Newstarads.com (Free Instructions) - Virus Removal Guide
Newstarads.com Removal Guide
What is Newstarads.com?
Newstarads.com – an adware website that is causing lots of redirects to malicious sites and loads fake security software deals
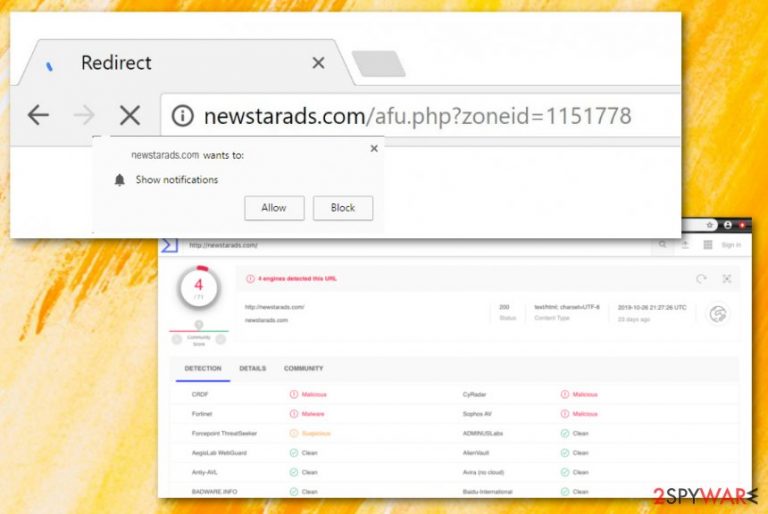
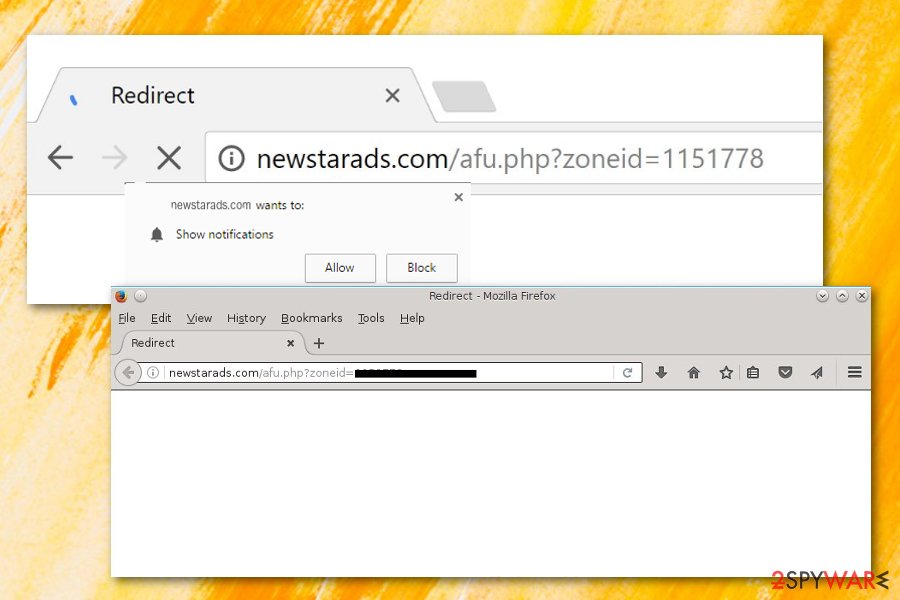
Newstarads.com is a potentially unwanted program that has an ability to redirect to porn websites and display rogue antivirus-related pop-ups, according to a user's report.[1] The adware app has also been detected by some antivirus engines as malicious/malware (CRDF, Fortinet, CyRadar, Sophos AV), and as suspicious (Forcepoint ThreatSeeker).[2] The most common signs of Newstarads.com virus infiltration would be frequent advertising, constant redirecting sessions, tracking of browsing information, injecting BHOs[3] such as extensions and plug-ins into browsers, messing with some major browser settings such as the homepage and new tab URL sections.
| Name | Newstarads.com |
|---|---|
| Type | Potentially unwanted program |
| Sub-type | Adware application |
| Detections | This rogue product has been flagged as malicious by CRDF, Fortinet, CyRadar, and Sophos AV engines. Also, Forcepoint ThreatSeeker finds the domain as a suspicious one |
| Abilities | Users' reports claim that the adware sends to pornography websites and loads with rogue software offers. Also, the PUP might be able to redirect to affiliate sources, display frequent ads, collect browsing-related data |
| Distribution | Third-party software sources such as download.com, soft32.com distribute adware programs. These PUPs also come through fake software updates, infectious hyperlinks/adverts, etc. |
| Removal | Employ automatical software to get rid of the adware program or use step-by-step guidelines that are added to the end of this article |
| System repair | If the adware program has corrupted some files or entries, employ a tool such as FortectIntego and try to fix the damage as it might appear helpful in this situation |
Newstarads.com is not a very huge threat as it is classified as an adware program and a PUP, however, the program still poses some risk. Its redirects might cause indirect danger to the user and the used computer. By landing on an infectious website, you risk catching a dangerous malware infection. Trojan horses, ransomware, worms, and other threats are commonly distributed via third-party sources and wait for their chance to catch a potential victim.
Furthermore, frequent redirecting might relate to constant browser struggles and slowdowns as two many activities at a time will overuse system resources and slow down its work. The same is valid for Newstarads.com pop-up ads that might start overloading your browser sessions with annoying notifications, surveys, deals, and coupons. Be aware of various surveys and questionnaires as they might ask for some personally-identifiable information.
Avoid providing any type of sensitive data for rogue applications and stay away from any content that comes from Newstarads.com. This adware might record browsing-related data such as hyperlinks clicked, commonly visited webpages, offers searched, recently saved bookmarks, your IP address, geolocation,[4] email address, and start spamming you with supposedly reliable offers when the true goal is to collect income by supporting rogue security software, and similar.
Ad-supported applications such as Newstarads.com might trick you into buying completely unnecessary services and products for a big sum of money. This is why it is better to refuse unknown offers and get your software from reliable developers only. Continuously, developers are also seeking to benefit from a marketing strategy known as cost-per-click when income falls into the developers' pockets within each click on an advertisement.
Nevertheless, Newstarads.com might end up changing your browser's homepage and new tab URL zones to its own. Additionally, you might see browser settings filled with bogus extensions, plug-ins, and add-ons that might have come as browser helper objects connected to the ad-supported application itself. Keep in mind that once you are performing the Newstarads.com removal process, the objects also need to be deleted for permanent removal.
You can remove Newstarads.com with the help of antimalware software or by applying step-by-step rules that are added to the end of this article. Also, if you keep experiencing adverts from this domain only occasionally, you can try downloading an ad-blocking tool to your web browser. After you get rid of the adware, check for possible file damage. If you see any corrupted components, you can try fixing them with a program such as FortectIntego.
Additionally, there is a chance to stop pop-up ads coming from Newstarads.com by eliminating the domain name from the Notification list in your browser settings. You can complete this type of process with the help of the following instructions:
- Open the browser that has been showing ads.
- Click on the three dots on your upper right.
- Go to Settings > Advanced.
- Afterward, continue with the Notification list that can be found under Site Settings.
- Then, find Newstarads.com and remove it from the list permanently.
The infection starts with a bundle
Experts from NoVirus.uk[5] claim that the most popular and easiest way to get adware into a particular system is to provide it together with a bundle of software. Original programs do not signal about anything suspicious and gullible users often apply for the entire package with the adware program hiding in it.
This mostly happens when the user opts for the Quick/Recommended technique instead of the Custom/Advanced mode. The first option does not protect the computer system and might allow silent infiltration of bogus content when the second option gives the user a choice of his own. Here you can deselect any pending downloading you want.
Continuously, adware apps can camouflage as fake Flash Player updates and end up on the computer by tricking a user to upgrade his/her software. Regarding this fact, you should always check if a new update was truly released before upgrading any program of yours.
In addition, ad-supported content might be provided in an infectious hyperlink or notification and end up on the user's computer system after he/she clicks on the suspicious component. It is very important to be careful online and also have reliable automatical protection working along your side.
Terminating Newstarads.com from your machine might be easy with automatical software
Newstarads.com virus is a sneaky program as it might place suspicious products all over the machine and act as nothing happened. As a result, the components might be hard to detect by a human eye, so antimalware software must get involved in this type of case.
Additionally, you can complete the Newstarads.com removal process by following our manual step-by-step guidelines that are added to the end of this article. Here you will find instructions on how to clean your operating systems and web browsers such as Safari, Microsoft Edge, Google Chrome, Mozilla Firefox, and Internet Explorer.
After you remove Newstarads.com, you should check the system for any possibly corrupted files. If you find any components that require fixing, employ a reliable repair tool and try repairing the damaged component back to its previous state.
You may remove virus damage with a help of FortectIntego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
Getting rid of Newstarads.com. Follow these steps
Uninstall from Windows
To remove the adware program and all its leftovers from Windows, apply the following guidelines:
Instructions for Windows 10/8 machines:
- Enter Control Panel into Windows search box and hit Enter or click on the search result.
- Under Programs, select Uninstall a program.

- From the list, find the entry of the suspicious program.
- Right-click on the application and select Uninstall.
- If User Account Control shows up, click Yes.
- Wait till uninstallation process is complete and click OK.

If you are Windows 7/XP user, proceed with the following instructions:
- Click on Windows Start > Control Panel located on the right pane (if you are Windows XP user, click on Add/Remove Programs).
- In Control Panel, select Programs > Uninstall a program.

- Pick the unwanted application by clicking on it once.
- At the top, click Uninstall/Change.
- In the confirmation prompt, pick Yes.
- Click OK once the removal process is finished.
Delete from macOS
To eliminate Newstarads.com virus from macOS, use these instructing steps:
Remove items from Applications folder:
- From the menu bar, select Go > Applications.
- In the Applications folder, look for all related entries.
- Click on the app and drag it to Trash (or right-click and pick Move to Trash)

To fully remove an unwanted app, you need to access Application Support, LaunchAgents, and LaunchDaemons folders and delete relevant files:
- Select Go > Go to Folder.
- Enter /Library/Application Support and click Go or press Enter.
- In the Application Support folder, look for any dubious entries and then delete them.
- Now enter /Library/LaunchAgents and /Library/LaunchDaemons folders the same way and terminate all the related .plist files.

Remove from Microsoft Edge
Delete unwanted extensions from MS Edge:
- Select Menu (three horizontal dots at the top-right of the browser window) and pick Extensions.
- From the list, pick the extension and click on the Gear icon.
- Click on Uninstall at the bottom.

Clear cookies and other browser data:
- Click on the Menu (three horizontal dots at the top-right of the browser window) and select Privacy & security.
- Under Clear browsing data, pick Choose what to clear.
- Select everything (apart from passwords, although you might want to include Media licenses as well, if applicable) and click on Clear.

Restore new tab and homepage settings:
- Click the menu icon and choose Settings.
- Then find On startup section.
- Click Disable if you found any suspicious domain.
Reset MS Edge if the above steps did not work:
- Press on Ctrl + Shift + Esc to open Task Manager.
- Click on More details arrow at the bottom of the window.
- Select Details tab.
- Now scroll down and locate every entry with Microsoft Edge name in it. Right-click on each of them and select End Task to stop MS Edge from running.

If this solution failed to help you, you need to use an advanced Edge reset method. Note that you need to backup your data before proceeding.
- Find the following folder on your computer: C:\\Users\\%username%\\AppData\\Local\\Packages\\Microsoft.MicrosoftEdge_8wekyb3d8bbwe.
- Press Ctrl + A on your keyboard to select all folders.
- Right-click on them and pick Delete

- Now right-click on the Start button and pick Windows PowerShell (Admin).
- When the new window opens, copy and paste the following command, and then press Enter:
Get-AppXPackage -AllUsers -Name Microsoft.MicrosoftEdge | Foreach {Add-AppxPackage -DisableDevelopmentMode -Register “$($_.InstallLocation)\\AppXManifest.xml” -Verbose

Instructions for Chromium-based Edge
Delete extensions from MS Edge (Chromium):
- Open Edge and click select Settings > Extensions.
- Delete unwanted extensions by clicking Remove.

Clear cache and site data:
- Click on Menu and go to Settings.
- Select Privacy, search and services.
- Under Clear browsing data, pick Choose what to clear.
- Under Time range, pick All time.
- Select Clear now.

Reset Chromium-based MS Edge:
- Click on Menu and select Settings.
- On the left side, pick Reset settings.
- Select Restore settings to their default values.
- Confirm with Reset.

Remove from Mozilla Firefox (FF)
To clean Mozilla Firefox from unwanted content, complete the below-given guidelines:
Remove dangerous extensions:
- Open Mozilla Firefox browser and click on the Menu (three horizontal lines at the top-right of the window).
- Select Add-ons.
- In here, select unwanted plugin and click Remove.

Reset the homepage:
- Click three horizontal lines at the top right corner to open the menu.
- Choose Options.
- Under Home options, enter your preferred site that will open every time you newly open the Mozilla Firefox.
Clear cookies and site data:
- Click Menu and pick Settings.
- Go to Privacy & Security section.
- Scroll down to locate Cookies and Site Data.
- Click on Clear Data…
- Select Cookies and Site Data, as well as Cached Web Content and press Clear.

Reset Mozilla Firefox
If clearing the browser as explained above did not help, reset Mozilla Firefox:
- Open Mozilla Firefox browser and click the Menu.
- Go to Help and then choose Troubleshooting Information.

- Under Give Firefox a tune up section, click on Refresh Firefox…
- Once the pop-up shows up, confirm the action by pressing on Refresh Firefox.

Remove from Google Chrome
To erase unwanted objects from Google Chrome, use the following steps:
Delete malicious extensions from Google Chrome:
- Open Google Chrome, click on the Menu (three vertical dots at the top-right corner) and select More tools > Extensions.
- In the newly opened window, you will see all the installed extensions. Uninstall all the suspicious plugins that might be related to the unwanted program by clicking Remove.

Clear cache and web data from Chrome:
- Click on Menu and pick Settings.
- Under Privacy and security, select Clear browsing data.
- Select Browsing history, Cookies and other site data, as well as Cached images and files.
- Click Clear data.

Change your homepage:
- Click menu and choose Settings.
- Look for a suspicious site in the On startup section.
- Click on Open a specific or set of pages and click on three dots to find the Remove option.
Reset Google Chrome:
If the previous methods did not help you, reset Google Chrome to eliminate all the unwanted components:
- Click on Menu and select Settings.
- In the Settings, scroll down and click Advanced.
- Scroll down and locate Reset and clean up section.
- Now click Restore settings to their original defaults.
- Confirm with Reset settings.

Delete from Safari
Remove unwanted extensions from Safari:
- Click Safari > Preferences…
- In the new window, pick Extensions.
- Select the unwanted extension and select Uninstall.

Clear cookies and other website data from Safari:
- Click Safari > Clear History…
- From the drop-down menu under Clear, pick all history.
- Confirm with Clear History.

Reset Safari if the above-mentioned steps did not help you:
- Click Safari > Preferences…
- Go to Advanced tab.
- Tick the Show Develop menu in menu bar.
- From the menu bar, click Develop, and then select Empty Caches.

After uninstalling this potentially unwanted program (PUP) and fixing each of your web browsers, we recommend you to scan your PC system with a reputable anti-spyware. This will help you to get rid of Newstarads.com registry traces and will also identify related parasites or possible malware infections on your computer. For that you can use our top-rated malware remover: FortectIntego, SpyHunter 5Combo Cleaner or Malwarebytes.
How to prevent from getting adware
Protect your privacy – employ a VPN
There are several ways how to make your online time more private – you can access an incognito tab. However, there is no secret that even in this mode, you are tracked for advertising purposes. There is a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
No backups? No problem. Use a data recovery tool
If you wonder how data loss can occur, you should not look any further for answers – human errors, malware attacks, hardware failures, power cuts, natural disasters, or even simple negligence. In some cases, lost files are extremely important, and many straight out panic when such an unfortunate course of events happen. Due to this, you should always ensure that you prepare proper data backups on a regular basis.
If you were caught by surprise and did not have any backups to restore your files from, not everything is lost. Data Recovery Pro is one of the leading file recovery solutions you can find on the market – it is likely to restore even lost emails or data located on an external device.
- ^ lSugol. NewStarAds Adware. Android Central. Forums.
- ^ URL detection information. VirusTotal. Detections.
- ^ What Is a BHO (Browser Helper Object) Add On?. Lifewire.com. An independent news source.
- ^ Geolocation. Wikipedia. The free encyclopedia.
- ^ NoVirus.uk. NoVirus.uk. Security and spyware news.
