Mahitra1 ransomware (Quick Decryption Solution) - Virus Removal Instructions
Mahitra1 virus Removal Guide
What is Mahitra1 ransomware?
Mahitra1 ransomware – a new cryptovirus from an unknown malware family
Mahitra1 ransomware is a data locking malware that was spotted in the wild at the end of January 2019. The virus usually gets to users' machines with the help of spam email attachments, breaks in via the unprotected RDP,[1] or gets extracted via the malicious executable. Soon after the infiltration, the infection spreads within the computer, infecting various system files. Mahitra1 ransomware then scans the machine for data to encrypt – it targets personal photos, music, videos, databases, documents, etc. Once detected, it appends .mahitra1 file extension, preventing victims using the data in any way. The virus then drops a ransom note how_to_open_files.html – a message from hackers. Allegedly, users have to email bad actors via mahitra1@outlook.com or mahitra1@cock.li and arrange the payment in cryptocurrency for the decryptor. Currently, it is unknown which virus family Mahitra1 ransomware belongs to.
| Name | Mahitra1 |
| Type | Ransomware |
| File extension | .mahitra1 |
| Ransom note | how_to_open_files.html |
| Contact | mahitra1@outlook.com or mahitra1@cock.li |
| Family | Unknown |
| Decryptable? | No |
| Elimination | Download anti-malware software and perform full system scan |
| Optimization | Use FortectIntegoto restore system's functions |
Our research team received several reports over the past week that claimed that their files are locked with .mahitra1 file virus. However, it is not much known about this string of malware yet – which family it belongs to or which security applications can detect it. Therefore, a scan with multiple anti-virus engines might be necessary to remove Mahitra1 ransomware.
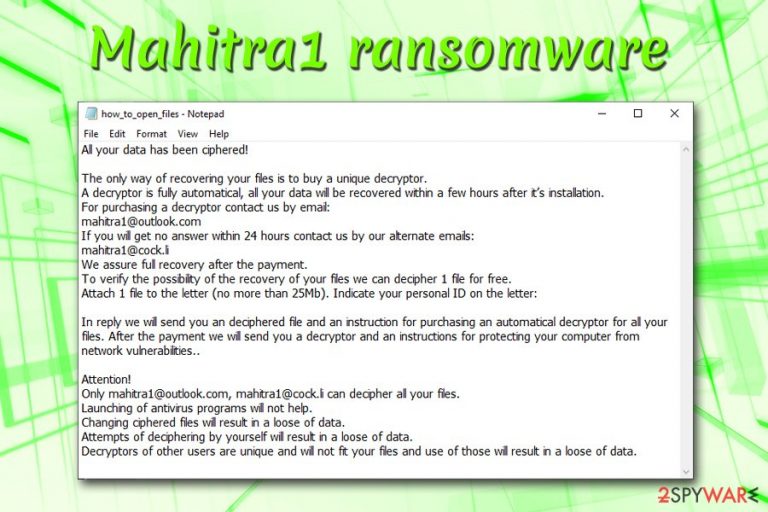
Nevertheless, file locking viruses all operate on the same principle: locking files in order to blackmail victims for money in Bitcoin or another cryptocurrency. To upload the ransom note and obtain the ID, Mahitra1 contacts a remote server which is in the read of hackers only. The message states as follows:
All your data has been ciphered!
The only way of recovering your files is to buy a unique decryptor.
A decryptor is fully automatical, all your data will be recovered within a few hours after it’s installation.
For purchasing a decryptor contact us by email:
mahitra1@outlook.com
If you will get no answer within 24 hours contact us by our alternate emails:
mahitra1@cock.li
We assure full recovery after the payment.
To verify the possibility of the recovery of your files we can decipher 1 file for free.
Attach 1 file to the letter (no more than 25Mb). Indicate your personal ID on the letter:In reply we will send you an deciphered file and an instruction for purchasing an automatical decryptor for all your files. After the payment we will send you a decryptor and an instructions for protecting your computer from network vulnerabilities..
Attention!
Only mahitra1@outlook.com, mahitra1@cock.li can decipher all your files.
Launching of antivirus programs will not help.
Changing ciphered files will result in a loose of data.
Attempts of deciphering by yourself will result in a loose of data.
Decryptors of other users are unique and will not fit your files and use of those will result in a loose of data.
It is not unusual for bad actors to offer test decryption, as it might make users believe hackers. However, multiple examples from the past confirm that cybercriminals do not always send back the decryption key. In some cases, they might even send executable that will infect the machine even more. Finally, paying Mahitra1 virus authors will only prompt them to create new malware and spread them further.
Therefore, do not contact cybercrooks, and do not pay the ransom. In addition to data loss, you might end up losing a hefty sum of money as well. Therefore, better take care of Mahitra1 ransomware removal first and then try alternative file recovery methods (we provide details below).
Once you get rid of Mahitra1 ransomware, make sure you scan your system with FortectIntego – it will restore its functions, such as scheduled tasks, Windows Registry, and other alternations to the system.
Beware of malicious spam emails and suspicious websites – ransomware infection is just around the corner
Ransomware authors usually are sophisticated individuals, and they are continually looking for new methods to spread their malware around the world. Unfortunately, malware is a very lucrative business for criminals currently, and that's why new variants, as well as new families, of ransomware, show up every day.[2]
Those who do get infected with data locking malware are unaware that they themselves initiated the infection – in one way or another. Thus, the main factor is the victim himself or herself – more caution while using the internet would stop various virus infections.
Experts[3] advise users to practice these simple security measures:
- Employ comprehensive security software and keep it up to date;
- Backup your files on a regular basis;
- Beware of spam emails: attached files (.doc, .html, .pdf, .txt, etc.) or hyperlinks can lead to ransomware infection;
- Protect Remote Desktop with adequate security measures – use strong passwords and employ VPN;
- Stay away from torrent and other file-sharing sites;
- Do not download cracks of keygens;
- Update your system on a regular basis – hackers can use software flaws (vulnerabilities) to inject malware without users' interaction.
Remove Mahitra1 ransomware and only then attempt file recovery
Be aware that you have to remove Mahitra1 virus before you proceed with any other actions, especially the file recovery. If you do not do so, all the files will be encrypted repeatedly (if you manage to recover some). Do not attempt to eliminate crypto malware manually – this practice should only be executed by trained IT specialists.
Instead, you should scan your machine with security software for full Mahitra1 ransomware removal. Because the behavior of the virus is not completely known, it is possible that it might interfere with the operation of the anti-malware program. In such a case, enter Safe Mode with Networking.
As soon as you delete Mahitra1 ransomware from your computer, proceed with file recovery. If you had backups – connect your external device or copy all the data from virtual cloud storage. In case you do not have such backups, recovering data might be quite complicated. You should download third-party software that might be able to help you – find download links and descriptions below.
Finally, in case you do not succeed to retrieve files, keep a copy of all the data because security researchers might create a free decryptor for .mahitra1 file virus.
Getting rid of Mahitra1 virus. Follow these steps
Manual removal using Safe Mode
To remove Mahitra1 malware from your machine safely, reboot your PC to reach Safe Mode with Networking:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Mahitra1 using System Restore
System Restore might also help you stop the virus:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Mahitra1. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Mahitra1 from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Mahitra1, you can use several methods to restore them:
Take advantage of Data Recovery Pro
Data Recovery Pro is a professional tool that might be able to decipher your files locked by .mahitra1 extension.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Mahitra1 ransomware;
- Restore them.
Windows Previous Versions feature might be able to get at least some of your files back
This option is available if you had System Restore enabled before the virus attack. Additionally, it allows you to recover files one by one, so recovery of large amounts of data might be impossible.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer can restore your files under certain conditions
Ransomware is programmed to delete Shadow Volume Copies – Windows backup for your files. In case the virus fails to do so, tools like ShadowExplorer will be able to recover all your data.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No decryptor is created yet
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Mahitra1 and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ Jakub Křoustek. Ransomware attacks via RDP choke SMBs. Avast. Official blog.
- ^ Bojana Dobran. 27 Terrifying Statistics on Ransomware & Facts You Need To Read. Phoenixnap. Data Center, Dedicated Servers, Cloud, & Colocation.
- ^ Virusler. Virusler. Security researchers.







