News-kuraxa.cc ads (fake) - Free Guide
News-kuraxa.cc ads Removal Guide
What is News-kuraxa.cc ads?
News-kuraxa.cc is a malicious website that misleads users using deceptive techniques

News-kuraxa.cc is a deceptive website that users may stumble upon when navigating through substandard websites or after engaging with hazardous links. Moreover, undisclosed adware present on one's computer can amplify the risk, as such software is known to carry insecure advertisements.
Typically, users become aware of News-kuraxa.cc when they observe unusual pop-ups surfacing on their desktops. While one might presume these pop-ups arise due to a malware infection on their device, this isn't the actual scenario. Certain conditions have to be fulfilled for these pop-ups to manifest:
- Previously, the user would have clicked the “Allow” button within the site's notification prompt.
- A browser must be operational, irrespective of whether it's actively in use or simply running in the background.
The cunning aspect of this scam lies in its use of sophisticated phishing strategies to convince users to enable its push notifications. In many instances, these tactics involve displaying misleading messages that obscure the true intention behind the notification request. Furthermore, after granting permission by clicking the “Allow” button, ads from News-kuraxa.cc might not immediately pop up, leading many users to inadvertently dismiss or forget their earlier interaction with the site.
| Name | News-kuraxa.cc |
| Type | Push notifications, ads, scam, pop-ups |
| Distribution | After users click the “Allow” button within the prompt upon site entry |
| Symptoms | Once enabled, notifications from malicious websites would bring misleading or other suspicious content to your screen. These links could lead to malware-laden, scam, phishing, or similar malicious sites |
| Risks | Push notification prompts might include links to malicious websites, resulting in financial losses, personal information disclosure, or malware infections |
| Removal | You may turn off notifications in your browser settings. If you notice more ads and redirects to suspicious sites, run SpyHunter 5Combo Cleaner anti-malware on your computer to check for adware infection |
| Other tips | Some remnants of apps stay in browsers and can be used for tracking. Delete these with FortectIntego |
Tricks that scammers use
It's evident that no rational individual would intentionally disrupt their online browsing with intrusive advertisements that emerge unexpectedly. Nevertheless, malefactors have devised a systematic approach to ensnare unsuspecting users into subscribing to these irksome push notifications. The process often commences with a dubious redirect stemming from another site. This can be triggered when a user engages with a compromised link or encounters a malevolent script. Such unforeseen redirects instill an element of surprise, which pairs effectively with phishing techniques since individuals are likelier to err when caught unawares.
Upon landing on the News-kuraxa.cc website, users are greeted with a seemingly innocuous message that might appear familiar. For instance, they might encounter prompts that mimic standard online verifications, such as:
- Click Allow to confirm that you are not a robot
- Click Allow to start downloading
- Press “Allow” to watch the video
- If you are 18+, click Allow
- Click “Allow” to win the prize and get it in our shop!
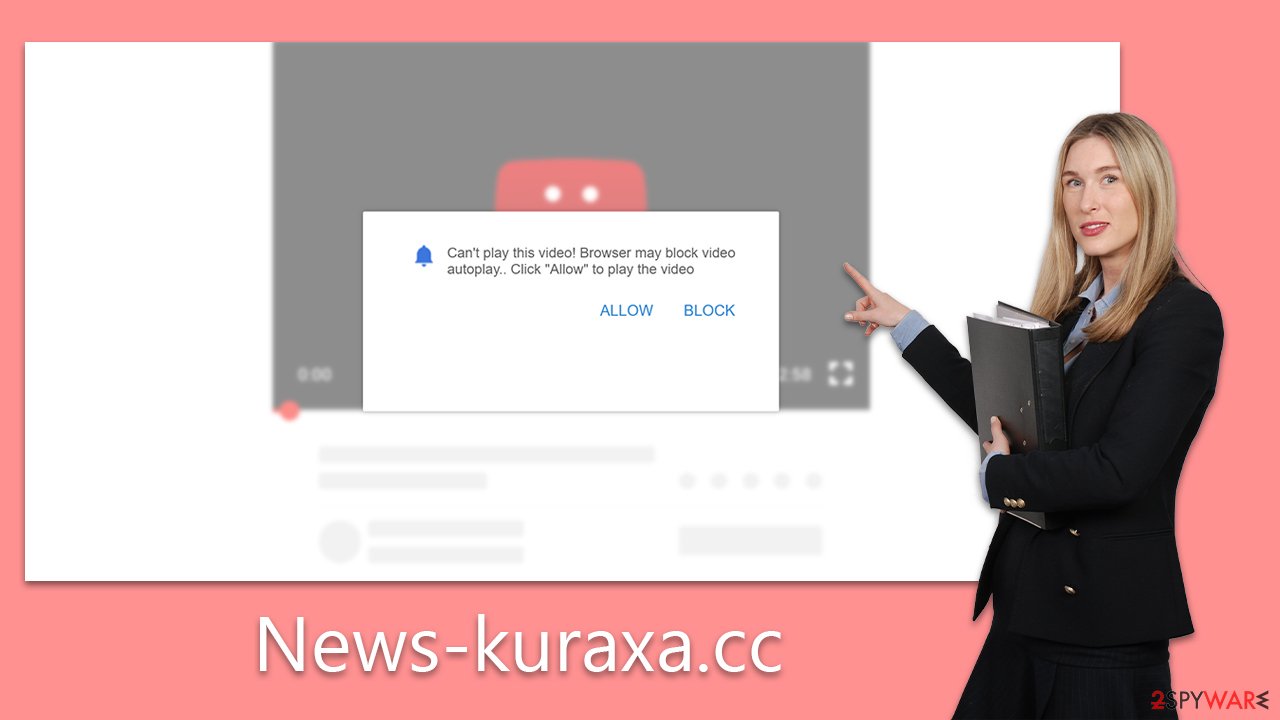
These prompts are fabricated and aim singularly at coaxing the user into clicking the “Allow” button in the notification dialog. Following this action, there's typically a period of inactivity, leading many to overlook or forget their previous engagement. Subsequently, however, users may be bombarded with News-kuraxa.cc ads showcasing deceptive content like phony malware warnings, get-rich-quick schemes, and other questionable offerings.
It's imperative to note that these misleading prompts aren't exclusive to News-kuraxa.cc. Numerous other websites employ strikingly similar phrases and visuals to hoodwink individuals into enabling push notifications, including Monuadsinc.com, Yourzev24.com, and many others.
Dangers of unwanted ads
While users may feel that push notifications from malicious websites appear unexpectedly, these notifications arise from prior consent, whether given knowingly or inadvertently. If you've encountered unanticipated pop-ups from News-kuraxa.cc, it indicates that at some point, permission was granted.
These notifications can surface irrespective of the websites currently being browsed and whether the browser is actively in use or idling. Typically, they manifest as pop-ups at specific corners of the screen, influenced by the operating system.
The primary concern is the detrimental content these ads can introduce. Users might encounter deceptive messages, such as lucrative work-from-home schemes demanding an upfront payment. Many fall prey, only to realize later that the promised opportunities are non-existent. Additionally, some notifications mimic security alerts, insinuating system infections and urging the installation of protective software. These can often be facades for tech support scams, leading users to unintentionally install adware or other undesired applications.
Removal of unwanted push notifications requires accessing browser settings
Many individuals perceive the intrusive ads from News-kuraxa.cc as indicative of a system infection, a common symptom of malicious software. Such reactions can be attributed to a general unfamiliarity with the intricacies of the push notification feature. When this lack of knowledge is paired with the fact that users were deceived into subscribing, it often leads to confusion, with many left puzzled about how to eliminate these unwarranted push notifications.
However, there's a silver lining. Even if one falls victim to such a scam, disabling push notifications from questionable sources is straightforward. The solution simply involves navigating to your browser's settings. Within site settings, one can easily restrict News-kuraxa.cc from leveraging the browser's API to dispatch ads. Here's a step-by-step guide tailored for your specific browser:
Google Chrome (desktop)
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.
![Stop notifications on Chrome PC 2 Stop notifications on Chrome PC 2]()
Google Chrome (Android)
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).
![Stop notifications on Chrome Android Stop notifications on Chrome Android]()
Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.
![Stop notifications on Mozilla Firefox 2 Stop notifications on Mozilla Firefox 2]()
MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.
![Stop notifications on Edge Chromium Stop notifications on Edge Chromium]()
Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.
![Stop notifications on Safari Stop notifications on Safari]()
Internet Explorer
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.
![Stop notifications on Internet Explorer Stop notifications on Internet Explorer]()
- Locate the web address in question under Allowed sites and pick Remove.
Checking the system for adware or other infections
Many individuals stumble upon News-kuraxa.cc after clicking on dubious links. However, another prevalent cause of such encounters is adware, a type of potentially unwanted program.
The primary aim of adware is to inundate users with a barrage of advertisements, which can severely disrupt regular browsing with pop-ups, deals, and other intrusive ads. Some aggressive adware variants operate covertly, maintaining hidden connections to remote servers and generating profits for cybercriminals.
To ascertain the presence of adware, review the applications and browser extensions on your device. An efficient alternative is to utilize reputable security software like SpyHunter 5Combo Cleaner or Malwarebytes, which can seamlessly detect and eradicate such threats. For thorough cleanup, tools like FortectIntego can be deployed to ensure no residual traces persist.
How to prevent from getting adware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.






