Mool ransomware (Bonus: Decryption Steps) - Free Guide
Mool virus Removal Guide
What is Mool ransomware?
Mool ransomware is the cryptovirus that locks files and claims to offer the potential recovery tool to trick you into paying the ransom

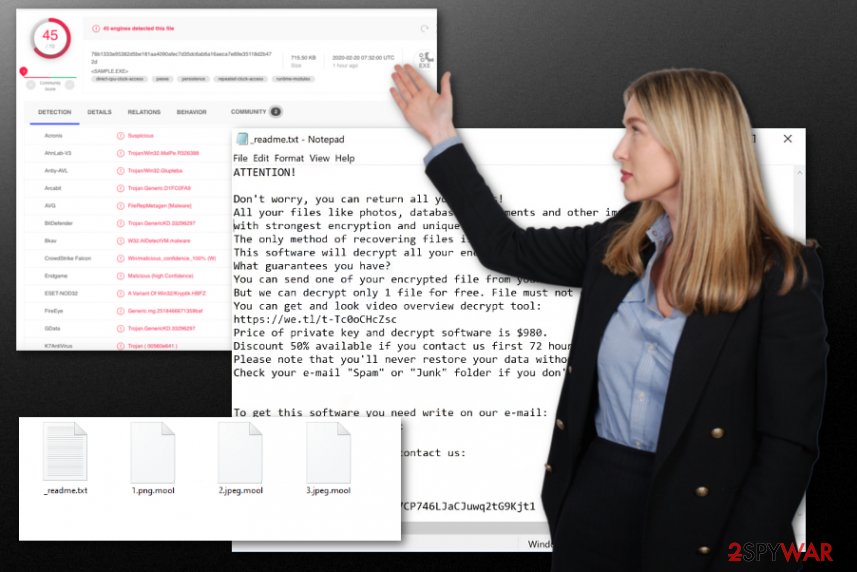
Then the .MOOL virus marks all the affected files using .mool file extension, hence the name of the threat. The appendix comes after the original name and extension, marking the type of particular data. Then the message with ransom demand is delivered on your machine in the text file _readme.txt with additional instructions and contact information.
Ransomware is the type of virus that affects commonly used types of files directly, but various system files, folders, and functions get affected in the background. Such behavior of the Mool ransomware virus interferes with various data recovery processes that can be possibly used for encrypted data restoring and keeps the threat more persistent when detection becomes almost impossible once AV tools and security functions get disabled.
| Name | Mool ransomware |
|---|---|
| Family | STOP ransomware virus |
| File marker | .mool is the extension that appears on every encoded file and indicates encoded data in various folders |
| Ransom note | _readme.txt is the file that developers generate after encryption and provides all the needed details there |
| Ransom amount | The demand starts at $980, but criminals offer the 50% discount for victims who contact them in the first 72 hours. This is the trick used to fake trust between virus developers and victims, so they are more eager to pay up |
| Distribution | Spam emails and malicious websites include malicious files with scripts triggering the drop pf a ransomware payload. The particular virus family is known for delivering such data via pirated software, cracks, cheatcodes and similar content that can be found on torrent sites and similar services |
| Contact email | helpdatarestore@firemail.cc, helpmanager@mail.ch |
| Elimination | When you are thinking about ways to remove Mool ransomware, you should start with anti-malware tools that can detect[1] malware like this and delete it from the machine |
| Repair | Even when you get rid of the virus, you need to check the system for possible virus damage and repair those issues to avoid performance problems later on. System tools like FortectIntego should check and repair affected system files, parts of the registry and other settings, functions for you |
Previous versions in the same family were potentially decryptable with the help of STOPDecrypter, major changes got made int he encoding procedures and other processes that threats like Mool ransomware runs on the infected machine. Since encryption now is more powerful and online keys get employed previously used methods cannot be helpful for new victims.
Some of the victims that know that their files got encoded using offline keys can use the Emsisoft decryptor for Djvu, but criminals rarely use offline IDs now. August 2019 was the last month when researchers were able to restore files easily. Unfortunately, Mool ransomware is one of the newer versions discovered[2] alongside other variants in February 2020.
Offline keys provided the opportunity to restore files for many victims once the particular ID is obtained for one of the versions. Victim keys got generated once for all the people affected by the same sample. However, developers got advanced methods and started to use proper RSA encryption[3] methods, so online keys got employed, meaning that each victims' ID is unique and randomly generated by connecting to the C2 server controlled by criminals.
So make sure to react as soon as you receive the following ransom message in the file _readme.txt that Mool ransomware developers plant in every folder with affected data:
ATTENTION!
Don’t worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://we.tl/t-7YSRbcuaMa
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.
Mool ransomware removal is possible with proper anti-malware tools that can detect potentially malicious programs, files that are related to harmful processes and terminate the threat completely. Make sure to choose the reliable program and trustworthy tool developer for this, so you can be sure that virus elimination is successful.
Users shouldn't pay the demanded ransom under any circumstances. Do not consider contacting these criminals also because Mool ransomware developers can trigger other malware scripts by sending you the injected file instead of the decryption tool. This software that supposedly restores encrypted files may not even exist.
Unfortunately, anti-malware tools are not a program that does everything, so when you get rid of the Mool ransomware, you need to target the particular virus damage that can be caused by the threat in the background and affect all the possible data recovery options. To do so, you should install a reliable PC repair program or a system optimizer like FortectIntego and run it to check the affected or damaged parts of the machine.
Then you can worry about encrypted files and restore damaged data using your data backups or third-party recovery software that can help you. Mool ransomware can always run the secondary encryption process on newly added files, so make sure to clean the machine fully. As for encoded data, check the bonus tips and suggestions below the atticle. 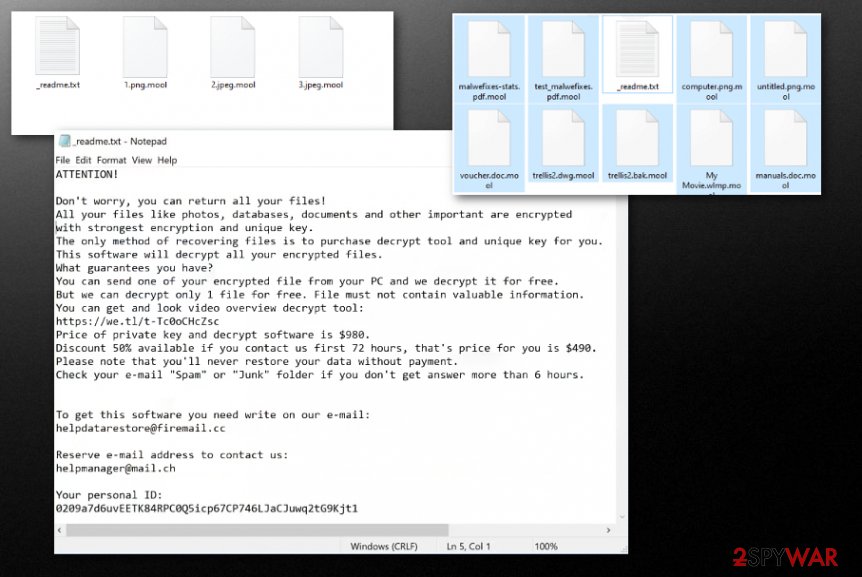
Pirating and other illegal activities can lead to even more harmful malware
The more common methods used for spreading these threats like ransomware and trojans involve misleading content and silent drops of the malicious script that triggers system damaging procedures. These techniques rely on malicious files or directly infected data, websites that trigger silent worm installation.
However, this particular ransomware family is known for spreading their versions around with the help of pirating services and torrent sites. When the person goes for such a source and downloads a software package, cracks, game cheats, and similar material, malicious files can be directly injected in the installation process and drop the ransomware directly on your system.
You can avoid such infections if you stay away from these sources and other illegal activities or delete suspicious emails once received, but the infiltration process cannot be noticed, unfortunately. So once the maliciosu macros-filled document or an infected crack gets loaded ransomware attack begins. Keep AV tools on the machine to check any suspicious email attachment or installation before allowing malware on the PC.
Avoid any interaction with criminals and terminate Mool file-locking virus now
Mool ransomware virus is the threat that encrypts files and demands payments from victims, but you shouldn't even consider that option because contact between you and any cybercriminal can cause more serious issues regarding the security state of your device and even privacy. Since paying cannot ensure that you will get your files back this is the way to lose your data and money at the same time.
You need to remove Mool ransomware without even thinking about paying the ransom, so your device is not permanently damaged by this threat. Get SpyHunter 5Combo Cleaner, or Malwarebytes, and clean the system from any traces of malware, potential threats, and remote tools of the malicious attackers.
Mool ransomware removal process should also be followed by a proper system check that is focused on damage and file repairing. AV tools not supposed to tackle virus damage, so rely on system optimizers or cleaners like FortectIntego. Then you can sure that virus damage is eliminated and you can freely restore encrypted data. If you need additional tips for that – check below.
Getting rid of Mool virus. Follow these steps
Manual removal using Safe Mode
Reboot the computer in Safe Mode with Networking before you scan the machine using the AV tool, so you can remove Mool ransomware fully from your device
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove Mool using System Restore
System Restore can help you with the virus by recovering the device in a previous state
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of Mool. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Mool from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by Mool, you can use several methods to restore them:
Data Recovery Pro is the method for file restoring
When you get affected by the Mool ransomware virus or accidentally delete valuable data, you can rely on Data Recovery Pro and restore those files
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Mool ransomware;
- Restore them.
Windows Previous Versions feature for the data recovery
When you enabled System Restore, you can use Windows Previous Versions for the encoded files and restore them individually
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer – a method for recovering the encoded data
When Shadow Volume Copies are not deleted, you can rely on ShadowExplorer and use it for the encrypted files
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Decryption tool for Mool ransomware is not developed yet
However, you can try this Djvu decrypter that can possibly help with encrypted files and restore them
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Mool and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.
- ^ Virus detection rate. VirusTotal. Online malware scanner.
- ^ Michael Gillespie. .mool ransomware report. Twitter. Social media platform.
- ^ RSA encryption. Wikipedia. The free encyclopedia.





















