News-hikuxe.cc ads (fake) - Free Guide
News-hikuxe.cc ads Removal Guide
What is News-hikuxe.cc ads?
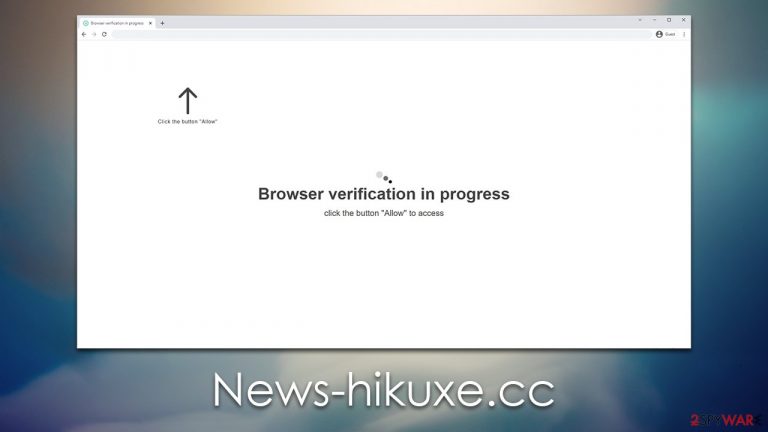
News-hikuxe.cc attempts to use phishing techniques to make expose users to intrusive ads later
Have you been seeing News-hikuxe.cc pop-ups on your screen often? You're likely being scammed by a deceptive advertisement. Such redirects to untrustworthy websites usually appear when users click on harmful links from other web pages or if their systems have been infected with adware and similar malicious software.
Content from News-hikuxe.cc can be of poor quality due to the fact that scammers habitually partner with untrustworthy advertising networks. The push notifications may link you to websites full of malicious code and could also lead to survey scams or get-rich-quick schemes, fooling you into believing your device is riddled with viruses.
You should never interact with these ads, as you may end up downloading malware or disclosing your personal details to cybercriminals. Luckily, it is not that difficult to stop push notifications from showing up on your screen – we explain how below. Also, we will provide some tips on how to effectively remove infections if such are present.
| Name | News-hikuxe.cc |
| Type | Push notifications, ads, scam, pop-ups |
| Distribution | Push notifications show up at some point after the “Allow” button in the notification prompt is clicked |
| Symptoms | Once enabled, notifications from malicious websites would bring misleading or other suspicious content to your screen. These links could lead to malware-laden, scam, phishing, or similar malicious sites |
| Risks | Shown pop-ups incorporate fake notices and push scams. Links can also lead to websites filled with malware |
| Removal | Access browser settings to stop intrusive push notifications. After that, make sure that your system is not infected with adware or malware – scan it with an AV tool |
| Other tips | It is important to clean web browser caches to prevent further data tracking and other issues related to web data corruption – use FortectIntego to do this quicker |
How users enter malicious websites
Since the internet is too huge to monitor strictly, online fraud can never be completely eliminated. This fraudulent activity includes a variety of components, entities, and regulators that are constantly changing every day. As such, scam sites like News-hikuxe.cc can appear suddenly and rapidly affect hundreds of users – no matter how long they stay active for.
Rogue advertising networks, coupled with malicious or poorly managed websites, are the main perpetrators of scams. For example, torrent and notorious pirated software sites have a reputation for being dangerous. There are often fake “Download” links leading to phishing websites and harmful ads that can result in malicious ransomware infection when clicked on. Visiting such websites could lead to irrevocable security damage, so it's important to be vigilant and take proper precautions before clicking on any suspicious link online.
It is also important to mention that adware has the potential to lead users to malicious and phishing websites. Adware is a deceptive form of software that usually runs in the background and causes numerous problems while browsing, such as layering ads over other content or introducing hyperlinks into text. Thusly there are even more access points available for dangerous sites when an infection is present.
How scammers convince users to accept push notifications
When people visit News-hikuxe.cc, they are often asked to confirm their age or if they're a robot – something that has become increasingly common among many internet users. However, with this request coming out of the blue, some may be easily tricked by its unexpectedness and fall prey to it.
If users aren't presented with the proper context, they could be misled into believing that something is about to happen – such as a video being played or that they are winning a gift. To give you an idea of how this might occur in practice, here are some examples:
Click Allow to watch the video
Press “Allow” bot verify, that you are not robot
Click “Allow” to win a prize and get it in our shop!
If you are 18+, click Allow
Browser verification in progress – click the button “Allow” to access
Scammers are taking advantage of the notification prompt, causing confusion among users who had previously encountered age verification via captchas. Additionally, they often entice people with fake promises, such as a video to watch or an unattainable reward for completing their task.

As previously stated, these sites are absolutely worthless, and messages hosted there should be ignored. If you have allowed push notifications from the site, there's minimal cause for concern – as long as you do not click on any of the pop-ups that appear, you should be safe.
Check your system for adware
Before proceeding with News-hikuxe.cc ads removal, we recommend checking your system for infections. If your computer has been infected with adware or another form of malware, you may experience frequent redirects to untrustworthy websites and an increase in advertisements while browsing the web.
To find and remove adware and malware easily, scan your system with SpyHunter 5Combo Cleaner or Malwarebytes security software. To ensure the optimal performance of your system FortectIntego and remove trackers while mending any virus-induced damage and eliminating computer stability concerns in an instant!
Remove unwanted News-hikuxe.cc ads
Push notifications, when enabled through suspicious means, can often be mistaken for a virus infection. It is important to remember that push notifications always require consent before they are allowed to run on the system level, whether this was intentional or not. If you have already checked your system for infections and are sure that it is clean, you can now proceed with removing notifications from your appearing in the future.
To do that, you need to block the website URL – News-hikuxe.cc – in the web browser settings. Find the appropriate web browser instructions below.
Google Chrome
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.

Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.

Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.

MS Edge
- Open Microsoft Edge, and click the Settings and more button (three horizontal dots) at the top-right of the window.
- Select Settings and then go to Advanced.
- Under Website permissions, pick Manage permissions and select the URL in question.
- Toggle the switch to the left to turn notifications off on Microsoft Edge.

MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.

Internet Explorer
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.

- Locate the web address in question under Allowed sites and pick Remove.
How to prevent from getting adware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
