Meds ransomware (Removal Instructions) - updated Sep 2019
Meds virus Removal Guide
What is Meds ransomware?
Meds ransomware is a crypto-locking malware that is used to blackmail users in paying money for the recovery tool
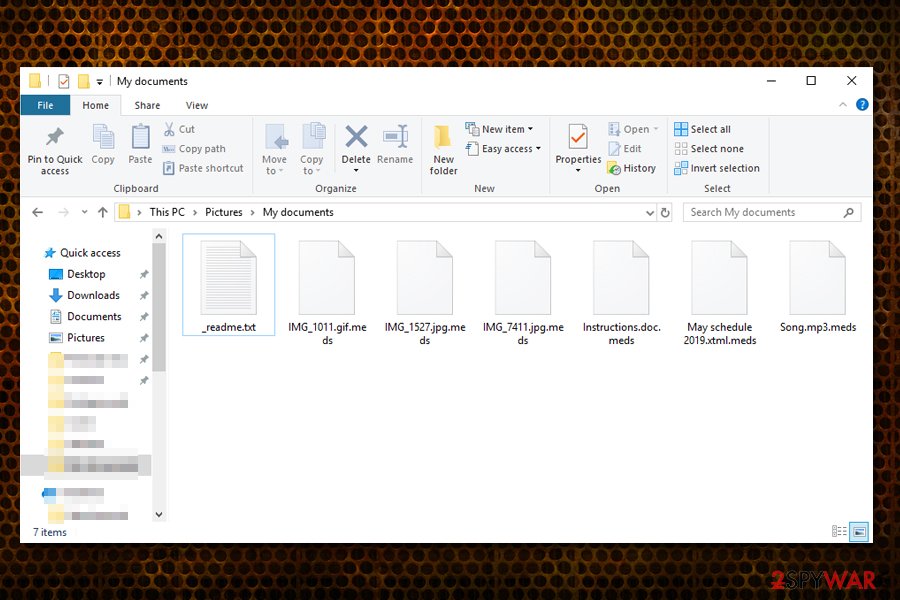
Meds ransomware is a type of malware that focuses on money extortion – it replaces regular personal files with the ones that have .meds extension appended. This guarantees that victims are unable to access any pictures, music, video, document, database, and other personal files – they need a unique key to unlock them. The key is generated during the asymmetric encryption process and is sent off to a remote server controlled by hackers.
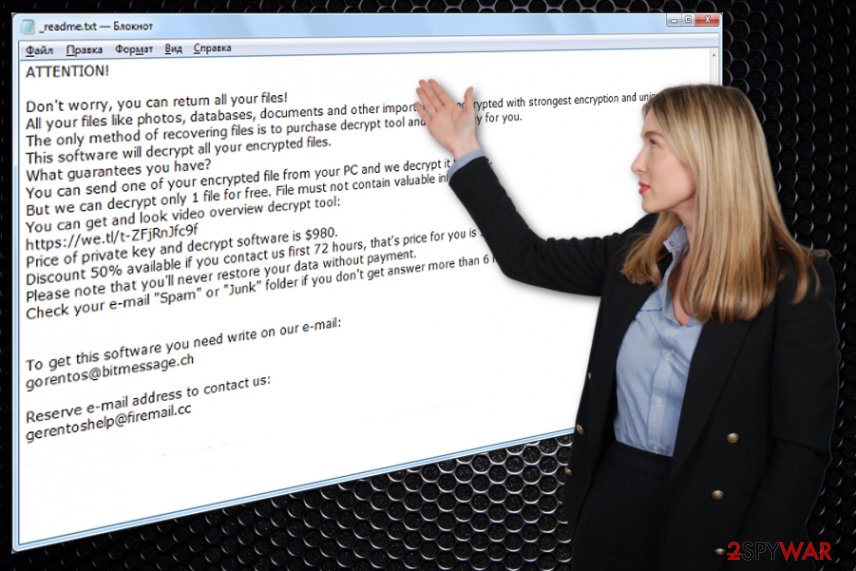
Meds virus also drops a ransom note _readme.txt, which is essentially a message from hackers. Victims are asked to pay the ransom of $980 or $490 to retrieve the key needed to decrypt Meds ransomware files. Unfortunately, STOPDecrypter, a tool that was useful for previous STOP/Djvu variant decryption, is no longer functional, and chances of recovering data without paying criminals is relatively low.
Regardless, users should avoid contacting Meds ransomware authors, as there is no guarantee that they will send the required tool. Experts advise users to avoid using gorentos@bitmessage.ch or gerentoshelp@firemail.cc emails to contact cybercriminals as well and rather focus on Meds ransomware removal process.
| Name | Meds |
| Malware type | Cryptovirus, ransomware |
| Malware family | STOP/Djvu – this is one of the most prominent ransomware families. Over 150 variants of this malware were released to date |
| Appended file marker | Pictures, databases, videos, documents, PDF, and other personal files are marked with .meds extension |
| Ransom note | _readme.txt ransom note is dropped into all the ransomware-affected file folders |
| Contact | gorentos@bitmessage.ch or gerentoshelp@firemail.cc |
| Ransom size | Victims are offered to pay a deducted ransom of $490 if they contact cybercriminals within 92 hours of the encryption process. After that, the decryption tool price doubles to $980 |
| Performs changes |
|
| Removal | To delete malware and all its modules, you should pick reliable security software that can detect all ransomware components. We also recommend scanning the machine with FortectIntego for best results |
| File recovery | Unfortunately, STOPDecrypter does not work for Meds ransomware. Users can request help from Dr.Web (the security company might be able to recover some file types for €150) or use third-party tools along with Windows Previous Versions feature in the attempt to recover the encrypted data. For full guide on file recovery, please check this article |
While most of the ransomware viruses delete themselves as soon as they perform the encryption process on the host machine, Meds virus might leave some traces or modules that will keep encrypting the incoming files and harvest the all the information entered by the victim. That is why Meds ransomware removal should be performed as soon as the symptoms of the infection become apparent.
Currently, multiple AV engines recognize Meds ransomware under the following names:[1]
- TR/AD.InstaBot.wrdas
- Trojan.PWS.Stealer.26685
- Win32/Trojan.Ransom.111
- Trojan.MalPack.GS
- Trojan-Ransom.Win32.Stop.dk
- Trojan:Win32/CryptInject.BE!MTB
- Win32:Malware-gen, etc.
We suggest using FortectIntego to remove Meds ransomware damage. Additionally, after you terminate the infection, you should also head to C:\Windows\System32\drivers\etc folder on your Windows machine and delete the file called “hosts.” This will allow you to enter security-related sites once again.
Meds ransomware can be injected into the machine via software cracks, although other methods are used by malware authors as well
Illegal software activation tools that can crack the otherwise-paid program (for example, Windows operating system, MS Office suite, video games such as Grand Theft Auto V, FIFA, Far Cry V, etc.) have been popular among users for years, and, even though most of them are aware of dangers that lie on crack and pirated software sites, the download rate of such programs does not diminish.
Without a doubt, malware authors are quick to utilize the popularity of crack tools – they often insert fake cracks to infect users with ransomware or other computer threats.[2] In some cases, cracks work as intended, but also download and install the malicious payload in the background.
Therefore, using crack tools and keygens is extremely unsafe, and users should avoid sites that host them. Nevertheless, if you are willing to risk your online security and computer safety, you should at least scan the executable with anti-virus software or tools like Virus Total. Note that cracks will often be flagged malicious due to its fundamental feature – cracking the software to bypass the license requirement.
Meds ransomware can also be installed via other methods, including spam email attachments (malicious .zip, .js, .rar, .html, .doc files), exploit kits,[3] unprotected RDP, adware bundles, and other methods. To protect yourself, make sure you pay attention to your time online, equip your computer with comprehensive security software, patch system as necessary, and backup all your personal files regularly.
Meds ransomware encryption and operation process
Before Meds ransomware starts the file encryption process, it performs various changes to the operating system. Before that, however, the malware creates an executable under a random name and places it into the %AppData% folder. This file is then launched to perform all the changes to the system.
To launch with every Windows boot, the virus alters registry database and spawns a new service under the name VaultSvc. Meds ransomware then performs other changes, such as hosts file modification, removal of Shadow Volume Copies, etc. Finally, once all the required modules are executed, the malware starts a scan – it looks for files to encrypt. Typically, the data that Meds ransomware looks for is the most commonly used file types – .pdf, .doc, .gif, .jpg, .mpeg, .mp4, etc.
Malware uses asymmetric[4] encryption algorithm to lock all personal files, meaning that the key required to lock data is public, while the one that is needed for decryption is different and is in the possession of hackers. Nevertheless, both of these keys are mathematically connected, hence the same key cannot be used to unlock other victims' files.
After the encryption process, Meds ransomware appends each of the files with .meds – a symptom that is hardly unnoticeable by the victims. Files modified in such a way are no longer accessible, and at that time users are asked to pay for the decryption key that hackers can provide.
Hackers behind Meds ransomware ask for a ransom in Bitcoin – do not trust them
Threat actors who launched Meds ransomware are sophisticated individuals, but, at the same time, they are willing to use their knowledge for malicious deeds, such as infecting thousands of users with malware. However, they also do not care about the well-being of their victims, as they are only interested in money, which is usually asked being paid in Bitcoin – a digital cryptocurrency.
Unlike stealthy malware, Meds ransomware does not hide its presence, since hackers are eager for users to pay the ransom. They ensure that victims would find out what happened to their files immediately by placing a message into a text file, which reads:
ATTENTION!
Don’t worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://we.tl/t-sTWdbjk1AY
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.To get this software you need write on our e-mail:
gorentos@bitmessage.chReserve e-mail address to contact us:
gerentoshelp@firemail.cc
Note how crooks are offering a 50% discount – it is a mere trick in order to create a sense of urgency and make users pay the ransom as soon as possible. However, industry experts[5] and security community discourage from doing so, as Meds virus authors might simply ignore you and never send the required tool that can unlock the encrypted files. Moreover, while we cannot say that the criminals will not send you Meds ransomware decryptor, be aware that the risk of losing your money as well is there, so do it at your own risk.
If you decided not to pay for Meds ransomware decryption tool, we suggest you try other methods if no backups were previously prepared. For example, you can try using third-party recovery software, as it might be able to retrieve data that is not yet overwritten from your hard drive. Additionally, Windows Previous Versions feature might be a way to recover files one-by-one. Finally, Dr.Web offers a partial file decryption service by offering Rescue Pack (not free).
Finally, security researchers are constantly working on Meds ransomware decryption tools. To check for updates on that, visit the following websites:
- https://www.nomoreransom.org/en/index.html
- https://id-ransomware.malwarehunterteam.com/
- https://www.emsisoft.com/ransomware-decryption-tools/
- https://www.avast.com/ransomware-decryption-tools
If you don't remove Meds ransomware, sensitive details might be leaked by cybercriminals
Since Meds virus belongs to Djvu/STOP ransomware family, it might be packed with various features. For example, some variants were seen being distributed along with info-stealing malware. In some cases, researchers found the virus installing additional modules that allow data harvesting directly from Google Chrome, Internet Explorer, Mozilla Firefox, or another browser.
Therefore, Meds ransomware removal is mandatory to protect all the incoming files from encryption, as well as stop cybercriminals from stealing sensitive data from the device. For that, you should employ powerful security software and perform a full system scan. In some cases, you might not be able to use an anti-malware program, as Meds ransomware might interfere with it. In such a case, enter Safe Mode and perform a full scan from there – check below on how to do that.
Only after you remove Meds ransomware, you can start the file recovery process. If you think that your personal data has been compromised, call your bank and ask for advice; change passwords for all your accounts.
Visual Meds ransomware removal guide
Meds ransomware is a virus that belongs to the newer versions of STOP/Djvu. Not only is it no longer decryptable with tools that used to help victims in some cases, but it is also packed with new features and improvements.
To prevent users from visiting websites that could advise them on what to do after Meds ransomware infection, malicious actors decided to modify the Windows “hosts” file – it includes a list of most popular security-focused websites around the web. Thus, this complicates the termination of the virus, as reaching the required instructions becomes more difficult.
Luckily, cybercriminals can not block victims from using YouTube, as the links for each video is generated separately. We prepared the video guide for users who cannot access our website or those who have general troubles with Meds ransomware removal. Please check out the visual instructions in the below-video:
Getting rid of Meds virus. Follow these steps
Manual removal using Safe Mode
If Meds ransomware is tampering with your security software, access Safe Mode with Networking as follows:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Meds using System Restore
System Restore can also be useful for malware termination:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Meds. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Meds from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Meds, you can use several methods to restore them:
Data Recovery Pro method
Recovery software does not use the encrypted files to restore them, but rather searches for untouched copies on the hard drive/solid-state drive. If no information is written on top of the space where the data was previously residing, the recovery process will be successful.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Meds ransomware;
- Restore them.
Windows Previous Versions Feature might be able to help you when trying to recover files encrypted by Meds virus
If you had System Restore enabled, you could use Windows Previous Versions feature in order to retrieve files on-by-one.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer could recover all the lost data under certain cicrumstances
If ransomware did not delete Shadow Volume Copies, you should try using ShadowExplorer – this tool should be able to recover all your files.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Do decryptor is currently available
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Meds and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ c2716fcc735a4f1b9fce29cb1dc20a26969b71f615e2b119e9680f015379d286. Virus Total. File and URL analyzer.
- ^ Brian Krebs. Software Cracks: A Great Way to Infect Your PC. Krebs on Security. Security website.
- ^ Exploit kit. Wikipedia. The free encyclopedia.
- ^ What is Asymmetric Encryption? Understand with Simple Examples. Cheap SSL. SSL/TLS Certificate provider.
- ^ Virusi. Virusi. Cybersecurity advice from Hungary.





















