Mafer ransomware (virus) - Free Guide
Mafer virus Removal Guide
What is Mafer ransomware?
Mafer is a malicious program that holds personal files hostage in exchange for a payment
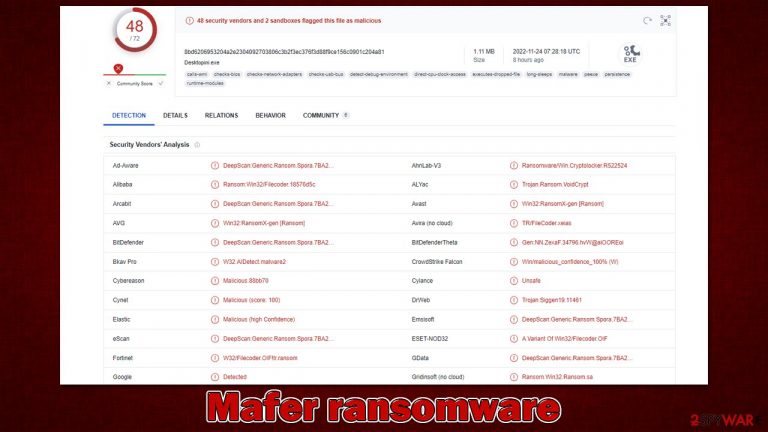
Many users have large collections of personal files on their laptops, including photos, videos, home projects, and confidential documents. However, few people believe they could ever lose access to these files. Unfortunately, this can happen when Mafer ransomware infiltrates a Windows computer and encrypts all photos, documents, databases, and other files there.
While applications or particular videos can be re-downloaded from the internet, personal files are sometimes invaluable, which is one of the main reasons ransomware is so devastating. It is important to note that the files do not get corrupted but are rather encrypted with RSA and AES encryption algorithms. Some other malware strains are known to be buggy or purposely malicious and can destroy files beyond repair.
Suchlike files are marked with a .Mafer extension, along with the user ID and cybercriminals' contact email. Locking users' files gives crooks a pretense to demand money for a decryption key they hold somewhere privately.
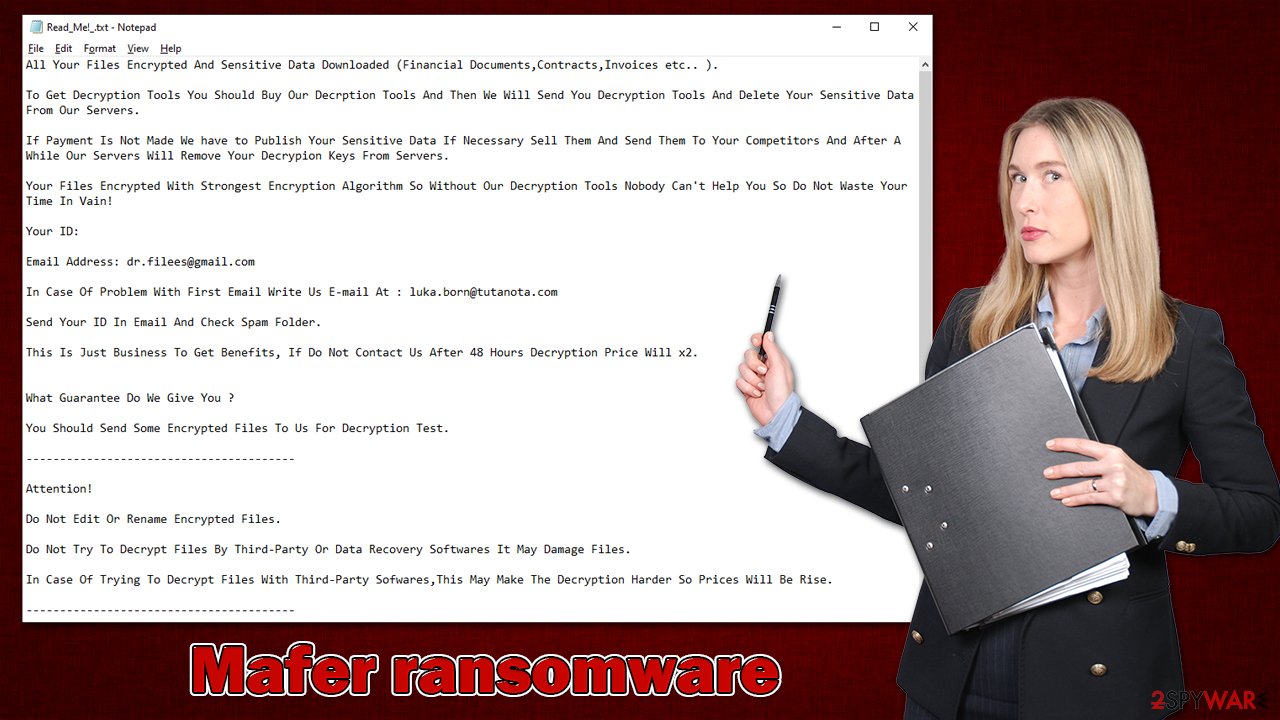
In the ransom note Read_Me!_.txt, attackers explain that users need to email them at dr.filees@gmail.com or luka.born@tutanota.com to negotiate the payment in bitcoin. However, it is extremely risky to pay, as they may never deliver the promised decryptor. Instead, follow the instructions below to follow an alternative route for resolution.
| Name | Mafer virus |
|---|---|
| Type | Ransomware, file-locking malware |
| File extension | [ID=XXXXXX-Mail=dr.filees@gmail.com].Mafer |
| Malware family | VoidCrypt |
| Ransom note | Read_Me!_.txt |
| File Recovery | The most reliable method to retrieve lost data is by using backups. If this is not an option or the files were encrypted as well, chances for recovery are very limited – see all potential solutions below |
| Malware removal | Remove the computer from the network and the internet, then run a complete system check with SpyHunter 5Combo Cleaner security software |
| System fix | If malware is installed on your system, it can potentially damage or corrupt crucial system files, which often results in crashes, errors, and other stability issues. FortectIntego PC repair software can automatically fix any such damage by replacing corrupted files |
Ransom note received by victims
VoidCrypt is a ransomware threat that surfaced in 2020 and continues to be a problem. Malware often uses extensions with several components, including cybercriminals' email addresses and unique IDs for each victim. The ransom note, which is one of the main components of any ransomware nowadays, can be displayed as a pop-up or a regular text file (or both). In this case, cybercriminals deliver a text message which reads:
All Your Files Encrypted And Sensitive Data Downloaded (Financial Documents,Contracts,Invoices etc.. ).
To Get Decryption Tools You Should Buy Our Decrption Tools And Then We Will Send You Decryption Tools And Delete Your Sensitive Data From Our Servers.
If Payment Is Not Made We have to Publish Your Sensitive Data If Necessary Sell Them And Send Them To Your Competitors And After A While Our Servers Will Remove Your Decrypion Keys From Servers.
Your Files Encrypted With Strongest Encryption Algorithm So Without Our Decryption Tools Nobody Can't Help You So Do Not Waste Your Time In Vain!
Your ID:
Email Address: dr.filees@gmail.com
In Case Of Problem With First Email Write Us E-mail At : luka.born@tutanota.com
Send Your ID In Email And Check Spam Folder.
This Is Just Business To Get Benefits, If Do Not Contact Us After 48 Hours Decryption Price Will x2.
What Guarantee Do We Give You ?
You Should Send Some Encrypted Files To Us For Decryption Test.
—————————————-
Attention!
Do Not Edit Or Rename Encrypted Files.
Do Not Try To Decrypt Files By Third-Party Or Data Recovery Softwares It May Damage Files.
In Case Of Trying To Decrypt Files With Third-Party Sofwares,This May Make The Decryption Harder So Prices Will Be Rise.
—————————————-
How To Buy Bitcoin :
Buy Bitcoin Instructions At LocalBitcoins :
https://localbitcoins.com/guides/how-to-buy-bitcoins
Buy Bitcoin Instructions At Coindesk And Get More Info By Searching At Google :
https://www.coindesk.com/learn/how-can-i-buy-bitcoin/
Hackers use a deceitful method: they present themselves as the only option to decrypt victims' files. However, it is not worth trusting them because developers of ransomware never care about users or their files; hence, they might never provide the decryptor after payment.[1] If you trust them, you run the risk of losing not only your money but also your files.
The security industry and law enforcement as a whole are against paying the ransom to crooks but ultimately, it is always a decision that the victim has to make. Below we provide all the necessary steps on how to remove Mafer ransomware from the system effectively and how to try recovering data using alternative methods.
Malware removal
Some ransomware has been known to self-destruct after encrypting data, but this is not always the case. Once it gains access to a system, the ransomware creates a connection with a remote server that criminals can use as storage for encryption keys and other purposes. This link also allows criminals to remotely send commands like stealing user data or transmitting additional payloads, which can be extremely dangerous for one's safety.
So, to begin, you need to disable this connection by unplugging your computer from the network and the internet. You can do this by using either the WiFi icon in the taskbar or disconnecting your Ethernet cable from the computer. If you want to do this for multiple computers at once, follow these steps:
- Type in Control Panel in Windows search and press Enter
- Go to Network and Internet

- Click Network and Sharing Center

- On the left, pick Change adapter settings

- Right-click on your connection (for example, Ethernet), and select Disable

- Confirm with Yes.
Some ransomware deletes itself after completing encryption. However, this is not always the case. For example, it is often spread in tandem with other malware, such as data stealers or keyloggers.[2] which means that all components of the malware must be removed together. While manual elimination is possible, technical challenges are guaranteed, so we recommend sticking to automatic Mafer virus removal with SpyHunter 5Combo Cleaner or Malwarebytes.
Even then, malware may start interfering with the removal process, as it may be programmed to stay on the system as long as possible. To bypass this defense mechanism, you can access Safe Mode:
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing the F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on the Start button and select Settings.
- Scroll down to pick Update & Security.
- On the left side of the window, pick Recovery.
- Now scroll down to find the Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.
- Go to Advanced options.
- Select Startup Settings.

- Click Restart.
- Press 5 or click 5) Enable Safe Mode with Networking.
Repair damaged system components
Once a computer is infected with malware, the way it operates changes. For example, an infection might delete important DLL[3] files or damage essential bootup and other registry parts. As soon as system components are affected by malware, users may experience speed or stability issues, as well as usability problems. Antivirus software cannot fix these issues, and users might need to reinstall Windows entirely.
We recommend that you scan your computer for damaged components and malware using PC repair software FortectIntego. This program can also help with a variety of technical problems, clear junk and third-party trackers from your computer, and boost its performance.
Recovering files without paying
Unless you have a key, files that have been encrypted by hackers are unreadable. The key is often stored on a server the hackers run. By using the user ID, they can figure out which key goes to which victim's data. There is no general password since each person has their own individualized key.
Data encryption and virus infection are two very different things that require separate solutions. This means that, by using antivirus software to scan your computer, you can rid it of any malicious files that would otherwise stay active and encrypt any new incoming documents, for example. Meanwhile, .Mafer files would remain locked.
Rather than negotiating with the attackers, we suggest you explore other data retrieval methods. Even though these may not work for everyone or bring back all encrypted files, it is worth a try. Before continuing, always make copies of any encrypted files if working backups are unavailable.
- Download Data Recovery Pro.
- Double-click the installer to launch it.

- Follow on-screen instructions to install the software.
- As soon as you press Finish, you can use the app.
- Select Everything or pick individual folders where you want the files to be recovered from.

- Press Next.
- At the bottom, enable Deep scan and pick which Disks you want to be scanned.

- Press Scan and wait till it is complete.

- You can now pick which folders/files to recover – don't forget you can search by the file name!
- Press Recover to retrieve your files.
Although security researchers cannot always create decryption tools for every ransomware variant, their work may prove helpful in specific cases. In other instances, law enforcement agencies have even seized the servers of cybercriminals and made ransomware keys available to everyone. Below you will find links that could be useful when trying to find these solutions, although keep in mind that this may never happen.
- No More Ransom Project
- Free Ransomware Decryptors by Kaspersky
- Free Ransomware Decryption Tools from Emsisoft
- Avast decryptors

How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Lawrence Abrams. UltraCrypter not providing Decryption Keys after payment. Launches Help Desk. Bleeping Computer. Cybersecurity and Technology News.
- ^ Josh Fruhlinger. Keyloggers explained: How attackers record computer inputs. CSO Online. Latest information and best practices on business continuity and data protection.
- ^ What is a DLL. Microsoft. Official website.
