MerryChristmas ransomware / virus (Removal Guide) - Dec 2017 update
MerryChristmas virus Removal Guide
What is MerryChristmas ransomware virus?
Christmas ransomware becomes active just before the feast
Christmas ransomware (also known as MerryChristmas ransomware, .Merry file extension virus, MRCR1 or Merry X-Mas! ransomware) is a file-encrypting virus that is more a joke than a serious virus. However, if you are not a tech-savvy person, Christmas virus may ruin your holiday mood by encrypting your files and asking $100 in bitcoin to get them back.
Christmas virus[1] encrypts files with an ordinary cipher[2] that blocks the victim from opening his/hers files. However, encrypted files are distorted in a way that no one can restore them without having a special decryption key. To the damaged files, the virus also appends complementary file extensions, such as:
- .PEGS1,
- .RARE1,
- .MRCR1,
- .RMCM1,
- .MERRY.
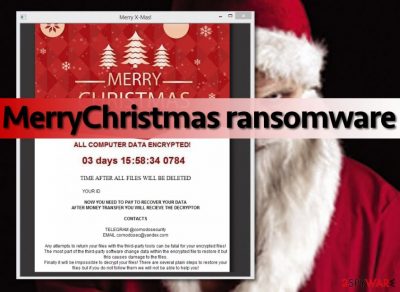
Following data encryption, Merry Christmas ransomware leaves a ransom note called “YOUR_FILES_ARE_DEAD.HTA”. The message opens in the web browser and includes information that users have to purchase a specific decryption key to recover their files:
ALL SERVER DATA ENCRYPTED! [or] ALL COMPUTER DATA ENCRYPTED
03 days 22:55:29 0149
TIME AFTER ALL FILES WILL BE DELETED
YOUR ID [removed]
Merry X-Mas!
NOW YOU NEED TO PAY TO RECOVER YOUR DATA
AFTER MONEY TRANSFER YOU WILL RECIEVE THE DECRYPTOR
CONTACTS
TELEGRAM @comodosecurity
EMAIL comodosec@yandex.com
The latest virus version uses a simplified note:
Your Files are Encrypted
Send 100 $ in Bitcoin to Decrypt Your Files
Merry Christmas
In the first example, you can see that the Christmas ransomware does not provide the exact price of the decryption software. It makes us think that virus’ authors ask for different sums of money from individual victims.
What is more, it is very likely that malware is a software developed by Globe[3] virus’ authors, because it provides the same Telegram messenger contact for victims who want to get in touch with the virus’ authors – @comodosecurity. It’s interesting that criminals use a name of a cyber security company, which is not related to this ransomware virus at all.
Paying the ransom for cybercriminals is always not recommended and risky method to recover encrypted data. But when dealing with this ransomware, transferring bitcoins is unnecessary. Security specialists have already cracked malware’s code and created a decryption tool. The Merry Christmas virus decrypter is safe and free to use.
However, before data recovery, you must eliminate malware from the system. At the end of the article, you will find detailed instructions how to remove Christmas virus from the computer using FortectIntego or other reputable malware removal programs.
Merry Christmas ransomware – the predecessor of Christmas virus
Security experts noticed that malware developers started preparing for the festive season early this year. A malicious Christmas.exe[4] file has been seen spreading on the web and bringing Christmas ransomware virus on the computer.
The recently discovered Christmas ransomware is still under investigation. However, it can use a strong encryption algorithm to take various image, audio, video, backups, databases or configuration files to hostage. Following successful data encryption, malware delivers a creepy-looking ransom note:
Christmas Ransomware
Your Files Have Been Encrypted!
To Get Your Files Back Pay 0.03 Worth of Bitcoin
to the Given Address Below!1FrlwkyAvCwxNLT49LkxQdJayLZMCXnZ67
Merry Christmas, He Knows If Your Bad!
Grammar is not the biggest strength of cybercriminals. However, transferring the ransom is not recommended. No one can assure that the virus is decryptable or crooks are willing to share the decryptor with you. Thus, you should remove Christmas ransomware from the computer using reputable antivirus.
As we have told before, Christmas virus is decryptable. Thus, it’s possible that this festive-themed malware will be soon cracked.

Merry X-mas ransomware can also steal sensitive information
Even though the holiday season is over, security experts report that ransomware is still active. On January 2017, the festive-themed ransomware has been noticed spreading DiamondFox malware.[5]
DiamondFox is mostly used for stealing passwords, credit card information and other sensitive data. Additionally, it might computers into DDoS bots or opening Remote Desktop (RDP) connections. Therefore, quick MerryChristmas removal is a must for avoiding privacy-related issues or money loss.
This version of the virus still spreads via malicious spam emails. However, it delivers a different-looking ransom note. Data recovery instructions and contact email address remained the same.
Numerous spam email campaigns spread malware executable
Despite the festive name, malware continues spreading after winter holidays. However, the virus continues spreading via email in the form of a deceptive file, which is named COMPLAINT.pdf.exe. Please pay attention that .pdf is not the real file extension – it is part of the filename, and .exe is the real file extension. Therefore, as soon as the victim opens this file, the virus gets activated and roots into the target computer system.
Additionally, the virus might arrive in a malicious document that contains scrambled text and asks the victim to enable Macros to view contents. Sadly, the scrambled text simply obfuscates a script that downloads and installs the ransomware as soon as the victim enables Macros function.
Therefore, security experts from No Virus[6] remind users to avoid suspicious emails that come from unknown people or companies, especially if you weren’t expecting to receive a letter from them. Cybercriminals use many different techniques[7] that help them to deceive naive victims, so try to keep up with the latest cybersecurity news if you do not want to become a victim of a ransomware attack.
Removal guide of the MerryChristmas ransomware virus
It’s important to remove Christmas ransomware (alternatively known as MerryChristmas ransomware) from the device in order to recover files safely using a decryption tool created by Emsisoft. Virus elimination requires obtaining reputable malware removal tool, such as FortectIntego or Malwarebytes. However, you might encounter some obstacles.
The virus might prevent from installing, opening or running security software. Thus, you should reboot the PC to Safe Mode with Networking before you start automatic Christmas ransomware removal. You can find the explanation below:
Getting rid of MerryChristmas virus. Follow these steps
Manual removal using Safe Mode
In some cases, ransomware authors make the viruses strong enough to disable antivirus and anti-malware programs. If your scanner is blocked as well, reboot your computer to Safe Mode with Networking. This mode helps deactivate the virus. However, it doesn't get rid of it, so make sure you run a full system scan right after using the following steps:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove MerryChristmas using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of MerryChristmas. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove MerryChristmas from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by MerryChristmas, you can use several methods to restore them:
Recover some files with Data Recovery Pro
If your files have been corrupted, run Data Recovery Pro and see if it can restore them. This tool can help to restore various corrupted, damaged, or encrypted files, so in our opinion, it can be really useful.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by MerryChristmas ransomware;
- Restore them.
Use Windows Previous Versions feature to get back your files
System Restore function allows you to restore lost files with a help of Windows Previous Versions. Although this method allows to restore individual files only, we find it very useful:
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Use MerryChristmas decryption tool
To help users infected with MerryChristmas ransomware, security experts presented the official decryter. You can download this tool from here. To use this tool properly, you will need to use an encrypted and the non-encrypted version of the same file. Then, drop those two files (between 64KB and 100MB in size) onto the decrypter's executable and start decryption process. NOTE. This decryptor can help victims who were attacked by ransomware versions leaving .PEGS1, .RAR1, .MERRY, .MRCR1, or .RMCCM1 extensions.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from MerryChristmas and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Crypto-ransomware. F-Secure. Cyber Security Solutions for your Home and Business.
- ^ Cipher. Wikipedia, the free encyclopedia.
- ^ Julie Splinters. Globe ransomware virus. How to delete? (Removal tutorial). NoVirus. Comprehensive information about various computer infections.
- ^ The analysis of Christmas.exe. VirusTotal. Online file scanner.
- ^ Yule be sorry: Belated Merry Christmas ransomware festively encrypts files, drops DiamondFox malware. SC Magazine. Breaking news on cybersecurity, cybercrime, industry insight and security product reviews.
- ^ Volume Shadow Copy Service. Microsoft Technet. Technical resources and tools for IT Professionals.
- ^ Understanding Ransomware and Strategies to Defeat it. McAfee Labs. The threat research division of Intel Security.





















