Maktub virus (Improved Guide) - Oct 2016 update
Maktub virus Removal Guide
What is Maktub virus?
The precisely designed Maktub ransomware project: protect your PC before it is too late
Nowadays, you have to be very careful while browsing the web, since it is full of all sorts of malicious programs, including Maktub virus, about which we want to warn you in the current article. This virus is a ransomware-type program which infiltrates the system without the user’s knowledge, encrypts the containing files and asks for a ransom in return. This may already sound terrifying but there is a lot more to this program. Once Maktub enters the computer through an infected email attachment, it scans the system for variety of file extensions. Pictures, video/audio files, archives and documents are among the most usual targets of this virus. After locating the files, virus encrypts them using a complex algorithm, reportedly used even in military. It is typical for the ransomware programs like Maktub to use such complex coding because its developers want to make sure the files cannot be retrieved any other way than paying the ransom for the encryption key. The encrypted files will be recognizable from an unusual file extensions, for example, .NORV or some other similar extension. As long as the files are encrypted, the virus victim has not access to them and the files are, virtually, lost.
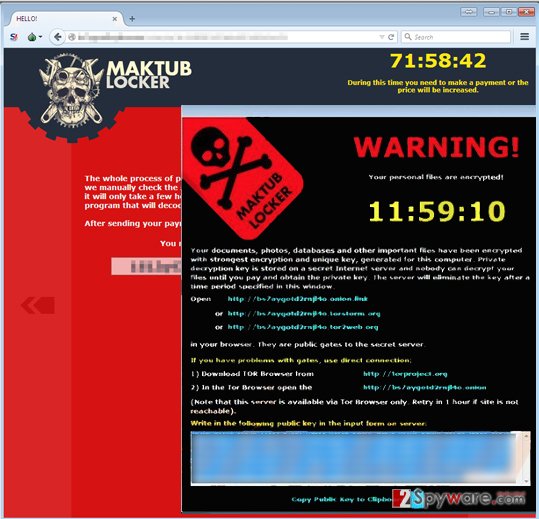
Maktub virus works similarly to other ransomware programs like Locky virus, Rokku virus and other. After encrypting the files a window displaying a ransom note is opened in which the victim is asked to pay 0.5 – 1.5 Bitcoin ($204.55 – $613.65) within 12 hours via the anonymous Tor network. The victim is put on the time pressure by threatening to double the sum if the ransom is not paid until the deadline. Maktub also allows the victim to encrypt some of the files as a form of insurance. However, it is not advisable to purchase anything from the virus creators. Do not forget that they are profit-focused criminals and returning your files back to you is the least of their concern. So the best decision, if infected with this virus is to delete it from your system. You can remove Maktub from your computer using some reputable antivirus tools such as FortectIntego.
How does Maktub infect the target system?
Even though this virus is a dangerous and deceptive program, it can be avoided. You have to be aware that it spreads through deceptive emails, fake software updates, Trojans and P2P networks, so you can be prepared for the counter-attack. For this, you will need to equip your computer with trustworthy antivirus tool. Also, avoid visiting unreliable websites and, more importantly, clicking on suspicious ads, software update and download notifications, which may appear on your screen. In addition, keep away from the “Spam” section in your email since it usually contains potentially malicious content-filled emails, filtered by your mail provider. Finally, keep a backup of your system. Ideally, you should store it on some external drive, which is not connected to your PC in any way. Taking such precautions should help you keep the viruses at bay and your files safe. However, if you are already become a victim of this fraudulent program, you should consider Maktub removal from your computer ASAP!
UPDATED October 19, 2016. Maktub ransomware uses another trick to convince users to open malicious emails – they pretend to be people that act on behalf of some reputable company and that their task is to make the victim pay the debt. The malicious email message provides a link to a “printable” version of the invoice, and also states that the original invoice will be sent out to user’s home address, which is also included in the email message. The fact that criminals know the user’s home addresses is pretty scary and proves that they can get access to some database that contains victim’s email and home addresses.
New Fake Maktub virus version has been detected
We have discovered that a fake Maktub virus version that actively attempts to find its way to users’ computers and encrypt files stored there. This version seems to be targeting Portuguese computer users since the ransom note is written in this language. What is more, this version adds .maktub file extensions and asks the victim to get in touch via email – it asks to write to contatomaktub@email.tg email. The full ransom note looks like this:
Olá, seus arquivos foram criptografados.
A única forma de tê los de volta, é atraves de um software juntamente com sua chave privada.
Caso haja interesse em recuperar seus arquivos, entreem contato pelo seguinte email:
contatomaktub@email.tg
No campo do email, me envie sua chave pública que está logo a baixo.
Te responderei o mais rápido possível.
Att
.maktub
Remove Maktub virus from the compromised computer
Removing ransomware from the computer’s system is not extremely difficult though it may require a little bit of your time. However, the worst part is that Maktub removal from the computer does not affect the state of your files. It means they remain encrypted. Nevertheless, if you want to keep using your computer or restoring files from a backup, you have to make sure the virus is completely removed from your computer. The security experts always recommend opting for the automatic removal method, using the antivirus tools. Yet, in some cases, the antivirus may fail to initiate due to the virus activities on your PC. In this case, you can try disconnecting your computer from the network and start your antivirus again. If this method does not help to boot your antivirus, you can always check out instructions, and try to remove Maktub manually. Just remember to scan your system with antivirus after doing that to make sure it is really virus-free!
Getting rid of Maktub virus. Follow these steps
Manual removal using Safe Mode
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Maktub using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Maktub. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Maktub from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.Criminals want your money, but do not let them win. Your files are lost, but you do not know whether frauds have or are willing to provide you with the decryption key and software. Therefore, we highly recommend you not to pay the ransom. Files can be recovered from a backup, and if you do not have one, use one of the following data recovery methods (these techniques might help you to get some files back).
If your files are encrypted by Maktub, you can use several methods to restore them:
Data Recovery Pro to recover your corrupted files
If your files were hastily distorted by the ransomware virus, you can try to use services of Data Recovery Pro. They might help you to recover some files!
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Maktub ransomware;
- Restore them.
Most important records can be restored with Windows Previous Versions feature
If your files have been encoded and you have no data copies, try to restore your files with the help of this guide. For this technique to work, you should have enabled System Restore function a while ago.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Maktub and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Stream videos without limitations, no matter where you are
There are multiple parties that could find out almost anything about you by checking your online activity. While this is highly unlikely, advertisers and tech companies are constantly tracking you online. The first step to privacy should be a secure browser that focuses on tracker reduction to a minimum.
Even if you employ a secure browser, you will not be able to access websites that are restricted due to local government laws or other reasons. In other words, you may not be able to stream Disney+ or US-based Netflix in some countries. To bypass these restrictions, you can employ a powerful Private Internet Access VPN, which provides dedicated servers for torrenting and streaming, not slowing you down in the process.
Data backups are important – recover your lost files
Ransomware is one of the biggest threats to personal data. Once it is executed on a machine, it launches a sophisticated encryption algorithm that locks all your files, although it does not destroy them. The most common misconception is that anti-malware software can return files to their previous states. This is not true, however, and data remains locked after the malicious payload is deleted.
While regular data backups are the only secure method to recover your files after a ransomware attack, tools such as Data Recovery Pro can also be effective and restore at least some of your lost data.







