LockFile ransomware (virus) - Recovery Instructions Included
LockFile virus Removal Guide
What is LockFile ransomware?
LockFile ransomware locks your files away and demands payment
Ransomware attacks have been on the rise all over the world. The most targeted entities are big companies, as you can get more money from them than private individuals. LockFile is no exception. The new group has been active since June 2021 and has targeted 10 organizations in a month. Victims are in manufacturing, financial, engineering, legal, business, and travel and tourism sectors.
The attackers gain access to victims' networks via vulnerabilities within the Microsoft Exchange Servers.[1] Once cybercriminals breach the network, they move laterally with elevated privileges. A final stage of the attack ends with the deployment of ransomware, which infects each of the Windows PCs within the network.
The files are encrypted using AES-256 and RSA-1024 encryption algorithms. This prevents the user from opening documents, pictures, videos, and other files, making it extremely difficult to recover data when no backups are available.
During the encryption process, the ransomware appends every file with an extension .lockfile. For example, if the file name is picture.jpg, it is renamed to picture.jpg.lockfile. Data encryption is the main indication of the attack, although, within corporate environments, intrusion can often be spotted early. This is also one of the reasons why ransomware is installed during the step of the attack.
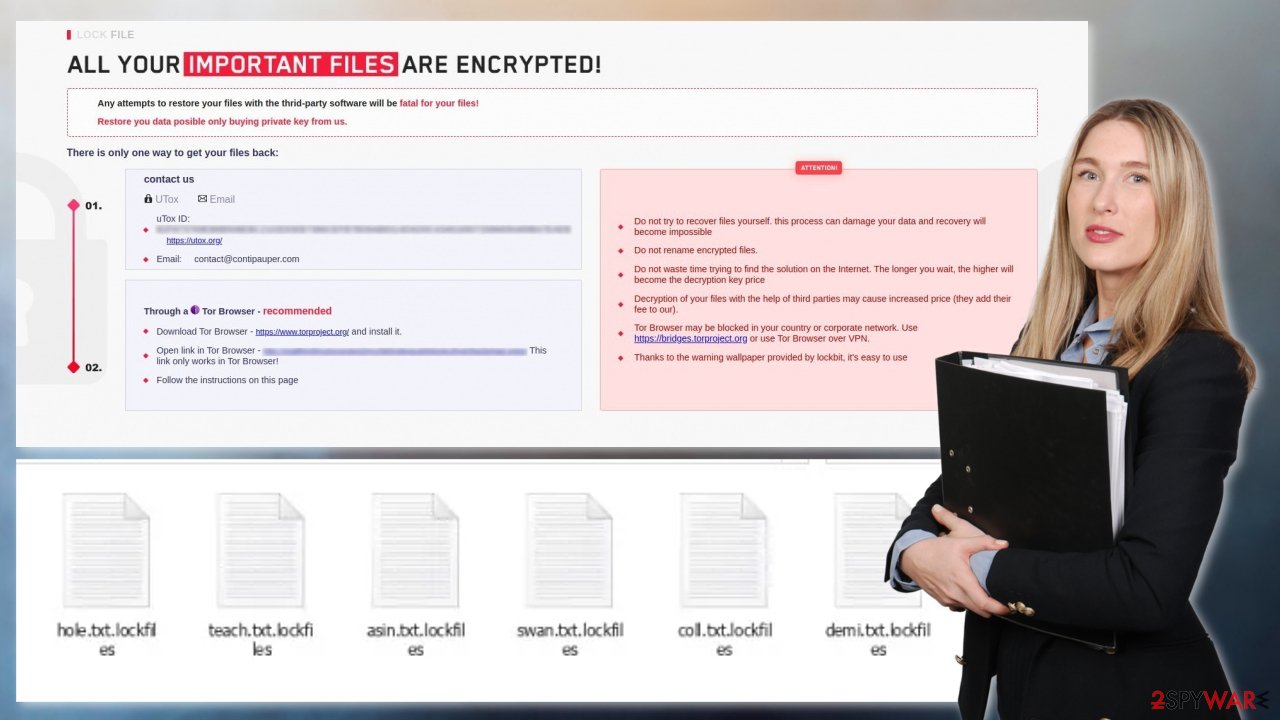
Shortly after file encryption is complete, LockFile ransomware sends a ransom note – a .hta file. Its' full name depends on the victim's computer name. This filename contains ransomware name, computer name, and a string of random characters. For example – LOCKFILE-README-COMPUTERNAME-7344587665.hta. The HTA file provides victims with instructions on what attackers want them to do. The note is similar to the one used by the LockBit ransomware group. It also includes a reference to the Conti ransomware.
The attackers state that the only way to retrieve files is to pay them. The ransom amount is not listed; perhaps it is a subject of negotiation. Victims are prompted to contact the attackers via the email address contact@contipauper.com or a link that is only accessible from the Tor browser.[2]
You should never pay the ransom because attackers are not obliged to provide you with a decryption key after payment. You might end up without money and your files. The only thing you can do is try to remove the malware and recover your files and system.
| NAME | LockFile ransomware |
| TYPE | Ransomware, cryptovirus, data locking malware |
| ENCRYPTION METHOD | AES+RSA |
| FILE EXTENSION | .lockfile |
| RANSOM NOTE | [victim_name]-LOCKFILE-README.hta |
| FILE RECOVERY | Recovering the data is close to impossible if you do not have backups |
| MALWARE REMOVAL | Use professional security software like SpyHunter 5Combo Cleaner to perform a full scan of your machine |
| SYSTEM FIX | To remediate your operating system and take care of errors, crashes scan it with the FortectIntego maintenance tool. |
The full .hta message after encryption from the attackers reads as follows:
LOCK FILE
ALL YOUR IMPORTANT FILES ARE ENCRYPTED!
Any attempts to restore your files with the thrid-party software will be fatal for your files!
Restore you data posible only buying private key from us.
There is only one way to get your files back:contact us
qTox ID: hxxps://tox.chat/download.html
Email: contact@contipauper.comThrough a Tor Browser – recommended
Download Tor Browser – hxxps://www.torproject.org/ and install it.
Open link in Tor Browser – hxxp://zqaflhty5hyziovsxgqvj2mrz5e5rs6oqxzb54zolccfnvtn5w2johad.onion This link only works in Tor Browser!
Follow the instructions on this pageATTENTION!
Do not try to recover files yourself. this process can damage your data and recovery will become impossible
Do not rename encrypted files.
Do not waste time trying to find the solution on the Internet. The longer you wait, the higher will become the decryption key price
Decryption of your files with the help of third parties may cause increased price (they add their fee to our).
Tor Browser may be blocked in your country or corporate network. Use https://bridges.torproject.org or use Tor Browser over VPN.
Thanks to the warning wallpaper provided by lockbit, it's easy to use
A never seen before strain of ransomware
LockFile virus seems to be a new threat in the ransomware universe. The investigations indicate that the attackers gain access to networks via Microsoft Exchange Servers and then use the incompletely patched PetitPotam[3] vulnerability to gain access to the domain controller and spread across the network. It is still unknown how attackers gain initial access to the Microsoft Exchange Servers.
Microsoft patched these vulnerabilities in May, but hackers have been able to recreate the exploit, which is now being used to enable the LockFile attacks. The hackers can also infiltrate Exchange servers that were not updated.
What to do if you were affected?
The most important thing is – do not try to retrieve files first, as it might result in permanent data loss. The first step has to be the elimination of malware to stop it from encrypting your files again. To remove the LockFile virus, you should use an anti-malware tool to scan your system, such as SpyHunter 5Combo Cleaner or Malwarebytes. This security software should find all the malicious files and entries and remove them automatically for you.
Once malware is deleted, you can proceed with the data recovery methods we provide below. If malware is not letting you use antivirus in normal mode, access Safe Mode and perform a full system scan from there:
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.
![Windows XP/7 Windows XP/7]()
Windows 10 / Windows 8
- Right-click on Start button and select Settings.
- Scroll down to pick Update & Security.
![Update & Security Update & Security]()
- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.
![Recovery Recovery]()
- Select Troubleshoot.
![Choose an option Choose an option]()
- Go to Advanced options.
![Advanced options Advanced options]()
- Select Startup Settings.
![Startup settings Startup settings]()
- Click Restart.
- Press 5 or click 5) Enable Safe Mode with Networking.
![Press F5 to enable Safe Mode with Networking Press F5 to enable Safe Mode with Networking]()
Data recovery
Many users do not back up their data properly, which is devastating because they might completely lose access to their files. Paying cybercriminals in cryptocurrencies is very risky as often, even after payment, victims do not receive decryption keys. Paying them money also supports their activities further and leads to more victims.
You can try to get back your data with data recovery software. The recovery of the files is not guaranteed as there are thousands of ransomware strains. We suggest trying regardless of which ransomware attacked your computer. Before you begin, there are a couple of important things to note:
- Since the encrypted data on your computer might permanently be damaged by security or data recovery software, you should first make backups of it – use a USB flash drive or another storage.
- Only attempt to recover your files using this method after you perform a scan with anti-malware software.
Install data recovery software
- Download Data Recovery Pro.
- Double-click the installer to launch it.
![LockFile ransomware LockFile ransomware]()
- Follow on-screen instructions to install the software.
![Install program Install program]()
- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders where you want the files to be recovered from.
![Select what to recover Select what to recover]()
- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.
![Select Deep scan Select Deep scan]()
- Press Scan and wait till it is complete.
![Scan Scan]()
- You can now pick which folders/files to recover – don't forget you also have the option to search by the file name!
- Press Recover to retrieve your files.
![Recover files Recover files]()
Fix your operating system
After a malware infection, users might experience performance, stability, and usability issues, to the point where a full Windows reinstall is required. These types of infections can alter the Windows registry database, damage vital bootup and other sections, delete or corrupt DLL files, etc. Once a system file is damaged by malware, antivirus software is not going to help you.
This problem requires a different tool – FortectIntego. It can fix damage caused by the infection like Blue Screen errors, freezes, registry errors, damaged DLLs, etc. By using this maintenance tool, you could avoid Windows reinstallation. To begin the process:
- Download the application by clicking on the link above
- Click on the ReimageRepair.exe
![Reimage download Reimage download]()
- If User Account Control (UAC) shows up, select Yes
- Press Install and wait till the program finishes the installation process
![Reimage installation Reimage installation]()
- The analysis of your machine will begin immediately
![Reimage scan Reimage scan]()
- Once complete, check the results – they will be listed in the Summary
- You can now click on each of the issues and fix them manually
- If you see many problems that you find difficult to fix, we recommend you purchase the license and fix them automatically.
![Reimage results Reimage results]()
Prevent ransomware attacks in the future
To protect yourself from malware infection, you should always be careful when opening emails from unknown senders. Do not download attached files that you were not expecting especially if it is an MS Office file. The most important part is checking the sender, their email address, searching the text for grammar and spelling mistakes. If the message comes from an unidentifiable sender or includes many mistakes, you should delete it without opening it. Also, scan all received attachments with reliable anti-malware software.
Additionally, ransomware infections can get delivered via peer-to-peer file-sharing networks.[4] That includes “free” or “cracked” software. Also, malware can use the disguise of a fake software update.[5] Get all the upgrades only from official websites, never from a window that popped up or a random website that appeared suddenly.
Below, you will find additional information on how you can back up your files so you would not lose them if this happens again and organizations you can report to about the attacks.
Getting rid of LockFile virus. Follow these steps
Isolate the infected computer
Some ransomware strains aim to infect not only one computer but hijack the entire network. As soon as one of the machines is infected, malware can spread via network and encrypt files everywhere else, including Network Attached Storage (NAS) devices. If your computer is connected to a network, it is important to isolate it to prevent re-infection after ransomware removal is complete.
The easiest way to disconnect a PC from everything is simply to plug out the ethernet cable. However, in the corporate environment, this might be extremely difficult to do (also would take a long time). The method below will disconnect from all the networks, including local and the internet, isolating each of the machines involved.
- Type in Control Panel in Windows search and press Enter
- Go to Network and Internet

- Click Network and Sharing Center

- On the left, pick Change adapter settings

- Right-click on your connection (for example, Ethernet), and select Disable

- Confirm with Yes.
If you are using some type of cloud storage you are connected to, you should disconnect from it immediately. It is also advisable to disconnect all the external devices, such as USB flash sticks, external HDDs, etc. Once the malware elimination process is finished, you can connect your computers to the network and internet, as explained above, but by pressing Enable instead.
Create data backups to avoid file loss in the future
One of the many countermeasures for home users against ransomware is data backups. Even if your Windows get corrupted, you can reinstall everything from scratch and retrieve files from backups with minimal losses overall. Most importantly, you would not have to pay cybercriminals and risk your money as well.
Therefore, if you have already dealt with a ransomware attack, we strongly advise you to prepare backups for future use. There are two options available to you:
- Backup on a physical external drive, such as a USB flash drive or external HDD.
- Use cloud storage services.
The first method is not that convenient, however, as backups need to constantly be updated manually – although it is very reliable. Therefore, we highly advise choosing cloud storage instead – it is easy to set up and efficient to sustain. The problem with it is that storage space is limited unless you want to pay for the subscription.
Using Microsoft OneDrive
OneDrive is a built-in tool that comes with every modern Windows version. By default, you get 5 GB of storage that you can use for free. You can increase that storage space, but for a price. Here's how to setup backups for OneDrive:
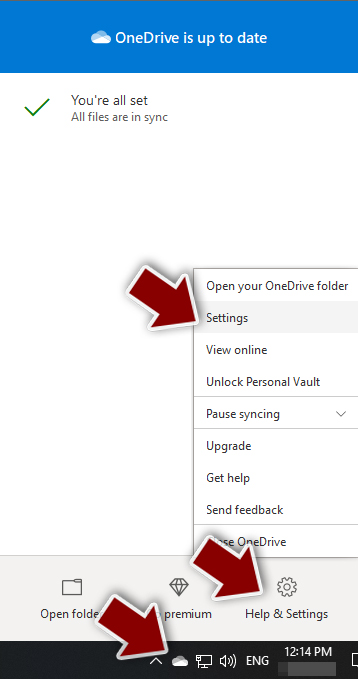
- Click on the OneDrive icon within your system tray.
- Select Help & Settings > Settings.

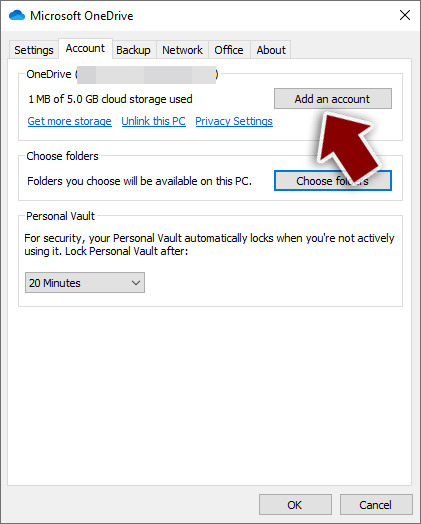
- If you don't see your email under the Account tab, you should click Add an account and proceed with the on-screen instructions to set yourself up.

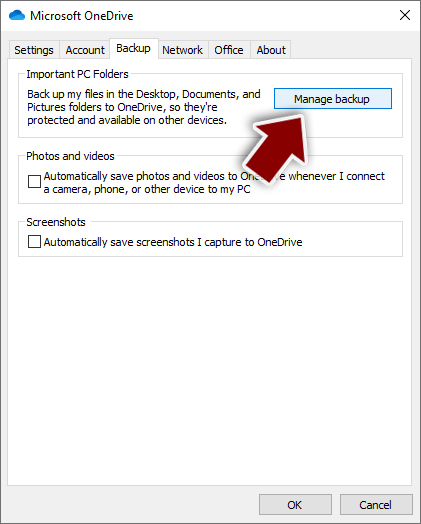
- Once done, move to the Backup tab and click Manage backup.

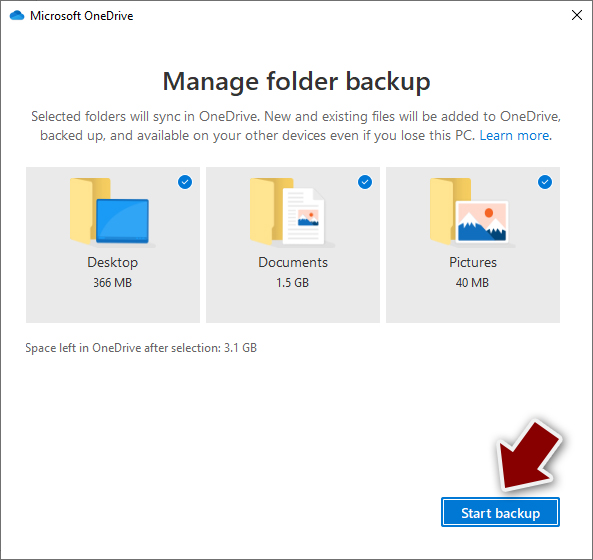
- Select Desktop, Documents, and Pictures, or a combination of whichever folders you want to backup.
- Press Start backup.

After this, all the files that are imported into the above-mentioned folders will be automatically backed for you. If you want to add other folders or files, you have to do that manually. For that, open File Explorer by pressing Win + E on your keyboard, and then click on the OneDrive icon. You should drag and drop folders you want to backup (or you can use Copy/Paste as well).
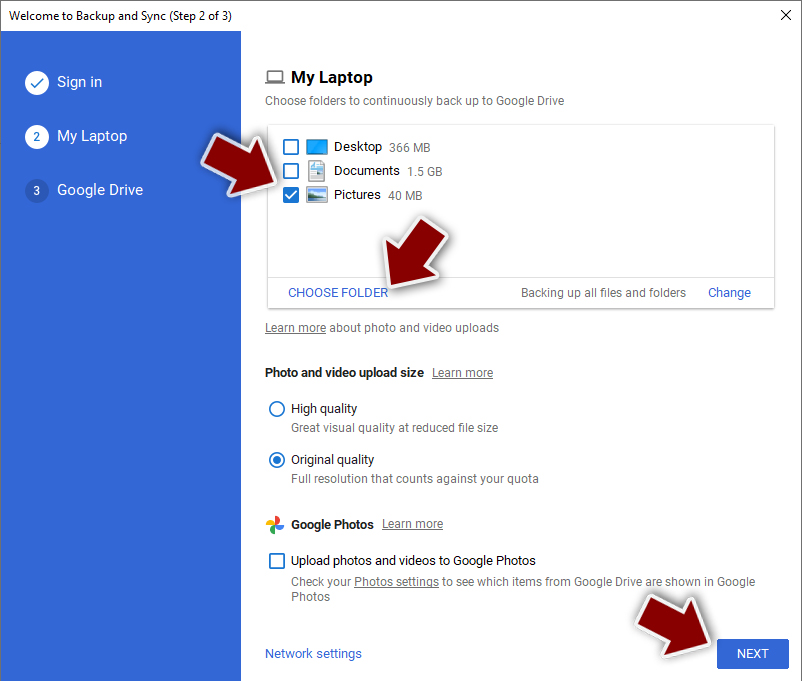
Using Google Drive
Google Drive is another great solution for free backups. The good news is that you get as much as 15GB for free by choosing this storage. There are also paid versions available, with significantly more storage to choose from.
You can access Google Drive via the web browser or use a desktop app you can download on the official website. If you want your files to be synced automatically, you will have to download the app, however.
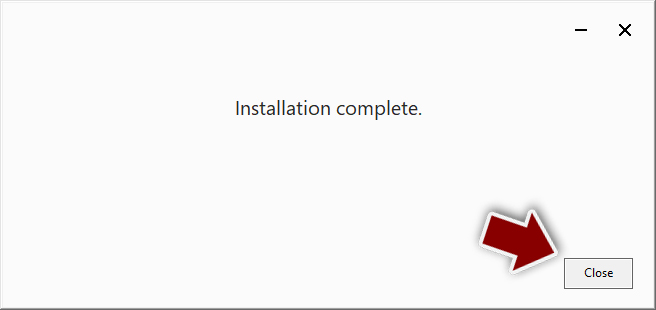
- Download the Google Drive app installer and click on it.

- Wait a few seconds for it to be installed.

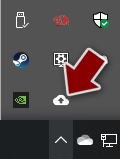
- Now click the arrow within your system tray – you should see Google Drive icon there, click it once.

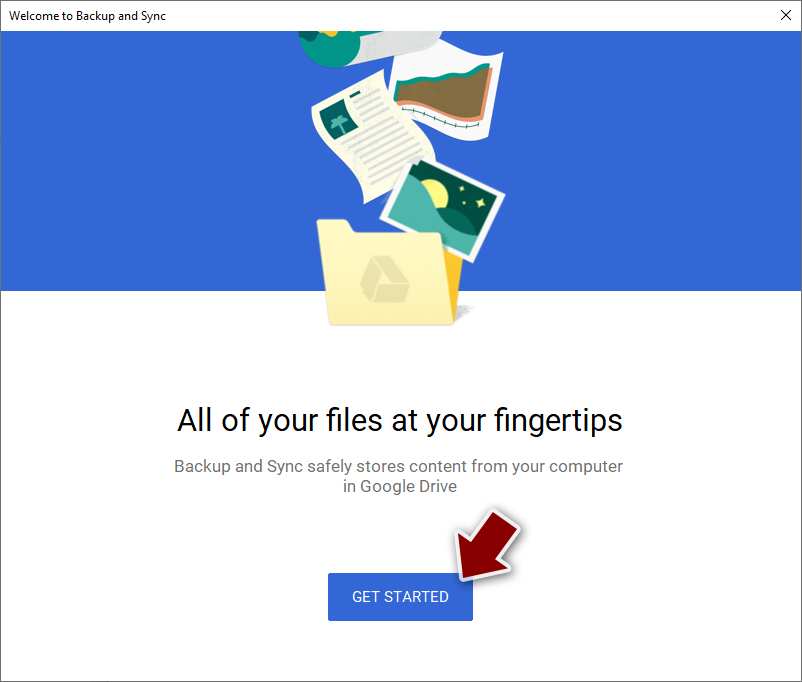
- Click Get Started.

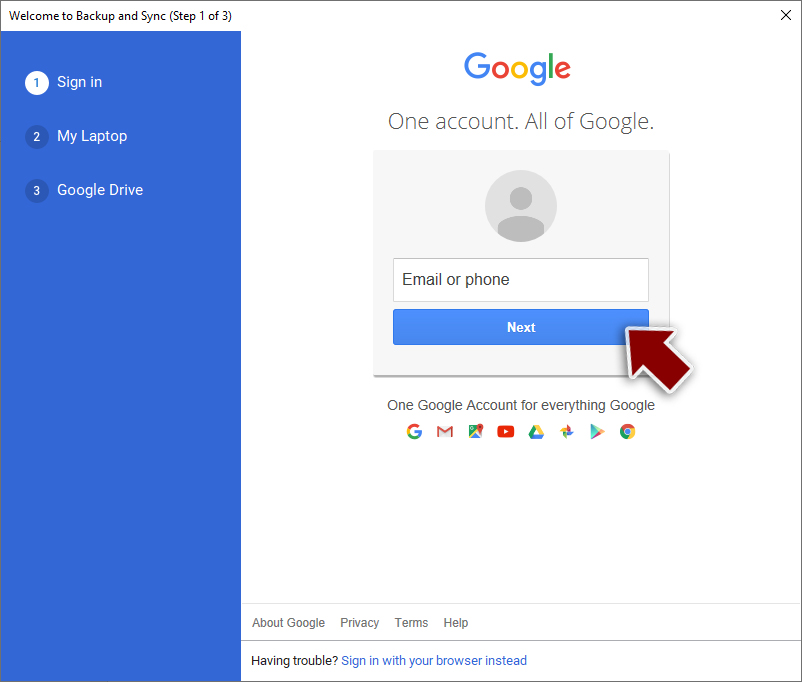
- Enter all the required information – your email/phone, and password.

- Now pick what you want to sync and backup. You can click on Choose Folder to add additional folders to the list.
- Once done, pick Next.

- Now you can select to sync items to be visible on your computer.
- Finally, press Start and wait till the sync is complete. Your files are now being backed up.
Report the incident to your local authorities
Ransomware is a huge business that is highly illegal, and authorities are very involved in catching malware operators. To have increased chances of identifying the culprits, the agencies need information. Therefore, by reporting the crime, you could help with stopping the cybercriminal activities and catching the threat actors. Make sure you include all the possible details, including how did you notice the attack, when it happened, etc. Additionally, providing documents such as ransom notes, examples of encrypted files, or malware executables would also be beneficial.
Law enforcement agencies typically deal with online fraud and cybercrime, although it depends on where you live. Here is the list of local authority groups that handle incidents like ransomware attacks, sorted by country:
- USA – Internet Crime Complaint Center IC3
- United Kingdom – ActionFraud
- Canada – Canadian Anti-Fraud Centre
- Australia – ScamWatch
- New Zealand – ConsumerProtection
- Germany – Polizei
- France – Ministère de l'Intérieur

If your country is not listed above, you should contact the local police department or communications center.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from LockFile and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Microsoft Exchange Server. Wikipedia. Free Encyclopedia.
- ^ Stuart Dredge. What is Tor? A beginner's guide to the privacy tool. TheGuardian. Technology. Internet.
- ^ Caitlin Condon. PetitPotam: Novel Attack Chain Can Fully Compromise Windows Domains Running AD CS. Rapid7. Vulnerability Risk Management.
- ^ Francis Dinha. The Dangers Of P2P File-Sharing Sites. Forbes. Innovation.
- ^ Adrian. Detect and Avoid Fake Software Updates! – A Short Guide. InternetSecurity. Tips.