Newgensearch browser hijacker (virus) - Free Instructions
Newgensearch browser hijacker Removal Guide
What is Newgensearch browser hijacker?
Newgensearch.com is a browser hijacker that might redirect you to suspicious places online

Newgensearch is a notorious browser hijacker that infiltrates systems primarily through dubious techniques, such as software bundling. Upon successful installation, it manipulates browser settings without users' explicit consent, disrupting regular internet usage. Its main function is to direct traffic to its affiliated sites, often altering default homepages (which is set to Newgensearch.com), search engines, and new tab preferences to achieve this.
The Newgensearch virus poses a significant risk due to its behavior of inserting ads into search results, which not only hinders the online browsing experience but can also be a source of inaccurate or misleading information. This may further expose users to potential security risks and unwanted content.
Often elusive to conventional uninstallation methods, Newgensearch proves challenging to eradicate, making it a significant nuisance for many users. Its capabilities to persistently alter browser settings while potentially compromising user data safety underline the importance of adopting robust security measures and being vigilant when installing new software. In this article, we provide all the information needed to successfully remove the app and its remnants from the system.
| Name | Newgensearch |
| Type | Browser hijacker, potentially unwanted application |
| Distribution | Bundled software, third-party websites, misleading ads |
| Symptoms |
|
| Risks | Installation of other potentially unwanted programs/malware, personal data disclosure to unknown parties, monetary loss |
| Removal | Remove the undesirable browser extension by going to your browser's settings. Using SpyHunter 5Combo Cleaner security software to check the system can also ensure that no malware is running in the background |
| Other tips | We recommend scanning the system with PC repair and maintenance utility FortectIntego to remove leftover files and ensure that trackers are eliminated from the browser |
How browser hijackers spread and how to avoid unintentional installation
The Newgensearch browser hijacker primarily spreads through “bundling,” a strategy used by many cyber threats. Software bundling involves packing the hijacker alongside legitimate applications, often free or trial versions. Unsuspecting users, when downloading or installing the primary software, unknowingly install Newgensearch as well.
Another distribution method includes deceptive ads or pop-ups that mislead users into downloading the hijacker by masquerading as software updates or essential downloads. Occasionally, it may also spread via malicious email attachments or compromised websites.
To avoid unexpected installation of Newgensearch or similar threats, several preventative measures should be taken. Firstly, be cautious while installing new software. Opt for the “custom” or “advanced” installation settings, which allow you to review and deselect any additional pre-checked applications.
Secondly, avoid clicking on suspicious ads, pop-ups, or websites, as these could be potential carriers of unwanted software. Avoid visiting websites of dubious origins, such as torrents, fake streaming platforms, YouTube converter sites, and similar. These often advertise dubious or even malicious software.
Lastly, you should always have a reputable security application installed on your system (for example, SpyHunter 5Combo Cleaner or Malwarebytes) – it can quickly warn you about the suspicious behavior of new applications, so you have a choice to avoid installation.
Ultimately, vigilance and prudent internet practices can significantly reduce the chances of inadvertently installing browser hijackers like Newgensearch.
Why you shouldn't use a browser-hijacking app
Despite not being direct vectors of malware, browser hijackers like Newgensearch can still inflict considerable damage. Their primary method of disruption comes through the promotion of potentially unwanted applications (PUAs) via advertisements placed strategically in users' browsers. This ad bombardment not only interferes with user experience but also increases the risk of inadvertent downloads of other browser hijackers or adware, further compounding the problem.
Equally concerning is Newgensearch's data monitoring capacity. This hijacker, like many of its kind, employs tracking cookies or web beacons to gather substantial amounts of user data, including search queries, visited websites, clicked links, timestamps, device information, ISP data, and more. This extensive data collection raises serious privacy issues as it might be exploited for nefarious purposes or even sold to third parties, creating a further dimension of risk.
A defining characteristic of such hijackers is their persistence. Once installed, they modify browser settings that typically remain altered unless the hijacker is completely disabled or removed. Considering the lack of any benefits and the abundance of potential risks associated with Newgensearch, it is strongly advised to uninstall it promptly. Keeping this hijacker or any similar PUA active in the background only serves to perpetuate risks and compromise your digital environment.
Removal of the unwanted extension
Extensions are an increasingly popular method for spreading browser hijackers like Newgensearch due to their ease of creation and potential for rebranding. This flexibility allows such hijackers to evade poor reputations and sometimes slip past security applications. The silver lining here is that these extensions typically have a smaller operational scope compared to programs installed at the system level, which means their impact can be somewhat less invasive.
However, the developers of such browser hijackers constantly innovate to impede user attempts at uninstalling these unwanted apps. A common tactic employed is the “Managed by your organization” feature, which effectively restricts users from removing the extension in the usual way. Hijackers can often manipulate this feature to maintain their hold on a user's system.
Fortunately, it appears that Newgensearch does not utilize this particular tactic. This means that removing the Newgensearch extension should not pose a significant challenge. However, each user must remain vigilant, as the tactics used by such hijackers are ever-evolving, and newer, more complex hurdles may emerge over time.
Google Chrome
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Mozilla Firefox
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

MS Edge
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Safari
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Internet Explorer
- Open Internet Explorer, click on the Gear icon (IE menu) on the top-right corner of the browser
- Pick Manage Add-ons.
- You will see a Manage Add-ons window. Here, look for suspicious plugins. Click on these entries and select Disable.

Additional steps to take
Given that many browser hijackers and potentially unwanted applications (PUAs), like Newgensearch, employ bundling or other deceptive methods to infiltrate systems, if you've identified such an app on your device without consciously installing it, it's highly likely other PUAs are lurking in the background.
Furthermore, engagement in high-risk online activities, such as visiting torrent sites, illegal video streaming platforms, or downloading software cracks, amplifies your vulnerability to malware infections. It's critical to avoid such practices to prevent more menacing threats like ransomware, which could result in the loss of personal files unless a ransom is paid to cybercriminals.
Therefore, a full system scan with trusted security software is highly recommended. This measure helps ascertain whether your device harbors any dangerous, concealed malware. Reliable anti-malware software serves as your primary defense against such malicious attacks.
Lastly, it's important to cleanse your browsers of cookies and other trackers, as third parties may continue monitoring your activities otherwise. The most straightforward way to eliminate leftover files is through a repair and maintenance utility, like FortectIntego. However, manual removal is also an option – follow these steps:
Google Chrome
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Mozilla Firefox
- Click Menu and pick Options.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content, and press Clear.

MS Edge (Chromium)
- Click on Menu and go to Settings.
- Select Privacy and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Safari
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

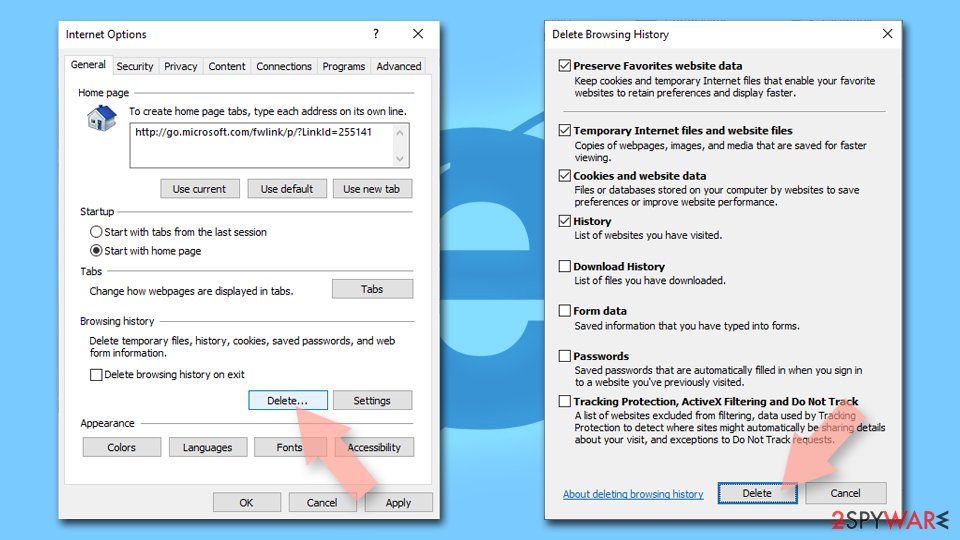
Internet Explorer
- Press on the Gear icon and select Internet Options.
- Under Browsing history, click Delete…
- Select relevant fields and press Delete.
How to prevent from getting browser hijacker
Access your website securely from any location
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. The best solution for creating a tighter network could be a dedicated/fixed IP address.
If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for the server or network manager that needs to monitor connections and activities. VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world.
Recover files after data-affecting malware attacks
While much of the data can be accidentally deleted due to various reasons, malware is one of the main culprits that can cause loss of pictures, documents, videos, and other important files. More serious malware infections lead to significant data loss when your documents, system files, and images get encrypted. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them.
Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system. In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
