N1n1n1 ransomware / virus (Virus Removal Guide) - updated Aug 2018
n1n1n1 virus Removal Guide
What is n1n1n1 ransomware virus?
N1n1n1 ransomware is a crypto virus that targets users' personal files
N1n1n1 ransomware is a file locking virus that first emerged in late 2016. The virus is propagated in usual methods, such as phishing[1] emails, malicious websites and through the unprotected RDP configuration, and uses the combination of AES an RSA encryption algorithms[2] to lock up data. The initial version of the virus modified file names as follows: [original_file_name][8-9 ransom characters][original_file_extension] and dropped ransom note “how return files.txt” that asked 1.5 BTC for file release. Since then, several variants emerged, but very few changes were added by cybercriminals. The newest version, which showed up in August 2018, adds .jpa prefix, asks victims to contact them via z44@ruggedinbox.com email and pay 4 Bitcoins for the decryptor.
| SUMMARY | |
| Name | N1n1n1 |
| Type | Ransomware |
| Cipher used | AES + RSA |
| Ransom size | 1-4 BTC (can be less or more) |
| Variants (extensions/prefixes) |
|
| Main dangers | Loss of personal data and/or money |
| Detection and elimination | Use FortectIntego or SpyHunter 5Combo Cleaner |
N1n1n1 virus belongs to the group of viruses which base their payment system on the notorious TOR network, keeping their developers’ anonymity safe. After the Locky virus swept by, the popularity of this server has significantly decreased, yet the ransomware developers seem to be getting back to using old and proven techniques all over again.
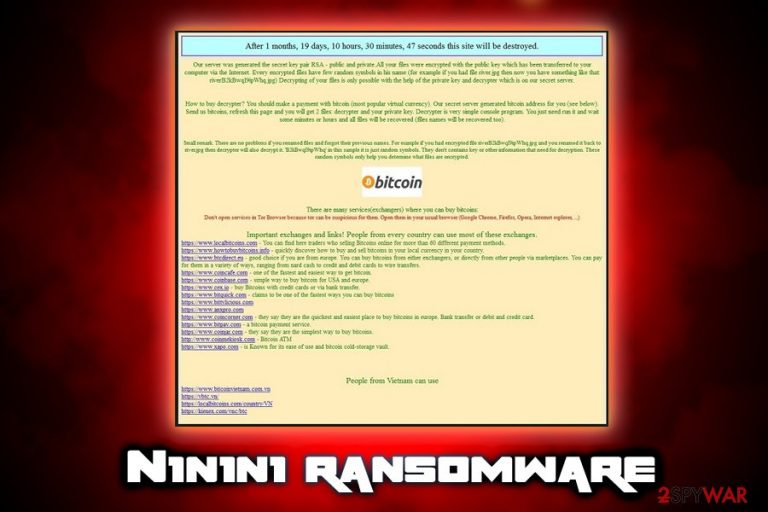
The hackers behind N1n1n1 ransomware might be just a bunch of wannabe teenagers, but that does not stop the virus from being able to inflict serious damage by locking your personal data. Currently, the criminals demand the ransomware victims to pay 4 Bitcoin for the private data decryption key — the only tool capable of deciphering the encrypted data. However, the newest variant uses an old ransom note that claims that Bitcoin is worth only $200, which is absolutely wrong (1BTC is currently worth US$6.9K).
However, we do not recommend behaving according to crooks‘ scenario because it is most likely designed to benefit them alone. Instead, you should focus on N1n1n1 removal. You will be able to eliminate the threat by running the scan with FortectIntego. It is important to eliminate the parasite at once before it entangles your entire operating system.
N1n1n1 creators do not take risks with data decryption either. They use the acknowledged AES and RSA encryption algorithms which remain undecryptable to this day. It is interesting that this type of encryption usually involves changing the file names or adding additional file extensions to the affected documents.
For instance, this particular N1n1n1 ransomware inserts a combination 8-9 randomized symbols between the original file name and the file extension, so the encrypted file may look something like this: randomfilenamejg9bl4mk.jpg. Please note: newer versions of the virus can use .n1n1n1 file extension, .999999 file extension or .jpa prefix to replace the regular ones.
After the files are encrypted, the N1n1n1 virus drops a ransom note named “How return files.txt” (other versions use different note names, such as why files renamed.txt for the jpa. version, although the contents are almost the same) on the desktop and infected folders. This file features a brief introduction of the virus and data recovery. The message starts out with a mocking advice to use a web translator for non-English speakers.
The note continues with the instructions how to download and install TOR browser. In the end, the hackers indicate the email address as their trademark logo – strongonion@sigaint.org. There are speculations that the threat might be linked to Flyper ransomware. They taunt their victims by offering to create an email account and contact them, while in the following lines, they warn that they may not receive or read victims‘ messages.
It would be unwise to follow any hackers‘ instructions and recommendations. There are few chances to recover the files even if you pay the cash, so it is better to remove n1n1n1 ransomware and try to retrieve your files some other way.
Ransomware transmission techniques and data recovery possibilities
N1n1n1 ransomware spreads like any other ransomware threat. It is suspected to disperse through spam email infections and malvertising. Malware developers are very clever and find numerous ways of tricking people into downloading the virus on their computer themselves.
For instance, they may pretend to be representatives of some governmental institution or organization and send you an email with an attached document on their behalf. When this document is opened, the virus is downloaded and activated on the computer automatically.
Additionally, virus is more likely to infiltrate system that are more vulnerable to infections, so updating all software installed is a way to prevent this infiltration technique. Keep in mind that the malware is likely to be distributed via file-sharing domains and applications. If you are not careful enough, clicking on an infected link might trigger the infection.
At the moment of writing, there is no way to decrypt the encrypted data other than by emptying your wallet for the private decryption key. Such way of data recovery is especially unfavorable also because it gives you no guarantees, while the criminals have all the control in their hands. Luckily, we are seeing some progress in data recovery software development. Tools like PhotoRec, R-Studio or Kaspersky virus-fighting utilities can be used to decrypt some data, though a full system recovery still remains an utopian idea.
Remove this destructive virus from your PC
Do not waste time and start automatic n1n1n1 removal immediately, experts[3] advise. Dealing with the threat manually might turn out to be futile and tiresome activity. Therefore, it is more convenient to download and install an anti-spyware application, for example, FortectIntego or Malwarebytes, to do the elimination for you.
In the ransom note, the hackers instruct victims to disable their security programs which might hinder the installation of TOR browser. Likewise, the anti-spyware application might be your trump card to the complete termination of the cyber threat. After it successfully eliminates the n1n1n1 virus, you may start looking for programs which help to recover the encrypted files.
The ransomware itself may not look like a highly complex virus. Nonetheless, it still might cause trouble not allowing you to remove n1n1n1 that easily. In such a case, please find the access recovery guidelines displayed below.
Getting rid of n1n1n1 virus. Follow these steps
Manual removal using Safe Mode
To eliminate the virus without trouble, enter Safe Mode with Networking:
Important! →
Manual removal guide might be too complicated for regular computer users. It requires advanced IT knowledge to be performed correctly (if vital system files are removed or damaged, it might result in full Windows compromise), and it also might take hours to complete. Therefore, we highly advise using the automatic method provided above instead.
Step 1. Access Safe Mode with Networking
Manual malware removal should be best performed in the Safe Mode environment.
Windows 7 / Vista / XP
- Click Start > Shutdown > Restart > OK.
- When your computer becomes active, start pressing F8 button (if that does not work, try F2, F12, Del, etc. – it all depends on your motherboard model) multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list.

Windows 10 / Windows 8
- Right-click on Start button and select Settings.

- Scroll down to pick Update & Security.

- On the left side of the window, pick Recovery.
- Now scroll down to find Advanced Startup section.
- Click Restart now.

- Select Troubleshoot.

- Go to Advanced options.

- Select Startup Settings.

- Press Restart.
- Now press 5 or click 5) Enable Safe Mode with Networking.

Step 2. Shut down suspicious processes
Windows Task Manager is a useful tool that shows all the processes running in the background. If malware is running a process, you need to shut it down:
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Click on More details.

- Scroll down to Background processes section, and look for anything suspicious.
- Right-click and select Open file location.

- Go back to the process, right-click and pick End Task.

- Delete the contents of the malicious folder.
Step 3. Check program Startup
- Press Ctrl + Shift + Esc on your keyboard to open Windows Task Manager.
- Go to Startup tab.
- Right-click on the suspicious program and pick Disable.

Step 4. Delete virus files
Malware-related files can be found in various places within your computer. Here are instructions that could help you find them:
- Type in Disk Cleanup in Windows search and press Enter.

- Select the drive you want to clean (C: is your main drive by default and is likely to be the one that has malicious files in).
- Scroll through the Files to delete list and select the following:
Temporary Internet Files
Downloads
Recycle Bin
Temporary files - Pick Clean up system files.

- You can also look for other malicious files hidden in the following folders (type these entries in Windows Search and press Enter):
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
After you are finished, reboot the PC in normal mode.
Remove n1n1n1 using System Restore
To disable the n1n1n1 virus, use System Restore:
-
Step 1: Reboot your computer to Safe Mode with Command Prompt
Windows 7 / Vista / XP- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
-
Select Command Prompt from the list

Windows 10 / Windows 8- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
-
Once your computer becomes active, select Enable Safe Mode with Command Prompt in Startup Settings window.

-
Step 2: Restore your system files and settings
-
Once the Command Prompt window shows up, enter cd restore and click Enter.

-
Now type rstrui.exe and press Enter again..

-
When a new window shows up, click Next and select your restore point that is prior the infiltration of n1n1n1. After doing that, click Next.


-
Now click Yes to start system restore.

-
Once the Command Prompt window shows up, enter cd restore and click Enter.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove n1n1n1 from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.If your files are encrypted by n1n1n1, you can use several methods to restore them:
Data Recovery Pro option
There is still little information about how the virus works. Likewise, there is a chance that this program might help you recover the files.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by n1n1n1 ransomware;
- Restore them.
Windows Previous Versions Feature might be useful
In some cases, restoring your system to a previous state might help you not only to escape the threat but save the files before they get encrypted.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Shadow Explorer might come in handy
Only few ransomware threats delete Shadow Volume Copies. It is unknown whether this particular virus eliminates the copies of your files. Likewise, this program might be your solution.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from n1n1n1 and other ransomwares, use a reputable anti-spyware, such as FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes
How to prevent from getting ransomware
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
- ^ Phishing. Wikipedia. The Free Encyclopedia.
- ^ What Is Encryption, and How Does It Work?. How-To Geek.
- ^ Lesvirus. Lesvirus. Malware research team.







