Mailto ransomware (Virus Removal Guide) - updated Feb 2020
Mailto virus Removal Guide
What is Mailto ransomware?
NetWalker ransomware is a multi-variant malware that targets large companies for bigger ransom payments
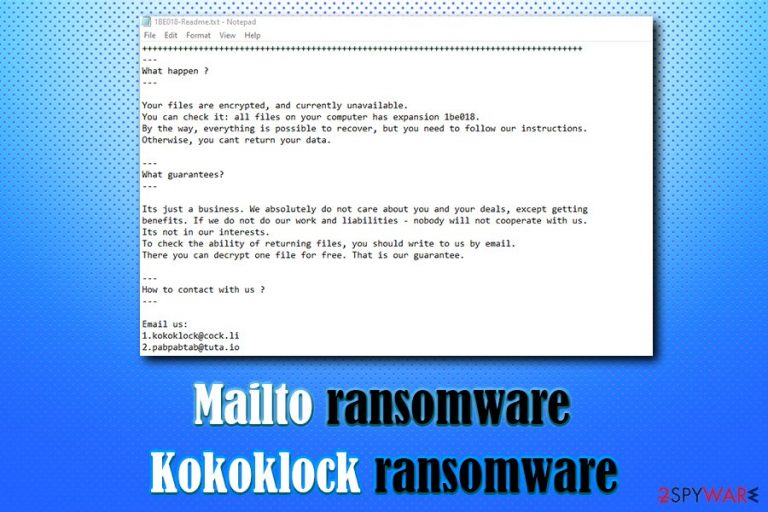
Once inside the system, Mailto ransomware virus looks for videos, pictures, documents, databases, music, and other personal files to perform encryption on. Using a Salsa20 cipher, it makes files unreachable and then marks data with a random appendix that usually consists of six alphanumeric characters (for example, .1be018 .d0e731). A ransom note [file extension]-Readme.txt is also dropped, which explains that users have to email crooks via kokoklock@cock.li or pabpabtab@tuta.io to have a chance to decrypt the compromised files.
Criminals behind Mailto ransomware ask for a ransom to be paid in Bitcoin or another cryptocurrency, although the exact sum is unknown – it may also vary from victim to victim. Security experts who managed to get hold of the decryption tool from the attackers noted that it was named “Netwalker Decryptor” in the header, so the same ransomware can be called a NetWalker virus too.
| Name | Mailto ransomware |
| Also known as | Kokoklock ransomware, Koko ransomware, NetWalker ransomware |
| Symptoms | Files appended with a random extension become unusable; a ransom-demanding note dropped in many different folders |
| Main targets | Newer versions were spotted hitting large companies and businesses |
| Encryption algorithm | Salsa20 |
| File extension | .[random], includes the contact email. Thus appendix gets added at the end of original name of the previously available data. Extension example: .mailto[kokoklock@cock.li].1be018 |
| Contact | kokoklock@cock.li, pabpabtab@tuta.io, hamlampampom@cock.li, galgalgalhalk@tutanota.com, sevenoneone@cock.li, kavariusing@tutanota.com |
| Ransom note | victims'_ID-Readme.txt or random_extension-Readme.txt |
| Termination | You should always employ powerful anti-malware when dealing with serious PC infections like this. So remove NetWalker ransomware from the system with a proper AV tool that can detect and delete traces of this virus |
| Recovery | To remediate damaged system files and ensure the machine is fully recovered from the infection, scan it with FortectIntego |
Mailto ransomware, otherwise known as Kokoklock ransomware or NetWalker, is malware that was first spotted in early September 2019.[2] This file-locking virus does not seem to have any relations to other ransomware families but has the same goal – money extortion. Fortunately, this virus is recognized by nearly over 50 security applications,[3] so its termination can be performed without any troubles.
Since NetWalker ransomware gets around the globe using various techniques, networks can get encrypted due to infected email attachment sent to the employe or after the visit on malicious websites laced with malicious codes. It is not known how specifically Mailto gets on targeted systems.
Regardless of how you might have infected your computer with the virus, your main goal should be Mailto ransomware removal. To achieve that, you should employ reputable security software. If unsuccessful, you should try entering Safe Mode with Networking and performing a scan from there – check out the instructions below on how to each it. Additionally, we recommend using FortectIntego to recover from virus damage quickly.
Note that we should first remove Mailto ransomware from your computer before proceeding to file recovery, as all the backups or retrieved files will be repeatedly locked. Currently, there is not an easy way to decrypt the data if no backup is available. Luckily, security experts work on decryption tools that become available to the public, although it is not known how much time it might take to create for this particular Kokoklock ransomware strain.
Another option that might help is third-party recovery software, although chances of recovering all of the NetWalker ransomware encrypted data using it are relatively low. We provide the guide below – please check the file recovery section below. 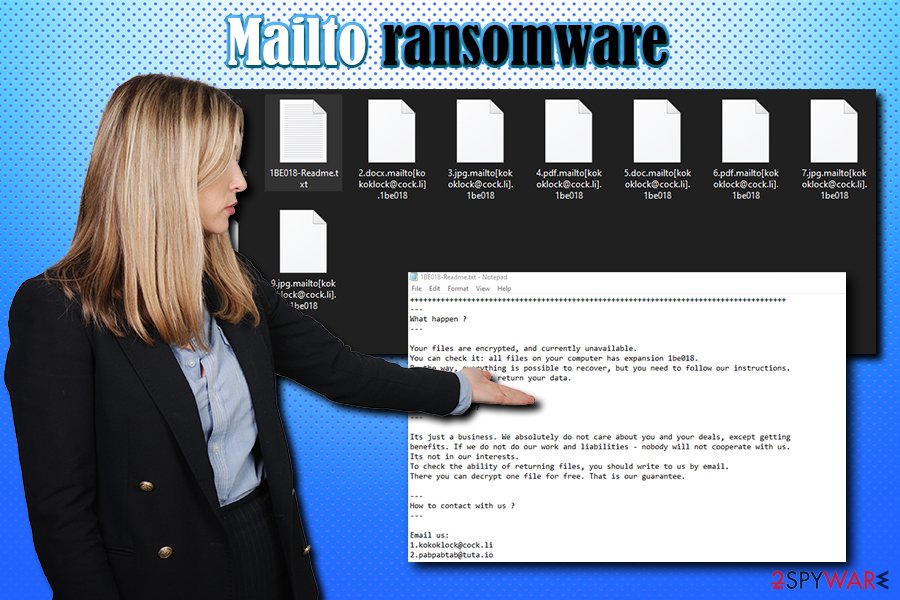
Mailto or NetWalker?
First instances when Mailto ransomware affected machines and researchers got a hold of samples, the investigation showed that the decryption tool offered by the criminals is named NetWalker Decrypter. In most cases, malware experts name the threat by something that developers state in the text file or base the name on the file appendix.
Since the decryption tool was discovered by MalwareHunterTeam the name of the virus family got questioned. This is how developers referred to their product, so the threat is known as NetWalker ransomware now. However, that is not changing any functionalities or removal processes. Victims still call this threat Mailto or generally indicate the file appendix, not the name of the ransomware that researchers use.
These newer releases of NetWalker/Mailto ransomware are now targetting bigger businesses and companies, institutions because blackmailing is more successful this way. Criminals demand bigger amounts from people whose networks get encrypted and can be surer that decryption tools get purchased when data is more valuable.
The example of the more recent NetWalker ransom note:
Hi!
Your files are encrypted.
All encrypted files for this computer has extension:—
If for some reason you read this text before the encryption ended,
this can be understood by the fact that the computer slows down,
and your heart rate has increased due to the ability to turn it off,
then we recommend that you move away from the computer and accept that you have been compromised,
rebooting/shutdown will cause you to lose files without the possibility of recovery and even god will not be able to help you,
it could be files on the network belonging to other users, sure you want to take that responsibility?—
Our encryption algorithms are very strong and your files are very well protected, you can't hope to recover them without our help.
The only way to get your files back is to cooperate with us and get the decrypter program.
Do not try to recover your files without a decrypt program, you may damage them and then they will be impossible to recover.We advise you to contact us as soon as possible, otherwise there is a possibility that your files will never be returned.
For us this is just business and to prove to you our seriousness, we will decrypt you some files for free,
but we will not wait for your letter for a long time, mail can be abused, we are moving on, hurry up with the decision.Сontact us:
1.sevenoneone@cock.li
2.kavariusing@tutanota.comDon't forget to include your code in the email:
Despite all those claims and possible offers in the text file, you should think twice before you pay cybercriminals for the decryptor – they might simply scam you and never send you the required tool. Even the large companies often restrain from such options due to the high risks of getting data permanently damaged and focuses on NetWalker ransomware removal instead. 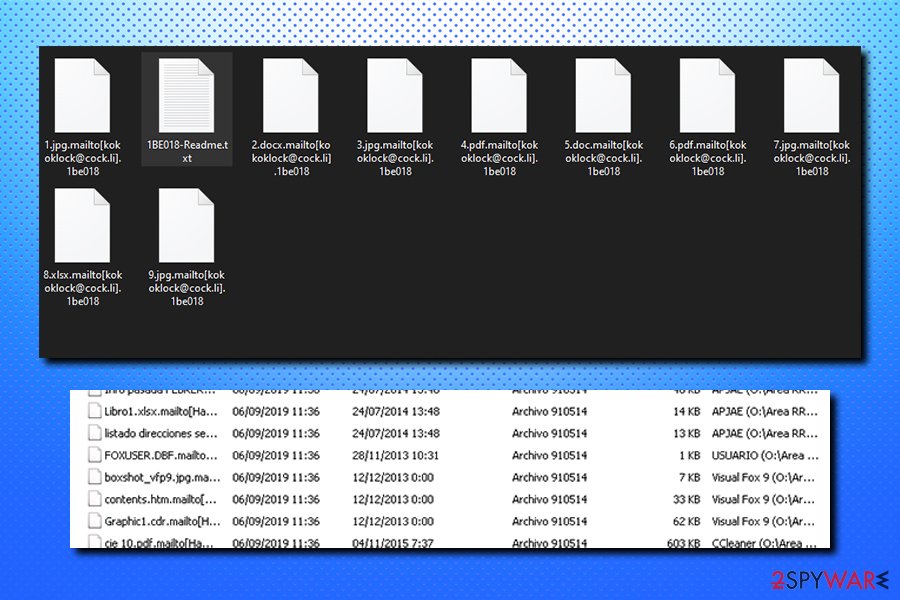
Due to its popularity, ransomware viruses became a real threat to regular users and corporations worldwide. Therefore, you should take precautionary measures in order to make sure either swift recovery or prevention of the infection. Here are some tips from industry experts that want to avoid infections like NetWalker:
- Employ comprehensive anti-malware software that would be able to stop the incoming threats;
- Always update your operating system along with all the installed applications (set the update option to automatic);
- Avoid visiting high-risk sites, such as porn, torrent, gambling, etc.;
- Never open an attachment from a spam email that asks you to enable macros;
- Do not download pirated software or cracks;
- Use ad-blocker;
- Use strong passwords for all your accounts;
- Backup your files on a regular basis.
Ways ransomware infection spreads
Unfortunately, ransomware trend among cybercriminals is only increasing, and, although the number of new ransomware strings released is in decline, the new variants of already existing file locking viruses keep emerging every day. The reason for that being is the fact that ransomware is now a lucrative business the attackers benefit from greatly, even if just a small fraction of users actually agree to pay the ransom.
It is yet unknown how particular ransomware is distributed by the threat actors because there are many different samples and campaigns that may get used. However, hackers usually use one or a few of the following methods:
- Exploits;[4]
- Spam emails;
- Cracks;
- Pirated software installers;
- Fake updates;
- Unprotected Remote Desktop connections;
- Malicious ads, etc.
The best tip should be to pay close attention to all the online content and activities that start on your machine. Take into consideration that criminals can inject malware into email attachments and websites that you visit, so malicious payload drop might not be easily noticed.
Remove NetWalker/Mailto ransomware and do not pay the attackers
To remove Mailto ransomware, you will have to employ anti-malware software that can detect and delete all the malicious files and components of the virus. In some cases, however, the malware might interfere with the software when trying to delete the infection. In that case, access Safe Mode with Networking, as we explained below, and then scan your system thoroughly with anti-malware software.
Only once you complete Mailto ransomware removal, you can connect your backup device or copy the data from the online storage. If you had no backups ready, please check for alternative methods below – they might help you get at least some portion of your data back.
Remember to choose reliable tools for NetWalker virus termination, so you can avoid additional damage and cyber threats that may end up on the system when you skip through crucial steps or ignore red flags. Security and system applications should be used to clean the machine and fix the damage this virus has caused: FortectIntego, SpyHunter 5Combo Cleaner, or Malwarebytes.
Getting rid of Mailto virus. Follow these steps
Manual removal using Safe Mode
To enter Safe Mode with Networking, please follow the following instructions:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Mailto using System Restore
You can also use System Restore to terminate the malicious payload of Mailto ransomware:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Mailto. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Mailto from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Mailto, you can use several methods to restore them:
Use Data Recovery Pro to have a chance of file restoration
Data Recovery software does not work the same way decryptors work, as it retrieves the copy of the locked file from the depths of the hard drive. If that storage space was already overwritten, the data kept there will no longer be possible. Nevertheless, some files might be saved by using Data Recovery Pro.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Mailto ransomware;
- Restore them.
Make use of Windows Previous versions feature
This option is only available if you had System Restore enabled before the infection of the computer. Additionally, only one file can be recovered at the time, so the process might be very time-consuming.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer might be employed to recover data locked by Mailto virus
ShadowExplorer can be useful if the malware fails to delete Shadow Volume Copies.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No decryption tool is currently available
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Mailto and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.
- ^ Ry Crozier. Toll Group hit by "new variant" of Mailto ransomware. ITnews. Cybersecurity and technology news from around the globe.
- ^ GrujaRS. NEW Unknown #Ransomware. Twitter. Social network.
- ^ 8c6d6a3ed7.exe detection rate. Virus Total. File and URL analyzer.
- ^ Josep Albors. Exploits: What are they and how do they work?. WeLiveSecurity. Security blog.







