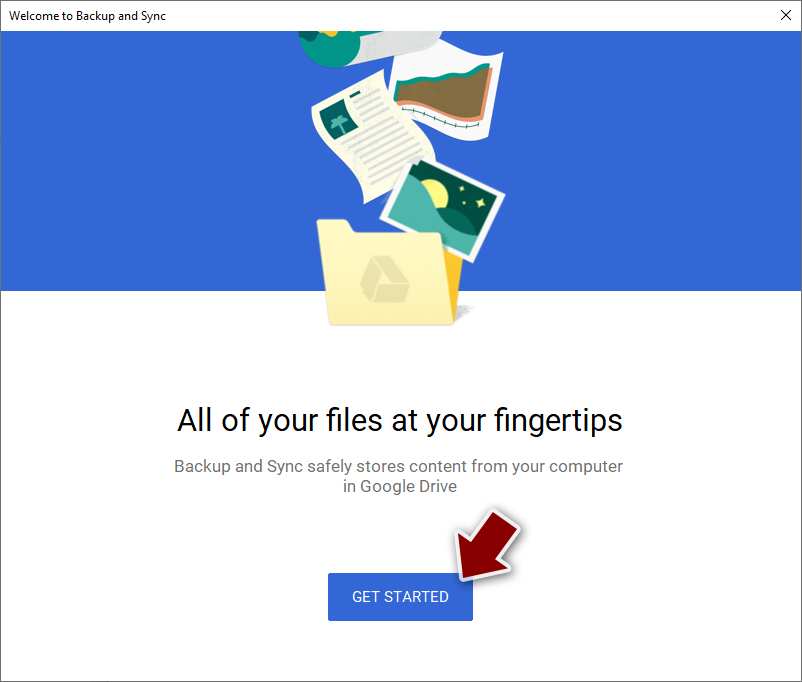
- Click Get Started.
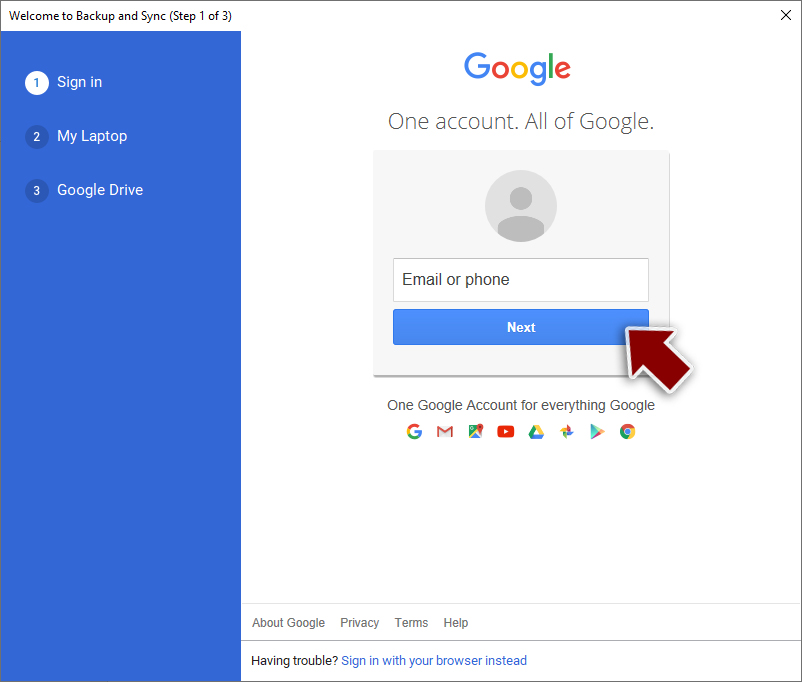
- Enter all the required information – your email/phone, and password.
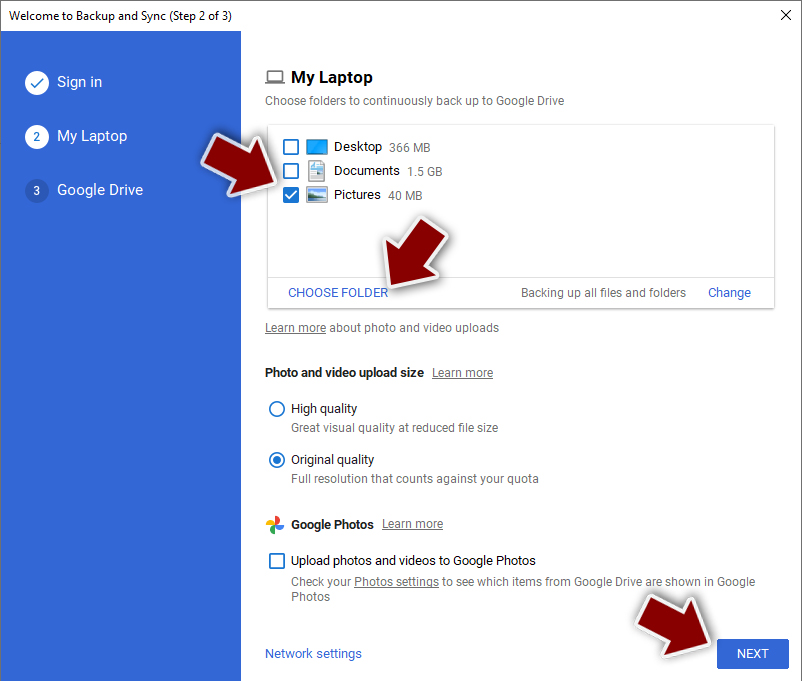
- Now pick what you want to sync and backup. You can click on Choose Folder to add additional folders to the list.
- Once done, pick Next.
- Now you can select to sync items to be visible on your computer.
- Finally, press Start and wait till the sync is complete. Your files are now being backed up.
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Like and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Executable file. Computerhope. Free computer related dictionary.
- ^ Sarah. Ransomware encryption methods. Emisoft blog. Security advice.
- ^ LesVirus. LesVirus. Spyware news.
