Not-robot.top ads (fake) - Free Guide
Not-robot.top ads Removal Guide
What is Not-robot.top ads?
Not-robot.top is a website that asks visitors to enable push notifications using deception
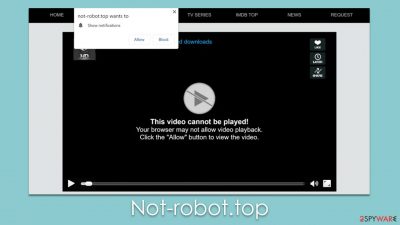
The Not-robot.top push notification scam is a prevalent internet threat that users often encounter inadvertently. Upon visiting these types of websites, a prompt appears asking users to allow push notifications. This request, while seemingly harmless, can lead to a disruptive chain of events.
Once users grant permission, they open the door to a barrage of unsolicited pop-ups. These pop-ups can surface anytime while using the browser, whether it is active or idle. The content of these pop-ups varies significantly, ranging from annoying ads to misleading messages and phishing attempts designed to deceive users into divulging sensitive information.
Not-robot.top scam exemplifies the sneaky techniques used by online scammers to exploit unsuspecting internet users. Recognizing these tactics and knowing how to protect oneself is essential in today's digital landscape. In the sections that follow, we provide a comprehensive overview of this scam, preventive measures, and what to do if you fall victim. Awareness and informed internet use are the best defenses against such online threats.
| Name | Not-robot.top |
| Similar scams | Monadvs.com, Aahdxn.com, Fast-update.com |
| Type | Push notifications, pop-ups, ads, scam |
| Distribution | After users click the “Allow” button within the prompt upon site entry |
| Symptoms | Pop-ups show up on a regular basis on the screen – these ads often include inappropriate, scam, phishing, or other similar content |
| Risks | Links from the site might cause you to go to harmful websites, which may result in malware infections, financial losses, or personal data exposure. |
| Removal | Access browser settings to stop intrusive push notifications. After that, make sure that your system is not infected with adware or malware – scan it with SpyHunter 5Combo Cleaner |
| Other tips | It is important to clean web browser caches to prevent further data tracking and other issues related to web data corruption – use FortectIntego to do this quicker |
How scams spread
Not-robot.top and similar malicious websites are typically encountered by users via the act of clicking on malicious links. These links are often found on torrent websites, platforms distributing pirated software, illegal video streaming services, and other similar locations. The content of these sites might seem attractive, promising free downloads of software, movies, or other media. However, in reality, they are breeding grounds for such harmful links.
The first step in avoiding these threats is exercising discretion while surfing the internet. It is crucial to understand the risks associated with downloading and streaming content from untrustworthy sources. Using legal and reputable platforms for downloading or streaming media can significantly reduce the risk of encountering such malicious links. Regularly updating your web browser and operating system can also help because updates often contain security patches that guard against known threats.
In addition to clicking on malicious links, adware can also lead users to websites like Not-robot.top. Adware is a form of software that automatically generates and displays advertisements when a user is online. Adware can be particularly insidious as it can redirect users to malicious websites or insert harmful links into otherwise safe websites.
Avoiding adware requires a combination of careful internet use and robust cybersecurity measures. Always download software from trusted sources, as adware can often be bundled with other software, especially free or pirated applications. It's also crucial to pay attention when installing new software. Opt for the custom installation process if available, as this allows you to see what's being installed and to deselect any unwanted programs.
Regular use of antivirus or antimalware software can provide another layer of protection against adware. These programs can scan for and remove adware and other types of malware from your device. Remember to keep your security software up-to-date to protect against the latest threats.
Finally, be cautious when clicking on ads, as some may be disguised as legitimate but are designed to install adware on your device. If an ad seems suspicious or too good to be true, it's best to avoid it.
How users get tricked
The key to the success of scams such as the Not-robot.top push notification scam is manipulation. Scammers employ a variety of strategies to trick users into granting permission for push notifications. They capitalize on users' familiarity with certain standard internet protocols or appeal to human curiosity and, in doing so, trick users into believing their requests are legitimate. Below are some common tactics employed:
- “Click Allow to confirm you are not a robot”: This tactic plays on the common “CAPTCHA” system used by many legitimate websites to distinguish human users from bots. CAPTCHA typically involves solving a puzzle or typing in a set of distorted characters. Scammers exploit this familiarity by asking users to click “Allow” to confirm they're not a robot. It feels familiar and seems harmless, so users often comply.
- “Click Allow if you are 18+”: This approach feeds on curiosity. It suggests there's adult or restricted content that can be accessed once the user confirms they are above 18 by clicking “Allow.” The hint of exclusive content can lead users to click without fully considering the consequences.
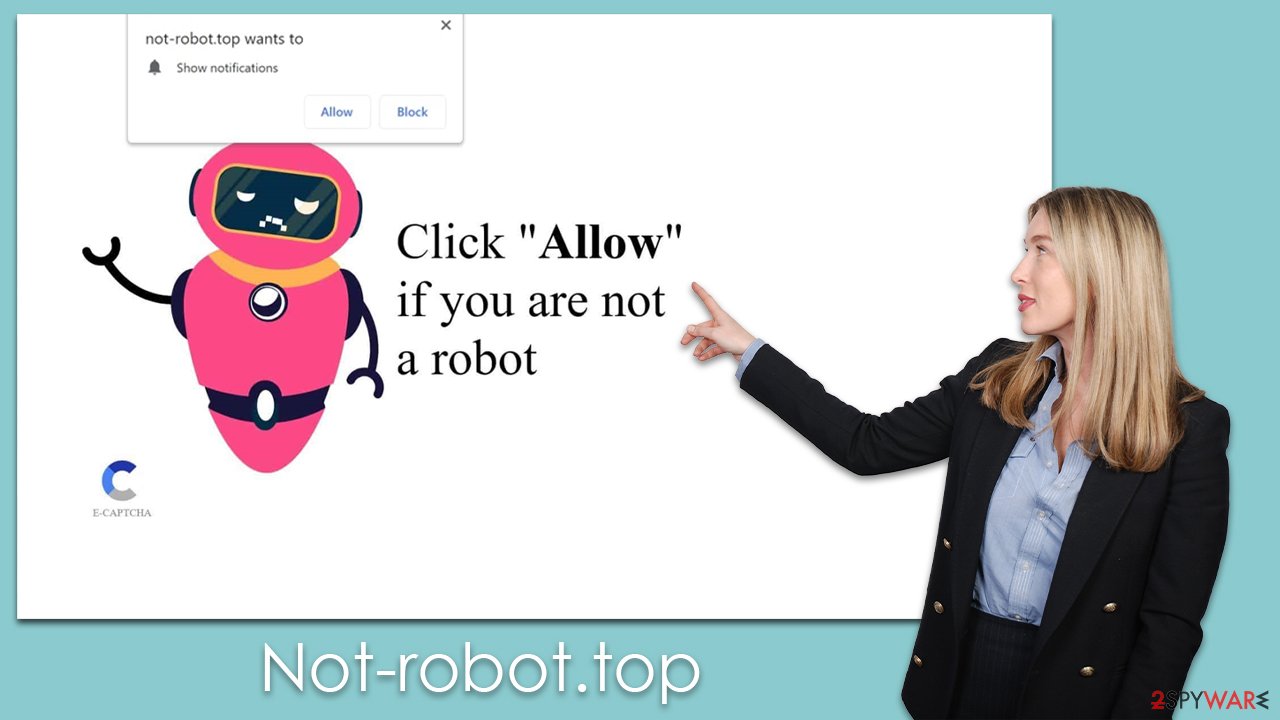
It's crucial to understand that these prompts are deceptive techniques. There is no content that will be revealed upon clicking “Allow,” nor is it a genuine CAPTCHA check. The only result is the enabling of push notifications which allows scammers to spam users with unwanted pop-ups.
Remember, legitimate websites will rarely ask you to confirm your age or humanity via push notifications. Always be skeptical of such requests, and if you encounter them, it's best to close the website or navigate away immediately. Internet safety is often about discerning the false from the true, and awareness of these scam tactics is a major step toward safer online experiences.
Not-robot.top ads removal
Unwanted push notifications, like those from Not-robot.top, often sow confusion among users. It's unclear where they originate, and their incessant nature can lead some to mistake them for symptoms of a virus infection. While it is natural to resort to security software scans in these scenarios, it's crucial to understand that the removal of these push notifications primarily involves manual adjustments in your browser settings.
Nevertheless, it's worth noting that your device may have adware or other unwanted software operating undetected in the background. These can pose potential risks, including malware infections. Hence, it's prudent to initiate a comprehensive system scan with trusted security software, such as SpyHunter 5Combo Cleaner or Malwarebytes. Conducting this scan prior to manually removing the Not-robot.top push notifications will ensure that your system is free from any underlying threats that might reinitiate the problem.
Furthermore, it is advisable to clear your browser's cache and cookies using a tool like FortectIntego. This step can prevent further tracking of your data and impede additional unwanted pop-ups. It's part of a holistic approach to ensure that your digital environment remains secure and free from intrusive elements like the Not-robot.top scam. Dealing with such internet nuisances requires a blend of automated security measures and manual interventions, underlined by an understanding of the threats and how they operate.
Google Chrome (desktop)
- Open the Google Chrome browser and go to Menu > Settings.
- Scroll down and click on Advanced.
- Locate the Privacy and security section and pick Site Settings > Notifications.
- Look at the Allow section and look for a suspicious URL.
- Click the three vertical dots next to it and pick Block. This should remove unwanted notifications from Google Chrome.
![Stop notifications on Chrome PC 2 Stop notifications on Chrome PC 2]()
Mozilla Firefox
- Open Mozilla Firefox and go to Menu > Options.
- Click on Privacy & Security section.
- Under Permissions, you should be able to see Notifications. Click the Settings button next to it.
- In the Settings – Notification Permissions window, click on the drop-down menu by the URL in question.
- Select Block and then click on Save Changes. This should remove unwanted notifications from Mozilla Firefox.
![Stop notifications on Mozilla Firefox 2 Stop notifications on Mozilla Firefox 2]()
MS Edge (Chromium)
- Open Microsoft Edge, and go to Settings.
- Select Site permissions.
- Go to Notifications on the right.
- Under Allow, you will find the unwanted entry.
- Click on More actions and select Block.
![Stop notifications on Edge Chromium Stop notifications on Edge Chromium]()
Safari
- Click on Safari > Preferences…
- Go to the Websites tab and, under General, select Notifications.
- Select the web address in question, click the drop-down menu and select Deny.
![Stop notifications on Safari Stop notifications on Safari]()
Internet Explorer
- Open Internet Explorer, and click on the Gear icon at the top-right of the window.
- Select Internet options and go to the Privacy tab.
- In the Pop-up Blocker section, click on Settings.
![Stop notifications on Internet Explorer Stop notifications on Internet Explorer]()
- Locate the web address in question under Allowed sites and pick Remove.
How to prevent from getting adware
Choose a proper web browser and improve your safety with a VPN tool
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can't grant full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features. However, if you want true anonymity, we suggest you employ a powerful Private Internet Access VPN – it can encrypt all the traffic that comes and goes out of your computer, preventing tracking completely.
Lost your files? Use data recovery software
While some files located on any computer are replaceable or useless, others can be extremely valuable. Family photos, work documents, school projects – these are types of files that we don't want to lose. Unfortunately, there are many ways how unexpected data loss can occur: power cuts, Blue Screen of Death errors, hardware failures, crypto-malware attack, or even accidental deletion.
To ensure that all the files remain intact, you should prepare regular data backups. You can choose cloud-based or physical copies you could restore from later in case of a disaster. If your backups were lost as well or you never bothered to prepare any, Data Recovery Pro can be your only hope to retrieve your invaluable files.





