Movewifetall.top ads (fake) - Free Instructions
Movewifetall.top ads Removal Guide
What is Movewifetall.top ads?
Movewifetall.top is a scam website designed to trick users into providing their personal data or downloading malicious software
Movewifetall.top might be encountered at any time while browsing the web on Google Chrome, Mozilla Firefox, MS Edge, or any other web browser. The contents of it may vary greatly but usually, various scam pages and phishing[1] attempts are the most common. While the content is dynamic, it is never beneficial or users to the visitors.
Users might end up on this site under different circumstances. The most common reason for this is link clicks on various suspicious, high-risk websites such as torrents or illegal video streaming. Alternatively, a potentially unwanted program or malware could be the reason why you are seeing online scams more often.
Adware is a type of software that relies on showing ads to users for monetization purposes. Quite often, it is installed by users themselves without knowing about the full extent of its operations. Likewise, the offered features of such apps are often useless or vastly overshadowed by their negative traits.
Alternatively, some users might not even know that they have adware installed on their system due to deceptive distribution methods. For example, software bundling is one of the primary methods how users unintentionally end up with optional apps on their systems without even noticing it.
On its own, the redirect to Movewifetall.top is unlikely to cause any harm; it is when one starts to interact with the site contents when things can become pretty bad. There could be numerous tricks that crooks use in order to make people do what they otherwise wouldn't, all for monetary gain while harming users' security or making them spend money on useless online services or goods.
Thus, if you have noticed redirects to this or any other website, make sure you take the necessary precautions and check your device for infections, as we explain in the below section of this article.
| Name | Movewifetall.top |
|---|---|
| Type | Scam, adware, redirect |
| Distribution | Software bundles, redirects, ads |
| Symptoms | Redirects to suspicious websites that accommodate commercial or scam content; fake messages offer to download malicious software; ads plague every visited website; unknown extension or program installed on the system |
| risks | Installation of other potentially unwanted software or malware, personal information disclosure to cybercriminals, financial losses due to scams, etc. |
| removal | You should not interact with the contents shown by a scam website and instead, check your system for adware or malware infections with SpyHunter 5Combo Cleaner security software |
| Additional tips | Make sure you clean your browsers after you delete PUPs from the system. To do that automatically, you can use FortectIntego |
Scam engineering explained
There are countless websites on the internet, and most of them are very secure – the authors make sure that visitors are protected as much as they can be thanks to adequate security measures. Despite this, even highly reputable websites can sometimes be hacked and start showing malicious ads or redirecting users to malicious places.[2]
That being said, there are plenty of websites created for malicious purposes exclusively. For example, various fake torrent sites are known to be spreading Vgkf or other ransomware from the Djvu family – a malware strain that has been infecting hundreds of users daily.
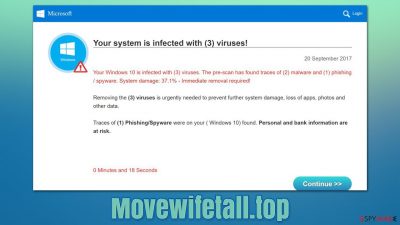
Movewifetall.top can show all types of scams or redirect to other URLs that would display them. Here are a few examples you might encounter:
- 5 Billionth Search scam
- Amazon Gift Card scam
- Your Computer Has Been Blocked scam
- Pornographic virus alert from Microsoft, etc.
Some of these rely on misleading users by showing them fake surveys or claiming that a gift card has been won. Alternatively, the fear factor might be used instead, and people could be told that their computers are infected and that personal information has been stolen or that the computer has been blocked.

All these scams use the names of very popular companies, such as Amazon, Microsoft, Google, or Apple. This is done in order to make it more believable, as people are more likely to trust a message that comes with a familiar branding and logo. Keep in mind that anything visual online can be faked, so it is never an indicator or message's legitimacy.
You should always check out the URL within the bar to ensure that the message is not fake. Also, none of these companies would randomly give free expensive gifts to users. Legitimate Windows or Mac error codes never include contact numbers of customer support either.
Thus, if you encounter messages or pictures that seem suspicious, never proceed with clicking links, downloading software, calling provided numbers, or entering your personal details. Visit the official websites of Microsoft, Apple, or other companies instead.
Remove Movewifetall.top redirects
First of all, it is important to mention that just because you have encountered a scam website, it does not automatically mean that your computer is infected. However, there are a few things that you should take into account:
- Whether you interacted with the promoted material in any way (clicked on links, downloaded and installed software, entered your passwords or other personal information, etc.)
- If you encounter online scams, malicious ads, and similar suspicious content while browsing the web, there is likely to be a potentially unwanted or malicious program involved.
We recommend you start with checking all the places where adware could reside – the installed program section, as well as the extensions installed on the web browser. Automatic checks to ensure the system is not infected with malware and files are not corrupted are also recommended.
1. Remove extensions and clean your browsers
Browser extensions have become the primary choice for potentially unwanted applications for many years now. They are super easy to produce and are often rebranded under different names to avoid security software detection or a bad reputation. Unfortunately, extensions are only recognized by security software when they possess really harmful traits (e.g., generating traffic in the background or allowing man-in-the-middle[3] attacks).
Adware and browser hijackers do not usually employ malicious tactics, although the links one might be exposed to thanks to the presence of these apps are questionable. Thus, we recommend you remove all the extensions you don't remember installing:
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.
![Remove extensions from Chrome Remove extensions from Chrome]()
Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select the unwanted plugin and click Remove.
![Remove extensions from Firefox Remove extensions from Firefox]()
MS Edge (Chromium)
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.
![Remove extensions from Chromium Edge Remove extensions from Chromium Edge]()
Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.
![Remove extensions from Safari Remove extensions from Safari]()
You should then take your time to clean the web browsers properly to ensure that the tracking is no longer is performed via cookies or other technologies. For example, cookies might stay on the browser locally for months or even years if they are not deleted manually. You can clear browser caches manually as we explain in the instructions or using FortectIntego PC maintenance and repair tool.
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.
![Clear cache and web data from Chrome Clear cache and web data from Chrome]()
Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.
![Clear cookies and site data from Firefox Clear cookies and site data from Firefox]()
MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.
![Clear browser data from Chroum Edge Clear browser data from Chroum Edge]()
Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.
![Clear cookies and website data from Safari Clear cookies and website data from Safari]()
2. Uninstall programs from the system
Adware can also be installed as a program on the system level. Media players, file converters, system optimizers, driver updaters, ad-blockers – all types of programs could be used as adware by their creators and distributors. If you have unintentionally installed one of such apps on your device, you can easily remove it by following these steps:
Note: if this step seems to be confusing for you, please skip it. Removing necessary files or programs might cause more harm than good. Instead, choose the automatic removal method, as we explain in the next section below.
Windows
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.
![Uninstall from Windows 1 Uninstall from Windows 1]()
- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.
![Uninstall from Windows 2 Uninstall from Windows 2]()
Mac
On a Mac, removing adware might require a few more steps besides moving the unwanted app into Trash. Adware is known for inserting additional files that might cause the infection to resurface, so we recommend removing them too.
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)
![Uninstall from Mac 1 Uninstall from Mac 1]()
To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.
Once again, if you are confused by any of these steps, please proceed with the next solution.
3. Scan your system with security software
The previous steps might not be necessary if you perform a full system scan with powerful security software, such as SpyHunter 5Combo Cleaner or Malwarebytes. Anti-malware software effectively finds and removes all the apps that behave maliciously or engage in suspicious activities behind users' backs. Most aggressive adware is always detected as long as a potentially unwanted program detection feature is enabled within the settings menu.
4. Other tips
Once you have finished with the steps above, you should take some precautionary measures to ensure that your system remains as secure as possible. It is evident that fully updated security software should always run in the background, and its messages are never ignored – people dismissing these warnings is one of the main reasons why they get infected with all types of malware.
If you have entered your personal information into a malicious website, make sure you change the password on all the accounts it was used. In fact, reusing the same password for multiple accounts is one of the worst decisions one can make when it comes to cybersecurity, so make sure you don't do that in the future.
How to prevent from getting adware
Do not let government spy on you
The government has many issues in regards to tracking users' data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Backup files for the later use, in case of the malware attack
Computer users can suffer from data losses due to cyber infections or their own faulty doings. Ransomware can encrypt and hold files hostage, while unforeseen power cuts might cause a loss of important documents. If you have proper up-to-date backups, you can easily recover after such an incident and get back to work. It is also equally important to update backups on a regular basis so that the newest information remains intact – you can set this process to be performed automatically.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware strikes out of nowhere. Use Data Recovery Pro for the data restoration process.
- ^ Phishing. Wikipedia. The free encyclopedia.
- ^ Art Martori. Understanding & Stopping Malicious Redirects. Security Boulevard. Security Bloggers Network.
- ^ Man in the middle (MITM) attack. Imperva. Application and data security.











