News-rihusi.cc ads (fake) - Free Instructions
News-rihusi.cc ads Removal Guide
What is News-rihusi.cc ads?
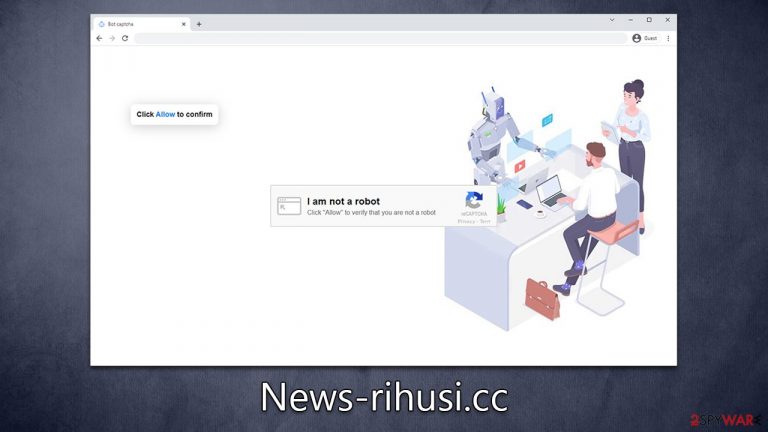
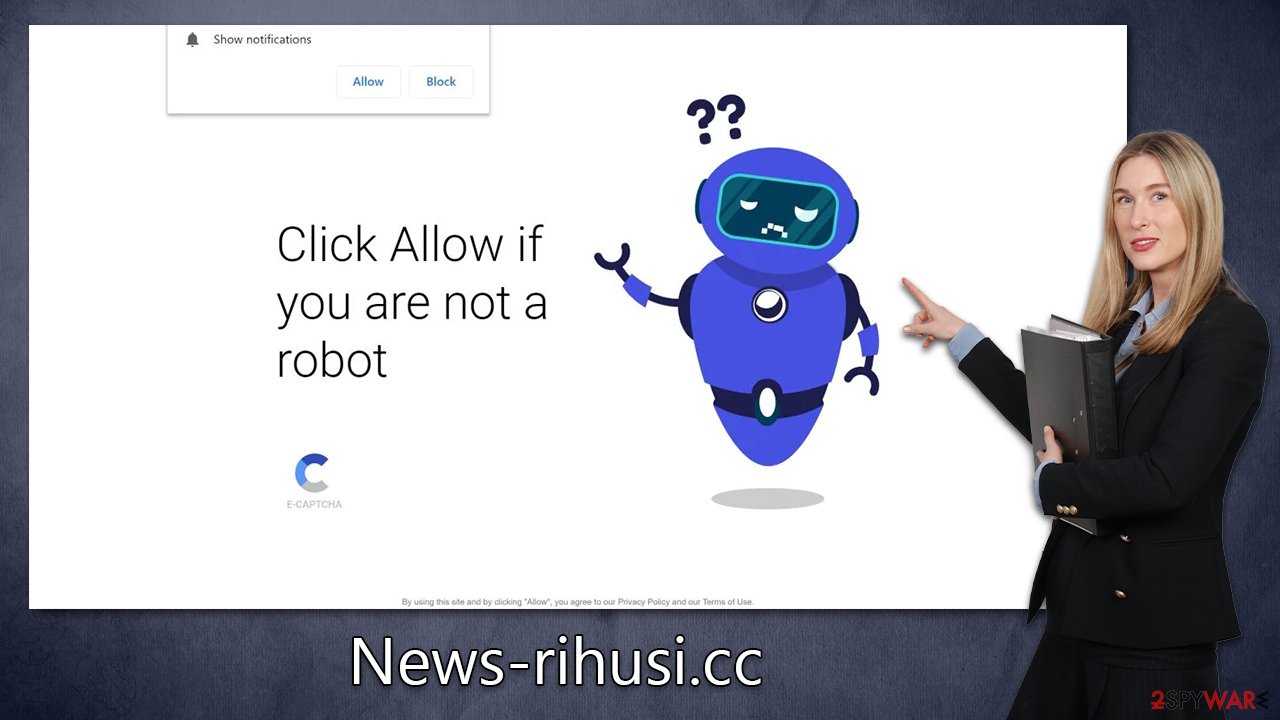
News-rihusi.cc attempts to make users allow notifications by showing them misleading content
News-rihusi.cc ads may seem to appear out of nowhere on your desktop or mobile device, but believe it or not, you're certainly not alone with this issue. Unprompted pop-ups have been popping up for countless users no matter what websites they visited – and it can be extremely annoying. To make matters worse, these intrusive ad windows often overshadow all other active programs running on the system.
If you are forced to see News-rihusi.cc pop-ups on a regular basis, you should not worry too much, as there is an easy way to get rid of them. Besides showing how to get rid of the notifications, we will also explain how to check your system for infections that could possibly be related to the mentioned activity.
| Name | News-rihusi.cc |
| Type | Push notifications, ads, pop-ups, scam |
| Distribution | Users allow push notifications after they click the “Allow” button within the prompt |
| Symptoms | Pop-up notifications are shown on a desktop randomly without a warning |
| Risks | The ads shown within push notifications might include misleading messages and links to malicious websites. If clicked, you might end up infecting your system with malware, disclosing your personal information, or losing money |
| Removal | Access browser settings to stop intrusive push notifications. After that, make sure that your system is not infected with adware or malware – scan it with SpyHunter 5Combo Cleaner |
| Other tips | You can employ FortectIntego to clean your browsers from trackers and fix any issues that could arise due to adware/malware infections |
News-rihusi.cc pop-ups: what are they?
Pop-up ads are a type of online advertisement that appears as a window or box on a webpage. They are often used by marketers to capture visitors’ attention and prompt them to take action, such as buying a product, signing up for a newsletter, or downloading an app. Pop-up ads can effectively drive conversions and be extremely lucrative to those hosting them, although they can also be annoying and intrusive to visitors of websites.
Unlike pop-up ads, News-rihusi.cc ads are not quite the same, despite that they may seem so in the first place. The major difference between these and pop-up ads is that they operate in a completely different manner – by using the push notification feature in the browser.
This means that while pop-up ads can show up only when entering particular websites or whenever they are called up by a particular potentially unwanted program installed on the system, push notifications run on the system level and can be called up as often as a request is sent from the website, in this case, News-rihusi.cc. This explains why users might see these pop-ups regardless of which websites they are visiting or even whether they are using a browser at all.
Since push notifications are initiated via the browser, shutting it down completely would get rid of the activity. However, this is not a great workaround because every time you'll start the browser, ads will come back. Since these ads may include links to malicious websites, we recommend not interacting with them and using the instructions below to remove them once and for all.
Get rid of News-rihusi.cc ads and check your system for infections
It can be difficult to pinpoint the source of intrusive pop-ups, and many users mistakenly believe that their systems have been infected with a virus. To ensure optimal security for your device, we highly recommend scanning your system with either SpyHunter 5Combo Cleaner or Malwarebytes antivirus software. If adware is detected during the scan, you should clean all browsers on your machine and repair any potential damage using FortectIntego. Taking these precautions will help protect against future suspicious activity.
Once you are sure that your system is clean and malware-free, you should check the instructions below to remove News-rihusi.cc ads from your screen once and for all. Note that this guide can be used to block any other suspicious website from showing push notifications to you.
Google Chrome (desktop)
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.

Google Chrome (Android)
- Open Google Chrome and tap on Settings (three vertical dots).
- Select Notifications.
- Scroll down to the Sites section.
- Locate the unwanted URL and toggle the button to the left (Off setting).

Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.

MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.

Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.

Internet Explorer
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.

- Locate the web address in question under Allowed sites and pick Remove.
Tips on how to avoid push notification scams in the future
Visiting high-risk websites can be a dangerous activity that puts users at risk of infecting their computers with malicious software or exposing personal information to cybercriminals. Such sites are typically identified by the presence of certain keywords in the URL or domain name, such as “hack,” “pirate,” “crack,” etc. That being said, most people visit these sites deliberately, whether knowing or not knowing the risk this poses.
To avoid being infected with malware or redirected to other dubious sites, such as News-rihusi.cc, you should stay away from pirated software distribution sites. Likewise, gambling, illegal video streaming, YouTube video converting, and similar places might be just as dangerous. Despite this, you might come across fake or malicious websites at one point, regardless of how many precautions you take, so you should be wary of that.
When it comes to scam messages hosted on malicious sites asking to enable push notifications, you are bound to see a request to press the “Allow” button within the notification prompt, but the reason given is always bogus. For example, you might be told that you need to verify you aren't a robot or that you are +18 of age.
Please ignore these requests. Regardless of which messages or pictures are shown on the site, clicking the “Allow” button within the prompt will always allow that site to deliver any kind of information directly to users' screens. Even if you do accept these notifications, please do not interact with them in any capacity.
For your general security, please make sure you have powerful anti-malware software running on your system at all times. Whenever a notification about a detected threat is triggered, do not ignore it or disable security software, as you may easily infect your system with dangerous malware.
How to prevent from getting adware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
