Globe3 ransomware / virus (Free Instructions) - Bonus: Decryption Steps
Globe3 virus Removal Guide
What is Globe3 ransomware virus?
Globe3 ransomware family keeps growing
Globe3 virus is the latest evil invention of the hacker team that has already created two more versions of this malware including the original Globe virus and its follow-up Globe2 ransomware. Despite that, it hasn’t been a successful year for the Globe authors. Both these versions have been decrypted by the virus experts, so the victims reclaimed thousands of dollars worth of files without paying a single penny to the malware creators. Undoubtedly, the extortionists anticipated making a comeback with the new Globe 3 ransomware. Have they made it? Not quite. There is already a Globe3 decrypter available on Emsisoft, but there are a lot of factors that give ransomware creators some hope. First of all, the virus is relatively new, and its distribution strategies are still rather obscure, so the users may unknowingly allow it on their computers. Secondly, the scare tactics [1] that Globe3 employs can seriously frighten the less experienced users and they pay the demanded ransom without even considering other alternatives. If you are ever in a situation where your computer is attacked by ransomware – stay rational. Maybe it will turn out that you simply have to download a free decryption tool [2] and all of your problems will be solved. When planning decryption in this particular case, you should remove Globe3 from the computer first. FortectIntego anti-malware software may come in handy for this purpose.
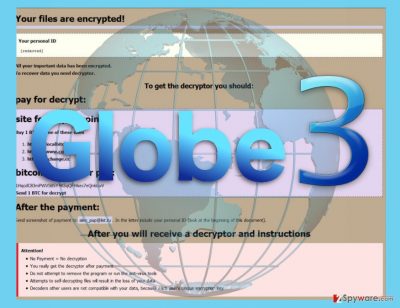
After the analysis of Globe 3 virus, it was found that the data encryption is launched by system32.exe — a malicious process obfuscated as a legitimate Windows system file [3]. Another new feature of this parasite is that it now uses AES-256 encryption instead of Blowfish, RC4 and XOR used in previous Globe versions [4]. Nevertheless, just like its predecessors, Globe3 is based on a ransomware builder [5] which allows easy malware creation using customizable variables. For this particular variant, the hackers have chosen to encrypt files with .decrypt2017 and .hnumkhotep extensions and target hard drive folders, connected storage devices, and network shares. After the encryption the virus also drops a lengthy ransom, not on every infected folder:
Your files are encrypted!
Your personal ID
[IDENTIFIER]
Your documents, photos, databases, save games and other important data has been encrypted.
Data recovery is required interpreter.
To get the interpreter should pay its costs: 3 Bitcoin (3 BTC).
Cash must be translated into Bitcoin-purse: [removed]
If you have no Bitcoin
Create a wallet Bitcoin: https://blockchain.info/ru/wallet/new
Get cryptocurrency Bitcoin:
https://localbitcoins.com/ru/buy_bitcoins (Visa/MasterCard, QIWI Visa Wallet \xE8 \xE4\xF0.)
https://ru.bitcoin.it/wiki/\xCF\xF0\xE8\xEE\xE1\xF0\xE5\xF2\xE5\xED\xE8\xE5_\xE1\xE8\xF2\xEA\xEE\xE9\xED\xEE\xE2(instruction for beginners)
Send 3 BTC bitcoin address [removed]
After the payment, send an e-mail address decrypt2017@india.com. In a letter to indicate your personal identifier.
In a response letter you will receive a program to decrypt.
After start-interpreter program, all your files will be restored.
Attention!
Do not attempt to remove the program or run the anti-virus tools
Attempts to self-decrypting files will result in the loss of your data
Decoders are not compatible with other users of your data because each user’s unique encryption key
Do not follow the extortionist’s rules and don’t pay the simply audacious amount of ransom they demand. You CAN decrypt your files for free and continue using your computer without unnecessary spendings. You will find a link to the free decryption tool just below the manual Globe3 removal instructions.
GLOBE3 ransomware modifications
.Wuciwug file extension virus. A new variant of Globe3 ransomware has emerged to the surface and has been quickly detected by malware analysts. This one is called Wuciwug Globe3 ransomware due to extensions it appends to encrypted data. This version is only slightly improved, but the main difference that distinguishes it from other Globe viruses is that it uses a different file extension and ransom note. Wuciwug Globe3 virus typically adds .wuciwug file extensions to encrypted files and then leaves READ_ME_TO_DECRYPT_YOU_INFORMA.jjj file, which is a ransom note. Criminals who have developed the virus tell the victim to contact them via email and leave a contact email address in the ransom note – KarlTruluck@india.com. Victims of this ransomware should not rush to pay the ransom and try Globe3 decrypter for data restoration. Of course, victims must remove Wuciwug ransomware virus before taking any data recovery measures.
.jeepdayz@india.com file extension virus. Another Globe3 virus variant starts adding an email address as a signature file extension to encrypted files. Let us remind you that such activity resembles Crysis ransomware viruses; the email address added to filenames is the only way to contact cybercriminals. The ransomware leaves a ransom note called How To Recover Encrypted Files.hta, which informs the victim that the computer system wasn’t secured efficiently and this resulted in a successful ransomware infiltration. What is interesting is that .jeepdayz@india.com virus doesn’t ask for a certain ransom but tells the victim that “The price depends on how fast you write to us.” The ransom note states that the decryption key ( the private key that can reverse the encryption procedure and make files normal again) will be available for 72 hours only. If you have been infected with this ransomware, we suggest trying Globe3 decryptor before even considering the option of paying the ransom. Before trying the decryptor, remove ransomware first!
Get to know how this ransomware operates
Globe3 virus may infect computers in multiple ways. It is a powerful Trojan which can pretend to be a legitimate application, system optimization tool or a regular attachment files that you receive in your email. In fact, malicious spam campaigns are the primary distribution technique that Globe3 and other ransomware developers use. The malicious payload may be hidden under random file names and types that imitate the legitimate documents, online purchase confirmation, billing information, etc. Usually, the hackers will think of a convincing story why this attachment must be downloaded on the computer. A way to prevent hijack through email, it is necessary to understand that not all of the correspondence you receive in your inbox is reliable and aims to benefit you. Thus, you should be very careful when opening emails received from unfamiliar senders. More importantly, forget about downloading random attachments without making sure they are safe.
Globe3 removal advice
Globe3 virus may be your worst nightmare if you do not have the proper skills and knowledge to manage it. Luckily, the 2-spyware team is here to help you. First and foremost, we advise you to obtain a reliable antivirus utility or update the one you already have to the latest version. Then, run the full system scan to remove Globe3. However, keep in mind that the virus might try to prevent its extermination by blocking the launch of your anti-malware utility. What you should do in this case is scroll down below and follow the indicated virus decontamination instructions. Although you should remember that this is not a Globe3 removal guide and you will still need to clean up your device with a powerful anti-malware afterward.
Getting rid of Globe3 virus. Follow these steps
Manual removal using Safe Mode
Get rid of Globe3 from your computer as fast as you can! As long as it stays on your computer, it controls it and depending on the virus version, you might get infected with another kind of malware at the same time (in case the ransomware has the ability to install additional malware or comes in a bundle with another virus). You must restart your computer using these instructions for a successful Globe3 ransomware removal.
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Globe3 using System Restore
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Globe3. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Globe3 from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Globe3, you can use several methods to restore them:
Free Globe3 decrypter
You can obtain the Free Globe3 decrypter by clicking the link or by visiting the official Emsisoft website. On the site you will also find steb-by-step instructions on how to use this tool.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Globe3 and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Browser-based ransomware uses scare tactics to extort money. Virus Bulletin. News about computer viruses.
- ^ Anand Khanse. List of free Ransomware Decryptor Tools to unlock files. The Windows Club. Windows 10/8/7 Tips, Tricks, Help, Support, Tutorials, News.
- ^ Joshua Cannell. Obfuscation: Malware’s best friend. Malwarebytes Labs. Security Blog.
- ^ Symmetric Encryption Algorithms. Omnisecu. Feed your Brain.
- ^ New Cybercrime Tool: Ransomware Kits. Mcafee. Security blog.





















